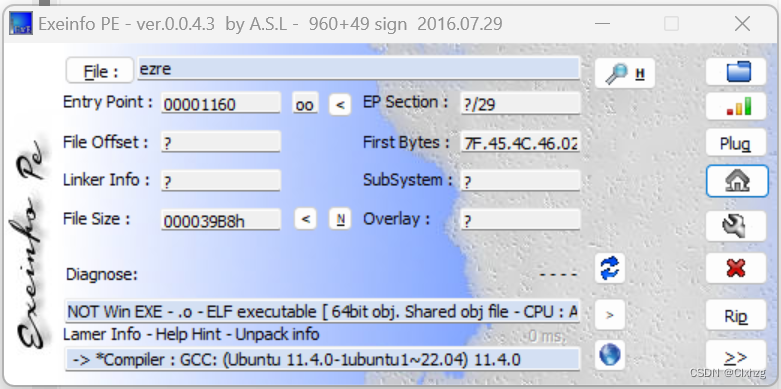
查壳
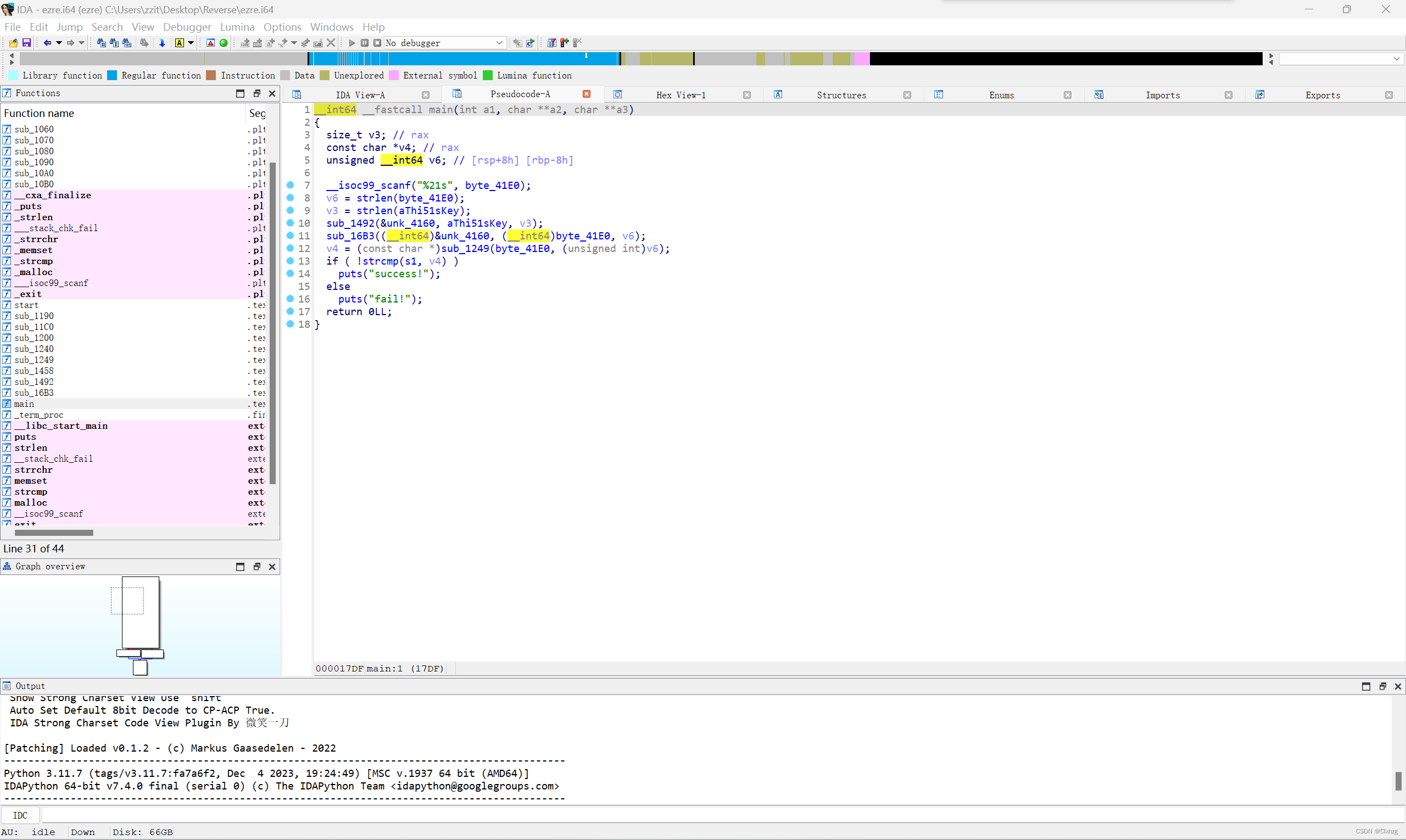
查看ida
完整exp:
import string
import base64
def reverse1():
old_table='ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/='
new_table='0123456789XYZabcdefghijklABCDEFGHIJKLMNOPQRSTUVWmnopqrstuvwxyz+/='
s1='3pn1Ek92hmAEg38EXMn99J9YBf8='
print(base64.b64decode(s1.translate(str.maketrans(new_table,old_table))))
return base64.b64decode(s1.translate(str.maketrans(new_table,old_table)))
def RC4_init(s,aThi51sKey,len):
v8=0
k=[0]*128
for i in range(128):
s[i]=i
k[i]=aThi51sKey[i%len]
for i in range(128):
v8=(v8+s[i]+ord(k







 本文介绍了如何在Python中使用IDA工具和RC4加密算法对字符串进行加密和解密操作,包括`reverse1`函数的逆序处理和`RC4_init`、`cry`函数的加密过程。
本文介绍了如何在Python中使用IDA工具和RC4加密算法对字符串进行加密和解密操作,包括`reverse1`函数的逆序处理和`RC4_init`、`cry`函数的加密过程。
 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章

















 2796
2796

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








