申请虚拟靶机,获取目标IP地址
Task1
What does the acronym SQL stand for?
Structured Query Language
Task2
What is one of the most common type of SQL vulnerabilities?
SQL Injection
Task3
What does PII stand for?
Personally Identifiable Information
Task4
What does the OWASP Top 10 list name the classification for this vulnerability?
查了一下
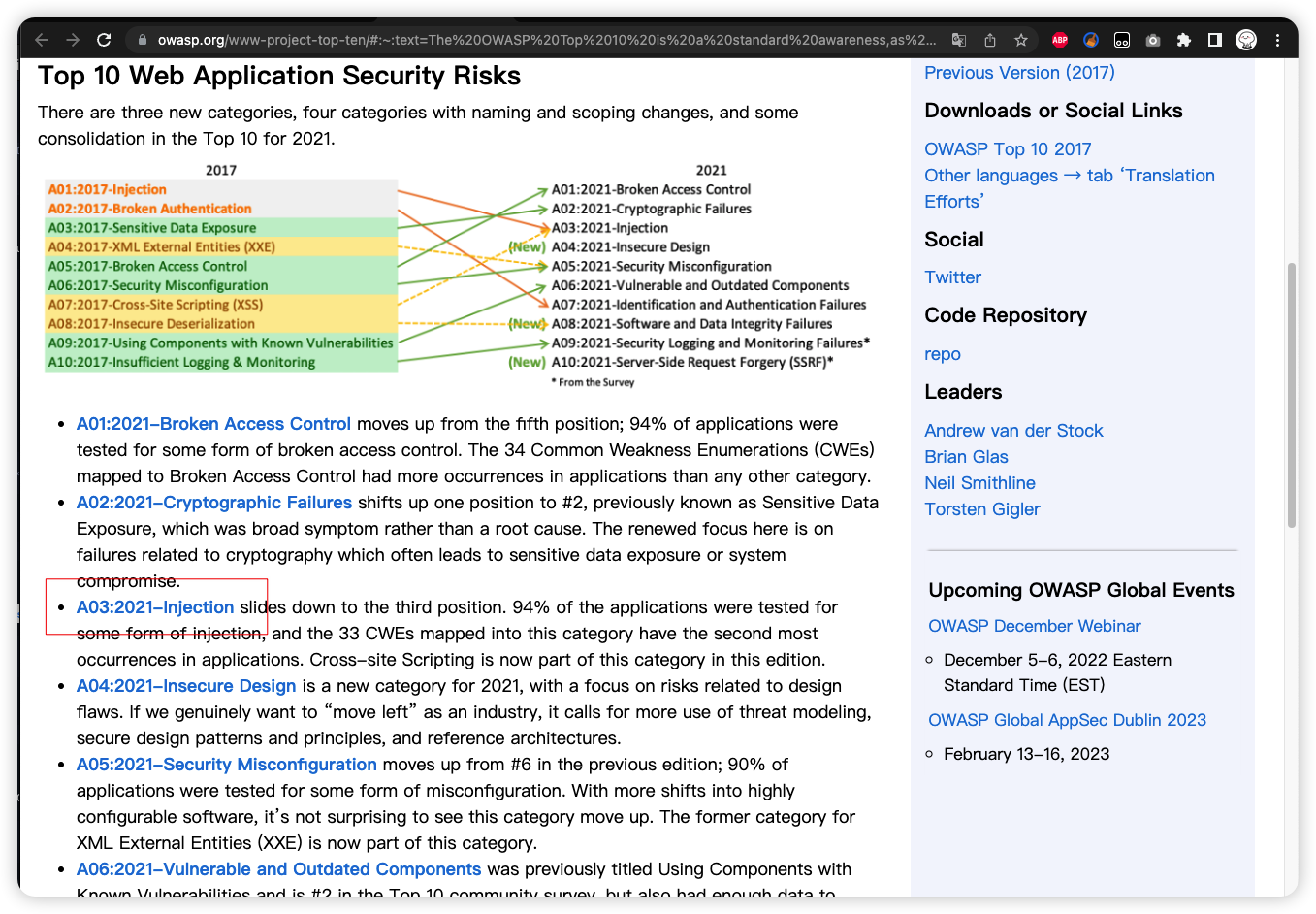
A03:2021-Injection
Task5
What service and version are running on port 80 of the target?
nmap扫一下靶机,可以看到80端口有apache服务。

Apache httpd 2.4.38 ((Debian))
Task6
What is the standard port used for the HTTPS protocol?
使用https的话应该是443.
Task7
What is one luck-based method of exploiting login pages?
暴力破解嘛!
brute-forcing
Task8
What is a folder called in web-application terminology?
directory
Task9
What response code is given for "Not Found" errors?
404
Task10
What switch do we use with Gobuster to specify we're looking to discover directories, and not subdomains?
dir
Task11
What symbol do we use to comment out parts of the code?
#
Task12
Submit root flag
访问目标地址,发现是个登陆页面,构造username:admin '#,password随意,尝试登陆,成功登陆并获取flag。

原理是后台未过滤输入信息,使用单引号闭合了前面查询语句,并用#注释了后面查询语句,如下所示。
SELECT * FROM users WHERE username=‘admin'#’ AND password=‘123456’
此时只要用户名为真整个查询语句就为真,从而实现登陆绕过。
e3d0796d002a446c0e622226f42e9672























 1721
1721











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








