kernel uaf
文章目录
分析
解包得到babydriver.ko文件,
这里其实有点奇怪,关于驱动文件我们要明白,他是常驻内核态的, 我们的程序打开这个文件描述符和读写关闭等操作会转入到这个驱动对应的函数内,我们编写用户态程序进行操作,其实是类似于我们直接去调用这些函数的。其中对应关系,
具体的关系一般要查看 data段的 file_operations, 这里说下一般遇到的常见命名方式。
- open(“driver_name”, flag) => Xopen
- Write => Xwrite
- read => Xread
- Ioctl => Xioctl
- close(fd) => Xrelease
然后载入和卸载驱动会自动调用 init exit两个函数。
漏洞
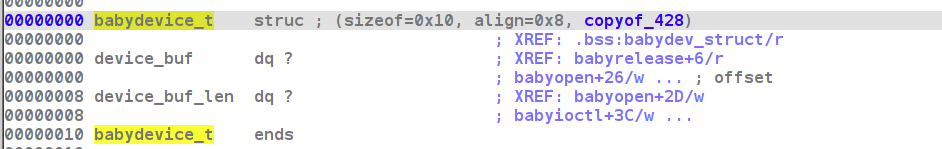
简单分析几个函数, 发现这个驱动主要使用了一个babydevice_t结构体, 其中保存起点和长度,
可以通过read和write进行读写,
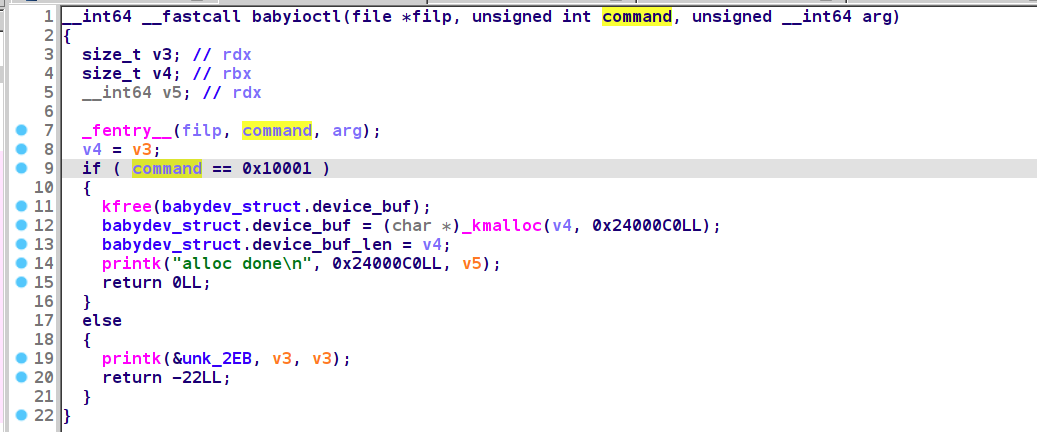
通过ioctl可以实现重设大小,
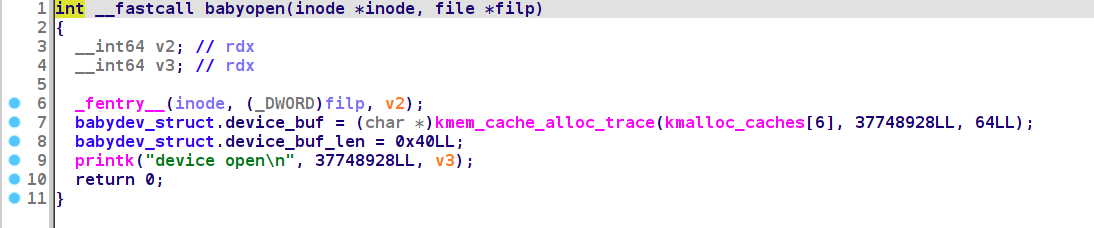
每次open都会设置下这个全局变量。
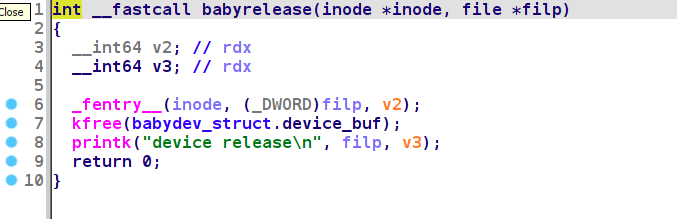
close的时候将这个buf free掉, 但是没有清除全局变量,存在一个uaf
我们可以同时打开两次, 两次共享这个全局变量, 其中一个关闭的时候,通过另一个就可以实现uaf的操作
利用
uaf的利用思路就是堆块再次使用,进行复写。
struct cred
这里介绍一个提权手段,linux下进程的权限管理是通过cred结构体实现的,定义如下:
// include/linux/cred.h
/*
* The security context of a task
*
* The parts of the context break down into two categories:
*
* (1) The objective context of a task. These parts are used when some other
* task is attempting to affect this one.
*
* (2) The subjective context. These details are used when the task is acting
* upon another object, be that a file, a task, a key or whatever.
*
* Note that some members of this structure belong to both categories - the
* LSM security pointer for instance.
*
* A task has two security pointers. task->real_cred points to the objective
* context that defines that task's actual details. The objective part of this
* context is used whenever that task is acted upon.
*
* task->cred points to the subjective context that defines the details of how
* that task is going to act upon another object. This may be overridden
* temporarily to point to another security context, but normally points to the
* same context as task->real_cred.
*/
struct cred {
atomic_t usage;
#ifdef CONFIG_DEBUG_CREDENTIALS
atomic_t subscribers; /* number of processes subscribed */
void *put_addr;
unsigned magic;
#define CRED_MAGIC 0x43736564
#define<







 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 566
566











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








