OP-TEE的TA签名、验签以及TA加载过程
文章目录
从本篇开始整理OP-TEE相关的技术点,整理过程中自己也慢慢归类和学习。
使用的op-tee版本号是3.12
一、TA的签名及验签
1.TA的签名
optee-os/ta/ta.mk
# Copy the scripts
ta-scripts = scripts/sign_encrypt.py scripts/symbolize.py
$(foreach f, $(ta-scripts), \
$(eval $(call copy-file, $(f), $(out-dir)/export-$(sm)/scripts)))
ta-mkfiles = mk/compile.mk mk/subdir.mk mk/gcc.mk mk/clang.mk mk/cleandirs.mk \
mk/cc-option.mk \
ta/arch/$(ARCH)/link.mk ta/arch/$(ARCH)/link_shlib.mk \
ta/mk/ta_dev_kit.mk
ta/arch/arm/link.mk,sign_encrypt.py就是用来签名用的,下面是定义,传的参数有key/uuid/ta-verision等信息:
SIGN_ENC ?= $(PYTHON3) $(ta-dev-kit-dir$(sm))/scripts/sign_encrypt.py
TA_SIGN_KEY ?= $(ta-dev-kit-dir$(sm))/keys/default_ta.pem
crypt-args$(user-ta-uuid) := --enc-key $(TA_ENC_KEY)
$(link-out-dir$(sm))/$(user-ta-uuid).ta: \
$(link-out-dir$(sm))/$(user-ta-uuid).stripped.elf \
$(TA_SIGN_KEY) \
$(lastword $(SIGN_ENC))
@$(cmd-echo-silent) ' $$(cmd-echo$(user-ta-uuid)) $$@'
$(q)$(SIGN_ENC) --key $(TA_SIGN_KEY) $$(crypt-args$(user-ta-uuid)) \
--uuid $(user-ta-uuid) --ta-version $(user-ta-version) \
--in $$< --out $$@
scripts/sign_encrypt.py,我们来看一下pyhon脚本的main函数
def main():
try:
from Cryptodome.Signature import pss
from Cryptodome.Signature import pkcs1_15
from Cryptodome.Hash import SHA256
from Cryptodome.PublicKey import RSA
##解析传入的参数
args = get_args(logger)
#读取RSA内容
with open(args.key, 'rb') as f:
key = RSA.importKey(f.read())
#打开TA原始镜像文件并读取内容
with open(args.inf, 'rb') as f:
img = f.read()
#创建RSA签名结构体和sha256运算结构体
h = SHA256.new()
digest_len = h.digest_size #digest长度
sig_len = key.size_in_bytes() #签名长度
img_size = len(img) #ta文件内容长度
hdr_version = args.ta_version #ta版本号
magic = 0x4f545348 #magic魔术值
#将magic/img_type这些参数按照一定的格式存到shdr变量中
shdr = struct.pack('<IIIIHH',
magic, img_type, img_size, algo[args.algo],
digest_len, sig_len)
shdr_uuid = args.uuid.bytes
shdr_version = struct.pack('<I', hdr_version)
#将shdr等内容填充到sha256结构体数据区域中
h.update(shdr)
h.update(shdr_uuid)
h.update(shdr_version)
h.update(img)
#获取h的digest摘要信息
img_digest = h.digest()
#对digest使用RSA私钥进行签名
#最后对shdr、shdr+img的SHA结果、signature、uuid等信息全部存到文件中
def write_image_with_signature(sig):
with open(args.outf, 'wb') as f:
f.write(shdr)
f.write(img_digest)
f.write(sig)
f.write(shdr_uuid)
f.write(shdr_version)
f.write(img)
最后签名后的TA镜像中的格式内容如下:
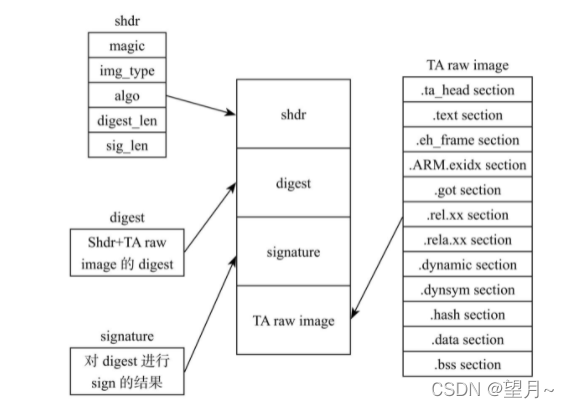
细看一下这个结构,其实和android AVB签名后的文件内容格式是十分相似的,大道同归了。
2.TA的public key处理
在@core/sub.mk中有生成ta的公钥的脚本处理,如下所示,将公钥转存到ta_pub_key.c中了。
这个公钥有什么用?可以理解为后面验签时提供身份证明,公钥相同的情况下验签才可靠。
ifeq ($(CFG_WITH_USER_TA),y)
gensrcs-y += ta_pub_key
produce-ta_pub_key = ta_pub_key.c
depends-ta_pub_key = $(TA_PUBLIC_KEY) scripts/pem_to_pub_c.py
recipe-ta_pub_key = $(PYTHON3) scripts/pem_to_pub_c.py --prefix ta_pub_key \
--key $(TA_PUBLIC_KEY) --out $(sub-dir-out)/ta_pub_key.c
ta_pub_key.c的生成路径在out/arm-plat-jlq/core/ta_pub_key.c
const uint32_t ta_pub_key_exponent = 65537;
const uint8_t ta_pub_key_modulus[] = {
0xa6, 0x5a, 0x18, 0xad, 0xc0, 0xb3, 0xce, 0xe3,
...
}
const size_t ta_pub_key_modulus_size = sizeof(ta_pub_key_modulus);
一共产生了三个全局变理ta_pub_key_exponent 、ta_pub_key_modulus、ta_pub_key_modulus_size ,后面的代码流程中可以直接使用。
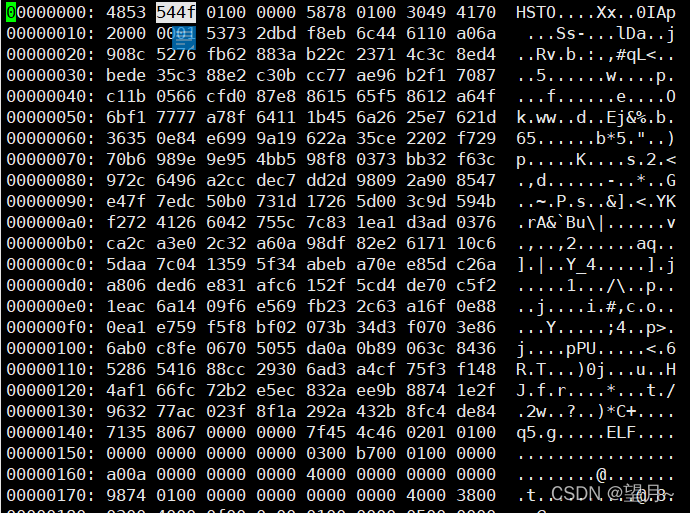
在验签之前,我们先看一下编译出来的ta头文件中到底长什么样?
我们随便找个find -name *.ta,然后vim xxx.ta,进去后输入%!xxd命令,下面是我随便找的TA内容,可以看到magic值是4853544f,和前面sign时的magic 0x4f545348 是相等的。
3.TA的验签
讲完了签名,接下来讲一下验证签名。
我们先看一下TA的加载,在加载的流程中验证了签名,请先跳转到本篇的第二章节了解TA的加载的过程,验签是Load的过程中完成的。
@ree_fs_ta.c
/* Validate header signature */
res = shdr_verify_signature(shdr);
/*
* Initialize a hash context and run the algorithm over the signed
* header (less the final file hash and its signature of course)
*/
res = crypto_hash_alloc_ctx(&hash_ctx,
TEE_DIGEST_HASH_TO_ALGO(shdr->algo));
if (res != TEE_SUCCESS)
goto error_free_payload;
res = crypto_hash_init(hash_ctx);
if (res != TEE_SUCCESS)
goto error_free_hash;
res = crypto_hash_update(hash_ctx, (uint8_t *)shdr, sizeof(*shdr));
if (res != TEE_SUCCESS)
goto error_free_hash;
shdr_sz = SHDR_GET_SIZE(shdr);
if (!shdr_sz) {
res = TEE_ERROR_SECURITY;
goto error_free_hash;
}
offs = shdr_sz;
先分析shdr_verify_signature函数
@signed_hdr.c
TEE_Result shdr_verify_signature(const struct shdr *shdr)
{
struct rsa_public_key key;
TEE_Result res;
uint32_t e = TEE_U32_TO_BIG_ENDIAN(ta_pub_key_exponent);
size_t hash_size;
#检查magic值是否匹配
if (shdr->magic != SHDR_MAGIC)
return TEE_ERROR_SECURITY;
if (TEE_ALG_GET_MAIN_ALG(shdr->algo) != TEE_MAIN_ALGO_RSA)
return TEE_ERROR_SECURITY;
res = tee_alg_get_digest_size(TEE_DIGEST_HASH_TO_ALGO(shdr->algo),
&hash_size);
if (res)
return TEE_ERROR_SECURITY;
if (hash_size != shdr->hash_size)
return TEE_ERROR_SECURITY;
res = crypto_acipher_alloc_rsa_public_key(&key, shdr->sig_size);
if (res)
return TEE_ERROR_SECURITY;
res = crypto_bignum_bin2bn((uint8_t *)&e, sizeof(e), key.e);
if (res)
goto out;
res = crypto_bignum_bin2bn(ta_pub_key_modulus, ta_pub_key_modulus_size,
key.n);
if (res)
goto out;
#重点是crypto_acipher_rsassa_verify函数
res = crypto_acipher_rsassa_verify(shdr->algo, &key, shdr->hash_size,
SHDR_GET_HASH(shdr), shdr->hash_size,
SHDR_GET_SIG(shdr), shdr->sig_size);
out:
crypto_acipher_free_rsa_public_key(&key);
if (res)
return TEE_ERROR_SECURITY;
return TEE_SUCCESS;
}
其中crypto_acipher_rsassa_verify调用的rsa.c中的函数
TEE_Result crypto_acipher_rsassa_verify(uint32_t algo,
struct rsa_public_key *key,
int salt_len, const uint8_t *msg,
size_t msg_len, const uint8_t *sig,
size_t sig_len)
{
...
rsa_ssa.key.key = key;
rsa_ssa.key.isprivate = false;
rsa_ssa.key.n_size = crypto_bignum_num_bytes(key->n);
rsa = drvcrypt_get_ops(CRYPTO_RSA);
ret = drvcrypt_rsassa_verify(&rsa_ssa);
}
@core/drivers/crypto/crypto_api/acipher/rsassa.c
TEE_Result drvcrypt_rsassa_verify(struct drvcrypt_rsa_ssa *ssa_data)
{
switch (ssa_data->algo) {
case TEE_ALG_RSASSA_PKCS1_V1_5:
case TEE_ALG_RSASSA_PKCS1_V1_5_MD5:
case TEE_ALG_RSASSA_PKCS1_V1_5_SHA1:
case TEE_ALG_RSASSA_PKCS1_V1_5_SHA224:
case TEE_ALG_RSASSA_PKCS1_V1_5_SHA256:
case TEE_ALG_RSASSA_PKCS1_V1_5_SHA384:
case TEE_ALG_RSASSA_PKCS1_V1_5_SHA512:
return rsassa_pkcs1_v1_5_verify(ssa_data);
case TEE_ALG_RSASSA_PKCS1_PSS_MGF1_SHA1:
case TEE_ALG_RSASSA_PKCS1_PSS_MGF1_SHA224:
case TEE_ALG_RSASSA_PKCS1_PSS_MGF1_SHA256:
case TEE_ALG_RSASSA_PKCS1_PSS_MGF1_SHA384:
case TEE_ALG_RSASSA_PKCS1_PSS_MGF1_SHA512:
return rsassa_pss_verify(ssa_data);
default:
break;
}
return TEE_ERROR_BAD_PARAMETERS;
}
对实现细节感兴趣的可以跟着下面代码继续分析一下。
static TEE_Result rsassa_pkcs1_v1_5_verify(struct drvcrypt_rsa_ssa *ssa_data)
{
...
EM.length = ssa_data->key.n_size;
EM.data = malloc(EM.length);
EM_gen.length = ssa_data->key.n_size;
EM_gen.data = malloc(EM.length);
/*
* RSA Encrypt/Decrypt are doing the same operation except
* that the encrypt takes a RSA Public key in parameter
*/
rsa_data.key.key = ssa_data->key.key;
rsa_data.key.isprivate = false;
rsa_data.key.n_size = ssa_data->key.n_size;
rsa = drvcrypt_get_ops(CRYPTO_RSA);
if (rsa) {
/* Prepare the encryption data parameters */
rsa_data.rsa_id = DRVCRYPT_RSASSA_PKCS_V1_5;
rsa_data.message.data = ssa_data->signature.data;
rsa_data.message.length = ssa_data->signature.length;
rsa_data.cipher.data = EM.data;
rsa_data.cipher.length = EM.length;
ret = rsa->encrypt(&rsa_data);
/* Set the cipher size */
EM.length = rsa_data.cipher.length;
} else {
ret = TEE_ERROR_NOT_IMPLEMENTED;
}
/* Encode the Message */
if (ssa_data->algo != TEE_ALG_RSASSA_PKCS1_V1_5)
ret = emsa_pkcs1_v1_5_encode(ssa_data, &EM_gen);
else
ret = emsa_pkcs1_v1_5_encode_noasn1(ssa_data, &EM_gen);
/* Check if EM decrypted and EM re-generated are identical */
ret = TEE_ERROR_SIGNATURE_INVALID;
if (EM.length == EM_gen.length) {
if (!memcmp(EM.data, EM_gen.data, EM.length))
ret = TEE_SUCCESS;
}
到这里验证签名就完成了。
二、TA的加载
ree_fs_ta.c 我们着重看一下buf_ta_open操作,看下TA的加载是怎样的。
REGISTER_TA_STORE(9) = {
.description = "REE [buffered]",
.open = buf_ta_open,
.get_size = buf_ta_get_size,
.get_tag = buf_ta_get_tag,
.read = buf_ta_read,
.close = buf_ta_close,
};
static TEE_Result buf_ta_open(const TEE_UUID *uuid,
struct ts_store_handle **h)
{
...
res = ree_fs_ta_open(uuid, &handle->h);
}
static TEE_Result ree_fs_ta_open(const TEE_UUID *uuid,
struct ts_store_handle **h)
{
...
/* Request TA from tee-supplicant */
res = rpc_load(uuid, &ta, &ta_size, &mobj);
rpc_load函数调用,是通过调用REE侧的tee-supplicant进程来完成的(optee本身不支持文件系统)
发送请求给tee-supplicant加载指定UUID的TA,optee会对收到的数据做安全性校验,如果验证通过会将相关段中的内存 保存到OP-TEE用户空间分配的TA内存中。
1.RPC请求加载TA
RPC请求一共有两次,第一次请求到REE内里获取TA的基本信息,第二次请求会将TA加载到OP-TEE的用户空间内存地址上。
2.获取TA文件内容到共享内存
static TEE_Result rpc_load(const TEE_UUID *uuid, struct shdr **ta,
size_t *ta_size, struct mobj **mobj)
{
...
#第一次RPC请求的参数,返回镜像的大小
memset(params, 0, sizeof(params));
params[0].attr = THREAD_PARAM_ATTR_VALUE_IN;
tee_uuid_to_octets((void *)¶ms[0].u.value, uuid);
params[1].attr = THREAD_PARAM_ATTR_MEMREF_OUT;
res = thread_rpc_cmd(OPTEE_RPC_CMD_LOAD_TA, 2, params);
#第二次RPC请求
#分配和TA镜像大小相等的共享内存
*mobj = thread_rpc_alloc_payload(params[1].u.memref.size);
#ta指向分配出来的内存,虚拟地址保存在*ta中
*ta = mobj_get_va(*mobj, 0);
#第二次RPC请求的参数
params[0].attr = THREAD_PARAM_ATTR_VALUE_IN;
tee_uuid_to_octets((void *)¶ms[0].u.value, uuid);
params[1].attr = THREAD_PARAM_ATTR_MEMREF_OUT;
params[1].u.memref.offs = 0;
params[1].u.memref.mobj = *mobj;
#发送第二次RPC请求,这样TA镜像的内容就会加载到刚分配出来的内存中了
res = thread_rpc_cmd(OPTEE_RPC_CMD_LOAD_TA, 2, params);
}
接下来分析一下thread_rpc_cmd是如何完成TEE和REE侧通讯的
@core/arch/arm/kernel/thread_optee_smc.c
uint32_t thread_rpc_cmd(uint32_t cmd, size_t num_params,
struct thread_param *params)
{
uint32_t rpc_args[THREAD_RPC_NUM_ARGS] = { OPTEE_SMC_RETURN_RPC_CMD };
void *arg = NULL;
uint64_t carg = 0;
uint32_t ret = 0;
/* The source CRYPTO_RNG_SRC_JITTER_RPC is safe to use here */
plat_prng_add_jitter_entropy(CRYPTO_RNG_SRC_JITTER_RPC,
&thread_rpc_pnum);
ret = get_rpc_arg(cmd, num_params, params, &arg, &carg);
if (ret)
return ret;
reg_pair_from_64(carg, rpc_args + 1, rpc_args + 2);
#重点是thread_rpc函数,本质是SMC命令,切换TEE和REE环境
thread_rpc(rpc_args);
return get_rpc_arg_res(arg, num_params, params);
}
thread_rpc是安全监控模式SMC的调用
@core/arch/arm/kernel/thread_optee_smc_a64.S,汇编代码,感兴趣的可以看看。
FUNC thread_rpc , :
/* Read daif and create an SPSR */
mrs x1, daif
orr x1, x1, #(SPSR_64_MODE_EL1 << SPSR_64_MODE_EL_SHIFT)
/* Mask all maskable exceptions before switching to temporary stack */
msr daifset, #DAIFBIT_ALL
push x0, xzr
push x1, x30
bl thread_get_ctx_regs
ldr x30, [sp, #8]
store_xregs x0, THREAD_CTX_REGS_X19, 19, 30
mov x19, x0
bl thread_get_tmp_sp
pop x1, xzr /* Match "push x1, x30" above */
mov x2, sp
str x2, [x19, #THREAD_CTX_REGS_SP]
ldr x20, [sp] /* Get pointer to rv[] */
mov sp, x0 /* Switch to tmp stack */
load_wregs x20, 0, 21, 23 /* Load rv[] into w20-w22 */
adr x2, .thread_rpc_return
mov w0, #THREAD_FLAGS_COPY_ARGS_ON_RETURN
bl thread_state_suspend
mov x4, x0 /* Supply thread index */
ldr w0, =TEESMC_OPTEED_RETURN_CALL_DONE
mov x1, x21
mov x2, x22
mov x3, x23
smc #0
b . /* SMC should not return */
.thread_rpc_return:
pop x16, xzr /* Get pointer to rv[] */
store_wregs x16, 0, 0, 3 /* Store w0-w3 into rv[] */
ret
END_FUNC thread_rpc
3.加载TA到OP-TEE的用户空间
我们回到rpc_load函数
res = thread_rpc_cmd(OPTEE_RPC_CMD_LOAD_TA, 2, params);
*mobj = thread_rpc_alloc_payload(params[1].u.memref.size);
我们稍跟踪一下thread_rpc_alloc_payload的实现,其实到最后也是thread_rpc SMC调用。
@core/arch/arm/kernel/thread_optee_smc.c
struct mobj *thread_rpc_alloc_payload(size_t size)
{
return thread_rpc_alloc(size, 8, OPTEE_RPC_SHM_TYPE_APPL);
}
/**
* Allocates shared memory buffer via RPC
*/
static struct mobj *thread_rpc_alloc(size_t size, size_t align, unsigned int bt)
{
uint32_t rpc_args[THREAD_RPC_NUM_ARGS] = { OPTEE_SMC_RETURN_RPC_CMD };
void *arg = NULL;
uint64_t carg = 0;
struct thread_param param = THREAD_PARAM_VALUE(IN, bt, size, align);
uint32_t ret = get_rpc_arg(OPTEE_RPC_CMD_SHM_ALLOC, 1, ¶m,
&arg, &carg);
reg_pair_from_64(carg, rpc_args + 1, rpc_args + 2);
thread_rpc(rpc_args);
return get_rpc_alloc_res(arg, bt);
}
rpc_load函数发起第二次RPC请求时才会将TA镜像文件的内容读取到OP-TEE提供的共享内存中,共享内存的分配是在rpc_load函数中调用thread_rpc_alloc_payload函数来实现的。
分配的共享内存的地址将会被保存到ta_handle变量的nw_ta成员中,读取到的TA镜像文件的内容将会被加载到OP-TEE用户空间TA运行的内存中。
到这里是完整的加载过程了,如下所示:
@ree_fs_ta.c
static TEE_Result ree_fs_ta_open(const TEE_UUID *uuid,
struct ts_store_handle **h)
{
struct ree_fs_ta_handle *handle;
handle = calloc(1, sizeof(*handle));#分配内存
res = rpc_load(uuid, &ta, &ta_size, &mobj);#RPC请求加载TA
shdr = shdr_alloc_and_copy(ta, ta_size);#内存映射
res = shdr_verify_signature(shdr);#验证签名
...
handle->nw_ta = ta; ##读取到的TA内容保存在nw_ta中了
handle->nw_ta_size = ta_size;
handle->offs = offs;
handle->hash_ctx = hash_ctx;
handle->shdr = shdr;
handle->mobj = mobj;
}
以上就是我理解的TA签名、验签,以及TA的加载过程了。
























 3823
3823

 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?








