原理自行百度,我们直接动手
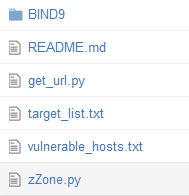
工具
DNS域传送漏洞的验证方式简单粗暴,我简单修改了lijiejie大牛的脚本,做批量:
https://github.com/Xyntax/zZone-Transfer
采集
采集自http://www.qkankan.com
输入为qkankan.com的某栏目url
如下例:国内网站列表
http://www.qkankan.com/guonei/all/
import re
import urllib
"""
url采集脚本
仅适用于此站点的list,自动翻页采集
http://www.qkankan.com/
"""
def getHtml(url):
print "hello cdxy\n\ntesting page 1"
page = urllib.urlopen(url)
html = page.read()
for i in range(2,10000):
page = urllib.urlopen(url+'/index_'+str(i)+'.html')
current_html = page.read()
if 'message.gif' not in current_html:
html+=current_html
print "gathering urls from page:"+str(i)
else:
print "\ntotal_page: "+str(i-1)
break
return html
def getUrl(html):
reg = r'http://(.*?)(/|\"|\')' #正则
urlre = re.compile(reg)
urllist = re.findall(urlre,html)
return urllist
html = getHtml("http://www.qkankan.com/guonei/all/") #地址输入
ans = getUrl(html)
fobj = open('target_list.txt','w') #输出位置
ans_list = []
white_list = ['www.w3.org','www.qkankan.com','m.qkankan.com'] #白名单,不作采集








 最低0.47元/天 解锁文章
最低0.47元/天 解锁文章















 339
339

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








