题目描述
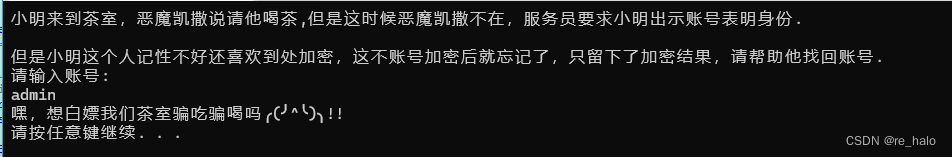
魔鬼凯撒请小明去RC4茶室喝茶,但是凯撒不在。小明需要用账号表明身份,但是他健忘,需要你帮助他验明身份,同时需要你帮助他解密出他的支付密码。
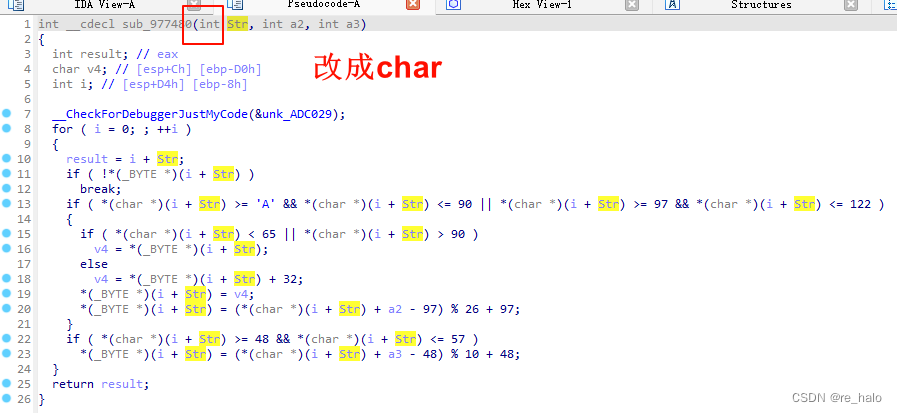
str = 'z8layn_b91_nb9ha1}'
str = list(str)
for i in range(len(str)):
if '0' <= str[i] <= '9':
str[i] = chr((ord(str[i]) - ord('0') - 8) % 10 + ord('0'))
elif 'A' <= str[i] <= 'Z' or 'a' <= str[i] <= 'z':
if 'a' <= str[i] <= 'z':
str[i] = chr((ord(str[i]) - ord('a') - 20) % 26 + ord('a'))
else:
str[i] = chr((ord(str[i]) - ord('A') - 20) % 26 + ord('A'))
print(''.join(str))
# f0rget_h13_th1ng3}
int __cdecl sub_976DB0(char *Str)
{
int m; // [esp+610h] [ebp-300CCh]
char v3[65556]; // [esp+61Ch] [ebp-300C0h] BYREF
FILE *v4; // [esp+10630h] [ebp-200ACh]
int k; // [esp+1063Ch] [ebp-200A0h]
char v6[65556]; // [esp+10648h] [ebp-20094h] BYREF
FILE *v7; // [esp+2065Ch] [ebp-10080h]
int j; // [esp+20668h] [ebp-10074h]
char FileName[65547]; // [esp+20674h] [ebp-10068h] BYREF
char v10; // [esp+3067Fh] [ebp-5Dh]
FILE *Stream; // [esp+30688h] [ebp-54h]
int v12; // [esp+30694h] [ebp-48h]
int i; // [esp+306A0h] [ebp-3Ch]
int v14; // [esp+306ACh] [ebp-30h]
int v15[8]; // [esp+306B8h] [ebp-24h] BYREF
__CheckForDebuggerJustMyCode(&unk_2EC029);
v15[0] = 5;
v15[1] = 2;
v15[2] = 0;
v15[3] = 1;
v15[4] = 3;
v15[5] = 1;
v15[6] = 4;
v14 = j__strlen(Str);
sub_17FBB3(); // init S
sub_182B5B(); // ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789填充hhh数组
sub_17FE0B();
sub_17F7EE(Str, v14); // 应该是 RC4
print(&asc_249EA0);
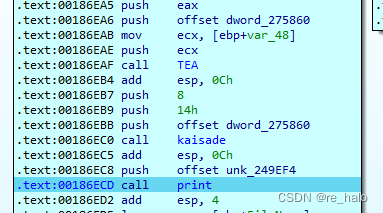
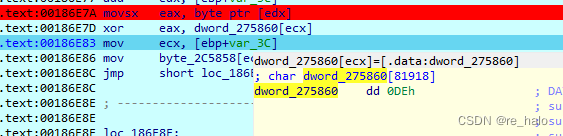
for ( i = 0; i < v14; ++i )
byte_2C5858[i] = LOBYTE(dword_275860[0]) ^ Str[i];
print(&asc_249EC8);
v12 = 64;
TEAde(64, dword_275860, v15);
kaisade((int)dword_275860, 20, 8);
print(&asc_249EF4);
scanf("%s", FileName);
Stream = j__fopen(FileName, "w+");
if ( !Stream )
{
print(&asc_249F18);
j___loaddll(0);
}
v10 = byte_2C5858[0];
v10 = j__getchar();
for ( j = 0; j < v14; ++j )
{
j__fputc(v10, Stream);
v10 = byte_2C5859[j];
}
j__fclose(Stream);
print(&asc_249F2C);
scanf("%s", v6);
v7 = j__fopen(v6, "w+");
if ( !v7 )
{
print(&asc_249F18);
j___loaddll(0);
}
v6[65547] = j__getchar();
for ( k = 0; k < 1; ++k )
guess(v7, "%d", dword_275860[0]);
j__fclose(v7);
print(&asc_249F54);
scanf("%s", v3);
v4 = j__fopen(v3, "w+");
if ( !v4 )
{
print(&asc_249F18);
j___loaddll(0);
}
v3[65547] = j__getchar();
for ( m = 0; m < 1; ++m )
guess(v4, "%d", dword_275860[1]);
return j__fclose(v4);
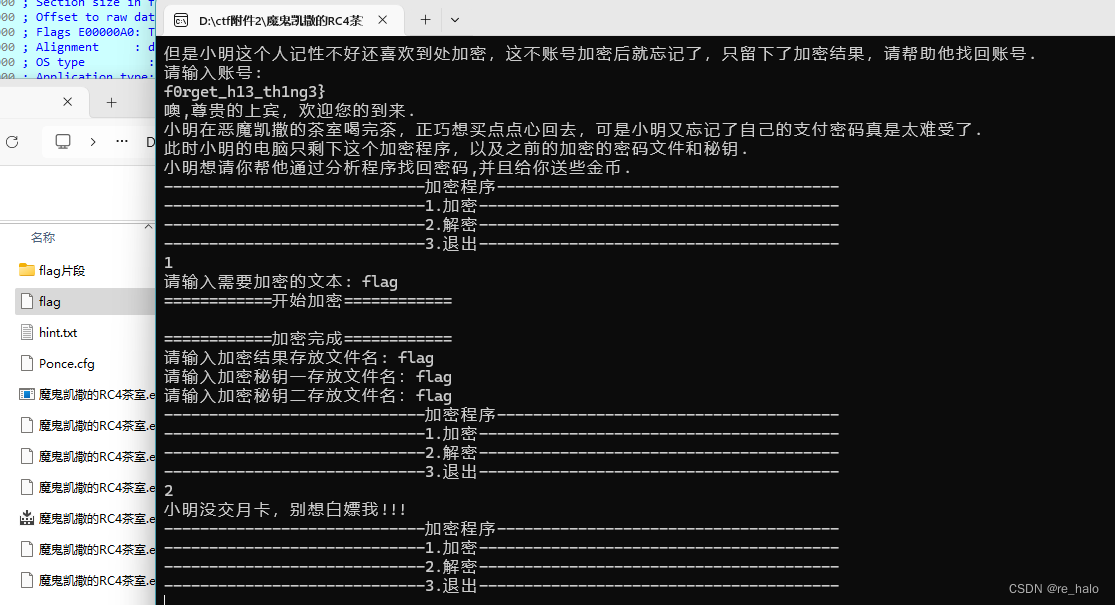
}发现了 RC4 , TEA , 凯撒 加密
嗯,密文应该就是在flag片段的flag中,确实也没看到key的信息
看了wp:好像这几个加密不重要,直接动调
也执行了啊,不知道为什么不重要。
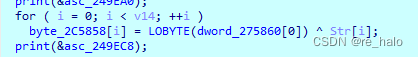
穷举得到异或的字节为0xde
f = open(r"D:\ctf附件2\魔鬼凯撒的RC4茶室\flag片段\flag", 'rb')
flag_encode = f.read()
flag1 = ''
for x in flag_encode:
flag1 += chr(x ^ 0xde)
print(flag1)
f.close()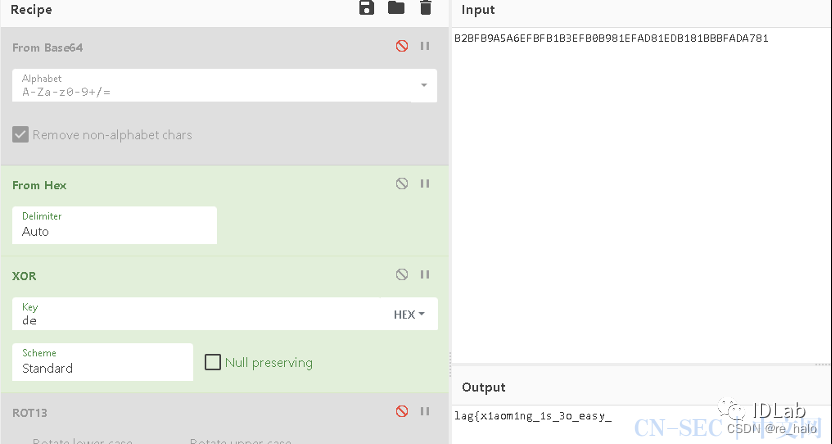
我不知道他从哪里提取的数据,还有个大佬直接爆破的。





















 860
860

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








