实验要求:

各个路由配置
r1配置显示:
interface GigabitEthernet0/0/0
ip address 100.1.1.1 255.255.255.0
#
interface GigabitEthernet0/0/1
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
interface LoopBack0
ip address 192.168.0.1 255.255.255.255
#
interface LoopBack1
ip address 192.168.1.1 255.255.255.255
#
rip 1
undo summary
version 2
network 100.0.0.0
network 192.168.0.0
network 192.168.1.0
#
user-interface con 0
authentication-mode password
user-interface vty 0 4
user-interface vty 16 20
#
wlan ac
#
return
r2所有配置
sysname r2
#
snmp-agent local-engineid 800007DB03000000000000
snmp-agent
#
clock timezone China-Standard-Time minus 08:00:00
#
portal local-server load portalpage.zip
#
drop illegal-mac alarm
#
set cpu-usage threshold 80 restore 75
#
acl number 2000
rule 5 deny source 192.168.4.0 0.0.1.255
rule 10 permit
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password cipher %$%$K8m.Nt84DZ}e#<0`8bmE3Uw}%$%$
local-user admin service-type http
#
firewall zone Local
priority 15
#
interface GigabitEthernet0/0/0
ip address 100.1.1.1 255.255.255.0
#
interface GigabitEthernet0/0/1
ip address 100.2.2.1 255.255.255.0
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
interface LoopBack0
ip address 192.168.0.1 255.255.255.255
#
interface LoopBack1
ip address 192.168.1.1 255.255.255.255
#
ospf 1 router-id 2.2.2.2
import-route rip 1
area 0.0.0.0
network 100.2.2.0 0.0.0.255
#
rip 1
undo summary
version 2
network 100.0.0.0
network 192.168.0.0
network 192.168.1.0
silent-interface GigabitEthernet0/0/1
import-route ospf 1 route-policy oinr
#
route-policy oinr permit node 10
if-match acl 2000
#
user-interface con 0
authentication-mode password
set authentication password cipher %$%$qMq`HR'%e14.x86yz|D8,&y;|D>CZ',_]Y*^09!~
QaA#&y>,%$%$
user-interface vty 0 4
user-interface vty 16 20
#
wlan ac
#
return
r3所有配置
sysname r3
#
snmp-agent local-engineid 800007DB03000000000000
snmp-agent
#
clock timezone China-Standard-Time minus 08:00:00
#
portal local-server load portalpage.zip
#
drop illegal-mac alarm
#
set cpu-usage threshold 80 restore 75
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password cipher %$%$K8m.Nt84DZ}e#<0`8bmE3Uw}%$%$
local-user admin service-type http
#
firewall zone Local
priority 15
#
interface GigabitEthernet0/0/0
ip address 100.2.2.3 255.255.255.0
#
interface GigabitEthernet0/0/1
ip address 100.3.3.3 255.255.255.0
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
interface LoopBack0
ip address 192.168.2.1 255.255.255.255
#
interface LoopBack1
ip address 192.168.3.1 255.255.255.255
#
ospf 1 router-id 3.3.3.3
area 0.0.0.0
network 100.2.2.0 0.0.0.255
network 192.168.2.0 0.0.1.255
area 0.0.0.1
network 100.3.3.0 0.0.0.255
#
user-interface con 0
authentication-mode password
user-interface vty 0 4
user-interface vty 16 20
#
wlan ac
#
return
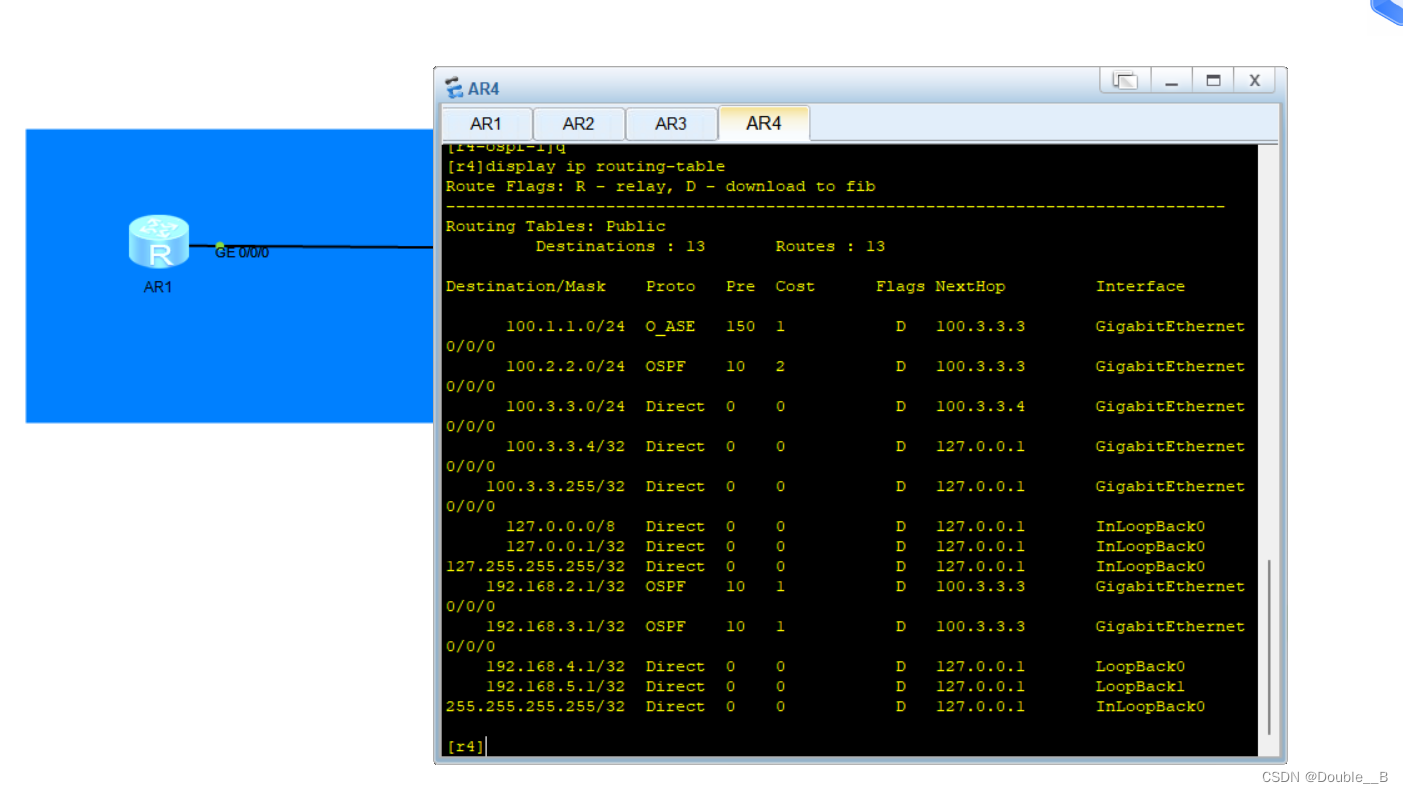
r4所有配置
sysname r4
#
snmp-agent local-engineid 800007DB03000000000000
snmp-agent
#
clock timezone China-Standard-Time minus 08:00:00
#
portal local-server load portalpage.zip
#
drop illegal-mac alarm
#
set cpu-usage threshold 80 restore 75
#
aaa
authentication-scheme default
authorization-scheme default
accounting-scheme default
domain default
domain default_admin
local-user admin password cipher %$%$K8m.Nt84DZ}e#<0`8bmE3Uw}%$%$
local-user admin service-type http
#
firewall zone Local
priority 15
#
interface GigabitEthernet0/0/0
ip address 100.3.3.4 255.255.255.0
#
interface GigabitEthernet0/0/1
#
interface GigabitEthernet0/0/2
#
interface NULL0
#
interface LoopBack0
ip address 192.168.4.1 255.255.255.255
#
interface LoopBack1
ip address 192.168.5.1 255.255.255.255
#
ospf 1 router-id 4.4.4.4
filter-policy ip-prefix rino import
area 0.0.0.0
area 0.0.0.1
network 100.3.3.0 0.0.0.255
network 192.168.4.0 0.0.1.255
#
ip ip-prefix rino index 10 deny 192.168.0.0 23 greater-equal 23 less-equal 32
ip ip-prefix rino index 20 permit 0.0.0.0 0 less-equal 32
#
user-interface con 0
authentication-mode password
user-interface vty 0 4
user-interface vty 16 20
#
wlan ac
#
return
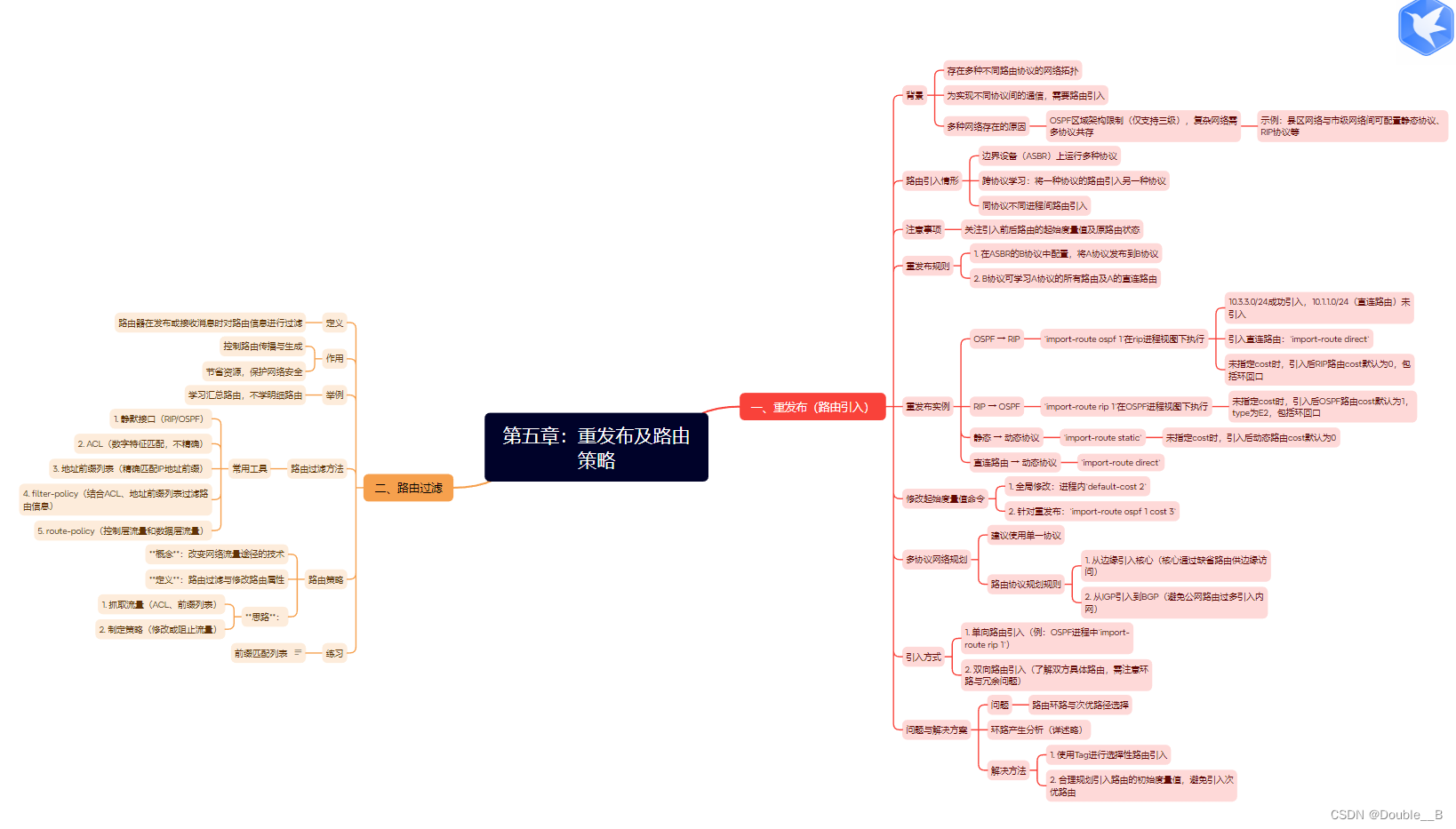
步骤 1:在 R2 上创建 ACL 来匹配 R3 上的业务网段路由,并把其他网段路由过滤掉
步骤 2:在 R2 上创建路由策略,关联 ACL
步骤 3:在 RIP 中引入 OSPF 路由,调用路由策略,只引入 R2 上的业务网段
步骤 4:在 OSPF 中引入 RIP 路由
OSPF 区域中不能出现 RIP 协议报文
r2-rip-1]silent-interface GigabitEthernet 0/0/1
步骤 1:在 R2 上创建 ACL 来匹配 R3 上的业务网段路由,并把其他网段路由过滤掉
步骤 2:在 R2 上创建路由策略,关联 ACL
步骤 3:在 RIP 中引入 OSPF 路由,调用路由策略,只引入 R2 上的业务网段
步骤 4:在 OSPF 中引入 RIP 路由
效果测试:在 R4 上查看路由表,发现已经无法学习到 R1 的业务网段路由





















 559
559











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








