Introduction
Crossbow provides the building blocks for network virtualization and resource control by virtualizing the stack and NIC around any service (HTTP, HTTPS, FTP, NFS, etc.), protocol or Virtual machine.
Each virtual stack can be assigned its own priority and bandwidth on a shared NIC without causing any performance degradation. The architecture dynamically manages priority and bandwidth resources, and can provide better defense against denial-of-service attacks directed at a particular service or virtual machine by isolating the impact just to that entity. The virtual stacks are separated by means of H/W classification engine such that traffic for one stack does not impact other virtual stacks.
Project Crossbow is next step in the evolution of Solaris networking stack and brings bandwidth resource control and virtualization as part of the architecture itself instead of the usual add-on layers which have heavy overheads and complexity.
The Crossbow architecture consists of the following major components: Virtual NICs (VNICs), network resource control using the network stack squeues, and hardware support for flow classification. These components and their interaction are represented by the following figure:
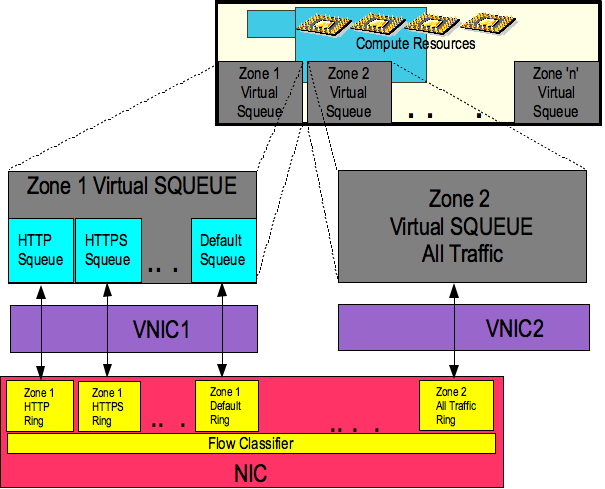
A single physical NIC can be carved up into multiple VNICs, which can be assigned to different zones or Xen instances running on the same system. VNICs are managed using the dladm(1M) command line utility which was introduced by the Nemo project. The NIC hardware classifier steers inbound traffic to the hardware receive rings that are associated with the VNICs.
Crossbow creates the concept of a flow, which comprises a class of traffic and a handling policy (bandwidth limit, priority, etc.) A flow, for example, can correspond to a particular protocol, service, or virtual machine. The squeues that were introduced in Solaris 10 as part of FireEngine are extended to control the resources used by flows. This is done by replacing the interrupt-driven packet processing by a polling mechanism where the squeue fetches packets from the hardware.
Hardware Support for Flow Processing
Modern NIC hardware provides capabilities that allow network traffic to be classified according to packet contents such as IP addresses, MAC addresses, upper layer protocols port numbers, etc. This classification allows us to steer incoming network traffic to different hardware receive rings (aka DMA channels, FIFOs). These receive rings are then associated with flows, which correspond to services or virtual machines, and are controlled by squeues.
dladm(1M) is extended to configure VNICs in a manner very similar to current link devices (create, destroy, modify, show). flowadm(1M) is provided to configure flows (create, destroy, modify, show). Each flow is affiliated with exactly one VNIC. Each VNIC has one flow when it is created. One of our major goals is to make the administration of VNICs, flows, and resource usage polices as seamless as possible. When possible, these operations will be tightly integrated with the zone administration tools.
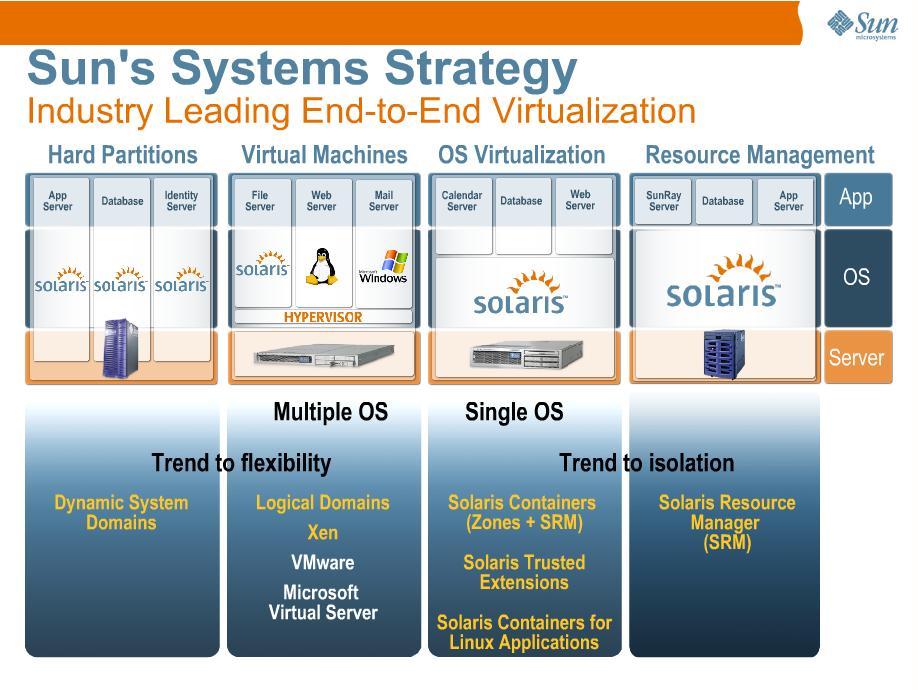
PS: Solaris Virtualization Strategy





















 416
416

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








