[RE1]P3
int __cdecl aesEncrypt(
const unsigned __int8 *Src,
size_t Size,
unsigned __int8 *a3,
unsigned __int8 *a4,
unsigned int a5)
{
char v6[356]; // [esp+1Ch] [ebp-1ACh] BYREF
unsigned __int8 v7[4]; // [esp+180h] [ebp-48h] BYREF
int v8; // [esp+184h] [ebp-44h]
int v9; // [esp+188h] [ebp-40h]
int v10; // [esp+18Ch] [ebp-3Ch]
int v11[8]; // [esp+190h] [ebp-38h] BYREF
int j; // [esp+1B0h] [ebp-18h]
unsigned int i; // [esp+1B4h] [ebp-14h]
unsigned int *v14; // [esp+1B8h] [ebp-10h]
unsigned __int8 *v15; // [esp+1BCh] [ebp-Ch]
v15 = a4;
v14 = (unsigned int *)v6;
memset(v11, 0, sizeof(v11));
*(_DWORD *)v7 = 0;
v8 = 0;
v9 = 0;
v10 = 0;
if ( Src && a3 && a4 )
{
if ( Size <= 0x10 )
{
if ( (a5 & 0xF) != 0 )
{
puts("inLen is invalid.");
return -1;
}
else
{
memcpy(v11, Src, Size);
keyExpansion(v11, 16, v6);
for ( i = 0; i < a5; i += 16 )
{
loadStateArray((unsigned __int8 (*)[4])v7, a3);
addRoundKey((unsigned __int8 (*)[4])v7, v14);
for ( j = 1; j <= 9; ++j )
{
v14 += 4;
subBytes((unsigned __int8 (*)[4])v7);
shiftRows((unsigned __int8 (*)[4])v7);
mixColumns((unsigned __int8 (*)[4])v7);
addRoundKey((unsigned __int8 (*)[4])v7, v14);
}
subBytes((unsigned __int8 (*)[4])v7);
shiftRows((unsigned __int8 (*)[4])v7);
addRoundKey((unsigned __int8 (*)[4])v7, v14 + 4);
storeStateArray((unsigned __int8 (*)[4])v7, v15);
v15 += 16;
a3 += 16;
v14 = (unsigned int *)v6;
}
return 0;
}
}
else
{
puts("keyLen must be 16.");
return -1;
}
}
else
{
puts("param err.");
return -1;
}
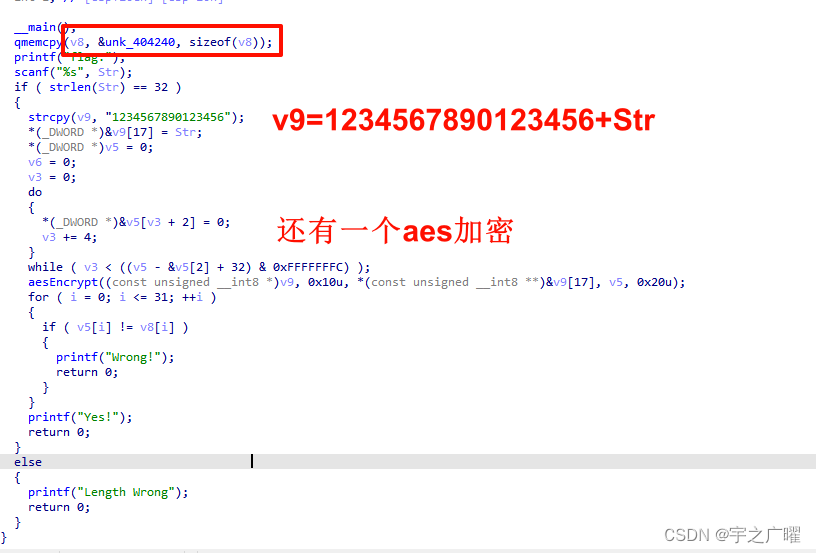
}得到密文:
F3498AED82CE44E2357C23F5DCF897A43B6A7BFEE467C591E31CBC38F99913 strcpy((char *)key, “1234567890123456”)此处可知加密的key,并知道其长度为16位,根据AES加密的特征可以计算循环加密轮次,16X8=128比特,即10轮
然后向下找到aes加密的函数aesEncrypt(key, 0x10u, v10, (uint8_t *)ct, 0x20u);,双击跟进,在for ( j = 1; j <= 9; ++j )处印证猜想
识别AES
- 密钥扩展–>轮密钥生成–>字节替换、行移位–>列替换和轮密钥加
密钥长度和轮数的对应
- 128bits–>10rounds
- 192bits–>12rounds
- 256bits–>14rounds
在kali中可以运行Crypto库
from Crypto.Cipher import AES
def aes_decrypt(key_str, ciphertext_hex):
# 将16进制字符串转换为字节序列
ciphertext_bytes = bytes.fromhex(ciphertext_hex)
# 将字符串密钥转换为字节序列
key = key_str.encode('utf-8')
# 创建AES解密器
cipher = AES.new(key, AES.MODE_ECB)
# 解密
decrypted_data = cipher.decrypt(ciphertext_bytes)
print(decrypted_data)
# 示例
key_str = '1234567890123456'
ciphertext_hex = 'F3498AED82CE44E2357C23F5DCF897A43B6A7BFEE0467C591E301CBC38F99913'
plaintext_hex_result = aes_decrypt(key_str, ciphertext_hex)
[RE1]P9
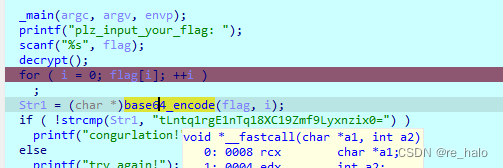
简单python解包+rot13
def caesar_cipher(text, shift):
result = ""
for char in text:
if char.isalpha(): #检测字符串是否只有字母,是则true
start = ord("A") if char.isupper() else ord("a") #是否是大写
result += chr((ord(char) - start + shift) % 26 + start)
else:
result += char
return result
def main():
flag = input("plz_input_your_flag:")
shift = 3
encrypted_text = caesar_cipher(flag, shift)
if encrypted_text == "QVVFWI{s9wkrq_Uh_1v_q0w_edG}":
print("congrulations!")
else:
print("wrong")
if __name__ == "__main__":
main()[RE1]P4
加了一个反调试函数,但不影响直接异或回去就行了。

可以jz改jnz,或者修改zf寄存器
也可以直接nop
还有断点(停止和跟踪(内嵌脚本,可以跟踪寄存器或某个变量值变化))
exp:
auto edx =GetRegValue("EDX");
Message("%c",edx&0xff);
//跟踪edx的idc脚本 

[RE1]P5
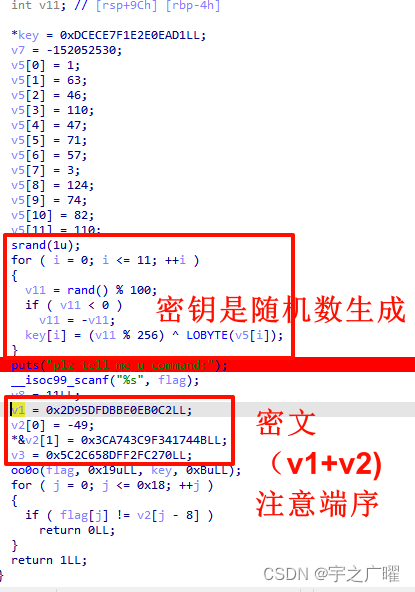
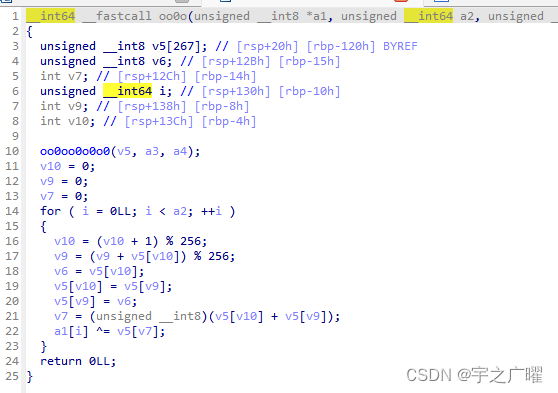
这个应该是rc4加密吧

那就找密文和密钥
对称加密,可以通过密文直接得到明文。
输入字符串后可以直接修改成密文,然后运行。
[RE9]P9

都异或了0x90好像
0xF1, 0xF2, 0xF3, 0xF4, 0xF5, 0xF6, 0xF7, 0xF8, 0xF9, 0xFA,
0xFB, 0xFC, 0xFD, 0xFE, 0xFF, 0xE0, 0xE1, 0xE2, 0xE3, 0xE4,
0xE5, 0xE6, 0xE7, 0xE8, 0xE9, 0xEA, 0xD1, 0xD2, 0xD3, 0xD4,
0xD5, 0xD6, 0xD7, 0xD8, 0xD9, 0xDA, 0xDB, 0xDC, 0xDD, 0xDE,
0xDF, 0xC0, 0xC1, 0xC2, 0xC3, 0xC4, 0xC5, 0xC6, 0xC7, 0xC8,
0xC9, 0xCA, 0xA0, 0xA1, 0xA2, 0xA3, 0xA4, 0xA5, 0xA6, 0xA7,
0xA8, 0xA9, 0xBB, 0xBF, 0xAD直接得到abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789+/=
对的,直接秒了。
但还是试试smc调试
也已经恢复了
试试写内嵌脚本的方法

还有可以通过输入输出判断加密方式是否魔改
[RE10]P10
upx想着手动脱壳,发现没有pushad和popad,看看怎么搞


记一次UPX的脱壳经历的问题和解决 - zpchcbd - 博客园 (cnblogs.com)
进入函数发现smc加密
之后可能还是数据形式 ,需要重定义。
发现是一个简单tea加密。

#include <stdint.h>
#include <stdio.h>
#include <string.h>
void decrypt(uint32_t v[2], uint32_t key[4]) {
uint32_t v0 = v[0], v1 = v[1], sum = 0xC6EF3720, i;
uint32_t delta = 0x9e3779b9;
for (i = 0; i < 32; i++) {
v1 -= ((v0 << 4) + key[2]) ^ (v0 + sum) ^ ((v0 >> 5) + key[3]);
v0 -= ((v1 << 4) + key[0]) ^ (v1 + sum) ^ ((v1 >> 5) + key[1]);
sum -= delta;
}
v[0] = v0;
v[1] = v1;
}
int main() {
uint32_t ciphertext[6] = {0x52286ECB,0x5A1EC44F,0xF284265E,0xF967E7D6,0x46dd0938,0x0a6950d3}; //密文位置
uint32_t key[4] = {0x01234567, 0x89ABCDEF, 0xFEDCBA98, 0x76543210};//key
for(int i = 0; i < 3; i++){
uint32_t temp[2] = {ciphertext[i*2],ciphertext[i*2+1]};
decrypt(temp, key);
printf("Decrypted String: %s\n", (char *)temp);
}
return 0;
}





















 170
170











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








