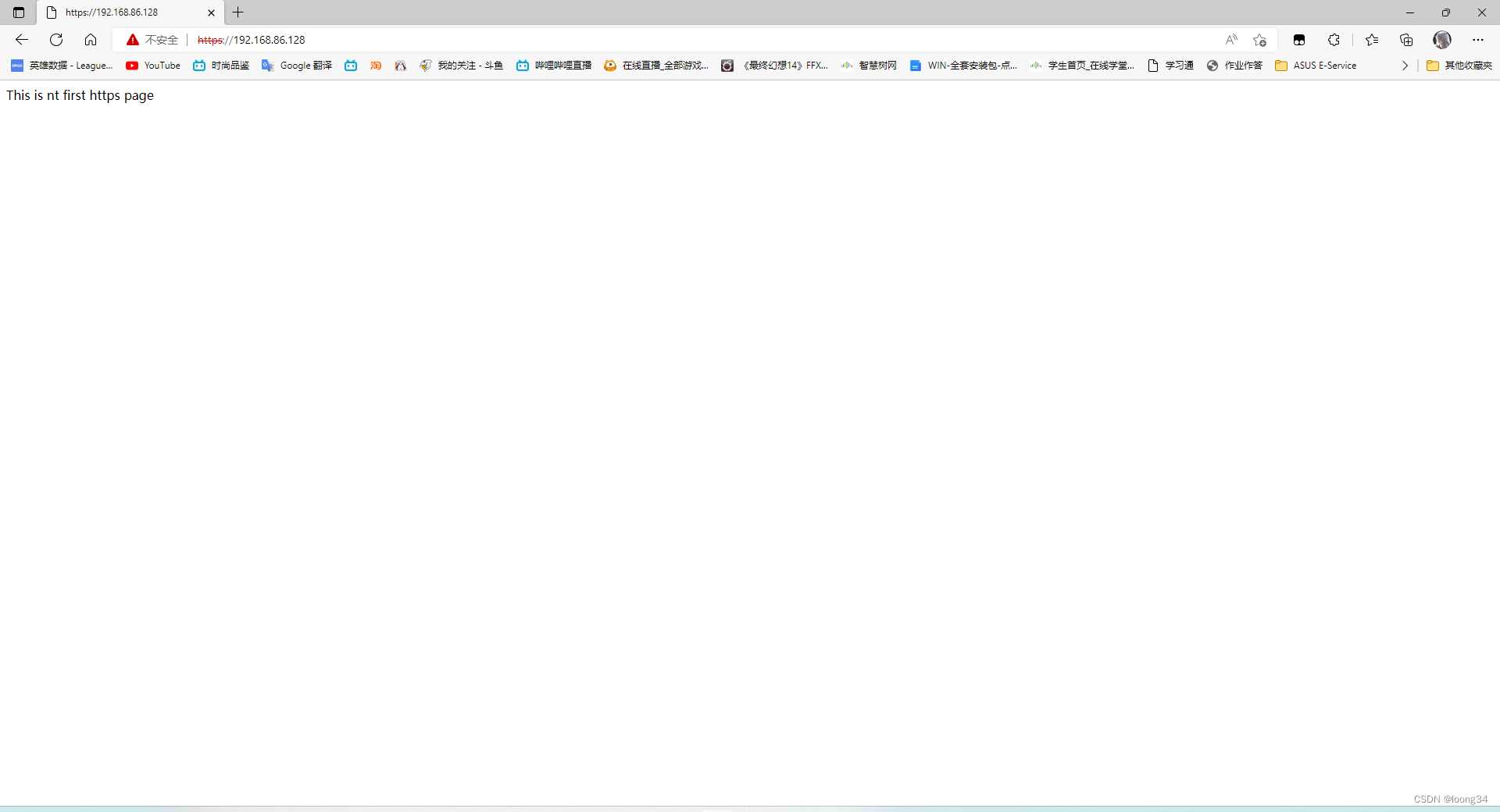
1.配置使用ssl完成https访问apache服务器
yum install mod_ssl -y
echo "This is nt first https page" > /var/www/html/index.html
vim /etc/httpd/conf.d/myhosts.conf
写入
<Directory /var/www/html>
AllowOverride none
Require all granted
</Directory>
<VirtualHost 192.168.86.128:443>
DocumentRoot "/var/www/html"
ServerName 192.168.86.128
SSLEngine on
SSLProtocol all -SSLv2
SSLCipherSuite HIGH:MEDIUM:!aNULL:!MD5:!SEED:!IDEA
SSLCertificateFile /etc/pki/tls/certs/localhost.crt
SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
</VirtualHost>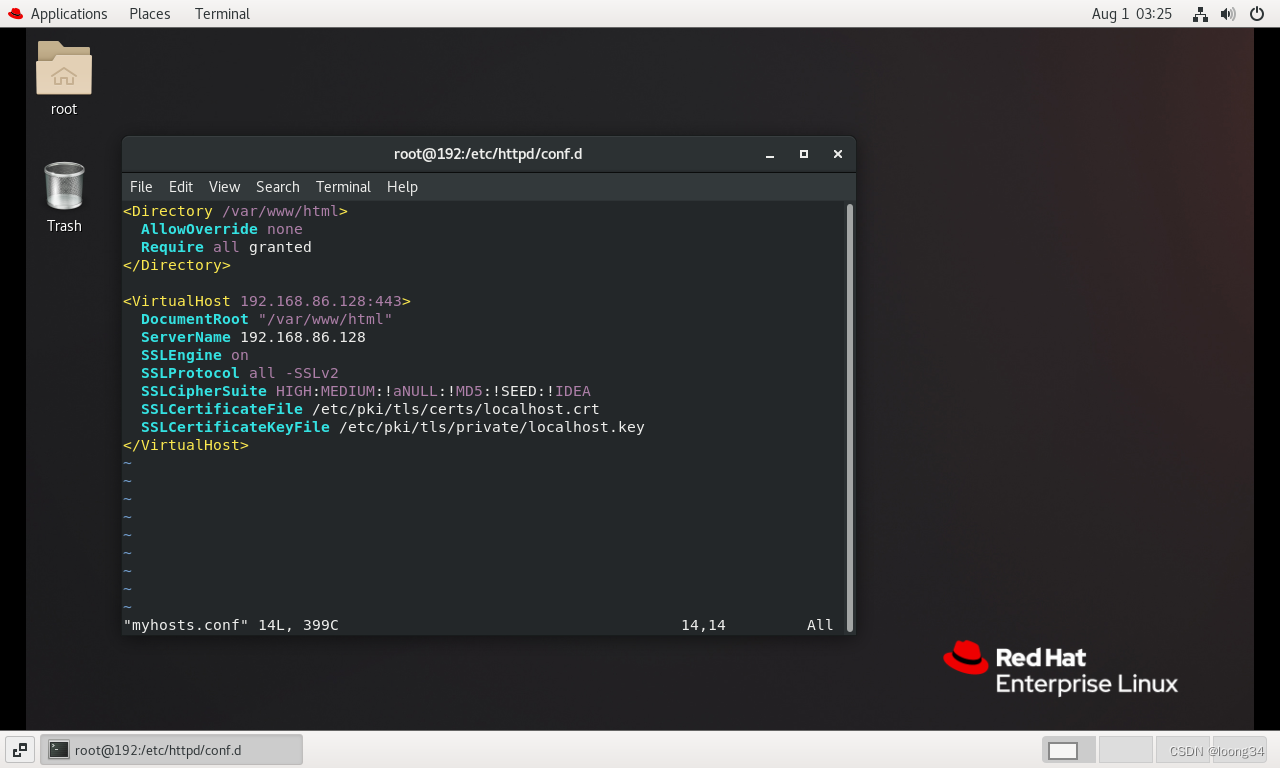
重启httpd服务
systemctl restart httpd
2.配置访问apache的cgi程序
vim /etc/httpd/conf/httpd.conf
配置 AddHandler cgi-script .cgi .pl 这段代码被注释掉了,将注释去掉
vim /var/www/cgi-bin/test.cgi
写入
<Directory /var/www/html>
AllowOverride none
Require all granted
</Directory>
<VirtualHost 192.168.86.128:443>
DocumentRoot "/var/www/html"
ServerName 192.168.86.128
SSLEngine on
SSLProtocol all -SSLv2
SSLCipherSuite HIGH:MEDIUM:!aNULL:!MD5:!SEED:!IDEA
SSLCertificateFile /etc/pki/tls/certs/localhost.crt
SSLCertificateKeyFile /etc/pki/tls/private/localhost.key
</VirtualHost>chmod 755 /var/www/cgi-bin/test.cgi
vim /etc/httpd/conf.d/myhosts.conf
写入
<Directory " /var/www/cgi-bin">
AllowOverride None
options +ExecCGI
AddHandler cgi-script .cgi
Require all granted
</Directory>
Listen 9000
<VirtualHost 192.168.86.128:9000>
DocumentRoot " /var/www/cgi-bin"
ServerName 192.168.86.128
</VirtualHost>systemctl restart httpd

192.168.86.128:9000/cgi-bin/test.cgi
3.nfs挂载
a、开放/nfs/shared目录,供所有用户查询资料
yum install rpcbind -y
yum install nfs-utils -y
systemctl stop firewalld.service
setenforce 0
systemctl start rpcbind
systemctl start nfs-server
mkdir -p /nfs/shared
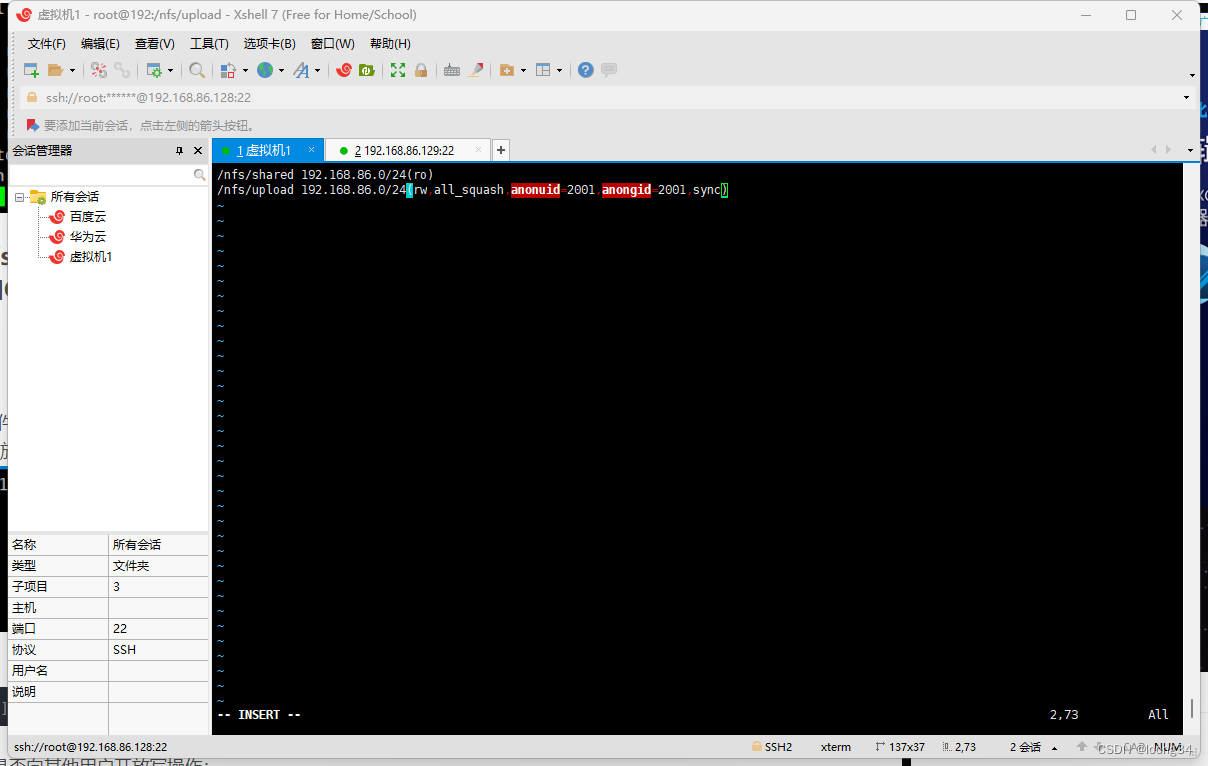
vim /etc/exports
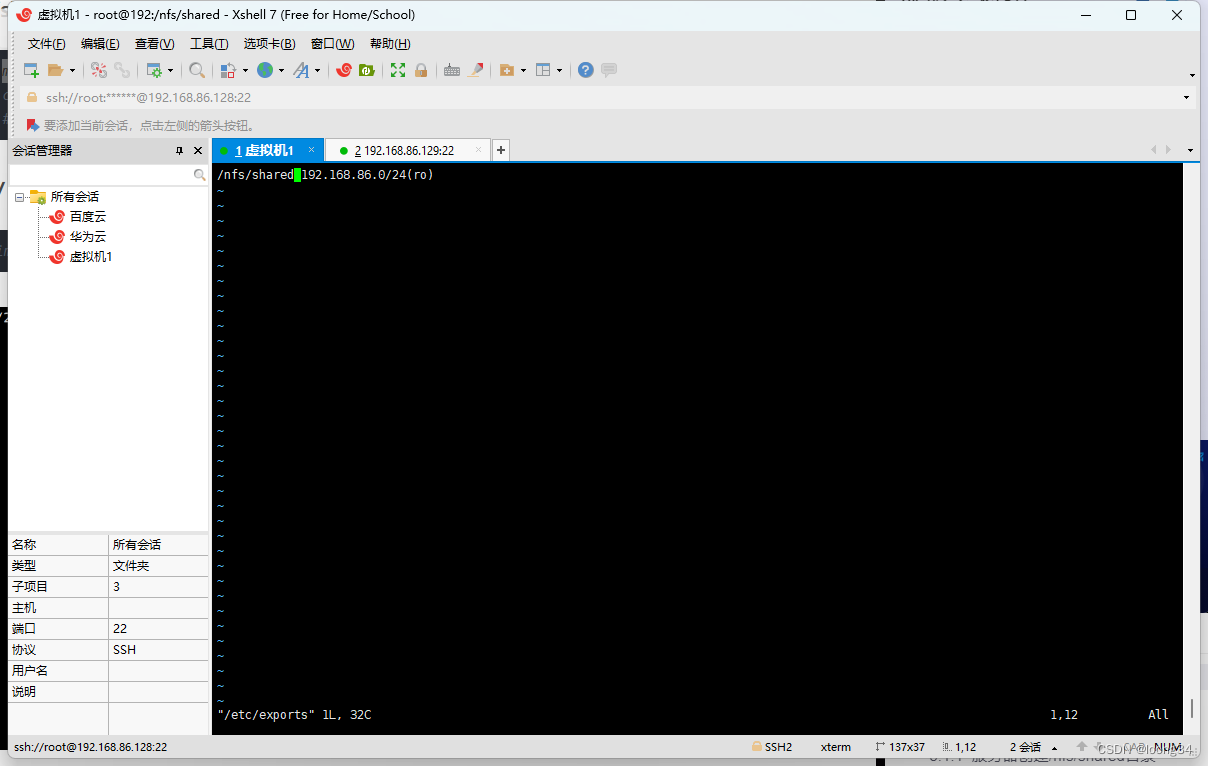
/nfs/shared 192.168.86.0/24(ro)
systemctl restart nfs-server
在客户端进行下面的配置
mkdir -p /client/shuju
服务器检测
showmount -e 192.168.86.128
![]()
客户端检测
showmount -e 192.168.86.128
![]()
客户端挂载
mount 192.168.102.131:/nfs/shared /client/shuju
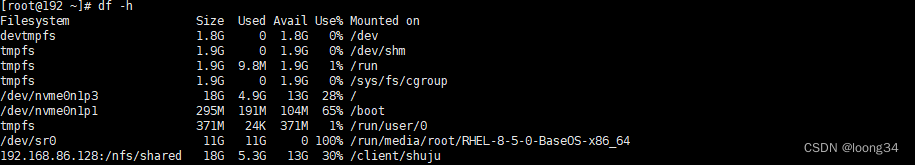
服务器添加内容
![]()
客户端查看内容

b、开放/nfs/upload目录,该目录为192.168.xxx.0/24网段的主机的数据上传目录,
并将所有该网段主机上传文件的所属者和所属组映射为nfs-upload,其UID和GID为2001;
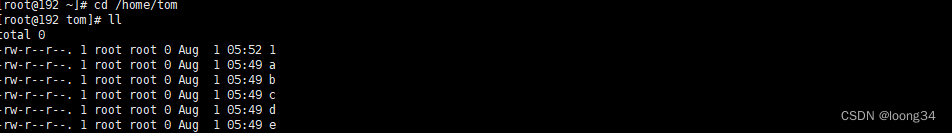
vim /etc/exports
mkdir /nfs/upload -p
chmod o+w /nfs/upload/
添加共享的用户及所属组映射为nfs-upload,其UID和GID均为2001
useradd -u 2001 nfs-upload
groupmod -g 2001 nfs-upload
重启
exportfs -r
客户端
useradd -u 2001 nfs-upload
groupmod -g 2001 nfs-upload
mount 192.168.86.128:/nfs/upload /client/download
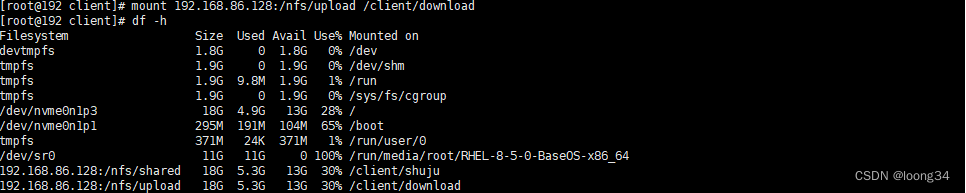
查看文件
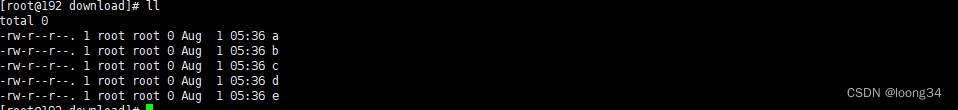
c、将/home/tom(该目录为uid=1111,gid=1111的tom用户的家目录)目录仅共享
给192.168.xxx.129这台主机上的jerry用户,jerry对该目录具有访问、新建和
删除文件的权限。
vim /etc/exports

创建tom用户
useradd -u 1111 tom
touch /home/tom/{a..e}
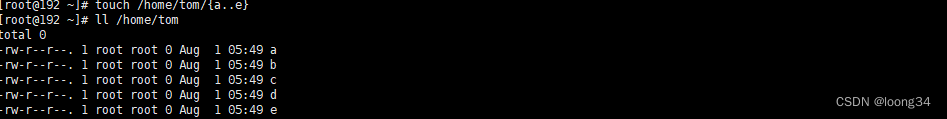
重启exportfs -r
客户端创建jerry用户
useradd -u 1111 jerry
挂载
mount 192.168.86.128:/home/tom /client/user
更改内容
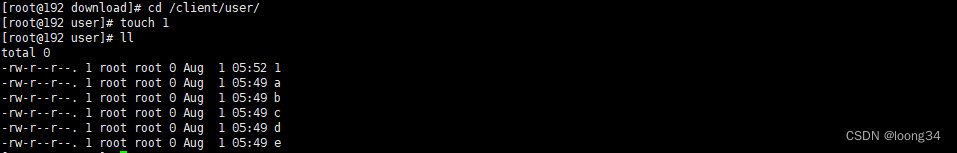
服务器的内容
4.autofs自动挂载
远程nfs服务器要的目录为/nfs/autofs
客户端的的挂载目录/data/autofs
且设置自动卸载时间为60秒
mkdir -p /nfs/autofs
chmod o+w /nfs/autofs
vim /etc/exports
切换到客户端
dnf install -y autofs
mkdir -p /data/autofs
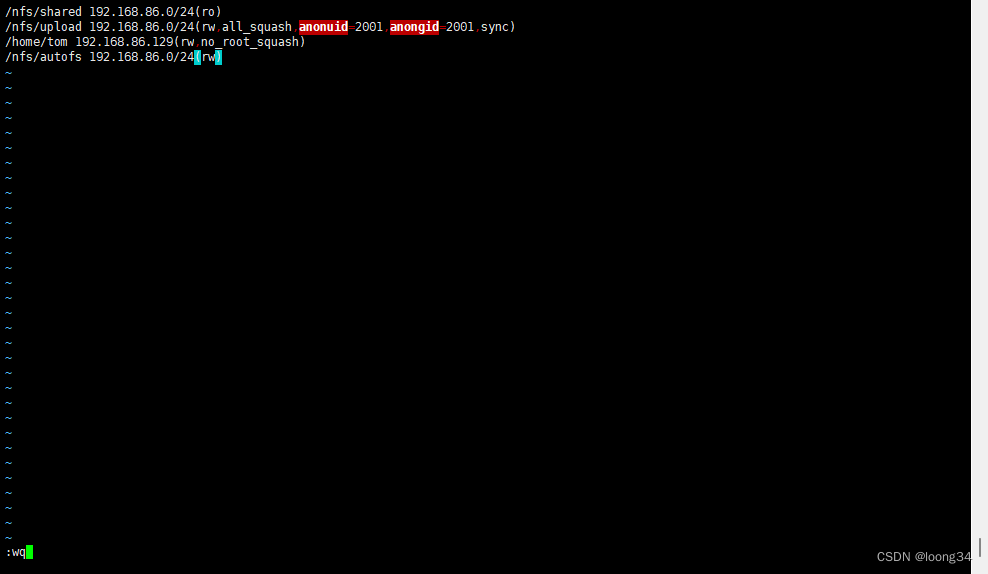
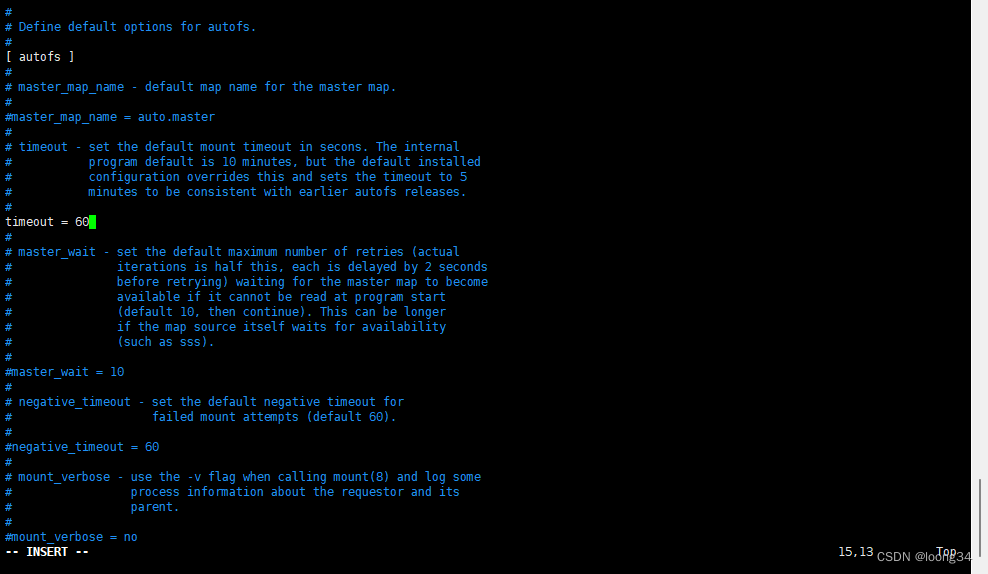
vim /etc/auto.master
vim /etc/auto.data
autofs -fstype=nfs,rw 192.168.86.128:/nfs/autofs

vim /etc/autofs.conf
systemctl restart autofs
5.使用https来访问的web服务器:
要求使用自签名的CA签名证书(openssl, x.509) .crt
以及私钥
自签名CA根证书
/root/ca目录下创建4个子目录:
newcerts:存放CA签署过的数字证书。
private:存放CA的私钥。
conf:存放一些简化参数用的配置文件。
server:存放服务器证书文件。
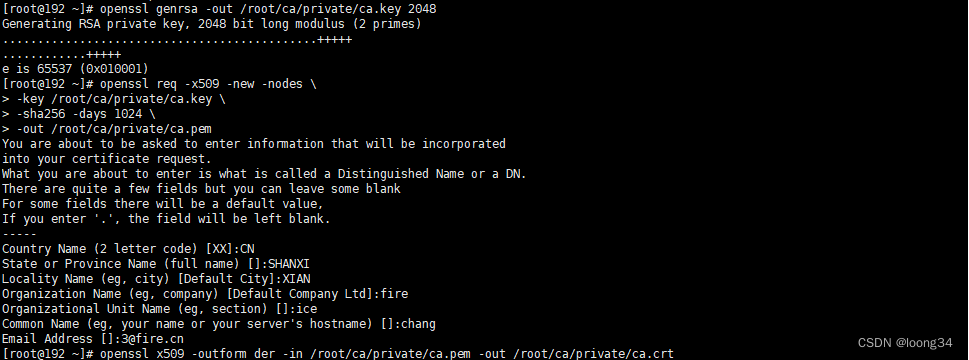
制作ca.key 私钥
openssl genrsa -out /root/ca/private/ca.key 2048
生成pem格式的根证书
openssl req -x509 -new -nodes \
-key /root/ca/private/ca.key \
-sha256 -days 1024 \
-out /root/ca/private/ca.pem
.pem转化为.crt(用于浏览器信任)
openssl x509 -outform der -in /root/ca/private/ca.pem -out /root/ca/private/ca.crt
签发服务器证书(客户端证书同理)
创建文件ca.conf
vim /root/ca/conf/ca.conf 写入
[req]
default_bits = 2048
prompt = no
default_md = sha256
distinguished_name = dn
[dn]
C = CN
ST = SHANXI
L = XIAN
O = fire
OU = ice
emailAddress = 3@fire.cn
CN = *.fire.cn创建文件v3.ext
vim /root/ca/conf/v3.ext
authorityKeyIdentifier=keyid,issuer
basicConstraints=CA:FALSE
keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
subjectAltName = @alt_names
[alt_names]
DNS.1 = *.fire.cn
DNS.2 = localhost
IP.1 = 192.168.86.128
IP.2 = 192.168.86.129生成服务端证书签名请求,同时生成服务端私钥(nginx用)
openssl req -new -sha256 -nodes \
-out /root/ca/server/server.csr \
-newkey rsa:2048 -keyout /root/ca/server/server.key \
-config /root/ca/conf/ca.cnf
用ca私钥以ca的名义(ca.pem)给网站证书签名,加上v3.ext中的配置
openssl x509 -req -in /root/ca/server/server.csr \
-CA /root/ca/private/ca.pem \
-CAkey /root/ca/private/ca.key \
-CAcreateserial -out /root/ca/server/server.crt -days 1800 -sha256 -extfile /root/ca/conf/v3.ext






















 210
210











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








