[root@localhost share]# man strncpy
Formatting page, please wait...
STRCPY(3) Linux Programmer’s Manual STRCPY(3)
NAME
strcpy, strncpy - copy a string
SYNOPSIS
#include <string.h>
char *strcpy(char *dest, const char *src);
char *strncpy(char *dest, const char *src, size_t n);
DESCRIPTION
The strcpy() function copies the string pointed to by src, including
the terminating null byte ('\0'), to the buffer pointed to by dest.
The strings may not overlap, and the destination string dest must be
large enough to receive the copy.
The strncpy() function is similar, except that at most n bytes of src
are copied. Warning: If there is no null byte among the first n bytes
of src, the string placed in dest will not be null terminated.
If the length of src is less than n, strncpy() pads the remainder of
dest with null bytes.
A simple implementation of strncpy() might be:
char*
strncpy(char *dest, const char *src, size_t n){
size_t i;
for (i = 0 ; i < n && src[i] != '\0' ; i++)
dest[i] = src[i];
for ( ; i < n ; i++)
dest[i] = '\0';
return dest;
}
RETURN VALUE
The strcpy() and strncpy() functions return a pointer to the destina-
tion string dest.
CONFORMING TO
SVr4, 4.3BSD, C89, C99.
NOTES
Some programmers consider strncpy() to be inefficient and error prone.
If the programmer knows (i.e., includes code to test!) that the size
of dest is greater than the length of src, then strcpy() can be used.
If there is no terminating null byte in the first n characters of src,
strncpy() produces an unterminated string in dest. Programmers often
prevent this mistake by forcing termination as follows:
strncpy(buf, str, n);
if (n > 0)
buf[n - 1]= '\0';
BUGS
If the destination string of a strcpy() is not large enough, then any-
thing might happen. Overflowing fixed-length string buffers is a
favorite cracker technique for taking complete control of the machine.
Any time a program reads or copies data into a buffer, the program
first needs to check that there’s enough space. This may be unneces-
sary if you can show that overflow is impossible, but be careful: pro-
grams can get changed over time, in ways that may make the impossible
possible.
SEE ALSO
bcopy(3), memccpy(3), memcpy(3), memmove(3), strdup(3), stpcpy(3),
wcscpy(3), wcsncpy(3)
COLOPHON
This page is part of release 3.22 of the Linux man-pages project. A
description of the project, and information about reporting bugs, can
be found at http://www.kernel.org/doc/man-pages/.
GNU 2009-06-01 STRCPY(3)
(END)
BUGS
If the destination string of a strcpy() is not large enough, then any-
thing might happen. Overflowing fixed-length string buffers is a
favorite cracker technique for taking complete control of the machine.
Any time a program reads or copies data into a buffer, the program
first needs to check that there’s enough space. This may be unneces-
sary if you can show that overflow is impossible, but be careful: pro-
grams can get changed over time, in ways that may make the impossible
possible.
SEE ALSO
bcopy(3), memccpy(3), memcpy(3), memmove(3), strdup(3), stpcpy(3),
wcscpy(3), wcsncpy(3)
COLOPHON
This page is part of release 3.22 of the Linux man-pages project. A
description of the project, and information about reporting bugs, can
be found at http://www.kernel.org/doc/man-pages/.
GNU 2009-06-01 STRCPY(3)
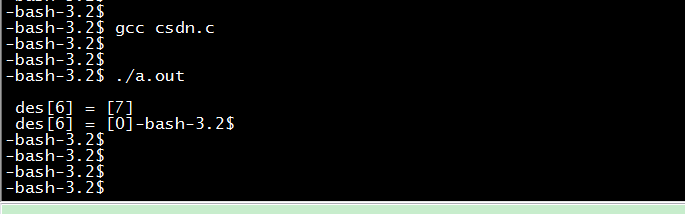
注意:当传入的拷贝长度n大于源数组src的长度时
即 n > ( strlen ( src ) + 1) ,strncpy将会把 目标数组 des 从( strlen ( src ) + 1)到n-1位置置0
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
int main()
{
char des[20]="123456789abcdef";
char src[]= "abc";
printf(" \n des[6] = [%d]",des[6]-'0');
strncpy(des,src,sizeof(des)-1);
printf(" \n des[6] = [%d]",des[6]);
}
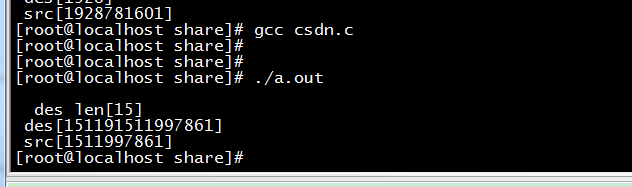
(1)无法保证以0结尾或目标数组溢出的情况。(拷贝异常)
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <time.h>
int main()
{
char src[20];
char des[5];
memset(des,0,sizeof(des));
//void srand (unsigned int seed);
srand( (unsigned int)(time(NULL)) );
snprintf(src,sizeof(src),"%d",rand());
strncpy(des,src,sizeof(des));
printf("\n des len[%d] \n des[%s] \n src[%s] \n",strlen(des),des,src);
return 0;
}
des的长度远远超过了5
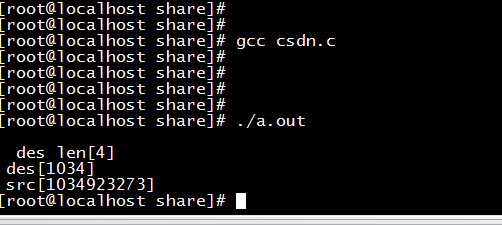
(2)正确用法如下:先memset 0 整个数组,strncpy传入的长度为目标数组最大长度减一。(拷贝正确)
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <time.h>
int main()
{
char src[20];
char des[5];
memset(des,0,sizeof(des));
//void srand (unsigned int seed);
srand( (unsigned int)(time(NULL)) );
snprintf(src,sizeof(src),"%d",rand());
strncpy(des,src,sizeof(des)-1);
printf("\n des len[%d] \n des[%s] \n src[%s] \n",strlen(des),des,src);
return 0;
}
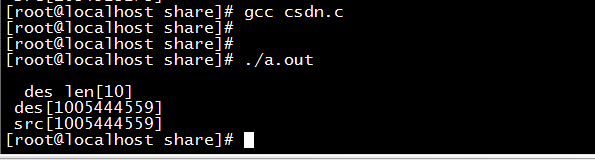
(3)源数组长度较小于目标数组的情况下拷贝,未出现问题。如下des长度5000,src长度20。(拷贝正确)
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <time.h>
int main()
{
char src[20];
char des[5000];
memset(des,0,sizeof(des));
//void srand (unsigned int seed);
srand( (unsigned int)(time(NULL)) );
snprintf(src,sizeof(src),"%d",rand());
strncpy(des,src,sizeof(des)-1);
printf("\n des len[%d] \n des[%s] \n src[%s] \n",strlen(des),des,src);
return 0;
}






















 1601
1601











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








