参考【JS 逆向百例】Fiddler 插件 Hook 实战,某创帮登录逆向
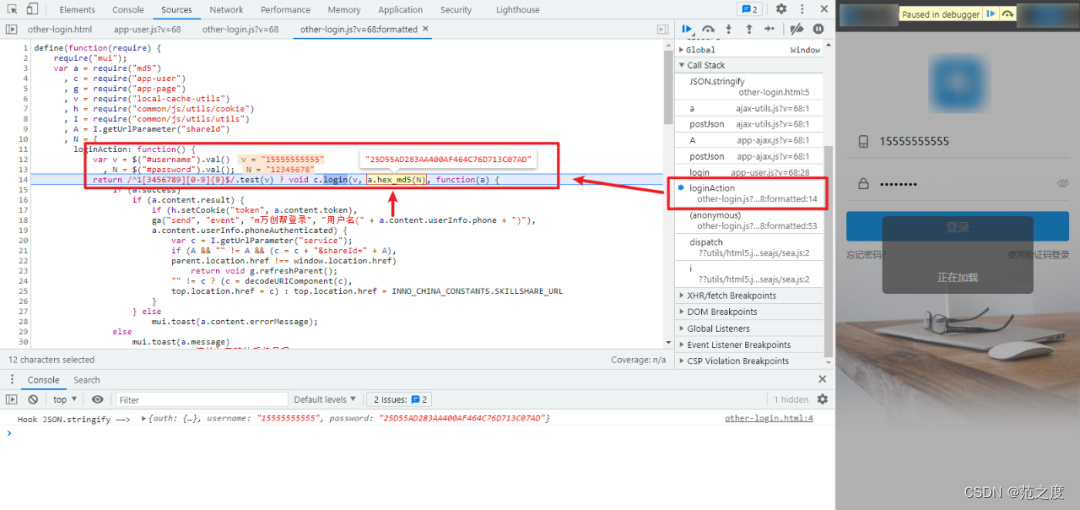
定位密码,用fiddler编程猫工具,在主网站hook,
(function() {
var stringify = JSON.stringify;
JSON.stringify = function(params) {
console.log("Hook JSON.stringify ——> ", params);
debugger;
return stringify(params);
}
})();然后刷新断住,如下图:
导进去将整个js复制下来
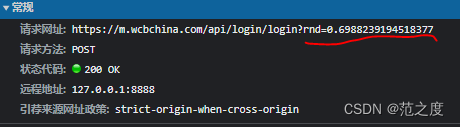
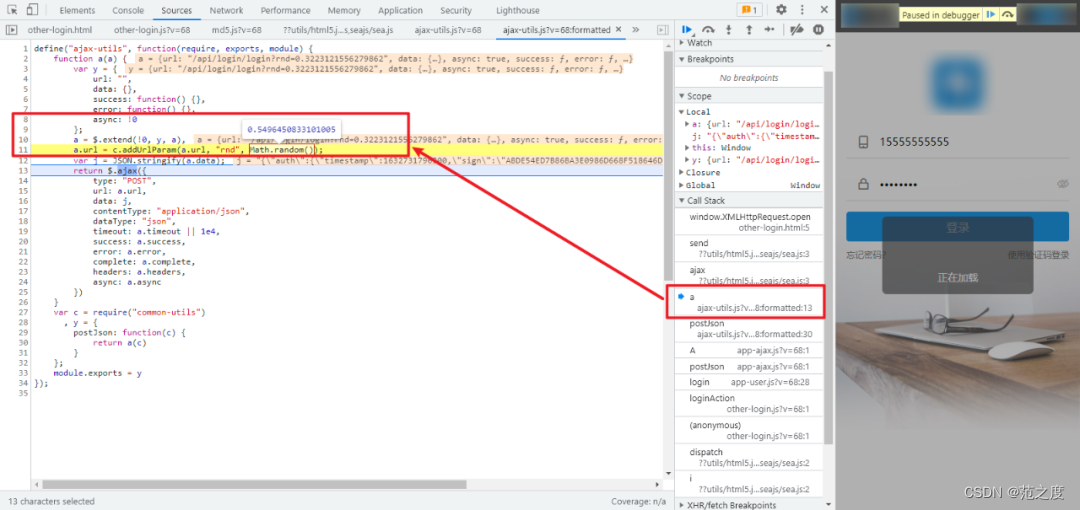
参数rnd,如下:
hook代码如下:
(function () {
var open = window.XMLHttpRequest.prototype.open;
window.XMLHttpRequest.prototype.open = function (method, url, async) {
if (url.indexOf("rnd") != -1) {
debugger;
}
return open.apply(this, arguments);
};
})();断住,跟值如下:
接下来是:timestamp和sign
全局搜索参数断住如下:
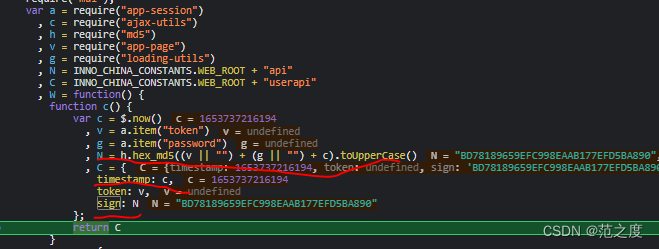
其中timestamp如下:
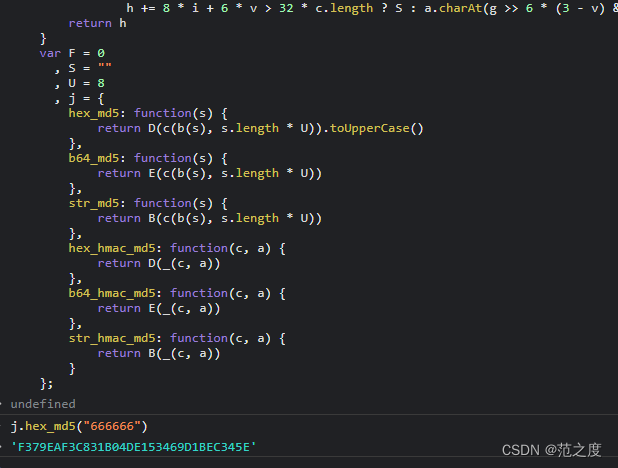
timestamp= (new Date).getTime();sign如下:
h.hex_md5((v || "") + (g || "") + c).toUpperCase()
//v和g未定义可以看成空值。
//简化版如下:
h.hex_md5(c).toUpperCase()md5加密
生成的py文件如下:
import time
import random
import hashlib
import execjs
import requests
login_url = '脱敏处理,完整代码关注 GitHub:https://github.com/kgepachong/crawler'
def get_enpwd_and_sign_by_javascript(password):
with open('encrypt.js', 'r', encoding='utf-8') as f:
encrypt_js = execjs.compile(f.read())
encrypted_password = encrypt_js.call('getdata', password)
sign = encrypt_js.call('getsign')
return encrypted_password, sign
def get_rnd():
rnd = 'rnd' + str(random.uniform(0, 1))
return rnd
def login(username, encrypted_password, sign, rnd):
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/91.0.4472.124 Safari/537.36'
}
json = {
"auth": {
"timestamp": str(int(time.time() * 1000)),
"sign": sign
},
"username": username,
"password": encrypted_password
}
response = requests.post(url=login_url, params=rnd, json=json, headers=headers)
print(response.json())
if __name__ == '__main__':
main()






















 1680
1680











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








