任务六 OSPF路由项欺骗攻击与防御策略
一、任务目的
掌握OSPF路由项欺骗攻击和OSPF源端鉴别的配置方法
二、任务设备、设施
Win10,华为ENSP,WPS
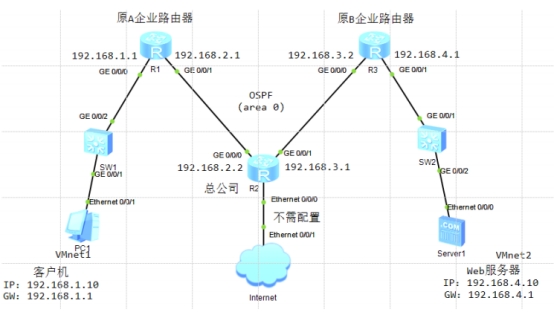
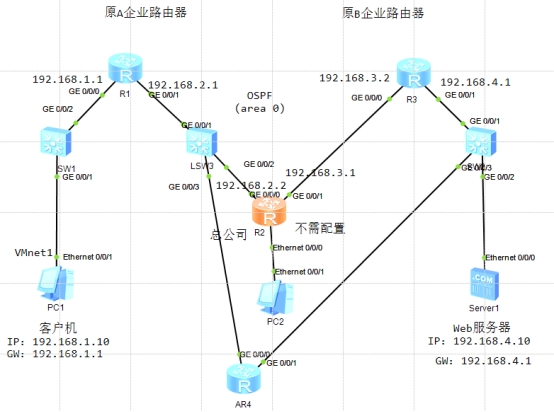
三、任务拓扑结构图
四、基本配置
R1:
<Huawei>sy
Enter system view, return user view with Ctrl+Z.
[Huawei]sy R1
[R1]in g0/0/0
[R1-GigabitEthernet0/0/0]ip ad 192.168.1.1 24
[R1-GigabitEthernet0/0/0]in g0/0/1
[R1-GigabitEthernet0/0/1]ip ad 192.168.2.1 24
[R1-GigabitEthernet0/0/1]q
[R1]ospf 1
[R1-ospf-1]a 0
[R1-ospf-1-area-0.0.0.0]net 192.168.1.0 0.0.0.255
[R1-ospf-1-area-0.0.0.0]net 192.168.2.0 0.0.0.255
R2:
<Huawei>sy
Enter system view, return user view with Ctrl+Z.
[Huawei]sy R2
[R2]in g0/0/0
[R2-GigabitEthernet0/0/0]ip ad 192.168.2.2 24
[R2-GigabitEthernet0/0/0]in g0/0/1
[R2-GigabitEthernet0/0/1]ip ad 192.168.3.1 24
[R2-GigabitEthernet0/0/1]q
[R2]ospf 1
[R2-ospf-1]a 0
[R2-ospf-1-area-0.0.0.0]net 192.168.2.0 0.0.0.255
[R2-ospf-1-area-0.0.0.0]net 192.168.3.0 0.0.0.255
[R2-ospf-1-area-0.0.0.0]dis th
[V200R003C00]
\#
area 0.0.0.0
network 192.168.2.0 0.0.0.255
network 192.168.3.0 0.0.0.255
\#
Return
R3:
<Huawei>sy
Enter system view, return user view with Ctrl+Z.
[Huawei]sy R3
[R3]in g0/0/0
[R3-GigabitEthernet0/0/0]ip ad 192.168.3.2 24
[R3-GigabitEthernet0/0/0]in g0/0/1
[R3-GigabitEthernet0/0/1]ip ad 192.168.4.1 24
[R3-GigabitEthernet0/0/1]q
[R3]ospf 1
[R3-ospf-1]a 0
[R3-ospf-1-area-0.0.0.0]net 192.168.3.0 0.0.0.255
[R3-ospf-1-area-0.0.0.0]net 192.168.4.0 0.0.0.255
[R3-ospf-1-area-0.0.0.0]dis th
[V200R003C00]
\#
area 0.0.0.0
network 192.168.3.0 0.0.0.255
network 192.168.4.0 0.0.0.255
\#
return
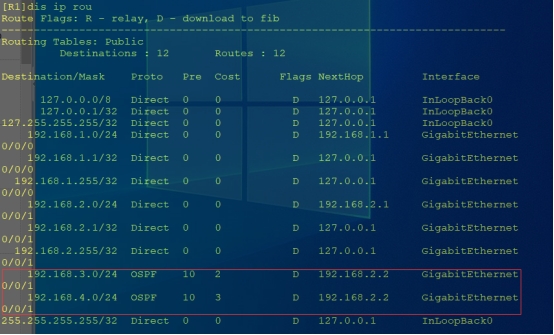
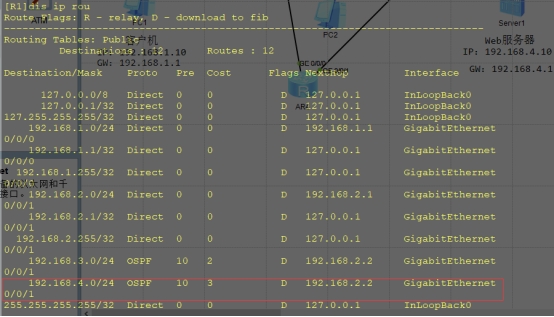
R1路由表:
五、入侵实战
实验拓扑:
R4:
<Huawei>sy
Enter system view, return user view with Ctrl+Z.
[Huawei]sy R4
[R4]in g0/0/0
[R4-GigabitEthernet0/0/0]ip ad 192.168.2.3 24
[R4-GigabitEthernet0/0/0]in g0/0/1
[R4-GigabitEthernet0/0/1]ip ad 192.168.4.1 24
[R4-GigabitEthernet0/0/1]q
[R4]ospf 1
[R4-ospf-1]a 0
[R4-ospf-1-area-0.0.0.0]net 192.168.2.0 0.0.0.255
[R4-ospf-1-area-0.0.0.0]net 192.168.4.0 0.0.0.255
[R4-ospf-1-area-0.0.0.0]q
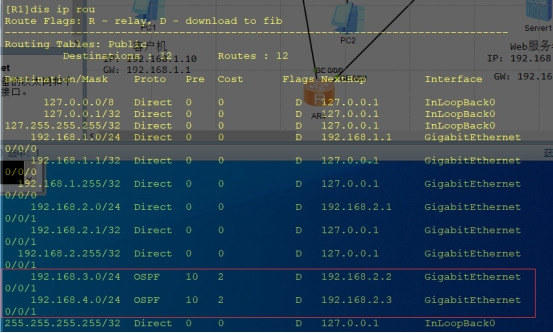
R1:
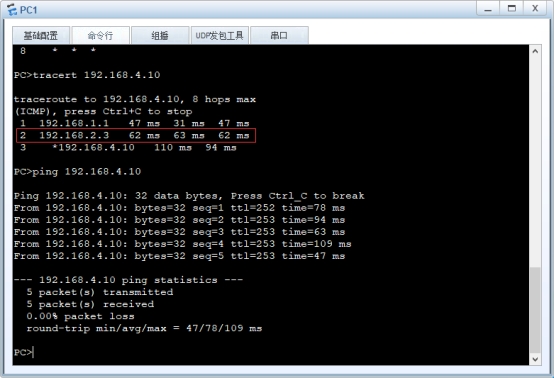
PC1:
R2:

六、防范策略
R1:
[R1]in g0/0/1
[R1-GigabitEthernet0/0/1]ospf authentication-mode hmac-md5 1 cipher huawei
R2:
[R2]in g0/0/0
[R2-GigabitEthernet0/0/0]ospf authentication-mode hmac-md5 1 cipher huawei
[R2-GigabitEthernet0/0/0]in g0/0/1
[R2-GigabitEthernet0/0/1]ospf authentication-mode hmac-md5 2 cipher aaaa
R3:
[R3]in g0/0/1
[R3-GigabitEthernet0/0/1]ospf authentication-mode hmac-md5 1 cipher aaaa
R1路由表:
PC1:

七、任务总结
(1)在配置OSPF路由项远端鉴别时,相邻路由器之间接口必须采用相同的鉴别方式(如Hmac-md5)、相同的鉴别密钥(密钥存储方式可以不同,如cipher或者plain)和相同的密钥标识符,否则不能建立邻居关系
(2)对于交换机SW2而言,去往目的IP地址192.168.4.1时,可能通过GE0/0/1接口(客户机与Web服务器通信时去跟回走不同路径),也可能通过GE0/0/3接口(客户机与Web服务器通信时去跟回走相同路径),由SW2端口映射表更新状态决定,无法人为指定





















 1974
1974











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








