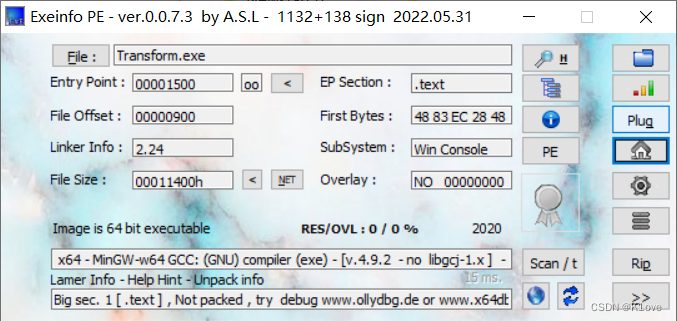
拖进 exeinfope查看pe文件的基本信息,发现没有壳是x64架构
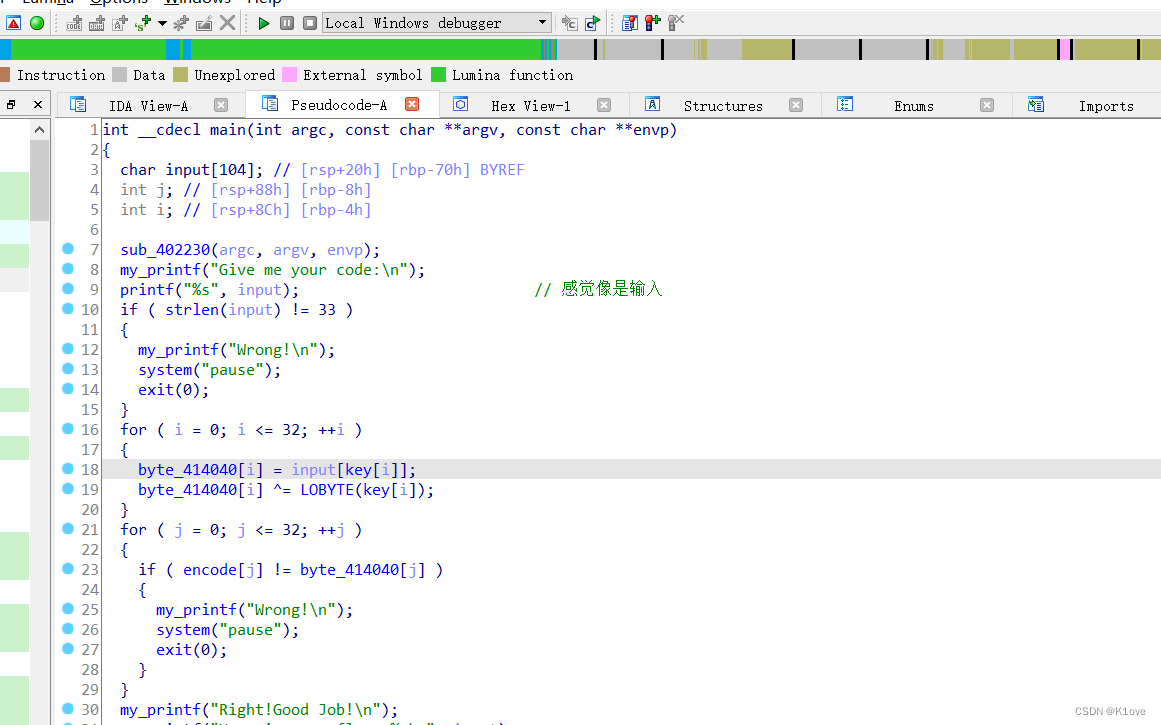
然后拖入 IDA f5进行静态分析
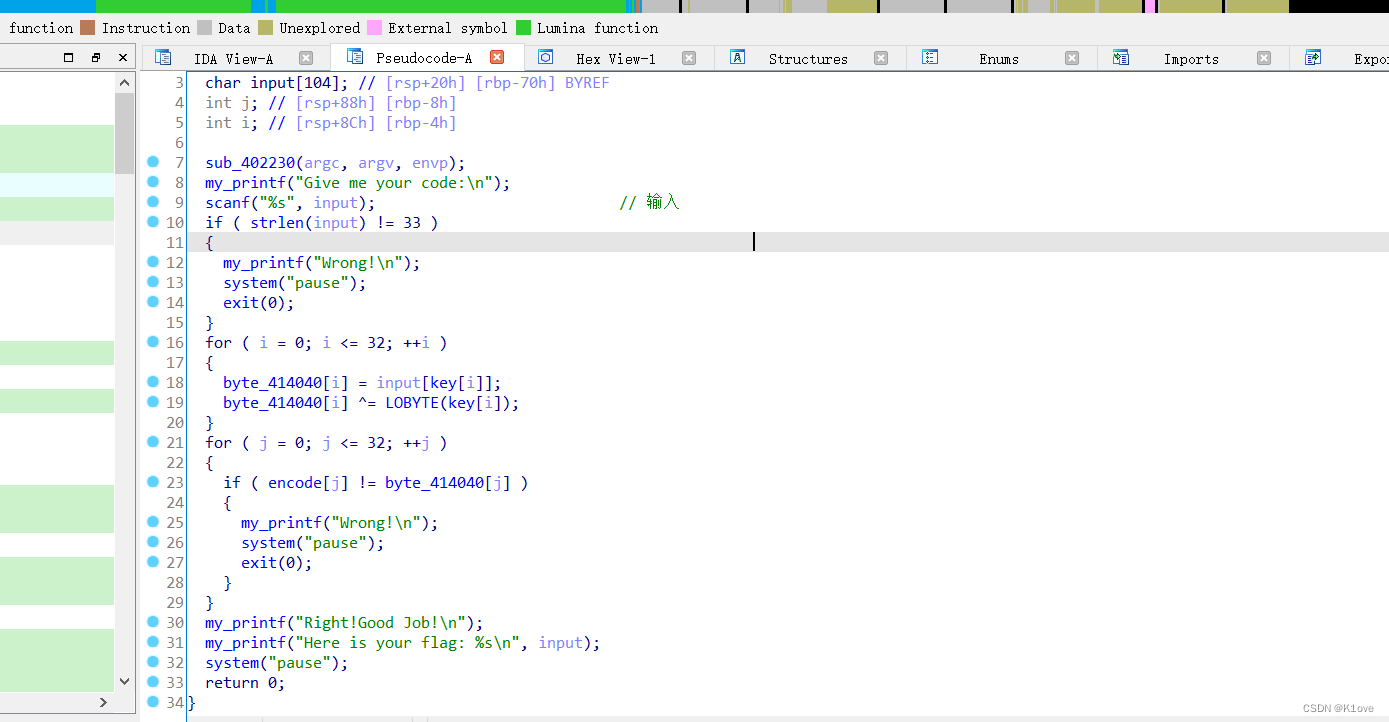
逻辑也很简单,就是先输入,然后检查长度是否是33字节,然后进行一个加密循环,然后比较密文,我们要做的事情就是先提取秘钥,然后提取密文,编写脚本就好了
key=[0x00000009, 0x0000000A, 0x0000000F, 0x00000017, 0x00000007, 0x00000018, 0x0000000C, 0x00000006, 0x00000001, 0x00000010 ,0x00000003, 0x00000011, 0x00000020, 0x0000001D, 0x0000000B, 0x0000001E ,0x0000001B, 0x00000016, 0x00000004, 0x0000000D, 0x00000013, 0x00000014, 0x00000015, 0x00000002, 0x00000019, 0x00000005, 0x0000001F, 0x00000008, 0x00000012, 0x0000001A, 0x0000001C, 0x0000000E,0x00] encode=[0x67, 0x79, 0x7B, 0x7F, 0x75, 0x2B, 0x3C, 0x52, 0x53, 0x79, 0x57, 0x5E, 0x5D, 0x42, 0x7B, 0x2D, 0x2A, 0x66, 0x42, 0x7E, 0x4C, 0x57, 0x79, 0x41, 0x6B, 0x7E, 0x65, 0x3C, 0x5C, 0x45, 0x6F, 0x62, 0x4D] flag = [0]*33 for i in range(33): encode[i] = encode[i] ^key[i] flag[key[i]]=chr(encode[i]) print(''.join(flag))





















 385
385











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








