Ipsec实验
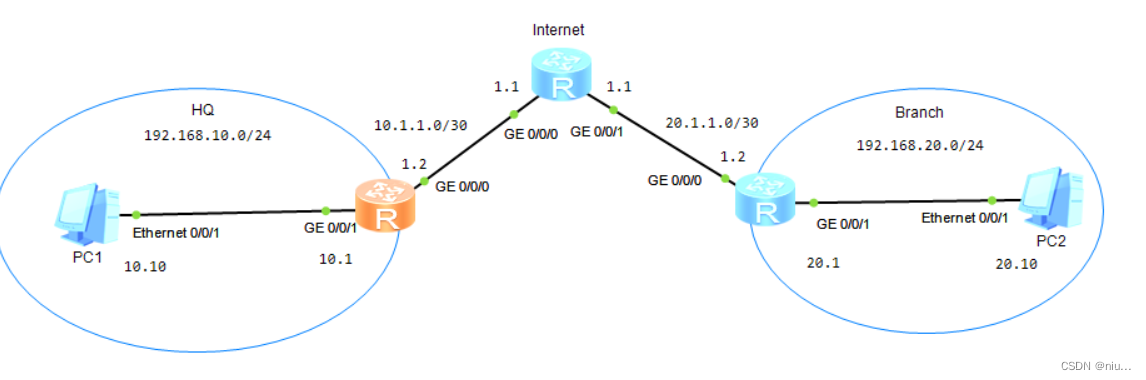
第一步,按照拓扑图放置设备。
第二步,配置PC的IP地址与网关。


第三步,配置各个路由的接口IP地址。
| HQ: [Huawei]int g 0/0/1 [Huawei-GigabitEthernet0/0/1]ip add 192.168.10.1 24 [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]ip address 10.1.1.2 30 |
| Internet: [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]ip add 10.1.1.1 30 [Huawei-GigabitEthernet0/0/0]int g 0/0/1 [Huawei-GigabitEthernet0/0/1]ip add 20.1.1.1 30 |
| Branch: [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]ip add 20.1.1.2 30 [Huawei-GigabitEthernet0/0/0]int g 0/0/1 [Huawei-GigabitEthernet0/0/1]ip add 192.168.20.1 24 |
第四步,配置HQ、Brach静态路由,并配置EASY IP。
| HQ: [Huawei]ip route-static 20.1.1.0 30 10.1.1.1 [Huawei]acl 2000 [Huawei-acl-basic-2000]rule permit source 192.168.10.0 0.0.0.255 [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]nat outbound 2000 |
| Branch: [Huawei]ip route-static 10.1.1.0 30 20.1.1.1 [Huawei]acl 2000 [Huawei-acl-basic-2000]rule permit source 192.168.20.0 0.0.0.255 [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]nat outbound 2000 |
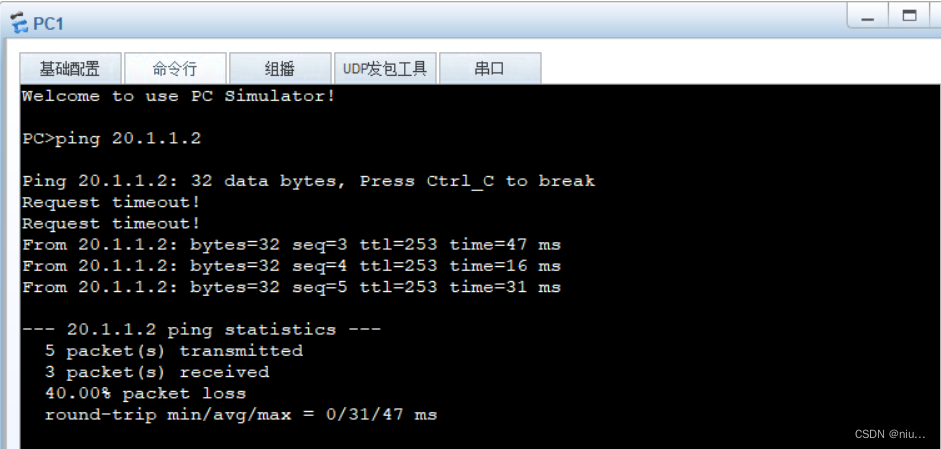
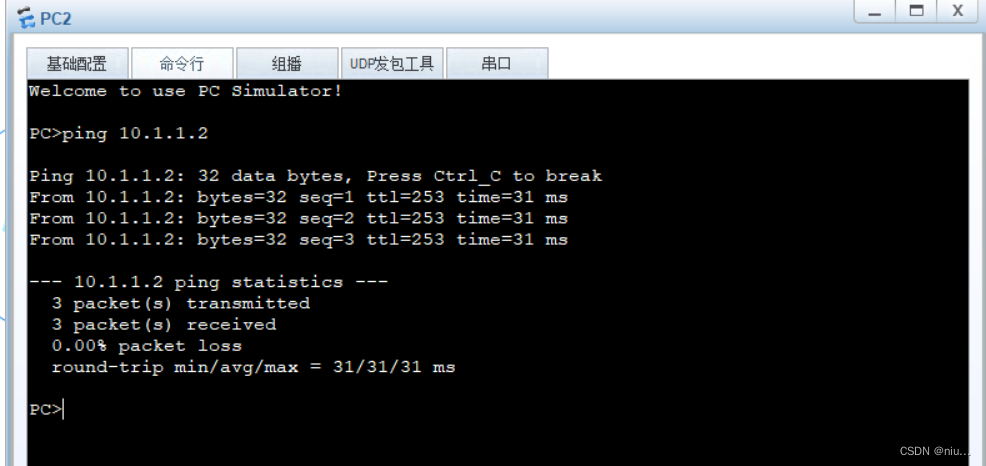
验证。在PC上ping对方的公网IP地址
第五步,配置静态路由,创建ACL识别兴趣流,创建安全提议,创建安全策略,应用安全策略。
| HQ: [Huawei]ip route-static 192.168.20.0 24 20.1.1.2 [Huawei]acl 3001 //创建兴趣流 [Huawei-acl-adv-3001]rule 5 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255 [Huawei]ipsec proposal HQ //创建安全提议 [Huawei-ipsec-proposal-HQ]encapsulation-mode tunnel //配置报文的封装模式 [Huawei-ipsec-proposal-HQ]transform esp //配置隧道采用的安全提议 [Huawei-ipsec-proposal-HQ]esp authentication-algorithm sha2-256 //配置esp认证的算法 [Huawei-ipsec-proposal-HQ]esp encryption-algorithm aes-128 //配置esp的加密算法 [Huawei-ipsec-proposal-HQ]display ipsec proposal //查看IPsec安全提议中配置的参数 Number of proposals: 1 IPSec proposal name: HQ Encapsulation mode: Tunnel Transform : esp-new ESP protocol : Authentication SHA2-HMAC-256 Encryption AES-128 [Huawei]ipsec policy P1 10 manual //创建并配置一条安全策略 [Huawei-ipsec-policy-manual-P1-10]security acl 3001指定安全策略所引用的访问控制列表(兴趣流) [Huawei-ipsec-policy-manual-P1-10]proposal HQ //指定ipsec安全策略所引用的提议 [Huawei-ipsec-policy-manual-P1-10]tunnel local 10.1.1.2 //配置安全隧道的本端地址 [Huawei-ipsec-policy-manual-P1-10]tunnel remote 20.1.1.2 //配置安全隧道的对端地址 [Huawei-ipsec-policy-manual-P1-10]sa spi outbound esp 12345 //设置安全联盟的spi(出口) [Huawei-ipsec-policy-manual-P1-10]sa spi inbound esp 54321 //设置安全联盟的spi(入口) [Huawei-ipsec-policy-manual-P1-10]sa string-key outbound esp cipher HQ //配置安全联盟的认证密钥 [Huawei-ipsec-policy-manual-P1-10]sa string-key inbound esp cipher HQ //配置安全联盟的认证密钥 [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]ipsec policy P1 //在接口上应用安全策略P1 [Huawei]display ipsec policy //查看出方向和入方向安全联盟相关参数 =========================================== IPSec policy group: "P1" Using interface: GigabitEthernet0/0/0 =========================================== Sequence number: 10 Security data flow: 3001 Tunnel local address: 10.1.1.2 Tunnel remote address: 20.1.1.2 Qos pre-classify: Disable Proposal name:HQ Inbound AH setting: AH SPI: AH string-key: AH authentication hex key: Inbound ESP setting: ESP SPI: 54321 (0xd431) ESP string-key: O55N#@=4H*'Q=^Q`MAF4<1!! ESP encryption hex key: ESP authentication hex key: Outbound AH setting: AH SPI: AH string-key: AH authentication hex key: Outbound ESP setting: ESP SPI: 12345 (0x3039) ESP string-key: O55N#@=4H*'Q=^Q`MAF4<1!! ESP encryption hex key: ESP authentication hex key: |
| Branch: [Huawei]ip route-static 192.168.10.0 24 10.1.1.2 [Huawei]acl 3001 [Huawei-acl-adv-3001]rule 5 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 [Huawei]ipsec proposal Branch [Huawei-ipsec-proposal-HQ]encapsulation-mode tunnel [Huawei-ipsec-proposal-HQ]transform esp [Huawei-ipsec-proposal-HQ]esp authentication-algorithm sha2-256 [Huawei-ipsec-proposal-HQ]esp encryption-algorithm aes-128 [Huawei-ipsec-proposal-HQ]display ipsec proposal Number of proposals: 1 IPSec proposal name: Branch Encapsulation mode: Tunnel Transform : esp-new ESP protocol : Authentication SHA2-HMAC-256 Encryption AES-128 [Huawei]ipsec policy P1 10 manual [Huawei-ipsec-policy-manual-P1-10]security acl 3001 [Huawei-ipsec-policy-manual-P1-10]proposal Branch [Huawei-ipsec-policy-manual-P1-10]tunnel local 20.1.1.2 [Huawei-ipsec-policy-manual-P1-10]tunnel remote 10.1.1.2 [Huawei-ipsec-policy-manual-P1-10]sa spi outbound esp 54321 [Huawei-ipsec-policy-manual-P1-10]sa spi inbound esp12345 [Huawei-ipsec-policy-manual-P1-10]sa string-key outbound esp cipher HQ [Huawei-ipsec-policy-manual-P1-10]sa string-key inbound esp cipher HQ [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]ipsec policy P1 [Huawei]display ipsec policy =========================================== IPSec policy group: "P1" Using interface: GigabitEthernet0/0/0 =========================================== Sequence number: 10 Security data flow: 3001 Tunnel local address: 20.1.1.2 Tunnel remote address: 10.1.1.2 Qos pre-classify: Disable Proposal name:Branch Inbound AH setting: AH SPI: AH string-key: AH authentication hex key: Inbound ESP setting: ESP SPI: 12345 (0x3039) ESP string-key: O55N#@=4H*'Q=^Q`MAF4<1!! ESP encryption hex key: ESP authentication hex key: Outbound AH setting: AH SPI: AH string-key: AH authentication hex key: Outbound ESP setting: ESP SPI: 54321 (0xd431) ESP string-key: O55N#@=4H*'Q=^Q`MAF4<1!! ESP encryption hex key: ESP authentication hex key: |
第六步,在NAT中排除VPN流量,采用新的ACL。
| HQ: [Huawei]acl 3002 [Huawei-acl-adv-3002]rule 5 deny ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255 //排除 192.168.10.0 与 192.168.20.0 互访流量 [Huawei-acl-adv-3002]rule 10 permit ip source 192.168.10.0 0.0.0.255 destination any [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]undo nat outbound 2000 [Huawei-GigabitEthernet0/0/0]nat outbound 3002 |
| Branch: [Huawei]acl 3002 [Huawei-acl-adv-3002]rule 5 deny ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255 [Huawei-acl-adv-3002]rule 10 permit ip source 192.168.20.0 0.0.0.255 destination any [Huawei]int g 0/0/0 [Huawei-GigabitEthernet0/0/0]undo nat outbound 2000 [Huawei-GigabitEthernet0/0/0]nat outbound 3002 |
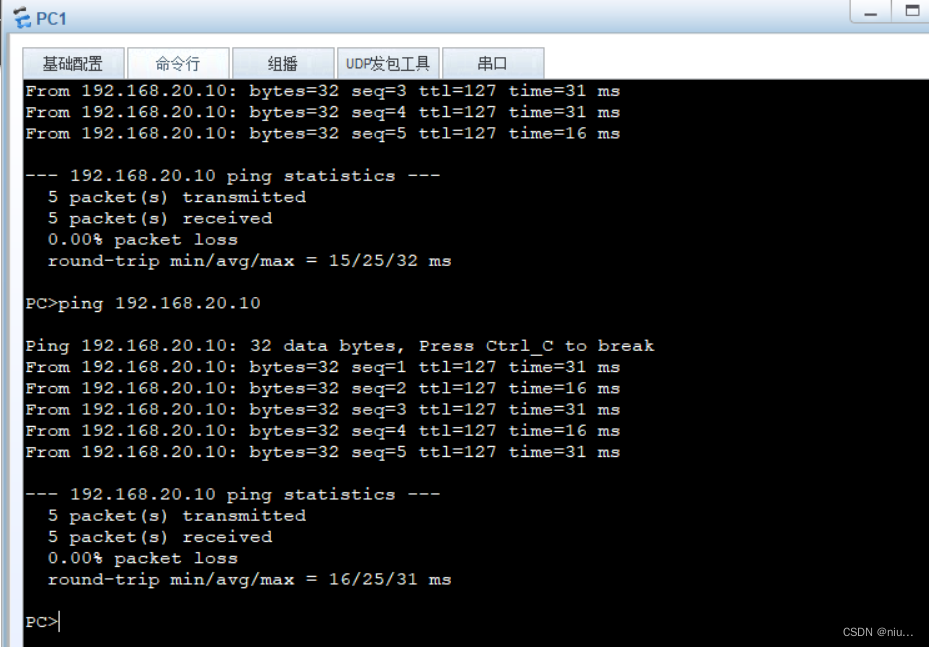
第七步,结果验证。





















 6380
6380











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








